Author: Fabio Pensa
LockBit 2.0 ransomware, during the last weeks, has been updated through the releasing of a new version and the announcing of a bug bounty program: in exchange of money it is possible to report to the developers of the threat possible bugs and security vulnerabilities to make it as evasive as possible and difficult to detect, both for Home and Enterprise security products (EDR,XDR).
In this dynamic analysis a LockBit 3.0 sample will be analyzed by highlighting the most interesting peculiarities, included evasion attempts.
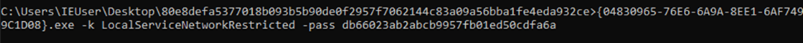
To be executed, LockBit 3.0 requires a launch password which can be specified with the option “-pass”, as below:
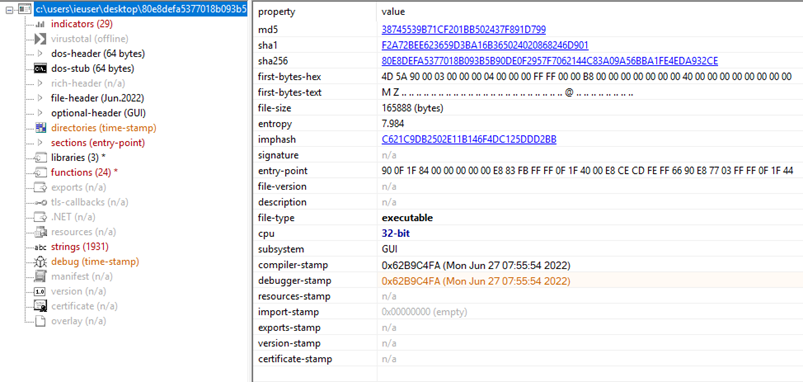
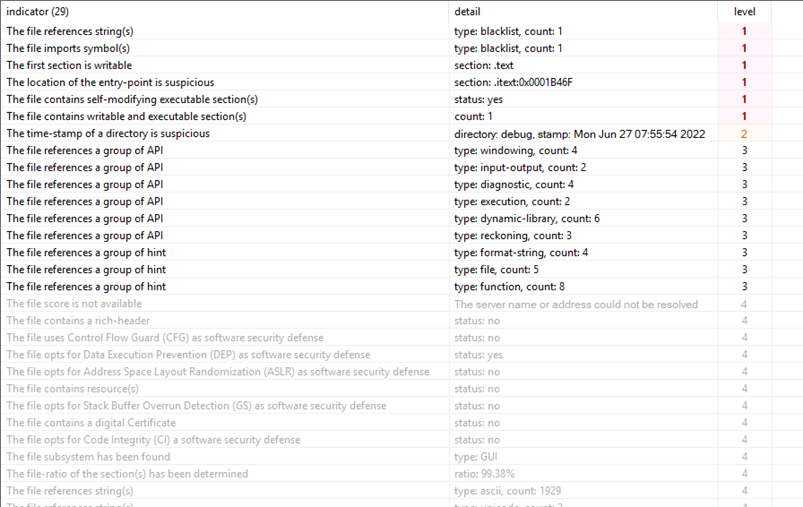
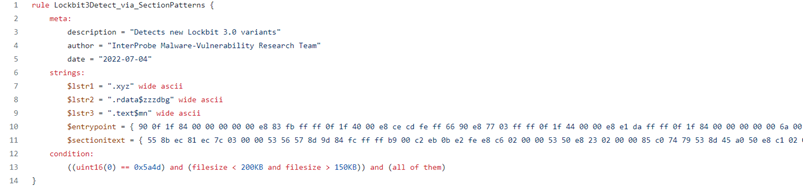
By performing an inspection of the sample it is possible to have the evidence of some malicious indicators, associated to the sections of the Portable Executable but also domain patterns, included in YARA rules created for the detection of LockBit 3.0:
