
Cross site scripting
Cross Site Scripting or XSS is a particular form of injection attack. Basically, attackers inject malicious scripts into a website. The attackers typically use web applications to transmit malicious codes, usually browser side scripts, to a different end user. In return, the web applications in a system generate output in response to the malicious input without validating or encoding it.
As we said in previous articles, SQLi or SQL injection and Path traversal are quite popular methods of attacking a website too. Actually, SQLi features are at the first position of Top 10 vulnerabilities of OWSAP. In SQLi, malicious data are sent as part of a query or a command to trick the websites’ interpreter and making it execute it and divulge data to the attacker. Path traversal (also known as Directory Traversal) attacks files/directories that are stored outside the web root folder. With this attack, the hacker can access such files or folder including critical system files or source code.
[post-button]
Cross site scripting: how does it work?
Through a XSS attack, hackers do not target the victims directly but exploit vulnerabilities within a website or web application that the victim visits. A malicious script will not be suspected by the victim’s browser and will be executed. Afterwards, this malicious script can get any session tokens, cookies or sensitive information accessed by the browser. These malicious scripts can even rewrite the content of an HTML page.
There are three common types of XSS:
- Type I or Persistent or Stored XSS;
- Type II or Non-persistent or Reflected XSS and
- DOM-based XSS or Type 0.
Since these three types of Cross Site Scripting can overlap, some people prefer to classify XSS on the basis of Server and Client XSS.
- In Server XSS the untrusted user-supplied data are integrated in HTML response that has been created by the server and the vulnerability lies in the code in the server side.
- In Client XSS malicious data are manipulated in order they can update the DOM with some insecure JavaScript calls.
As a matter of fact, you can prevent Server Cross site Scripting with context-sensitive server side output encoding. Moreover, you can protect yourself from Client XSS incorporating safe Java Script APIs.
Cross site scripting: prevention
You can fully protect your business from these types of vulnerability. You should thoroughly check your systems using an automated online tool to assess your website’s risk.
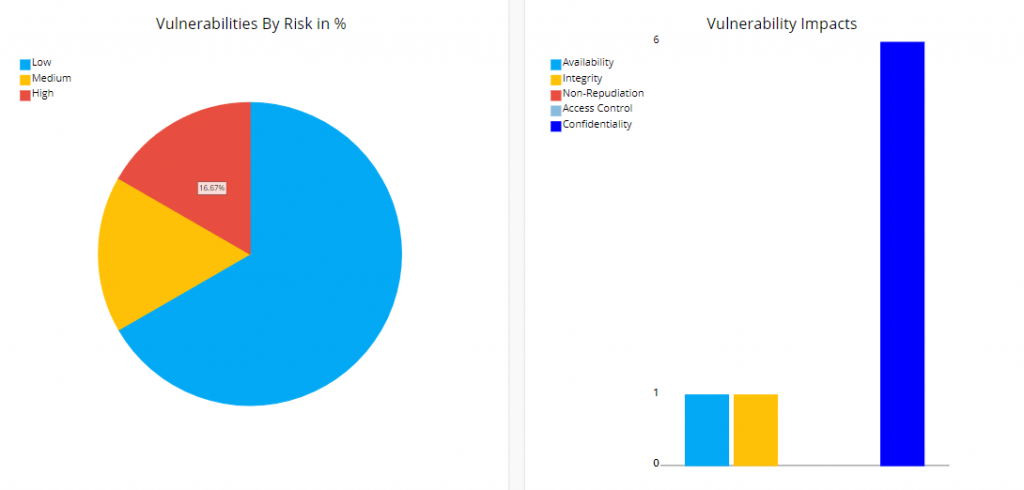
Swascan Vulnerability Assessment is the perfect tool. Basically, the scanner crawls the entire website to check for vulnerabilities. Afterwards, it prepares a detailed report along with suggesting the means to fix them. There are some advantages of such scanners. As a matter of fact, it can also check the website’s vulnerability for SQL injection, Path traversal, etc.
In order to ensure absolute protection, Swascan developed a unique Vulnerability Assessment tool.
[post-button]
Swascan
In order to assure to your business the best tool available, Swascan developed a special ( Premio Cisco-Marzotto winner ) cybersecurity platform. It is completely in Cloud, Pay per Use and SaaS. You can see for yourself in our brochure: Cybersecurity platform and have an in-depth look at our services. Our four services cover all the governance needs in terms of risk management and periodic assessment. Basically, if you need to understand the areas in which your efforts must focus, Vulnerability Assessment, Network Scan, Code Review and GDPR Self-Assessment are the right tools for you. Last but not least, don’t forget GDPR: our platform is 100% GDPR compliant ( GDPR infographic ).




