BitLocker Ransomware – analysis by Fabrizio Rendina, Riccardo Paglia and the Soc As a Service Team Swascan
Common antivirus software currently manages to intercept almost all ransomware in circulation. But what happens when the ransomware actually exploits a Windows feature? We are talking about BitLocker, an add-on already installed in common operating systems which, if used fraudulently, could lead to the loss of data availability.
This is the case of BitLocker Ransomware, a malware that is spreading like wildfire these days in Italy: it is a crypto ransomware that has been spreading all over the world since 2015 (when it was only aimed at English-speaking users).
Its name comes from the Windows feature used to extort money: BitLocker (well-known encryption software included with all versions of Windows Professional and Enterprise, both Client and Server), which allows entire partitions to be encrypted without adding extensions to the encrypted files.
If the PC does not have a ‘data partition’ other than the operating system partition, the malware is able to create (and encrypt with BitLocker) a file containing a virtual partition (VHD) and move all the user’s documents into this ‘virtual partition’ (this is referred to as ‘VHD Locker Ransomware’).
BitLocker deactivated, are we safe from danger?
Nope! The attacker has also thought of this possibility and is able, with simple commands executed automatically, to enable the BitLocker functionality:
![]()
The commands can for instance be included in a Powershell script installed at the time the machine is infected.
Infection can take place in different ways: generally, human risk is exploited (phishing, smishing, social engineering techniques that convince the user to click on a malicious link).
Other times, technological risk is exploited: vulnerabilities exposed and never solved, antivirus signatures not updated, inadequate defense measures, services exposed with default credentials…
Once the machine has been infected, the victim’s partition containing data is fully encrypted with a complex password known only to the attacker. The victim’s machine is then rebooted and the partition is no longer accessible. A Word document appears on the victim’s desktop with instructions on how to pay the ransom: the amount required ranges from EUR 150 to EUR 100,000, payable in bitcoin to the address given in the Word document.
BitLocker Ransomware: How to proceed in such cases?
The only way to recover the data is to be able to find traces of the encryption password used by the attacker or, alternatively, the recovery code in the .txt file automatically generated by BitLocker at the end of encryption of the partition.
Actually, there is also a third option: trying to guess the password using Bruteforcing or Dictionary Attack techniques. These techniques can only (and only) be used if the encryption method used by BitLocker is ‘with Password’ (rather than with ‘certificate’ or using TPM) and if the password chosen is ‘simple’ (a word from the dictionary or a word no longer than 10 characters).
In the case of BitLocker Ransomware, the method used is always ‘with Password’.
To detect the method used, you must issue the following command from an open Windows command shell with admin rights:
manage-bde -protectors <Unità> -get
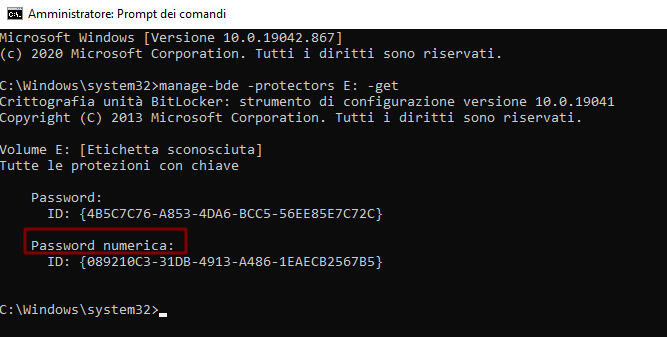
“Numerical Password” is the method used to encrypt the partition. Please note that this is the password ID, not the password! The same command, but given with the partition unlocked, would also show the password used for encryption in clear text.
But the complexity of the password detected during these infections is such that any attempt at bruteforcing is useless, effectively ruling out the use of this technique.
All that remains, therefore, is to find the password (or its recovery code).
But where to look for it?
