
ICT Security Assessment -Today’s Cyber Security landscape requires the utmost attention to a set of internal macro indicators for all organisations.
Maybe your organisation has an antivirus software to protect your company’s data? Or maybe you also have firewalls and encryption technology, so you think you can sit back and let the technology protect you from a cyber attack.
But Cyber Security today is no longer monolithic, not a matter of pure technology, but also of human and organisational matters.
In order to cope with any kind of future problems and to be especially prepared in the event of a cyber attack, you need to be aware of the level of risk to which your company is exposed.
But where to start? How to ensure that the operational and technological aspects are functional and comply with 100% best practice?
Simple, you need to carry out an ICT Security Assessment.
ICT Security Assessment: what is it
The ICT Security Assessment is a Swascan proprietary methodology that allows companies to verify and measure their cyber risk level and assess the effectiveness of the security measures taken.
The service provides indications and corrective actions to be taken at the Organisation, Policy, Personnel, Technology and Control Systems level.
The ICT Security Assessment analyses two separate macro-categories that are:
Functional Cyber Risk
These indicators determine safety levels in terms of:
- Technology Risk
- Governance Risk
- Human Risk
- Data Risk
Operational Cyber Risk
These indicators determine safety levels in terms of:
- Preventive Security Gap Risk
- Proactive Security Gap Risk
- Data Breach Exposure
- Ransomware Recovery Exposure
ICT Security Assessment: how does it work
The ICT Security Assessment allows you to analyse the current situation of your company at Organisation, Policy, Personnel, Technology and Control Systems level, providing – based on the results – an assessment including the AS-IS.
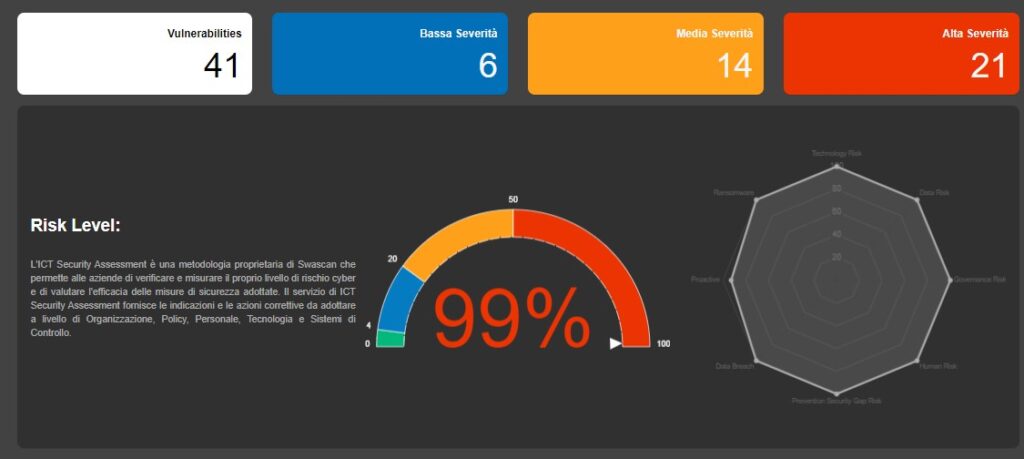
Results Sample Source: Swascan
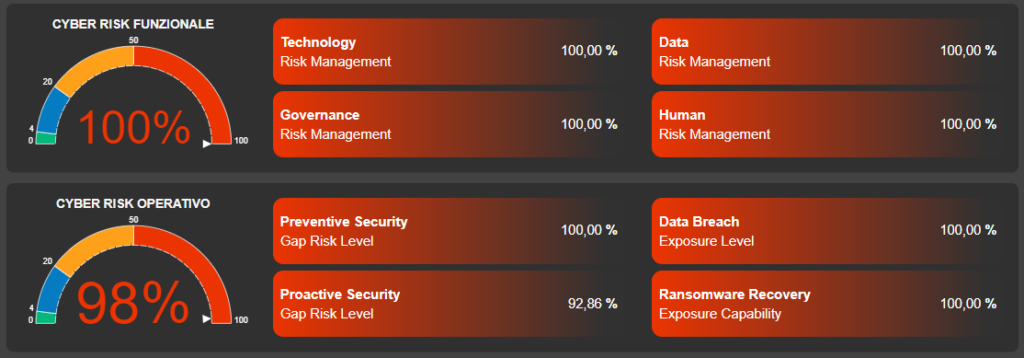
Results Sample Source: Swascan
The analysis is followed by official documentation with all the indications and corrective actions to be taken at the Organisation, Policy, Personnel, Technology and Control Systems level to be in line with best practices and to minimize the level of exposure and risk.
All documentation is immediately accessible and available both via web interface and dedicated PDF.




