In the period of time between January and May 2021, Ransomware has done nothing but confirmed itself as the primary threat in the global IT security landscape.
The spike in infections and strains that had begun to appear around the end of 2019, has only increased with a consequent evolution of TTPs (Tactics, Techniques, and Procedures) adopted and honed by different groups of Criminal Hackers, which now have evolved into full-fledged Cyber Crime cartels.
In particular double extortion has risen to prominence. With this in mind, Swascan’s SoC as a Service Team has undertaken an analysis of the profiles of the victims targeted by Criminal Hackers.
In particular, through specific OSINT & CLOSINT researches, the data concerning the Ransomware victims who had their data published on the Darkweb has been collected and analysed.
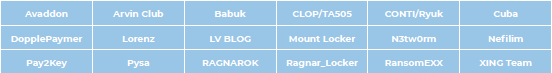
Swascan has studied 18 Ransomware strains which now use Double extortion as their fixture and the sites where the data is published.
The approach was the following:
- Identify the Darkweb sites of the analysed Ransomware groups;
- Identify the targeted companies which had their data published on Darkweb portals;
- Clustering information related to victims in terms of:
- Geographic area
- Volume of published data
- Turnover of affected firms
- Strains involved
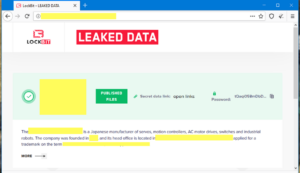
Figure 1: An example of a Double extortion website in
which the data is published
Context
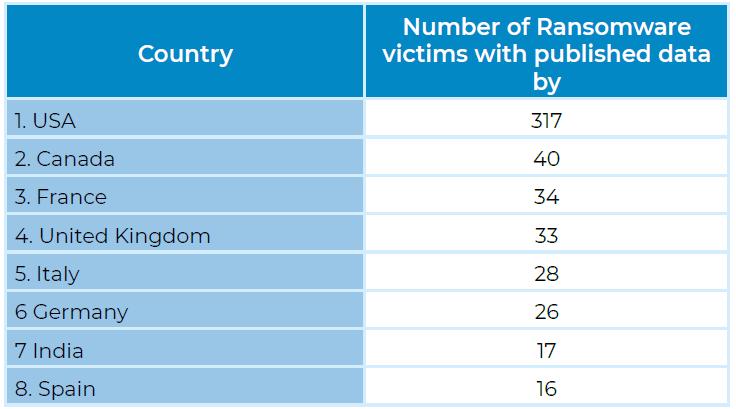
Focusing on the top 8 countries in terms of the number of cases detected, it is possible to observe that the number of victims that had their data published reaches 511 cases.
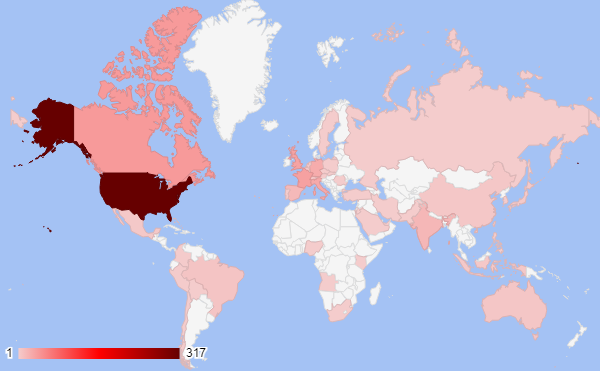
Figure 2: Geographical distribution of victims with data published in double extortion sites
As can be seen from this first chart (Figure 2), North America stands out as the absolute leader
for companies with published information with 69.8% of strains hitting between the US and
Canada. The former remains in the lead with 317 companies involved in the period between
January 2021 and May 2021.
Canada follows with 40 instances, while the podium is closed by France with 34.