Bitcoin wallets: why .dat files?
To trade in Bitcoin, a potential investor has to establish a digital wallet. A Bitcoin wallet is analogous to a physical wallet. However, instead of storing the physical currency, the wallet stores relevant information such as the secure private key used to access Bitcoin addresses and perform transactions.
Technically, when we buy such a cryptocurrency and transfer it into our wallet, the original Bitcoin client stores the private key information in a file called wallet.dat.
The wallet.dat file contains our private keys, public keys, scripts (which correspond to addresses), key metadata and transactions relating to our wallet.
There are various types of Bitcoin wallets: desktop, mobile, web and hardware.
Bitcoin wallets: The illigal trade in .dat files
All these types of wallets have one thing in common, therefore: they store .dat files, the passkey to access Bitcoins.
Obviously, the incredible attention and – above all – the incredible value of bitcoin has attracted a large number of criminal hackers and aggressive ‘scammers’ trying to get their hands on bitcoin wallets.
There are two ways in which criminal hackers manage to get their hands on these files: through the use of Botnets – in particular those carrying the Azorult malware – or simply by buying from various file databases that have already been stolen in the past.
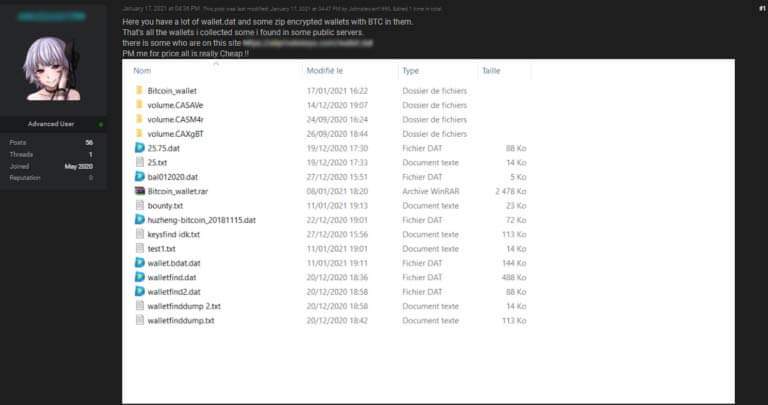
Through an OSINT analysis, Swascan was able to collect a lot of evidence of forums and sites where this trade takes place.
In this post, for example, the user sponsors a “collection” of stolen wallet.dat, on sale for 0.00147174 BTC or about 70 euros.
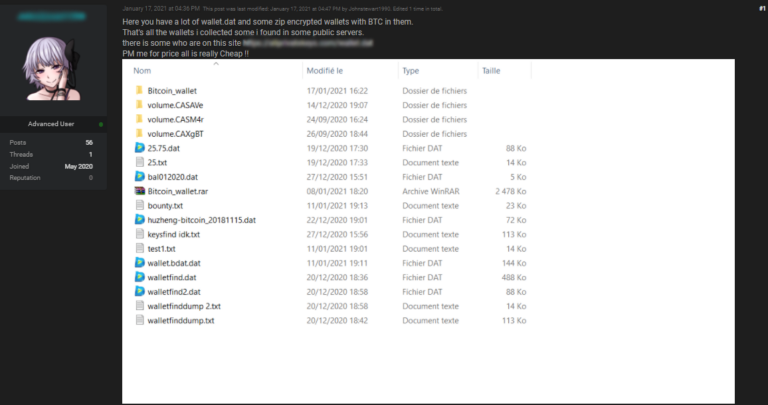
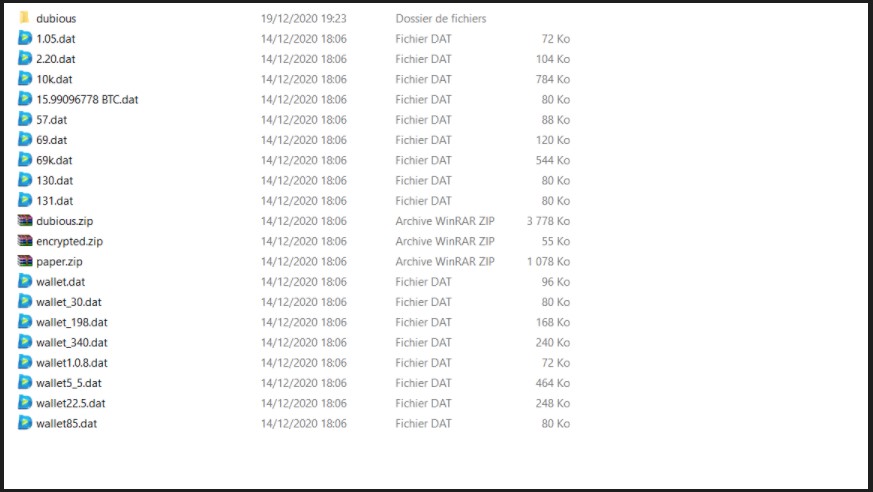
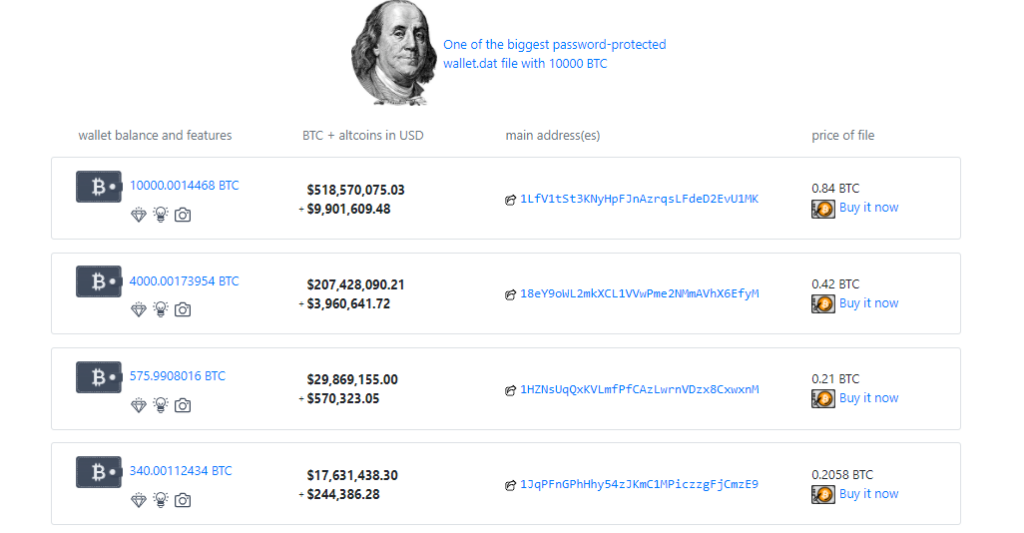
But there are also those who go further, selling wallets containing large sums of Bitcoin, thereby raising the price of the stolen ‘goods’.
- Some wallets date back as far as 2010-2011. A “collection” known as Satoshi’s Treasure or even more commonly as Satoshi’s Box. It dates back to a time when Bitcoin cost nothing and you could mine it for free on your laptop.
The latter case is even more refined as a method of illegal trade, fully equipped with guides and how-tos, as well as warnings – ironically – on how to avoid being scammed!
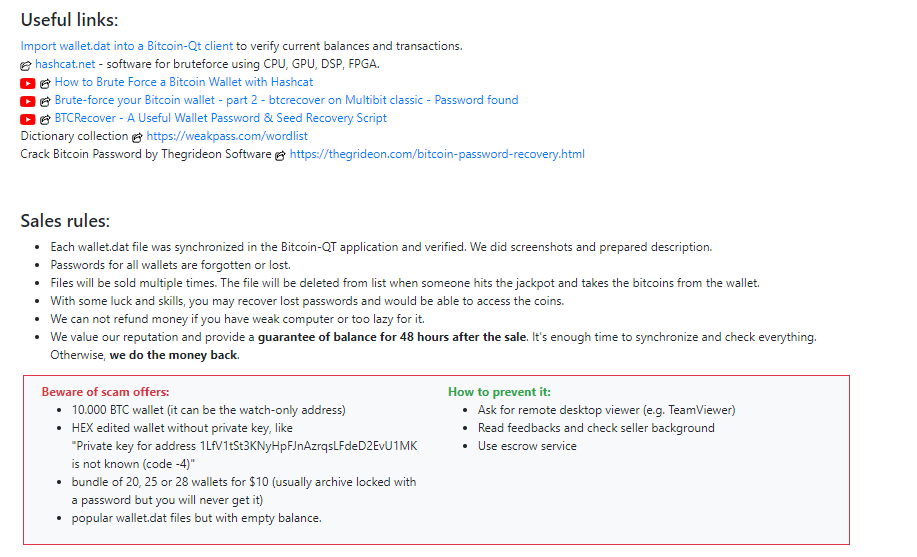
Of course, the process is not that simple; criminal hackers are selling encrypted archives anyway, which are almost useless if you are unable to extract the stolen .dat files.