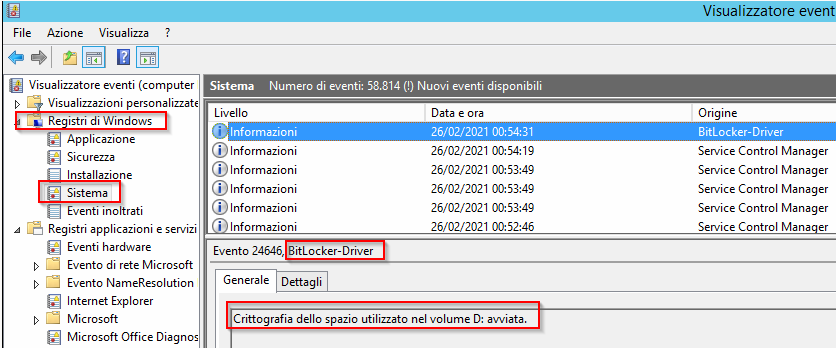
The first step is to use the Event Viewer (Windows Registry -> System) to find out exactly when the partition was encrypted using BitLocker.
At the end of the encryption process BitLocker forces the user to save a copy of the recovery key (composed of 48 digits): it is possible to choose whether to save it on the Microsoft account possibly connected to the user session, on an external USB device, on a .txt file or on a paper printout.
In this case, since the attack was carried out remotely, the choice is compulsory: save it to a .txt file.
BitLocker Ransomware: Finding this .txt file would then make the partition accessible again
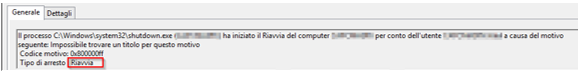
Once encryption is complete, the ransomware attack requires the user’s PC to be automatically rebooted: since the ‘Automatic Unlock at Boot’ option has not been configured, the partition becomes inaccessible to the user who has neither the password nor the recovery code:
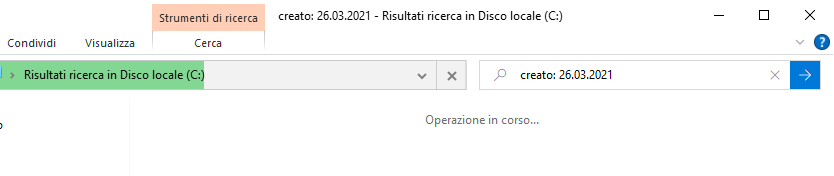
Once you know the exact time of the infection, you can search your operating system for all ‘.txt’ files created on the day the partition was encrypted.
To do this, you can use the search tool in ‘Windows Explorer’ by specifying the creation date of interest with the keyword ‘created: <DATE>’:
But there is a possibility that the attacker has deleted the .txt file with the recovery code.
BitLocker Ransomware: What to do in this case?
Use programs to recover deleted files.
One of the best (free and OpenSource) is PhotoRec (https://www.cgsecurity.org/wiki/PhotoRec):
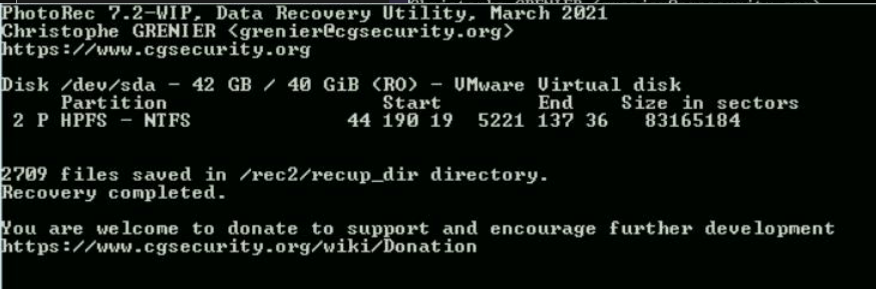
You can use it to search for any file extension or specify only those of interest (.txt).
To search through the thousands of recovered text files for the one that suits your needs, you can use the following command:
findstr /s /i “<ID_Password_Numerica>” *.txt
If we are lucky, we will then find the text file containing the ID of the password we were looking for and the recovery code that can be used to unlock the partition.
However, our team’s analysis has shown that the text file with the recovery code was saved inside the encrypted partition at the end of the encryption process, making recovery impossible.