Here are the details of the YARA rule specified above [1]:
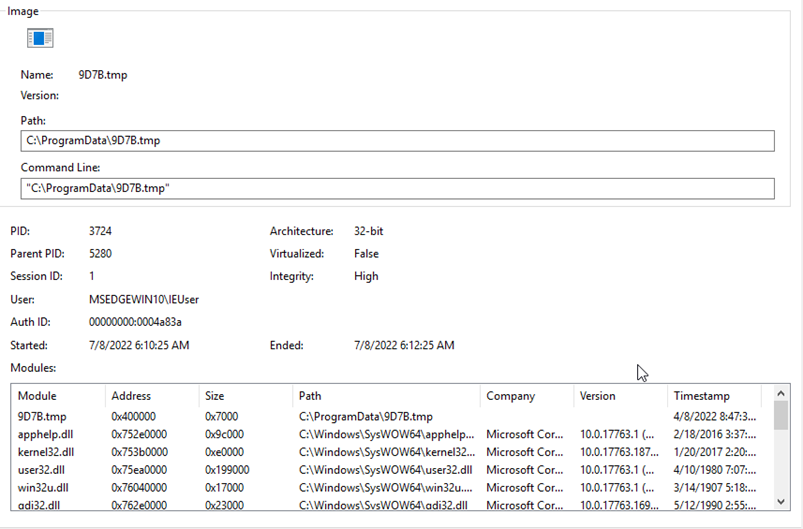
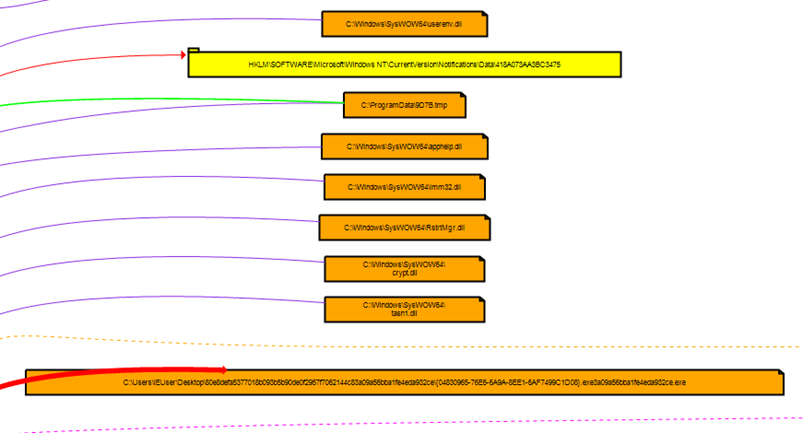
After the start of the malicious execution is possible to have the evidence the launched process (child process of CMD.exe instance), which executes “dropped” n.TMP threat (where n represents a random string) in the folder C:\ProgramData:
Here are the details of the file dropping action through WriteFile:
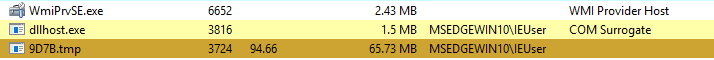
It’s possible to see an elevated use of CPU because of the execution of the threat 9D7B.tmp:
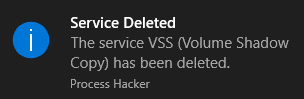
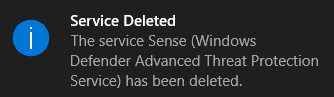
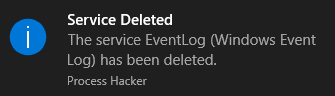
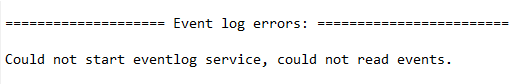
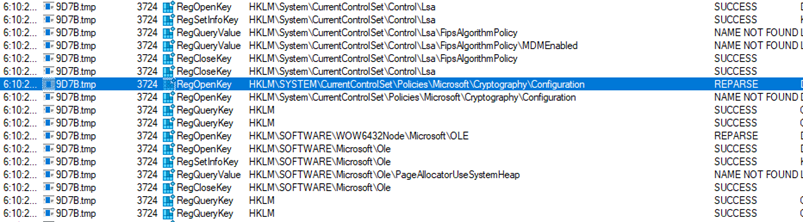
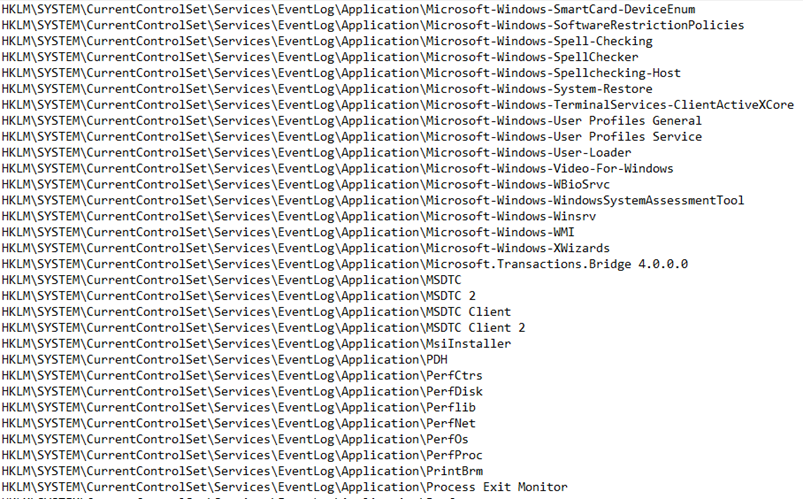
