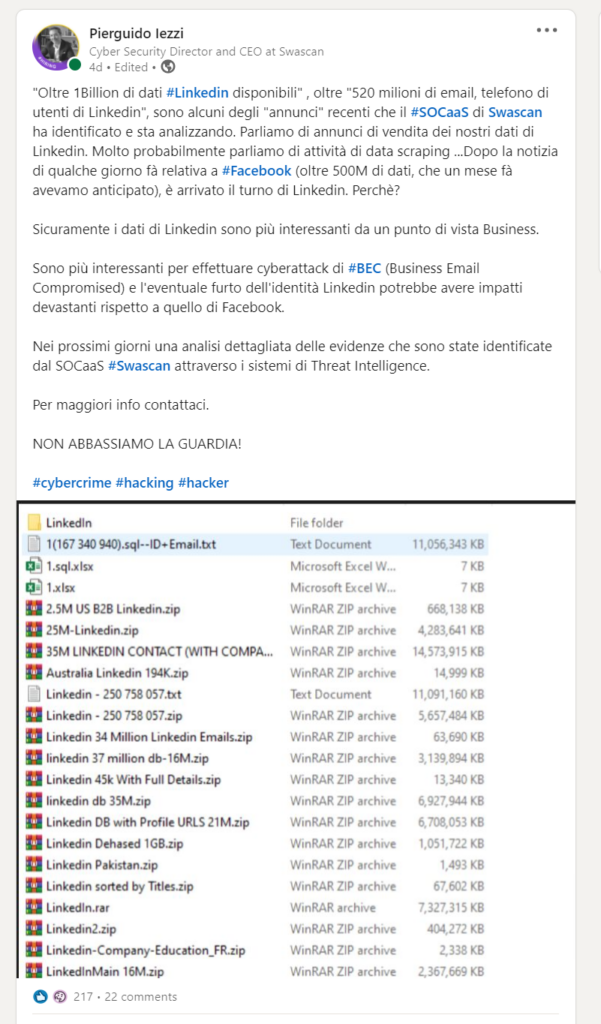
On April 5th Swascan’s SOCaaS and Cyber Threat Intelligence Teams first identified and reported the presence of a huge Linkedin database for sale on the web and dark web. The Linkedin news was preceded by the discovery of the most recent Facebook data leak which involved 553 million users.
https://www.linkedin.com/feed/update/urn:li:activity:6785063470124560384/
Traslated:
“Over 1Billion recds of #Linkedin data available”. over “520 million emails, phone of LinkedIn users”, are some of the recent “ads” that Swascan’s #SOCaaS has identified and is analyzing. We are talking about ads selling our LinkedIn data. Most likely we are talking about data scraping activities… After the news a few days ago about #Facebook (over 500M of data, which we had anticipated a month ago), it is now LinkedIn’s turn. Why?
Linkedin’s data are certainly more interesting from a business point of view.
They are more interesting to carry out cyber attacks than #BEC (Business Email Compromised) and the possible theft of LinkedIn’s identity could have devastating impacts compared to Facebook’s.
In the coming days, a detailed analysis of the evidence that has been identified by the #Swascan SOCaaS through Threat Intelligence systems.
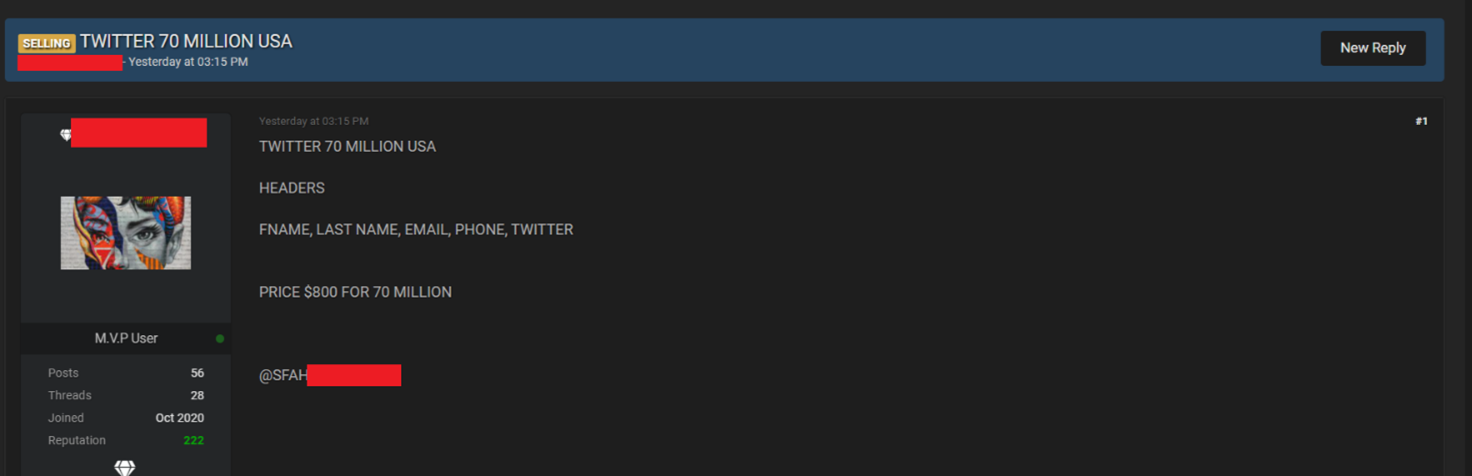
Today Swascan discovered another announcement selling Profile Data from another Social Network, Twitter.