And here is the second stage of hacking stolen wallets: decryption.
Once the scammers get hold of the .dat files, they have to go in search of specialised decryptors capable of ‘opening’ these wallets. By doing a simple search on the ever-popular GitHub, we were able to isolate some (obviously dated) examples of such software.
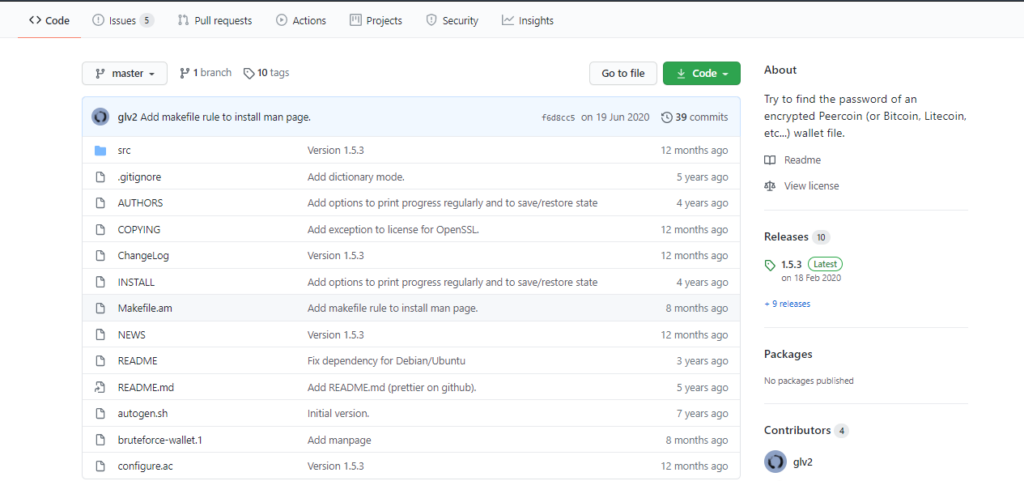
Called Brute Force wallet, the programme promises to:
The purpose of this program is to try to find the password of an encrypted Peercoin (or Bitcoin, Litecoin, etc…) wallet file (i.e. wallet.dat).
It can be used in two ways:
- try all the possible passwords given a charset
- try all the passwords in a file
There is a command line option to specify the number of threads to use.
Sending a USR1 signal to a running bruteforce-wallet process makes it print progress and continue.
Another similar tool we have tracked down is Walletool.
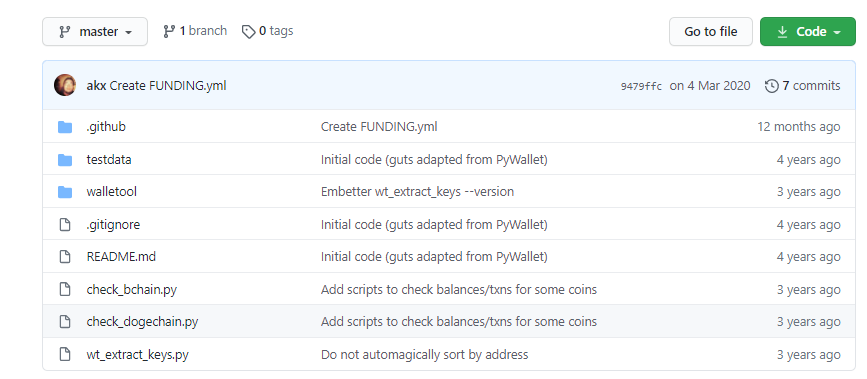
This simply states that it is able to:
Extracting private keys from Bitcoin-QT/Litecoin-QT wallets
- Have your
wallet.dathandy. - For Bitcoin, run
python wt_extract_keys.py -d wallet.dat -v 0 - For Litecoin, run
python wt_extract_keys.py -d wallet.dat -v 48
A list of addresses / private keys is printed.
Alongside the newfound boom in Bitcoin and on the wings of the enthusiasm typical of the initiatives created by Elon Musk – promoter of the latest surge in value, we can nevertheless note that the Cyber Crime market linked to the illegal trade in stolen Bitcoins is still strong and more dangerous than ever.




