IP address: introduction
You can visualize the IP address or “internet protocol address” in the graphic interface as a numerical label. It allows to univocally identify a host (which is a physical device such as a computer, a printer, a router or a smartphone).
The host is connected to a network that uses the internet protocol as network protocol.
[post-button]
IP address: division and versions
Every IP address is divided in two sides:
- the first one identifies the network and it’s related to the routing at the level of subnets.
- the second one identifies the host in the network as well as eventual subnets.
ICAAN releases and rules public IP addresses. This is the international management organization which, because of the lack of room for the IPv4 addresses and the necessity to avoid limitations related to the version 4 of this protocol, released a second version of the protocol. The name of this version is IPv6.
There is a crucial difference between these two versions of the IP protocol; the IPv4 address is made of 32 bits and it’s divided in 4 groups of 8 separate-by-a-point bits each (for example→ 192.168.80.1). On the other hand, the IPv6 address is made of 128 bits divided in 8 groups made of 2 bytes each. This symbol ” : ” represents the separation between these groups. This method allows the allocation of a greater amount of addresses compared to the number that could have been assigned with the first version of the protocol (for example→ 2001:0DB8:0000:0000:0000:0000:0000:0001).
Moreover, it exists an additional difference in the definitions of:
- Static IP address: this IP address is assigned every time to the same device (ISP permitting).
- Dynamic IP address: as we’ve seen before, the number of the available IPs is not endless. In order to face this issue, we have dynamic IP addresses: an IP address chosen among the ones available for the ISP. Once this IP address has been chosen, it is assigned (and changed) automatically whenever a new connection happens.
The first providers
The first internet connection providers managed to obtain a huge amount of IP addresses that did not reflect their actual needs. This behavior, together with the increased amount of the hosts that need to be public on the internet, is one of the causes of the saturation of the IPv4 space. This pace caused the exhaustion of the IPv4 addresses available and the necessity to move to the IPv6.
[post-button]
The following providers
The providers who entered the market in a second moment tried to address this shortage situation putting their users, which belong to a specific area, inside a private network that accesses the web using a single public IP address (NAT), assigning on the other hand private IP addresses to the single users.
IP address: protection
In order to protect and secure your network, you had better run a Network Scan. This test will identify all the vulnerabilities in your network, this is a very important step because these vulnerabilities and weak spots are all that hackers are waiting for in order to sneak in the network of a company. To this end, there is a urgent need: implementing all the adequate measures in order to avoid the exploitation of these situations.
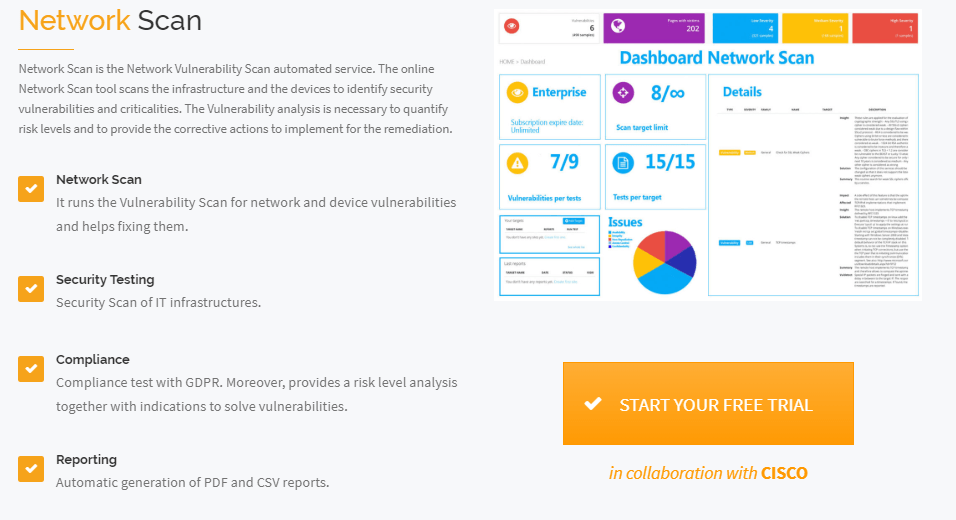
Swascan and its Network Scan service, provides detailed information regarding the “health” of your network identifying vulnerabilities and criticalities. Moreover, the Network Scan report allows to fix these weak spots providing a detailed action plan to follow. For a free trial of the solution, just click the button below:
[post-button]
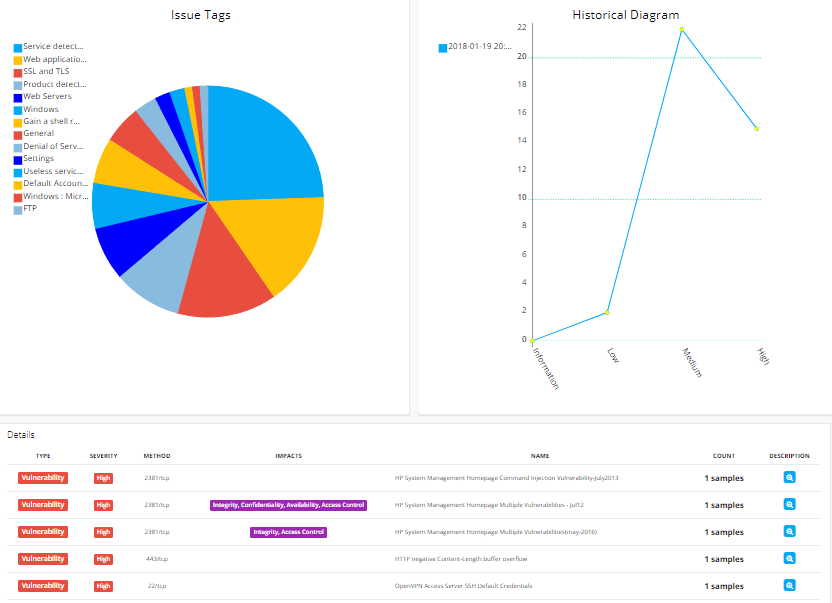
Here you can see an overview of the Network Scan report:
Swascan
In order to assure to your business the best tool available, Swascan developed a special cybersecurity platform. It is completely in Cloud, Pay per Use and SaaS. You can see for yourself in our brochure: Cybersecurity platform and have an in-depth look at our services. Our four services cover all the governance needs in terms of risk management and periodic assessment. Basically, if you need to understand the areas in which your efforts must focus, Vulnerability Assessment, Network Scan and Code Review are the right tools for you. Last but not least, don’t forget GDPR: our platform provides a GDPR Self-Assessment that gives the indicators in terms of GDPR Compliance level, our platform is 100% GDPR compliant ( GDPR infographic ).




