
Cybersecurity service: Swascan proposition
Security Management has become, over the past few years, an essential aspect to consider for companies. Organizations can not afford to underestimate the impacts of a bad Security Management: loss of reputation, stop of the normal activities of the company, fines,…
In this regard, Swascan offers a various range of solutions useful to to face Security Management issues. Through specialized and extremely professional consultations, Swascan allows companies to achieve the goal of a correct Risk and Security Management and Compliance with current laws as well. In order to have a full overview of Swascan consultancy services, here you can find the CyberSecurity Service brochure.
Security Management: a professional point of view
As a guarantee of professionalism, Swascan has among its founders Raoul Chiesa: Italian CyberSecurity expert, known worldwide for his knowledge in cybersecurity, hacking and cyber-crime. He is a member of several European and International governmental and non-governmental security organizations. Here’s a video of Raoul explaining Swascan innovative soul:
Security Management
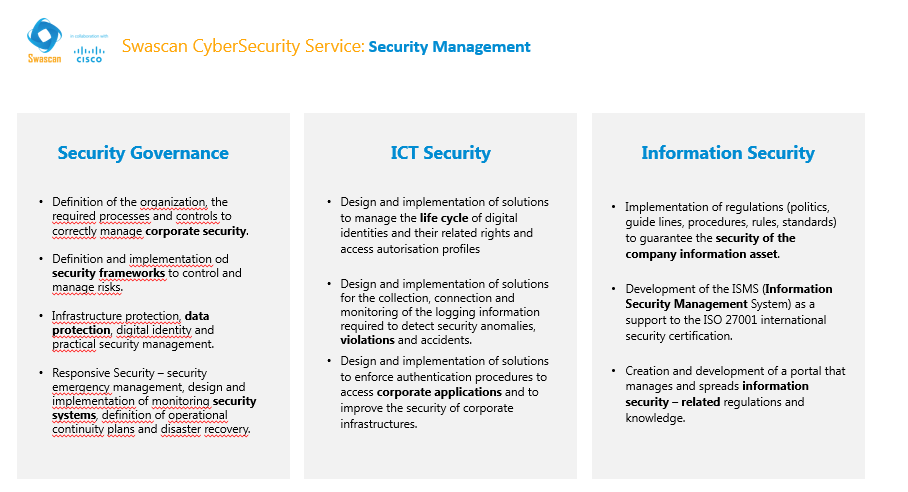
Security Management considers several aspects:
- Security Governance:
- Definition of the organization, the required processes and controls to correctly manage corporate security;
- Definition and implementation od security frameworks to control and manage risks;
- Infrastructure protection, data protection, digital identity and practical security management;
- Responsive Security – security emergency management, design and implementation of monitoring security systems, definition of operational continuity plans and disaster recovery.
- ICT Security:
- Design and implementation of solutions to manage the life cycle of digital identities and their related rights and access autorisation profiles;
- Design and implementation of solutions for the collection, connection and monitoring of the logging information required to detect security anomalies, violations and accidents;
- Design and implementation of solutions to enforce authentication procedures to access corporate applications and to improve the security of corporate infrastructures.
- Information Security:
- Implementation of regulations (politics, guide lines, procedures, rules, standards) to guarantee the security of the company information asset.
- Development of the ISMS (Information Security Management System) as a support to the ISO 27001 international security certification.
- Creation and development of a portal that manages and spreads information security – related regulations and knowledge.
Risk Management
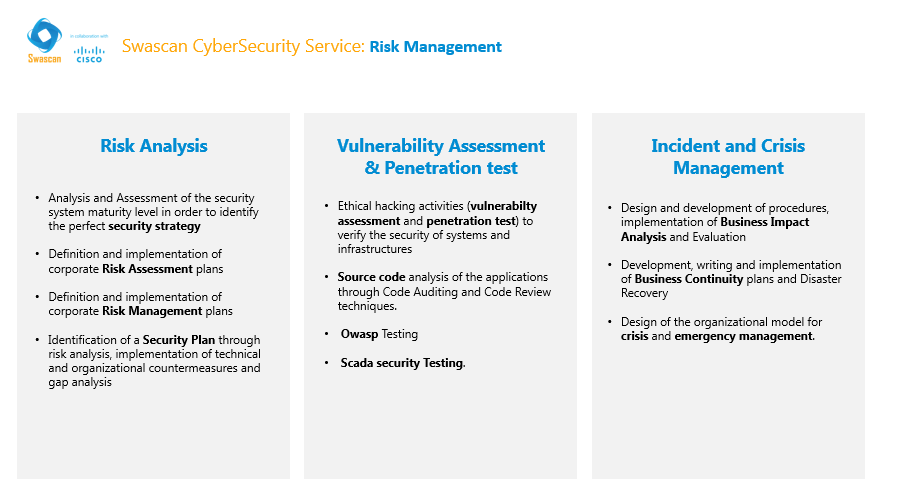 On the other hand, Risk Management, divides itself into:
On the other hand, Risk Management, divides itself into:
- Risk Analysis:
- Analysis and Assessment of the security system maturity level in order to identify the perfect security strategy;
- Definition and implementation of corporate Risk Assessment plans;
- Definition and implementation of corporate Risk Management plans;
- Identification of a Security Plan through risk analysis, implementation of technical and organizational countermeasures and gap analysis.
- Vulnerability Assessment & Penetration test:
- Ethical hacking activities (vulnerabilty assessment and penetration test) to verify the security of systems and infrastructures;
- Source code analysis of the applications through Code Auditing and Code Review techniques.
- Owasp Testing;
- Scada security Testing.
