
DOS: introduction
DoS stands for “Denial of Service” and this term, in the CyberSecurity field, specifies a failure due to an illegal attack. The resources of an IT system run out because of the just mentioned attack, this leads to the impossibility from the system side to erogate the service to the clients who require it.
The most simple example of a DoS attack is the Syn-Flood. This is generated simulating thousands and thousands of clicks on a single page. As a matter of fact, it’s possible to program a PC and make it open loads and loads of connections each second that reach at the same time the server and consume its memory, this leads to a block or a crash of the server.
To boost and make a DoS attack more effective, often the attackers use a botnet. It is a network of previously infected computers which the attacker can control. In these specific attacks, different sources target the objective at the same time making it difficult for him to recognize the original source of the attack.
[post-button]
DOS: different attacks
On the other side, DoS attacks carried out by a single host can be traceable because of their single source.
Nowadays, we know two different types of DoS attack:
- Direct attack → the attacker directly interacts with the target. In this scenario the attacker’s said real and we have a primary victim.
- Indirect attack → the attacker exploits third parties to attack the victim. In this particular scenario we have a reflected attacker, a secondary victim (the third party) and the final target that is the primary victim.
Both the direct and the indirect attack are useless in these days. The technologic evolution of the IT systems and the devices cancelled completely the effects of such attacks (no up-to-date PC can be a target of such attacks). It is a different thing as far as DDoS attacks are concerned.
DOS: protect your network
In order to protect and secure your network, you had better run a Network Scan. This test will identify all the vulnerabilities in your network, Network Scanning is crucial because these vulnerabilities and weak spots are all that hackers are waiting for in order to sneak in the network of a company. To this end, there is a urgent need. It’s important to implement all the adequate measures in order to avoid the exploitation of these situations.
Swascan and its Network Scan service, provides detailed information regarding the “health” of your network identifying vulnerabilities and criticalities. Moreover, the Network Scan report allows to fix these weak spots providing a detailed action plan to follow. For a free trial of the solution, just click the button below:
[post-button]
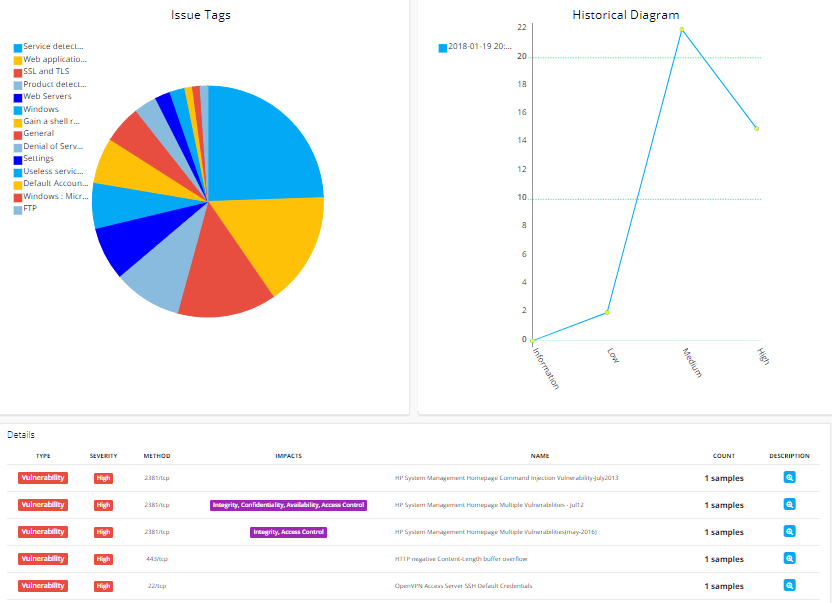
Here you can see an overview of the Network Scan report:
Swascan
In order to assure to your business the best tool available, Swascan developed a special cybersecurity platform. It is completely in Cloud, Pay per Use and SaaS. You can see for yourself in our brochure: Cybersecurity platform and have an in-depth look at our services. Our four services cover all the governance needs in terms of risk management and periodic assessment. Basically, if you need to understand the areas in which your efforts must focus, Vulnerability Assessment, Network Scan and Code Review are the right tools for you. Last but not least, don’t forget GDPR: our platform provides a GDPR Self-Assessment that gives the indicators in terms of GDPR Compliance level, our platform is 100% GDPR compliant ( GDPR infographic ).




