Cloud Cyber Security PlatformEuropean Cyber Research TeamThreat Intelligence PlatformThe Cyber Security Partner
Swascan's Security Testing - Threat Intelligence platform & Cyber Competence Center for your Enterprise Cyber Security Framework.
Predict. Prevent. Be Proactive.
Highlights
Threatland Report H2 - 2023
The second half of 2023 saw a significant increase in cyber attacks aimed at stealing data and demanding ransoms in exchange for restoring affected systems. Swascan's SOC and Threat Intelligence Team conducted an in-depth analysis on ransomware, malware and phishing scenarios, providing a detailed picture of emerging threats and evolving trends.
Discovere morePreparatory Course for CISSP Certification
In addition to preparing for the certification exam, the course allows you to acquire knowledge and skills for the development of an integrated vision of security, so as to be able to put its implementation into practice throughout the company. Register for the course and attend lessons from May 13, 2024.
Discover moreThreatland
Swascan has created a Cyber Compromission Dashboard to support companies in implementing an emergency plan for the correct management of Cyber risks.
Discover more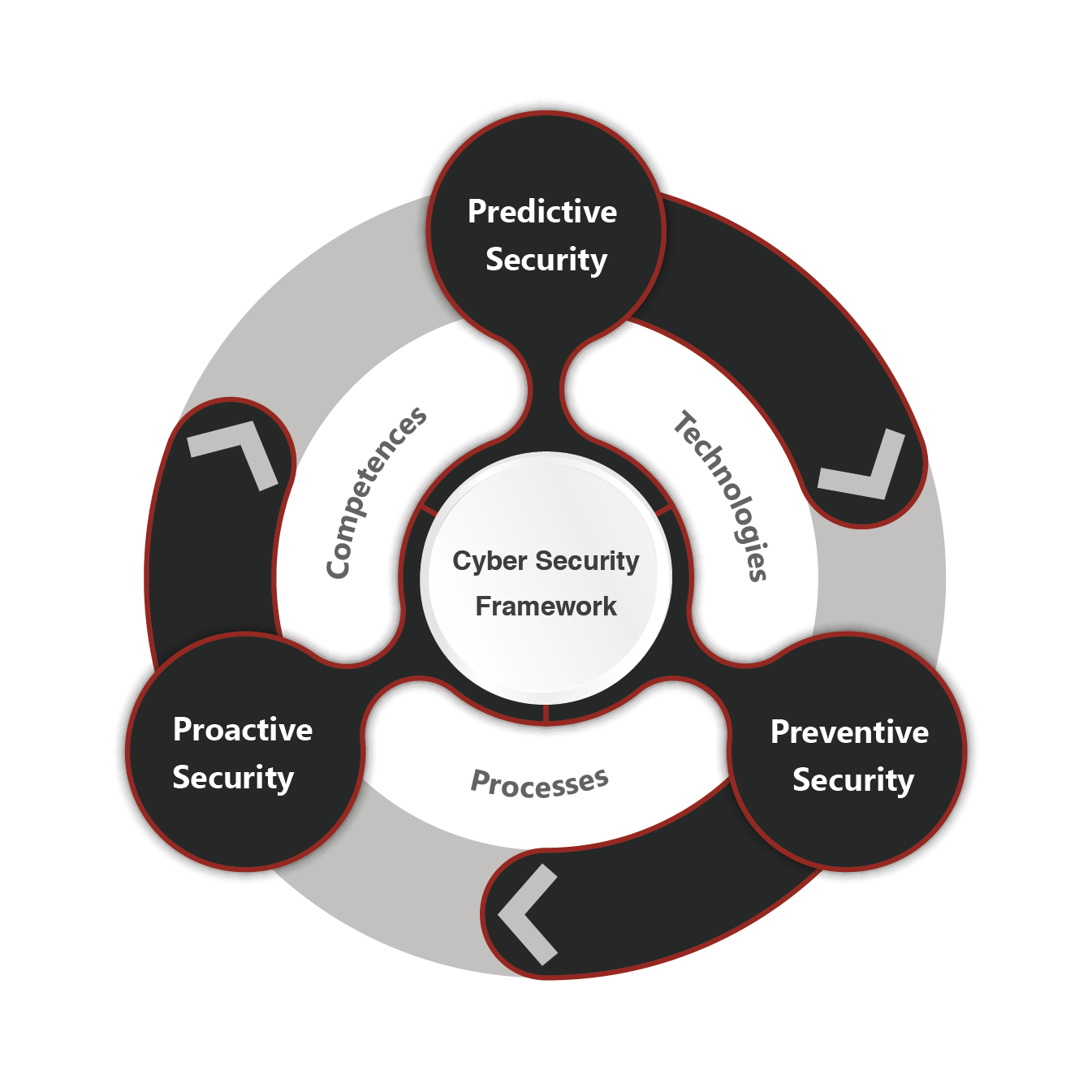
Cyber Security Framework
The Cyber Security Framework is the foundation of your company’s security posture. A set of processes and technologies that work in unison to minimise exposure to cyber risk. It is built on predictive, preventive and proactive security.