During the infection chain is possible to point out the deletion of shadow copies to make more difficult the restoring operation of the encrypted files. There are numerous attempts of defense evasion and traces clearing through the deletion of logs of Event log and the deletion of critical services of Windows Defender Advanced Threat Protection. This operation makes the compromised host more vulnerable.
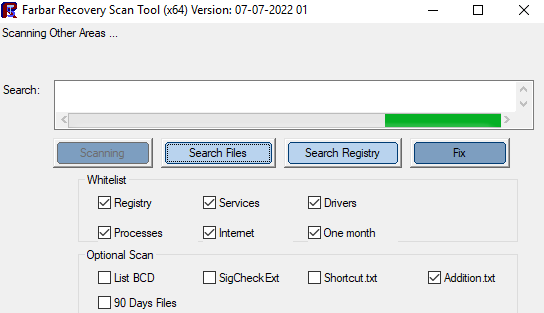
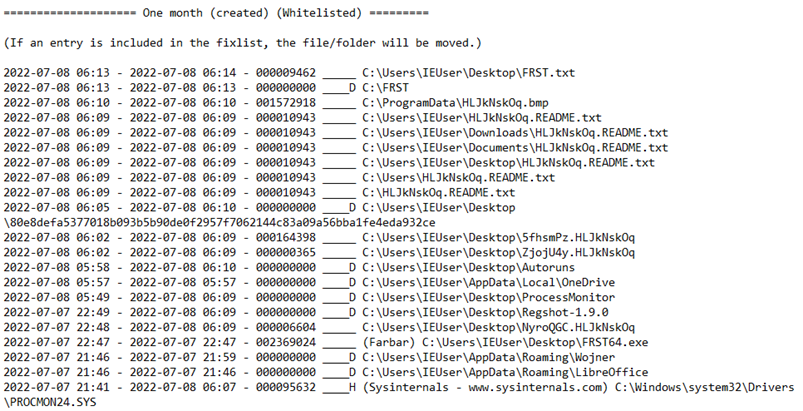
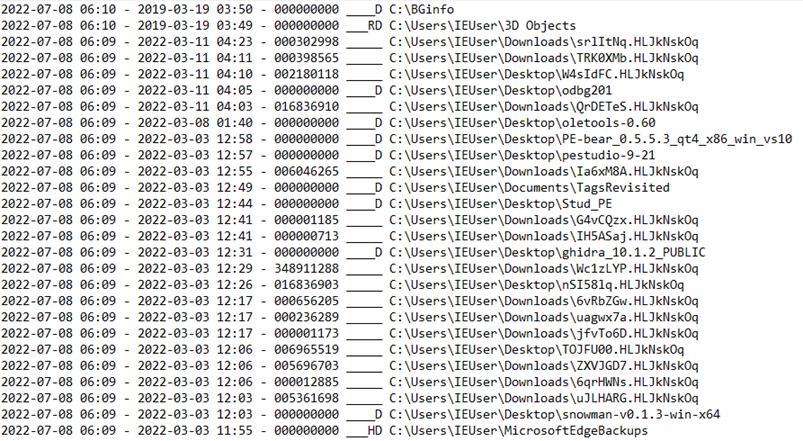
To identify others infection traces, it has been executed an infection tracing identification scan with FRST (Farbar Recovery Scan Tool). FRST is a tool which permits to perform malware removal through scripts called “fixlist.txt” that, starting from logs called “FRST.txt” and “Addition.txt”, permit to delete all the infection traces in the compromised operating system. Although that Farbar Recovery Scan Tool can be used also in dynamic malware analysis contexts, to identify dropped files, created registry keys, scheduled tasks, etc.