Scraped data of 70 Million Twitter users
Through Swascan’s Osint Search Engine platform, we have identified an announcement dated Friday April 9th 2021 which sells data of over 70 million American Twitter users. The information available in the database entails:
- First Name
- Last Name
- Email address
- Phone number
- Twitter account
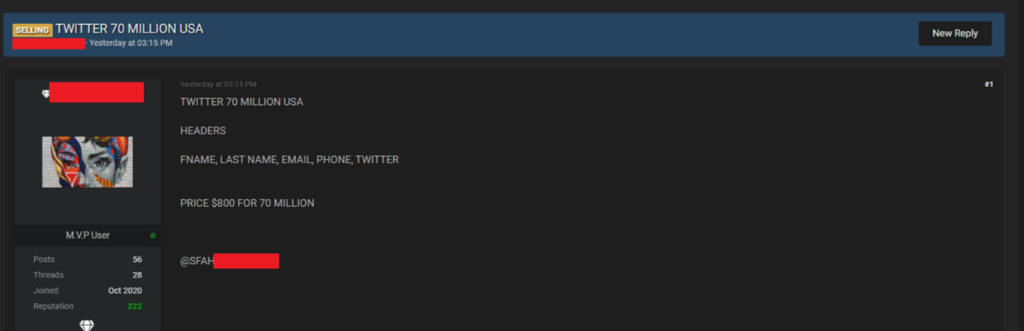
Based on what was declared by the “seller”, the database in question is being sold for $ 800 and does not contain passwords.
The fact that the absence of a password is explicitly indicated would confirm that it is not a database of compromised accounts. To be clear, it is not a list of accounts and data obtained through credential stuffing activities. “Credential stuffing” is a type of cyber attack in which the attacker uses the username and password credentials obtained from a Data Breach to verify, through automated systems, whether the same credentials are also valid on other services and portals.
At this point, if the database of the announcement is “valid” and “real” it is most likely that this information could refer to data obtained through data scraping: a technique that allows information to be extracted from a website using programs and / or applications, as in the cases of Linkedin and Facebook.
TWITTER DATA SCRAPING
By carrying out some simple research, we have identified several available and ready-to-use services designed to carry out targeted data scraping activities on Twitter.
It is enough to research on Google “twitter profile scraper” to get different solutions to test and try with the FREE TRIAL formula.
By searching for “github twitter data scraping”, which is also on Google, specific opensource projects for Twitter and scraping are directly available.
We did not have the opportunity to test and verify them, but by watching this demo video on Youtube, published on March 13th 2021, they seem to be effective for the purpose.
https://www.youtube.com/watch?v=ZlXXNzpPLYk
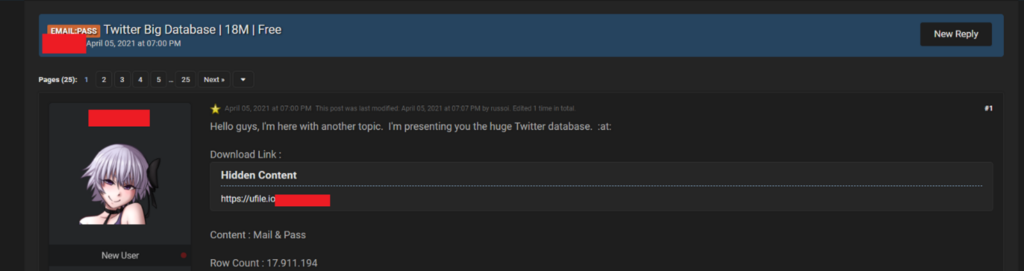
SCAMMER?
As indicated, we do not currently have the possibility to confirm the authenticity of the data; even if the community itself is doubtful that the database, subject to this analysis, is in fact a scam and/or that it refers to the Database of other sales announcements. However, we identified another announcement published on April 5th 2021 referring to a combo list detailing emails and Twitter account passwords. In this case, about 18 million Twitter credentials are at risk.
What is the impact of this Leak?
At the moment it is not possible to establish and determine the authenticity of the data or whether in fact the announcement in question is a scam. However, it is certain that the presence of several combo lists, relating to our data and credentials involved in one of the many daily Data Breaches, could be used for different purposes and attacks:
- Phishing
- Smishing
- Spam
- Business Email Compromised
- Identity Fraud
- Credential Stuffing
- ….
HOW TO DEFEND OURSELVES?
The best solution is always to adopt two-factor authentication and periodically change the password.