- Incident and Crisis Management:
- Design and development of procedures, implementation of Business Impact Analysis and Evaluation;
- Development, writing and implementation of Business Continuity plans and Disaster Recovery;
- Design of the organizational model for crisis and emergency management.
Compliance Management
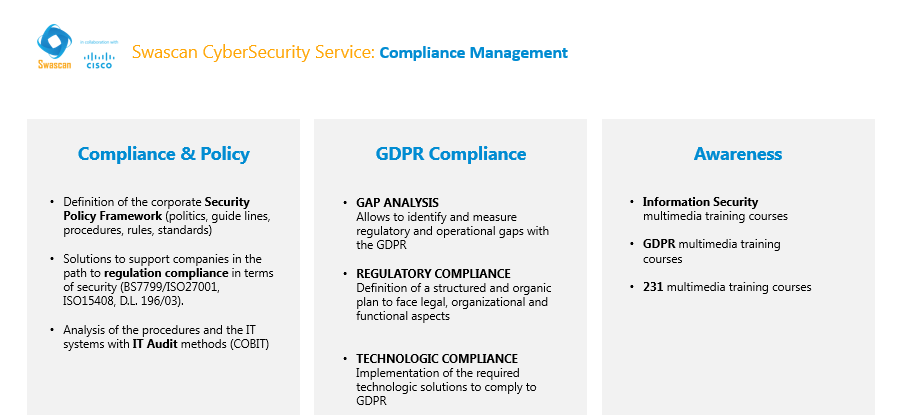
Compliance Management is structured as follows:
- Compliance & Policy:
- Definition of the corporate Security Policy Framework (politics, guide lines, procedures, rules, standards);
- Solutions to support companies in the path to regulation compliance in terms of security (BS7799/ISO27001, ISO15408, D.L. 196/03);
- Analysis of the procedures and the IT systems with IT Audit methods (COBIT).
- GDPR Compliance:
- GAP ANALYSIS = Allows to identify and measure regulatory and operational gaps with the GDPR;
- REGULATORY COMPLIANCE = Definition of a structured and organic plan to face legal, organizational and functional aspects;
- TECHNOLOGIC COMPLIANCE = Implementation of the required technologic solutions to comply to GDPR.
- Awareness:
- Information Security multimedia training courses;
- GDPR multimedia training courses;
- 231 multimedia training courses.
Security Management: value proposition
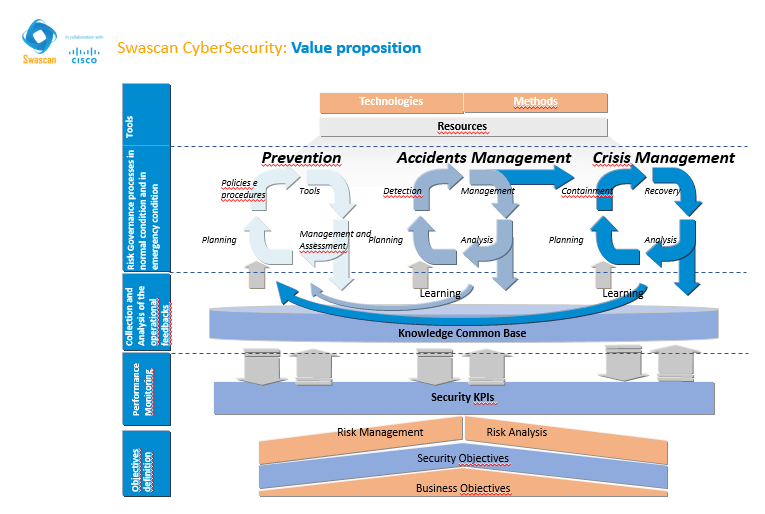
Here’s Swascan value proposition in terms of Security Management.
Security Management: Framework
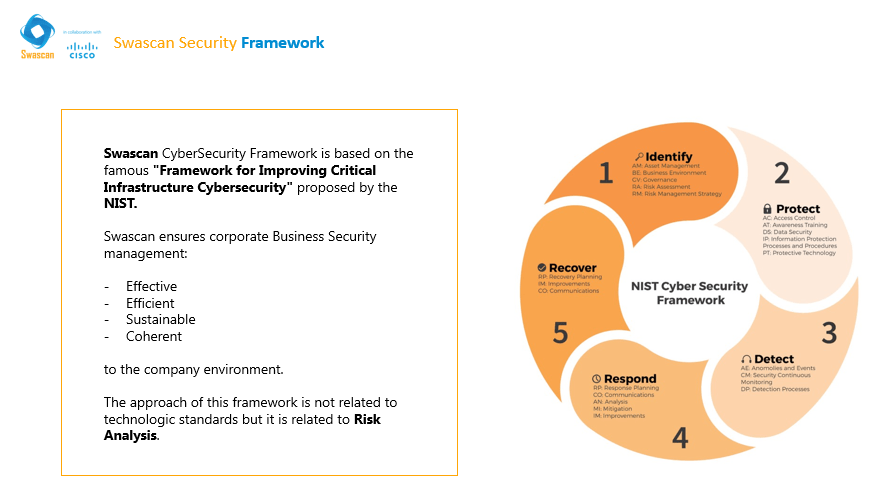
Swascan CyberSecurity Framework is based on the famous “Framework for Improving Critical Infrastructure Cybersecurity” proposed by the NIST.
Swascan ensures corporate Business Security management:
- Effective
- Efficient
- Sustainable
- Coherent
to the company environment.
The approach of this framework is not related to technologic standards but it is related to Risk Analysis.