Here are the most relevant findings in this specific case which highlight the traces of dropped files in the file system, included readme files:
Here are the evidences of the disabling of Windows Defender services and the deletion of Event log logs, detected also with the use of FRST:
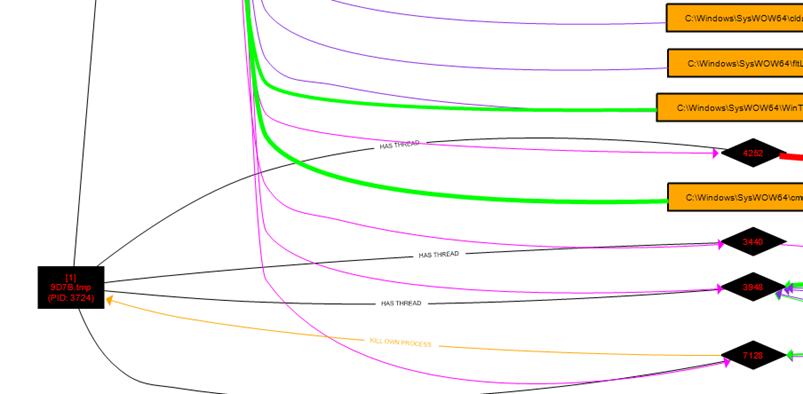
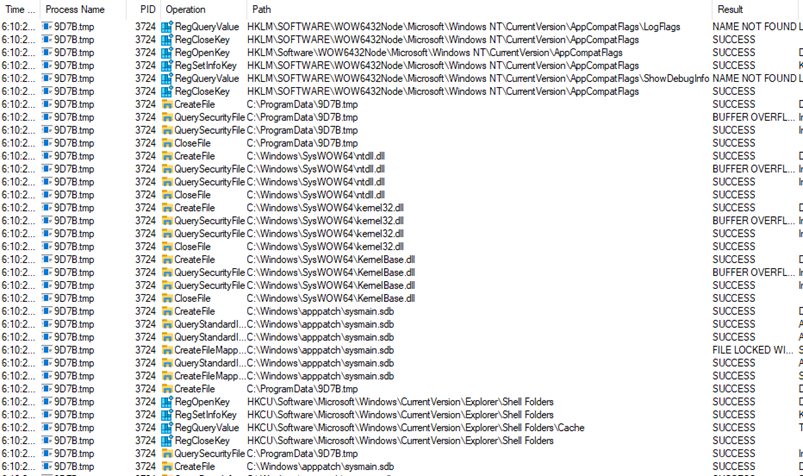
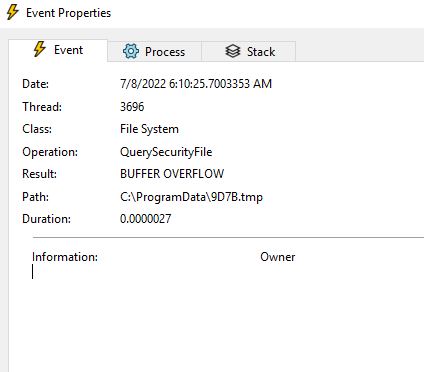
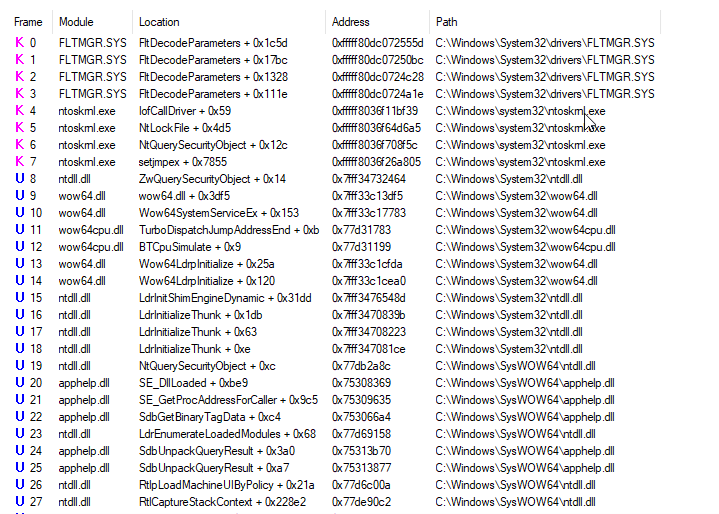
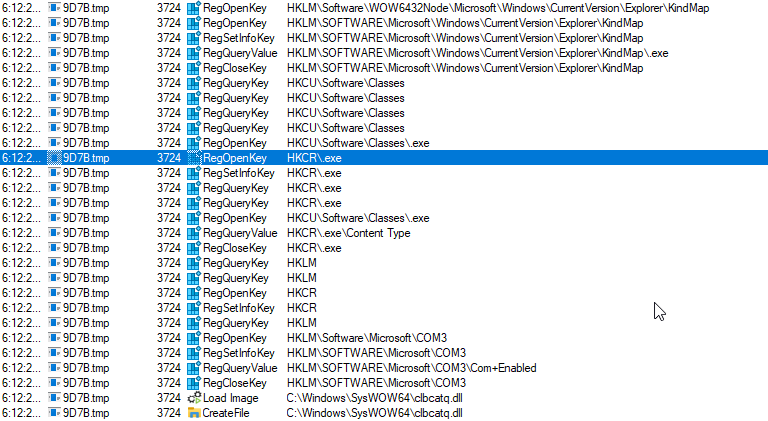
Here below numerous operations of the process 9D7B.tmp. In some cases Buffer Overflow exceptions have been detected during the iterative reading of the files attributes:
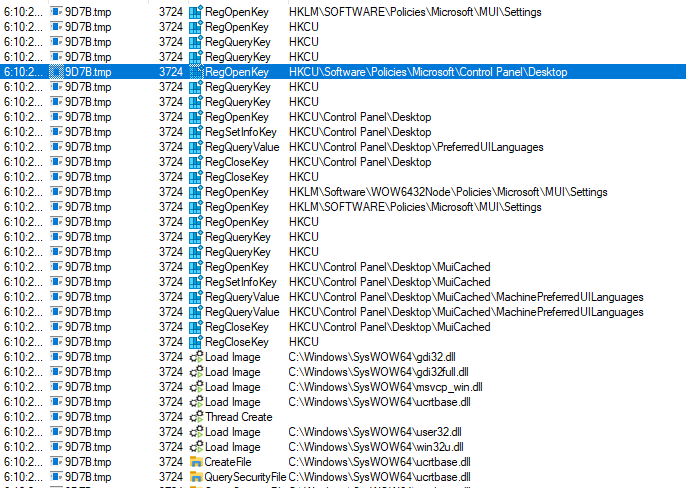