Predictive Security
Predictive Security operates at the Threat Intelligence level. Through the analysis of OSINT and CLOSINT sources, at Web, Dark Web and Deep Web level, it identifies threats, risks and information related to the target company. Predictive Security allows you to anticipate critical issues by correctly setting up preventive and proactive security.
Preventive Security
Preventive Security acts in terms of technological, human and process Risk Analysis. Activities that fall under legislative obligations and in terms of international best practices. The activities refer to penetration testing, vulnerability assessment, ransomware attack simulation, phishing simulation, training, CIS, NIST, ISO27001, GDPR Assessment.
Proactive Security
Proactive Security enables the adoption of approaches related to security by detection and security by reaction. Through the adoption of security operation center (SOC) it allows to monitor, identify, analyze, manage and block possible threats inside the company. The incident response management component guarantees the correct management of company incidents through the use of specialized and competent teams.

The Swascan Platform
Swascan is the first entirely cloud-based suite with Software as a Service for security testing and threat intelligence: check out all the services available now!
Cyber Security Competence Center
Cyber Incident Response
Swascan’s Cyber Incident Response team dedicated to handling cyber incidents, DDOS attacks, data breaches and ransomware attacks. Swascan’s Cyber team was the first in Europe to have identified, analysed and managed two of the most active ransomware gangs.
Soc as a Service
Swascan’s Security Operations Center service, recognised as a reference point for the Italian market by various international cyber vendors, for the correct management of proactive security and preventive security.
Penetration Test
Penetration test activities are conducted by certified penetration testers in accordance with the OWASP, PTES and OSSTMM international standards.
GRC Management
Security Advisory consulting and operational services to support customers with their remediation plans, management of cyber security, compliance management and risk management.
Cyber Academy
Dedicated training courses on cyber security in the classroom or by webinar. Awareness activities for technical personnel, employees and top managers.
Cyber Threat Intelligence
Aims to analyze corporate domain information present at the Dark web and Deep web level. It discovers the presence of Botnets related to the devices of employees, suppliers and customers.
24/7 Cyber Security Operation Center
A dedicated Security Operations Center team, working proactively and reactively on the threats and cyber risks of corporate systems, cloud environments, applications and corporate endpoints. Our team of security analysts monitors data and resources, H24, 7 days a week, 365 days a year.
Penetration Testing
Swascan’s offensive team is ISO 27001 and ISO 9001 certified
All activities comply with OWASP, PTES and OSSTMM standards.

Cyber Academy
In cyber security, human actions undoubtedly influence situations much more than technology. Our Cyber Academy wide range of training courses structured to respond to different levels of experience and technical specialisation.
Discover our courses
Cyber Threat Intelligence
Swascan’s Cyber Threat Intelligence service purpose and aim is to identify any information and data available at the at the web, dark web and deep web levels relating to a specific target. The activity involves the collection and analysis of information relating to a series of critical macro areas such as.
Become a Swascan Partner
Learn more about the Swascan Partner Program, thanks to which our partners serve customers better, provide fast solutions and drive growth.
Discover the Partner Program