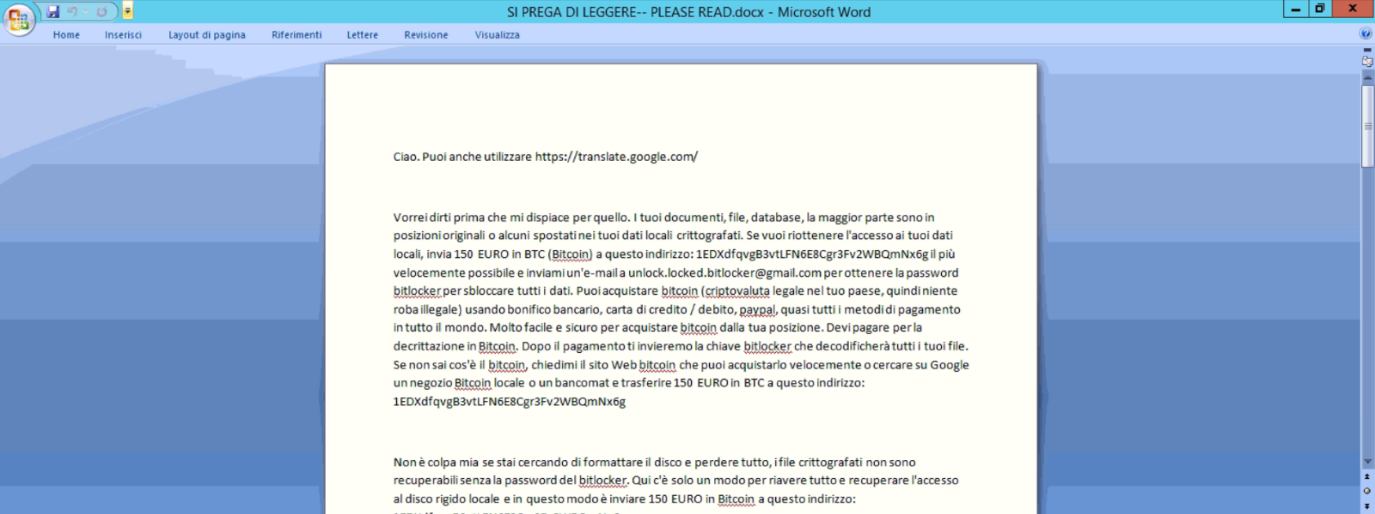
A “PLEASE READ.docx” file appears on the desktop of the BitLocker Ransomware victim with the following ransom demand:
“Hi. You can also use https://translate.google.com/
I would like to tell you first that I am sorry about this. Your documents, files, databases more are in the original location or some have been moved to your local encrypted data. If you want to get back access to your local drive, all your files, documents, etc., send 150 EURO in BTC (Bitcoin) to this address: 1EDXdfqvgB3vtLFN6E8Cgr3Fv2WBQmNx6g as fast as possible and email me at [email protected] to get the BitLocker password to unlock all your data. You can buy bitcoin (cryptocurrency legal in your country, so no illegal stuff) using bank transfer, credit/debit card, PayPal , almost all payment methods worldwide. Very easy and safe to buy bitcoin from your location. You have to pay for bitcoin decryption. After payment we will send BitLocker key which will decrypt all your files.
If you don’t know what bitcoin is, ask me for a bitcoin website that you can buy it quickly or google a local bitcoin shop or ATM and transfer 150 EURO BTC to this address: 1EDXdfqvgB3vtLFN6E8Cgr3Fv2WBQmNx6g
It’s not my fault if you try to format the drive and lose everything, encrypted files are not recoverable without the BitLocker password. Here is only one way to recover everything and regain access to your local hard drive and that is to send 150 EURO BTC to this address: 1EDXdfqvgB3vtLFN6E8Cgr3Fv2WBQmNx6g
After payment, we will send you the Bitlocker password that will immediately decrypt all your files.
It’s just business not trying to get your money and then not giving you the BitLocker password. Looking forward to your reply to my email address ([email protected]) or my second email in case gmail doesn’t work ([email protected]) if you want to get the BitLocker password.