Here below some evidences of system registry access where Desktop settings are managed to modify it with the ransomware wallpaper:
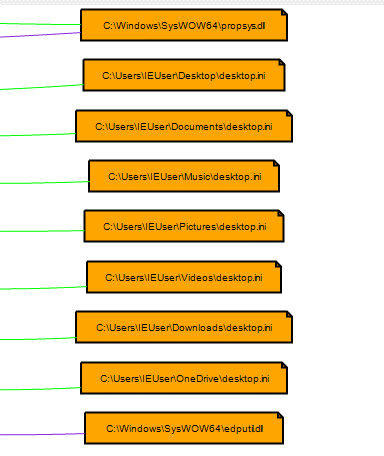
Please see the access to the desktop.ini file settings:
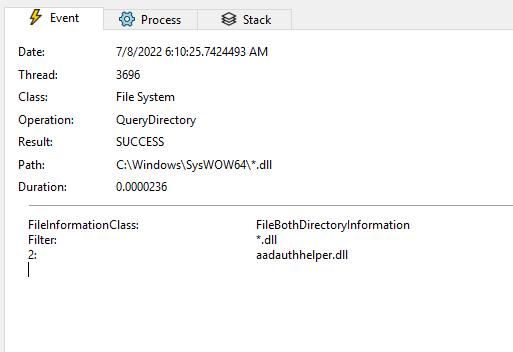
A general DLL retrieve in SysWOW64 through QueryDirectory has been performed with the argument “*.dll”:
The core of the infection is related to the use from the ransomware of encryption functions, in particular the use of the module bcrypt.dll, here below the evidences identified in the dynamic analysis phase:
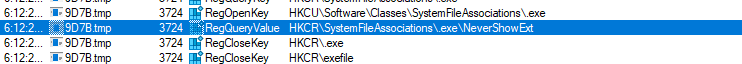
It seems that the ransomware accesses to the settings of executables file types file associations (.EXE) through some specific registry keys, in particular “NeverShowExt”:
