Open port checker and port scanner
The open port checker allows the user to obtain different pieces of information:
- the status of a port of an IP address;
- the status of a port on his own connection (verify is the port is open or not);
- if the user’s server applications are blocked by a firewall;
- if the setup of the user’s port forwarding is correct;
- the status of commonly used ports.
One of the most well-known practices to attack a single computer, LAN-connected computers or WAN-connected computers is port scanning. Why so? Because each PC which is online uses ports to allow Internet services to communicate with external world. Through a port scanner, a both LAN and WAN user can test which ports are active and which ones are not. How does this software work? Basically, it sends a data package to each port, scanning each one of the ports of a computer. This scan gives the hacker an idea about vulnerabilities and weak spots of a device.
Ports
It’s well known that authorities assign public IP addresses, these authorities must check for the uniqueness of each IP address. On the other hand, ports behave in a different way. There has been a sort of standardization but there is still freedom in this specific field. However, we can find, within a single IT system, univocal port numbers split into three groups:
Well known ports: from 0 to 1023
Registered ports: from 1024 to 49151
Dynamic and/or private ports: from 49152 to 65535
Here’s a list of the most common ports:
Port number
- 7 Ping
- 21 FTP(File transfer protocol)
- 22 SSH (Secure shell)
- 23 Telnet
- 25 SMTP (Mail)
- 43 WHOIS
- 53 DNS
- 80 HTTP
- 110 POP3 (Mail Access)
- 119 Network News Transfer Protocol (NNTP)
- 143 Internet Message Access Protocol (IMAP)
- 161 Simple Network Management Protocol (SNMP)
- 443 HTTP Secure (HTTPS)
- 513 Remote login
- 4444 Generic Malicious Software
- 8080 Proxy
Open port checker and Network Scan
Once an open port checker tells you which ports are open and which ones are not, it begins phase two. This step consists in understanding whether it’s necessary or not for these ports to be accessible.
The answer is no: you should block them or shut them down
The answer is yes: you should try to figure out the vulnerability these ports represent for your network
In order to ensure your network the best protection available you could perform a network scan with Swascan to spot all of your network vulnerabilities. These vulnerabilities and weak spots are the ideal place for attackers to come after you and your company. it is absolutely necessary to implement all the adequate measures in order to prevent these possible exploits from hackers.
Swascan, through its Network Scan service, provides detailed information about your network vulnerabilities and criticalities. In addition, the report of the Network Scan activity helps managers in fixing these errors and vulnerabilities because it provides a detailed action plan to face your current network situation. To have a free trial of Swascan Network Scan, just click the button below:
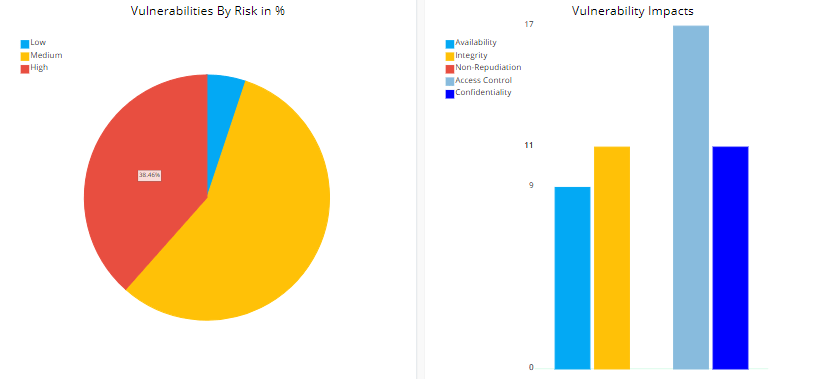
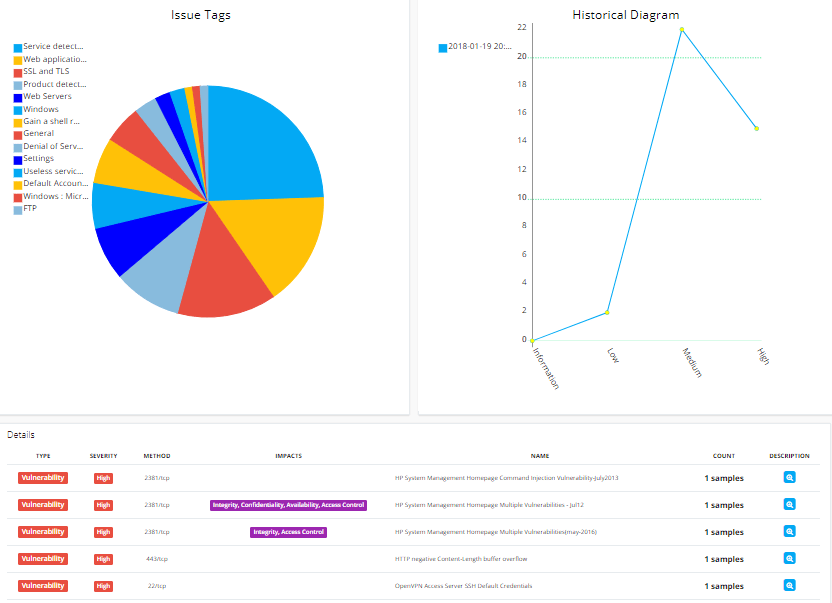
Here you can have a detail of the Swascan Network Scan report:
Swascan
In order to assure to your business the best tool available, Swascan developed a special cybersecurity platform. It is completely in Cloud, Pay per Use and SaaS. You can see for yourself in our brochure: Cybersecurity platform and have an in-depth look at our services. Our three services cover all the governance needs in terms of risk management and periodic assessment. Basically, if you need to understand the areas in which your efforts must focus, Vulnerability Assessment, Network Scan and Code Review are the right tools for you. Last but not least, don’t forget GDPR: our platform is 100% GDPR compliant ( GDPR infographic ).