If you have any other questions, please do not hesitate to contact me at any time.
Thanks for your time!”
Within the ransom note shown are the following two email addresses:
And the following bitcoin address to send the ransom to:
- 1EDXdfqvgB3vtLFN6E8Cgr3Fv2WBQmNx6g
Very often the attacker’s goal is to have as many victims as possible: the same malware is then sent to all users, indiscriminately. This has a small advantage: the password used for encryption is the same and can be re-used to unlock partitions infected by different users!
By performing thorough Threat Intelligence activities on the above IoCs, Swascan’s SOC as a Service was able to find the encryption password associated with the currently running BitLocker Ransomware campaign:
The password is as follows:
- 123Φxî◙╧▬╫¶╘≥N^&_%0135å>ô0á÷º-y#$%13#%$φ1ùφ”]¯Σ√IÆD╡▀^@@╞1φ”.$ú¡Z↔╝↓ë@”4╓|I2æ
Other passwords found (and used in the past by the same attackers to encrypt partitions) are:
- 122Φxî◙╧▬╫¶╘≥N^&_%#$%#$φ”♫╡▀CUS01åå▌Qqe¥>╞ì<$^@╞♪*.$ú¡Z↔╝↓ë2ßφ1ór¥-2¼88849
- 123Φxî◙╧▬╫¶╘≥N^&_%0135å>ô0á÷º-y#$%13#%$φ1ùφ”]¯Σ√√IÆD╡▀^@@╞1φ”.$ú¡Z↔╝↓ë2ßφ1ór¥!@#$@
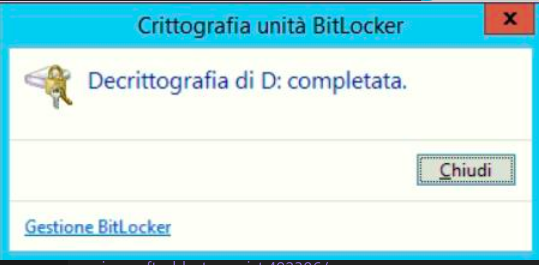
In the case analysed by our team, entering the highlighted password enabled the partition to be unlocked and correctly decrypted, allowing the user to regain possession of their data.
Within the decrypted partition, an ‘as.txt’ file containing the data of the recovery key was detected:
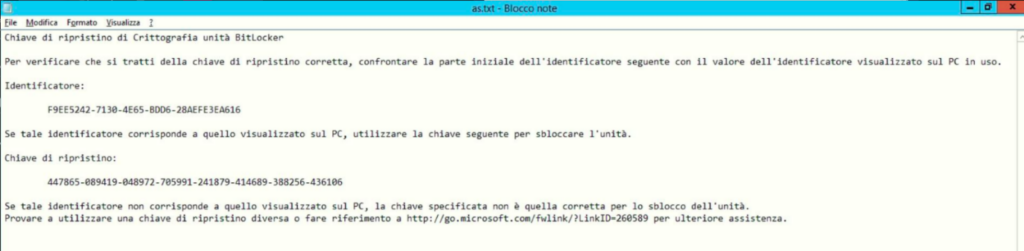
By storing this key in the encrypted partition, the attacker therefore made it untraceable, thus making any forensic analysis of the ‘unencrypted’ partition impossible.
If you too have been a victim of this Bitlocker Ransomware and have found yourself with an encrypted partition and need to perform Data Recovery try entering one of the three passwords shown above: with a bit of luck, you may have found the key to regain possession of your data.
Or contact Swascan’s Cyber Incident Response: https://www.swascan.com/incident-response/
IoC:
[email protected]
[email protected]
1EDXdfqvgB3vtLFN6E8Cgr3Fv2WBQmNx6g
as.txt
This article is intended to help security managers and CERT teams, including personnel in the various Security Operation Centres (SOCs). Security professionals can use this intelligence analysis to better understand the behaviour of BitLocker Ransomware and to understand what indicators of compromise (IoC) are available. The article provided can also help inform ongoing intelligence analysis, forensic investigations, particularly for the discovery of compromised hosts, damage control and risk minimisation.