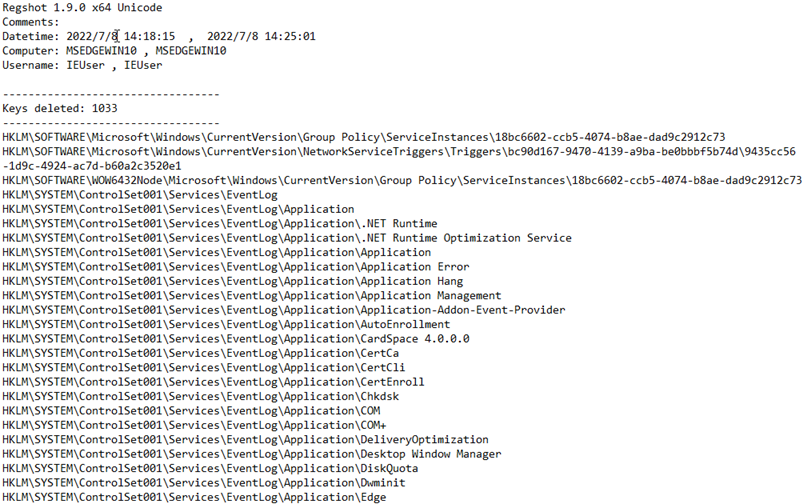
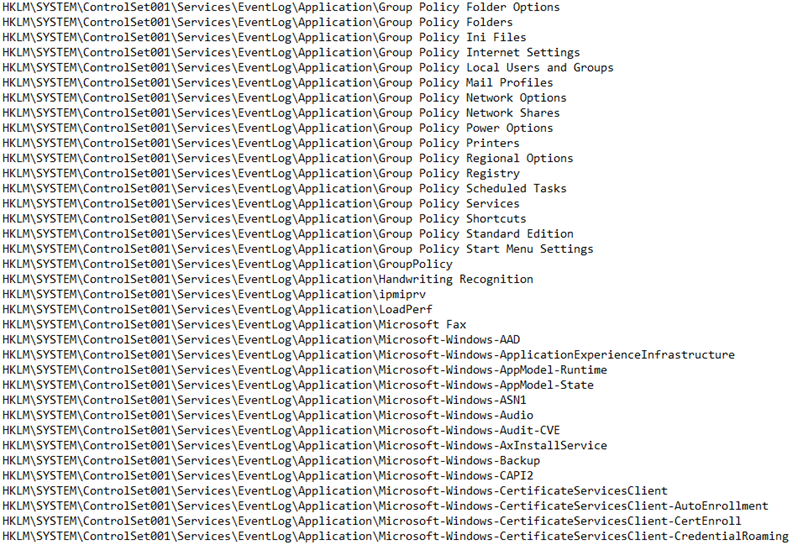
Here are the details of the differences between the two registry snapshots, before and after the infection of LockBit 3.0. Please note that there are the deletion of Group Policies registry keys and Event Log registry keys:
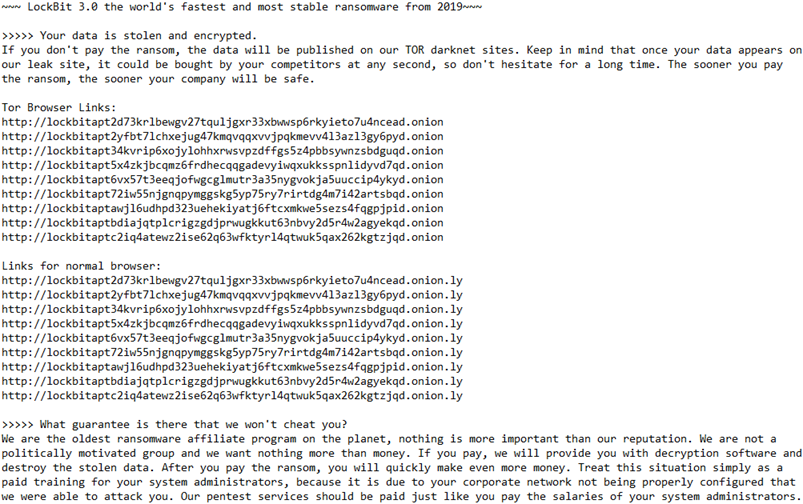
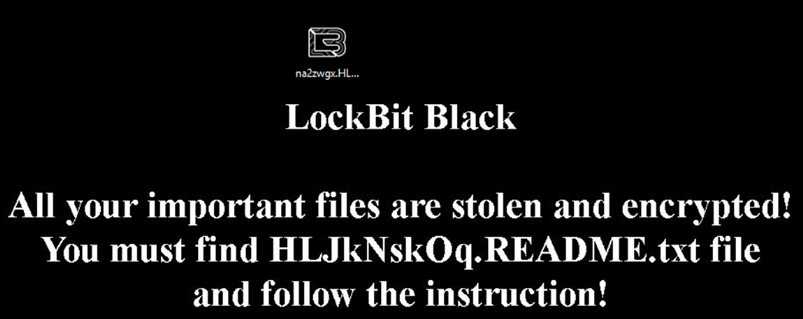
Here are the details of the ransom notes:
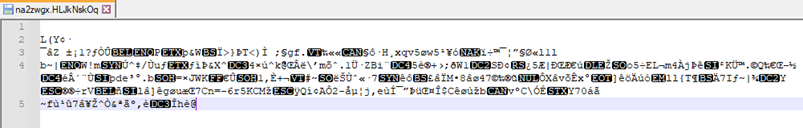
Here are the details of one of the files encrypted during the dynamic analysis session:
CONCLUSIONS:
LockBit 3.0 is a very efficient ransomware, well designed and developed and with an high level of evasion. It is fundamental to consider it is mainly delivered with Phishing emails which are related to fake PDF documents. During the session of the dynamic malware analysis, it is emerged that LockBit 3.0 manages to perform a quite fast encryption routine, renaming in a randomic mode the encrypted files. It is curious that a ransomware gang has created a bug bounty system: this demonstrates that the trend of threat actors is more oriented to create threats with specific objectives (probably also with targeted Phishing emails) and at the same time paying scrupulous attention to anti-detection attempts. Also, the fact that LockBit 3.0 deletes the events of the Event Log, makes a possible Incident Response phase more difficult and complex.